- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
15868 Courses
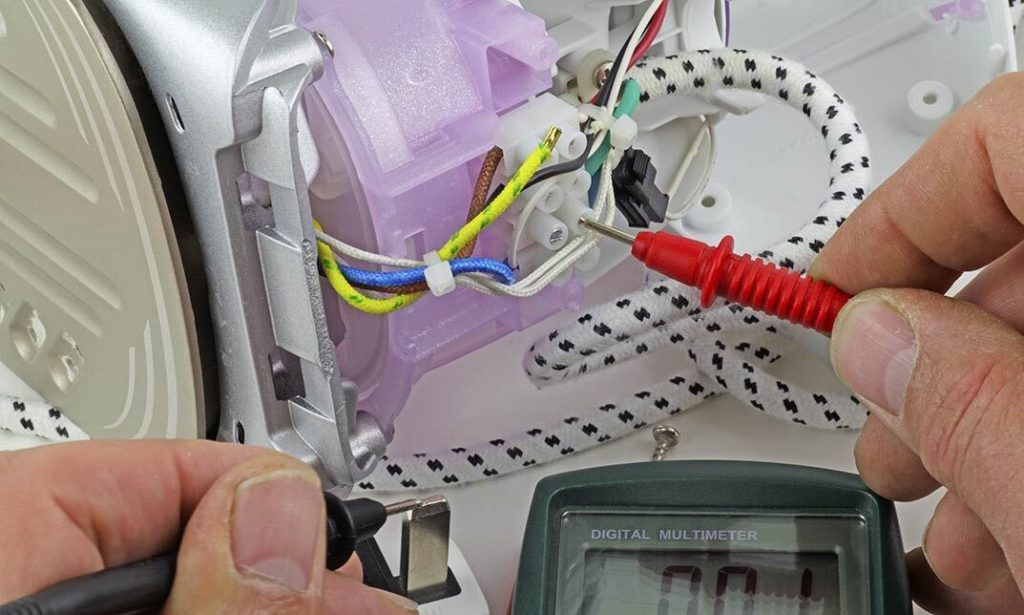
Enhance workplace safety with our comprehensive PAT Testing Training in 2021. Stay up-to-date with the latest industry standards and regulations, ensuring your team is well-equipped to perform Portable Appliance Testing effectively. Gain practical skills, knowledge, and certification for a secure and compliant work environment. Enroll now for the latest PAT Testing Training and empower your team to prioritize electrical safety in the modern workplace.
ONLINE MEDITATION, PSYCHIC AND SPIRITUAL DEVELOPMENT CIRCLE
By Kay Downie
This class runs weekly to encourage psychic and spiritual gifts through meditation

Business Teacher
By The Teachers Training
Unlock your potential as a business teacher with our comprehensive Business Teacher Course. Gain essential skills, resources, and strategies to excel in the classroom and empower future business leaders. Enroll now to transform your teaching and inspire the next generation of entrepreneurs.

SEN Teaching Assistant Certificate
By The Teachers Training
Support the learning and development of students with special educational needs. This SEN Teaching Assistant Certificate prepares you to make a positive impact in inclusive classrooms.

HLTA- Level 4 Certificates for Higher Level Teaching Assistants (RQF)
By Kingston Open College
Updated 2024 | Level 4 HLTA | Ofqual Regulated | By Focus Awards | Tutor Support | 100% Online | For Teaching Assistants
The Control of Substances Hazardous to Health (COSHH) Training Level 3 Course offers a comprehensive introduction to handling hazardous substances in the workplace, ensuring compliance with UK safety regulations. This instructor-guided course provides learners with an in-depth understanding of COSHH principles, including the safe management, risk assessment, and control of hazardous substances. It is designed to equip you with the critical knowledge and skills needed to excel in the field of health and safety management.

Description: The 70-662 - Deploying Microsoft Exchange Server 2010 S course prepares you for the exam 70-662 - Deploying Microsoft Exchange Server 2010 S. The purpose of the MCTS: Microsoft Exchange Server 2010 certification is to validate your skills in support for the maintenance and administration of the Exchange servers in an enterprise environment. In the course, you will learn how to use active directory and support infrastructure, use active directory components, and the network-based services. The course also teaches you about the server roles in Exchange Server 2010, and infrastructure requirements for Exchange Server 2010. You will learn about mailbox servers and recipients, securing the server, mailbox database update process, public folder process for MAPI clients, and e-mail address policies. The course will focus the ways of managing client access, POP3 and IMAP4 options, and Outlook client connectivity troubleshooting. Finally, the course will teach you how to manage Message Transports, Exchange Security and how to implement High Availability. Assessment: At the end of the course, you will be required to sit for an online MCQ test. Your test will be assessed automatically and immediately. You will instantly know whether you have been successful or not. Before sitting for your final exam you will have the opportunity to test your proficiency with a mock exam. Certification: After completing and passing the course successfully, you will be able to obtain an Accredited Certificate of Achievement. Certificates can be obtained either in hard copy at a cost of £39 or in PDF format at a cost of £24. Who is this Course for? 70-662 - Deploying Microsoft Exchange Server 2010 S is certified by CPD Qualifications Standards and CiQ. This makes it perfect for anyone trying to learn potential professional skills. As there is no experience and qualification required for this course, it is available for all students from any academic background. Requirements Our 70-662 - Deploying Microsoft Exchange Server 2010 S is fully compatible with any kind of device. Whether you are using Windows computer, Mac, smartphones or tablets, you will get the same experience while learning. Besides that, you will be able to access the course with any kind of internet connection from anywhere at any time without any kind of limitation. Career Path After completing this course you will be able to build up accurate knowledge and skills with proper confidence to enrich yourself and brighten up your career in the relevant job market. Active Directory and Supporting Infrastructure 70-662-Active Directory and Supporting Infrastructure FREE 00:15:00 70-662-Active Directory Components 00:24:00 70-662-Network Based Services 00:21:00 70-662-Server Roles in Exchange Server 2010 00:21:00 70-662-Infrastructure Requirements for Exchange Server 2010 00:21:00 Mailbox Servers and Recipients 70-662-Mailbox Servers and Recipients 00:58:00 70-662-Secure the Server 00:38:00 70-662-Mailbox Database Update Process 00:26:00 70-662-Public Folder Process for MAPI Clients 00:29:00 70-662- E-Mail Address Policies 00:17:00 Managing Client Access 70-662-Managing Client Access 00:46:00 70-662-POP3 and IMAP4 Options 00:35:00 70-662-Outlook Client Connectivity Troubleshooting 00:23:00 Managing Message Transports 70-662-Managing Message Transports 00:49:00 70-662-How S MIME Works 00:39:00 70-662- Back Pressure - System Monitoring 00:15:00 70-662-Edge Transport Server Security 00:36:00 Exchange Security 70-662-Exchange Security 00:36:00 70-662-Management Role Assignment Policies 00:26:00 70-662-Messaging Policy and Compliance 00:34:00 70-662-Message Classifications 00:21:00 70-662-Considerations for Managing the Message Journal Mailbox 00:37:00 70-662-Managed Folders 00:19:00 Implementing High Availability 70-662-Implementing High Availability 00:18:00 70-662-Database Availability Group 00:32:00 70-662-Transport Dumpster 00:27:00 70-662-Backup and Restore Scenarios 00:26:00 70-662-Database Mobility 00:21:00 70-662-Network and Performance Guidelines 00:18:00 Mock Exam Mock Exam- 70-662 - Deploying Microsoft Exchange Server 2010 S 00:20:00 Final Exam Final Exam- 70-662 - Deploying Microsoft Exchange Server 2010 S 00:20:00 Certificate and Transcript Order Your Certificates and Transcripts 00:00:00

Description: The 70-744 - Securing Windows Server 2016 (MCSE) course explains how to secure Windows Server 2016 environments. It covers methods and technologies for hardening server environments and securing virtual machine infrastructures using Shielded and encryption-supported virtual machines and Guarded Fabric. After completing the course, you will be able to manage the of Active Directory and Identity infrastructures. You will able to handle privileged identities using Just in Time (JIT), and Just Enough Administration (JEA) approaches, as well as implement Privileged Access Workstations (PAWs) and secure servers using the Local Administrator Password Solution (LAPS). The course will also help you to use threat detection solutions such as auditing access, implementing Advanced Threat Analytics (ATA), deploying Operations Management Suite (OMS) solutions, and identifying solutions for specific workloads. Finally, the purpose of the course is to prepare you for the exam Securing Windows Server 2016 ( MCSE). Assessment: At the end of the course, you will be required to sit for an online MCQ test. Your test will be assessed automatically and immediately. You will instantly know whether you have been successful or not. Before sitting for your final exam you will have the opportunity to test your proficiency with a mock exam. Certification: After completing and passing the course successfully, you will be able to obtain an Accredited Certificate of Achievement. Certificates can be obtained either in hard copy at a cost of £39 or in PDF format at a cost of £24. Who is this Course for? 70-744 - Securing Windows Server 2016 (MCSE) is certified by CPD Qualifications Standards and CiQ. This makes it perfect for anyone trying to learn potential professional skills. As there is no experience and qualification required for this course, it is available for all students from any academic background. Requirements Our 70-744 - Securing Windows Server 2016 (MCSE) is fully compatible with any kind of device. Whether you are using Windows computer, Mac, smartphones or tablets, you will get the same experience while learning. Besides that, you will be able to access the course with any kind of internet connection from anywhere at any time without any kind of limitation. Career Path After completing this course you will be able to build up accurate knowledge and skills with proper confidence to enrich yourself and brighten up your career in the relevant job market. Introduction to Attacks, Breaches, and Detection Understanding Types of Attacks FREE 00:33:00 Detecting Security Breaches 00:06:00 Using Sysinternals Tools 00:30:00 Protecting Users and Workstations User Rights and Privileges 01:28:00 Working with Computer and Service Accounts 00:19:00 Protecting User Credentials 00:20:00 Using Privileged Access Workstations 00:12:00 Managing Administrative Access Understanding and Deploying JEA 00:32:00 Using Enhanced Security Administrative Environments (ESAE) Forests 00:12:00 Using Microsoft Identity Manager 00:08:00 Using JIT Administration and PAM 00:16:00 Configuring Anti-Malware and Patch Management Configuring and Managing Windows Defender 00:18:00 Restricting Software 00:28:00 Using Device Guard 00:12:00 Patch Management with WSUS 00:29:00 Auditing and Advanced Threat Analytics Configuring Auditing for Windows Server 2016 00:21:00 Advanced Auditing and Management 00:42:00 Deploying and Configuring ATA 00:15:00 Deploying and Configuring Operations Management Suite 00:07:00 Securing the Infrastructure Secure the Virtualization Infrastructure 00:15:00 Deploying Security Baselines 00:20:00 Deploying Nano Server 00:08:00 Configuring Data Protection Planning and Implementing File Encryption 00:29:00 Planning and Implementing BitLocker 00:32:00 Advanced File Server Management Using File Server Resource Manager 00:58:00 Implementing Classification and File Management Tasks 00:16:00 Working with Dynamic Access Control 00:39:00 Securing the Network Infrastructure Using the Windows Firewall with Advanced Security 00:33:00 Datacenter Firewall 00:08:00 Utilizing IP Security 00:29:00 Configuring Advanced DNS Settings 00:42:00 Monitoring Network Traffic 00:09:00 Securing SMB Traffic 00:07:00 Mock Exam Mock Exam- 70-744 - Securing Windows Server 2016 (MCSE) 00:20:00 Final Exam Final Exam- 70-744 - Securing Windows Server 2016 (MCSE) 00:20:00 Certificate and Transcript Order Your Certificates and Transcripts 00:00:00

Be on the Inside: Decode the Jargon of Project Management
By OnlinePMCourses
Understand the Terminology of Modern Project Management with this Handy Guide and Glossary

CyberSec First Responder: Threat Detection and Response (Exam CFR-210)-Logical Operations
4.3(43)By John Academy
Description: This CyberSec First Responder: Threat Detection and Response (Exam CFR-210)-Logical Operations will help you to understand the anatomy of cyber-attacks. You will gain the skills needed to serve your organizations before, during, and after a breach. A CyberSec First Responder is the first line of defence against cyber-attacks. You will be able to prepare to analyze threats, design secure computing and network environments, proactively defend networks and respond/investigate cybersecurity incidents. It covers the duties of those who are responsible for monitoring and detecting security incidents in information systems and networks, and for executing a proper response to such incidents. Depending on the size of the organization, this individual may act alone or may be a member of a computer security incident response team (CSIRT), and more. So, learn to assess and respond to security threats and operating systems and network security analysis platform by taking this course. Assessment: At the end of the course, you will be required to sit for an online MCQ test. Your test will be assessed automatically and immediately. You will instantly know whether you have been successful or not. Before sitting for your final exam you will have the opportunity to test your proficiency with a mock exam. Certification: After completing and passing the course successfully, you will be able to obtain an Accredited Certificate of Achievement. Certificates can be obtained either in hard copy at a cost of £39 or in PDF format at a cost of £24. Who is this Course for? CyberSec First Responder: Threat Detection and Response (Exam CFR-210)-Logical Operations is certified by CPD Qualifications Standards and CiQ. This makes it perfect for anyone trying to learn potential professional skills. As there is no experience and qualification required for this course, it is available for all students from any academic background. Requirements Our CyberSec First Responder: Threat Detection and Response (Exam CFR-210)-Logical Operations is fully compatible with any kind of device. Whether you are using Windows computer, Mac, smartphones or tablets, you will get the same experience while learning. Besides that, you will be able to access the course with any kind of internet connection from anywhere at any time without any kind of limitation. Career Path After completing this course you will be able to build up accurate knowledge and skills with proper confidence to enrich yourself and brighten up your career in the relevant job market. Overview of Wireless Communications Identify the Importance of Risk Management FREE 00:11:00 Assess Risk 00:13:00 Mitigate Risk 00:22:00 Integrate Documentation into Risk Management 00:14:00 Analyzing the Threat Landscape Classify Threats and Threat Profiles 00:07:00 Perform Ongoing Threat Research 00:12:00 Resources that Aid in Research of Threats 00:03:00 Analyzing Recon Threats to Computing and Network Environments Implement Threat Modeling 00:09:00 Assess the Impact of Reconnaissance Incidents 00:10:00 Performing Reconnaissance on a Network 00:07:00 Examining Reconnaissance Incidents 00:08:00 Assess the Impact of Social Engineering 00:10:00 Assessing the impact of Social Engineering 00:07:00 Assessing the Impact of Phishing 00:03:00 Analyzing Attacks on Computing and Network Environments Assess the Impact of System Hacking Attacks 00:10:00 Cracking Passwords Using a Password File 00:08:00 Assess the Impact of Web Based Attacks 00:11:00 Assessing the Impact of Web-Based Threats 00:03:00 Assess the Impact of Malware 00:08:00 Malware Detection and Removal 00:05:00 Assess the Impact of Hijacking and Impersonation Attacks 00:13:00 Assess the Impact of DoS Incidents 00:09:00 Assessing the Impact of DoS Attacks 00:04:00 Assess the Impact of Threats to Mobile Security 00:08:00 Assess the Impact of Threats to Cloud Security 00:10:00 Analyzing Post-Attack Techniques Assess Command and Control Techniques 00:08:00 Assessing Command and Control Techniques 00:10:00 Assess Persistence Techniques 00:05:00 Detecting Rootkits 00:03:00 Assess Lateral Movement and Pivoting Techniques 00:13:00 Assess Data Exfiltration Techniques 00:04:00 Steganography 00:03:00 Assess Anti Forensics Techniques 00:09:00 Assessing Anti-Forensics 00:03:00 Evaluating the Organization's Security Posture Conduct Vulnerability Assessments 00:16:00 Perform a Vulnerability Scan with Nessus 00:07:00 Perform a Vulnerability Scan with MBSA 00:05:00 Conduct Penetration Tests on Network Assets 00:18:00 Follow Up on Penetration Testing 00:06:00 Collecting Cyber security Intelligence Deploy a Security Intelligence Collection and Analysis Platform 00:19:00 Collect Data from Network Based Intelligence Sources 00:15:00 Collecting Network-Based Security Intelligence 00:07:00 Collect Data from Host Based Intelligence Sources 00:13:00 Collecting Host-Based Security Intelligence 00:15:00 Parsing Log files 00:03:00 Analyzing Log Data Use Common Tools to Analyze Logs 00:22:00 Analyzing Linux Logs for Security Intelligence 00:08:00 Use SIEM Tools for Analysis 00:07:00 Incorporating SIEMs into Security Intelligence Analysis 00:18:00 Parse Log Files with Regular Expressions 00:25:00 Performing Active Asset and Network Analysis Analyze Incidents with Windows-Based Tools 00:17:00 Windows-Based Incident Analysis Tools 00:19:00 Analyze Incidents with Linux Based Tools 00:05:00 Linux-Based Incident Analysis Tools 00:07:00 Analyze Malware 00:11:00 Analyzing Malware 00:03:00 Analyze Indicators of Compromise 00:20:00 Analyzing Indicators of Compromise 00:15:00 Responding to Cyber security Incidents Deploy an Incident Handling and Response Architecture 00:22:00 Mitigate Incidents 00:16:00 Hardening Windows Servers 00:14:00 DNS Filtering 00:05:00 Blacklisting and Whitelisting 00:09:00 Prepare for Forensic Investigation as a CSIRT 00:03:00 Investigating Cyber security Incidents Apply a Forensic Investigation Plan 00:10:00 Securely Collect and Analyze Electronic Evidence 00:08:00 Securely Collecting Electronic Evidence 00:05:00 Analyzing Forensic Evidence 00:07:00 Follow Up on the Results of an Investigation 00:04:00 Mock Exam Mock Exam- CyberSec First Responder: Threat Detection and Response (Exam CFR-210)-Logical Operations 00:20:00 Final Exam Final Exam- CyberSec First Responder: Threat Detection and Response (Exam CFR-210)-Logical Operations 00:20:00 Certificate and Transcript Order Your Certificates and Transcripts 00:00:00
Search By Location
- class Courses in London
- class Courses in Birmingham
- class Courses in Glasgow
- class Courses in Liverpool
- class Courses in Bristol
- class Courses in Manchester
- class Courses in Sheffield
- class Courses in Leeds
- class Courses in Edinburgh
- class Courses in Leicester
- class Courses in Coventry
- class Courses in Bradford
- class Courses in Cardiff
- class Courses in Belfast
- class Courses in Nottingham