- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
2612 Courses
Microsoft Excel Macros & VBA - classroom
By Microsoft Office Training
Course Objectives At the end of this course you will be able to: Record and edit a Macro Assign macros to keyboard shortcuts, Quick Access Toolbar, Buttons and Shape objects. Use the Visual Basic Editor; change the properties of an object; add a module to a project; write the code for a procedure and then run it; and use the Object Browser to search procedures Manipulate data by declaring variables of different data types; combine data by using expressions; use functions to accept input and display output; and declare variables and procedures with the appropriate scope Use decision structures to create procedures that make decisions; and use loop structures to perform repetitive tasks Create an error handling routine in case things go wrong with VBA code ' 1 year email support service Take a closer look at the consistent excellent feedback from our growing corporate clients visiting our site ms-officetraining co uk Customer Feedback Best Training Ever! Just finished a bespoke 1-1 training course in Excel Advanced, Macros & VBA. Pedro is an excellent trainer, imparting his skills and knowledge in the best way - appropriately to audience skills, knowledge and ability. Pedro is always approachable, encouraging and supportive, giving delegates the optimum learning environment. I would not hesitate to recommend Pedro as a trainer, whatever your level of ability. Amanda Morris - Treasury & Systems Accountant at Reall - Real Equity for All The trainer was very knowledgeable, kept everyone involved and was enthusiastic. A great experience.. Simon Harper - Lloyd's of London My learning experience was awesome. Perdinand Reagan - Subsea7 Very nice and relaxed approach to teaching. Was definitely a good learning experience. Jerome Pupe - S5 Agency World The Trainer – Very positive + patient + helpful + thorough Agnes Souza - Direct Wines ' With more than 20 years experience, we deliver courses on all levels of the Desktop version of Microsoft Office and Office 365; ranging from Beginner, Intermediate, Advanced to the VBA level. Our trainers are Microsoft certified professionals with a proven track record with several years experience in delivering classroom, one to one, tailored and bespoke courses. Tailored In Company training: You can choose to run the course exactly as they are outlined by us or we can customise it so that it meets your specific needs. A tailored or bespoke course will follow the standard outline but may be adapted to your specific organisational needs. Introduction to Macros and VBA Introducing Visual Basic for Applications Recording a Macro Naming conventions for Macro Procedures Running a Macro Absolute or Relative Cell Referencing Saving and Opening Files with Macros Making macros always available Adding Macros to Keyboard Shortcuts, Quick Access Toolbar, Buttons and Shapes Editing a Macro in the Visual Basic Editor Understanding the Development Environment Customising the Editor Tips for General Typing in VBA Using Visual Basic Help Working with Procedures Program Design Understanding Modules Naming Rules Creating a Module Understanding Procedures Programming Macro Concepts Creating a Subroutine Creating a Function Understanding Arguments Exiting Procedures Calling Procedures Objects, Properties, Methods and Events Understanding Objects Properties, Methods, and Events Navigating the Object Hierarchy Understanding Collections Accessing a Member of a Collection Understanding Hierarchy Using the Object Browser Using the With Statement Working with Properties Working with Methods Creating an Event Procedure Reserved Macro Names Using Expressions, Variables and Intrinsic Functions Understanding Expressions and Statements Declaring Variables Understanding Data Types Determining the Value of Variables Working with Variable Scope Using Built-in VBA Functions Understanding Constants Using Message Boxes Controlling the Answer to a Message Box Using Input Boxes Declaring and Using Object Variables Controlling Program Execution Understanding Control-of-Flow Structures Using the If...End If Decision Structures Nested If Statements Using the Select Case ... End Select Structure Using the Do ... Loop Structure Using the For ... Next Structure Using the For Each ... Next Structure Guidelines for Use of Control-of-Flow Structures Debugging and Handling Errors Understanding Errors Using Debugging Tools Setting Breakpoints and Using Break Mode Stepping Through Code Trapping Errors with the On Error Statement Understanding the Err Object Working with Inline Error Handling Writing an Error-Handling Routine Working with Forms and Controls Understanding UserForms Creating a Form Displaying and Removing a Form Aligning and Sizing Controls Using the Toolbox Working with a Form's Properties, Methods, and Events Working with Form and Control Properties, Methods and Event Setting the Tab Order Populating a Control Who is this course for? Who is this course for? This course is designed to give proficiency in the Visual Basic Editor (VBE), predominantly making use of Excel objects, understanding Object's Properties, Events and Methods, basic VBA Object oriented programming, event handling, control structures, and debugging tools. Requirements Requirements Preferably, delegates should have attended the Excel Advanced course. Career path Career path Excel know-how can instantly increase your job prospects as well as your salary. 80 percent of job openings require spreadsheet and word-processing software skills

Brain and Behaviour in Organisations
By Ideas for Leaders
Image Caption Your Master Mentor: Prof Paul Brown Applied neuroscientist, Prof Paul Brown introduces his General Theory on Individuals and Organisations in this ground-breaking program on how to create a 21st century sustainable organisation. Prof Paul Brown briefly introduces the 'Brain and Behaviour in Organisations': Applied neuroscience is going to be the need-to-know basis for anyone interested in human behaviour in organisations. Understanding how the brain is the master controller of everything we do, the role our emotions play in that and the Limbic Leadership qualities we need to adopt to self-regulate ourselves and tune in to those of our team. Course Content In this eight-part program, Prof Brown introduces you to how the brain is actually the central controller of everything we do. And how our increasing knowledge of the neurosciences can help us mobilise that knowledge in organisations. In the program Paul will introduce you to the idea that it is not our Thinking system that drives everything we do but our Emotions. We want to develop an understanding of how to create the relationships where people bring their best to the organisation. We're introduce the London Protocol of the Emotions, a working model of how it all happens. And discuss the differences and benefits of male and female energy. How can you lead and mobilise the best in both men and women in organisations in order to actually get the diversity that male and female brains bring. How can we manage stress and pressure better in the 21st Century Sustainable Organisation. The program looks at the Yerkes -Dodson law which tells us a great deal about how stress impairs performance. But most of all, we want to fascinate and excite interest in you about this remarkable organ that at last, we're beginning to understand join us if you can.

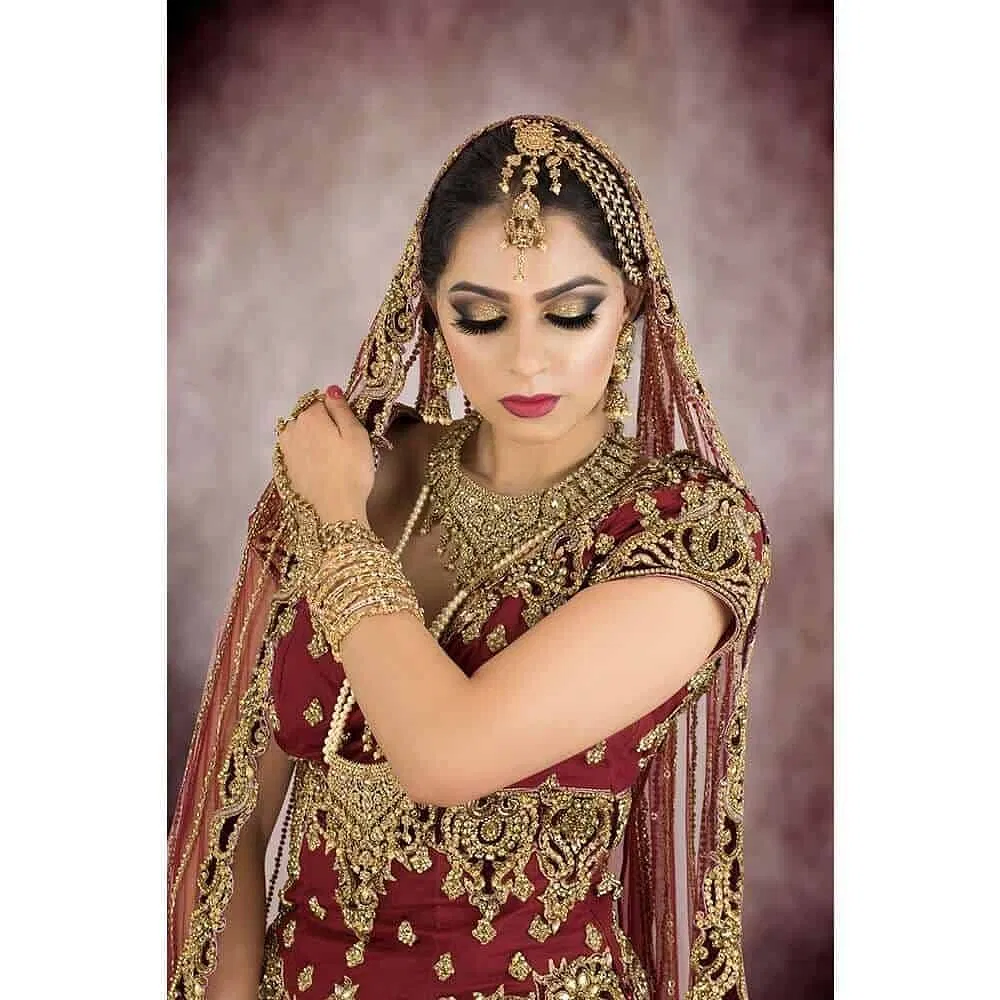
ASIAN BRIDAL HAIRSTYLING and MAKEUP COURSE (8 DAYS) – Accredited, Certified, & Insurable
5.0(48)By Asian Bridal Looks
In this Advanced Bridal Hair and Makeup Course you are taught 20+ Bridal Makeup Looks and 37+ Bridal Hairstyles with scope to creating more than 50 makeup looks and more than 50 hairstyles. This course is suitable for beginners (no experience required) and professionals wishing to update their existing knowledge and skills and add new ones. The course is accredited by the Guild of Beauty Therapists, one of the largest trade bodies in the beauty industry. Accredited certificates help to obtain liability insurance, discounts (upto 35%) from makeup brands, and access to specialised hairstyling products through trade only companies. Whereas, non-accredited courses run by many academies are unable to provide such benefits. Students Work After Course All makeup, hairstyling, jewellery and outfit setting is done solely by the student. Practice Sessions All makeup, false eyelashes, hair pieces, padding, hair products tools and equipment will be provided for students to use during the course in their practice sessions. During this Advanced Bridal Hair and Makeup Course you will be given full details of all products and tools used, both high end and cheaper alternatives. A lot of information is covered therefore students should take suitable notes and photographs to assist in further practice after the course. For the first 4 days you will be practising makeup techniques learnt on the course on a model which you can bring, or one can be provided for you for an extra fee of £60 per day. Training heads / mannequins will be provided for students to use during the hairstyling part of the course. It is not practical to use live models as multiple hairstyles are demonstrated each day and it is necessary to use different hair products and backcombing. Continuous backcombing and application of strong hair products on a live model would cause severe damage to the hair. View Content for Advanced Bridal Course: Day 1, Makeup : Health and Safety including safety practices for covid-19. Importance of using correct PPE. Keeping Products and equipment clean – brush cleaners and makeup sanitisers. Different types of lighting, makeup chairs, additional equipment for speed and efficiency. How to make your business cost effective. Different types of primers for eye makeup and face makeup, and which ones to use according to skin type and skin tone. Different types of foundations. How to assess different skin types and skin tones. How to select the correct eye primer, face primer and foundation. Different makeup removers. Different moisturisers for different skin types. Recommendations for eyeshadow palettes especially for beginners. How to blend eyeshadows seamlessly. How to do eyebrows, ombre, natural, and 3D. Different types of eyebrow products. Different types of eyelashes. How to correctly apply false lashes. Different types of colour correctors, and how to use them. How to highlight and contour. Highlights and contouring products. How to apply blusher. Recommendations for blusher colours for different looks. How to identify different skin undertones to help select correct face and eye products. How to set makeup for lasting results. How to avoid creasing under eyes and around mouth. How to stop lipstick bleeding. Covering dark circles and blemishes. How to apply lipstick including over-lining lips. Different types of lipsticks.x How to do eyeliner including winged eyeliner. How to do smokey eyes. Which brushes to use. Different types of eyeliner and how to preserve gel eyeliner. Traditional Asian Bridal Makeup. How to change soft bridal makeup to bold bridal makeup. Foundation colours required for different ethnicities. How to do Glitter makeup How to apply mascara. Day 2, Makeup : Smokey eye makeup Registry makeup Mehndi makeup Engagement makeup How to transform one makeup look into a completely different makeup look to save time where clients have booked for more than one event on the same day, and time constraints apply. Bold Makeup – how to Smokey Eye Makeup. Spotlight or halo makeup Subtle makeup. Ombre Makeup. Ombre glitter makeup How to apply pigments. How to use or apply liquid foundation. Different tools for different applications. Where to purchase makeup tools and makeup products. How to apply for pro makeup artist discount schemes. Soft cut crease makeup Different types of setting sprays. How to use different highlighting products. How to prevent creasing under the eye and mouth. How to makeup last longer. How to conduct client trials. How to manage bookings. How to avoid scams. How to conduct phone consultations. How to deal with difficult / fussy clients. Must have products for beginners and how to build up your kit. Reverse highlighting and contouring. Colour correction theory. How to use an artist colour wheel to coordinate eyeshadow colours. Customer care. How to use glitter. Day 3, Makeup : How to highlight and contour for different face shapes i.e. corrective highlighting and contouring. How to identify different eye shapes. How to apply makeup for different eye shapes. Advanced foundation makeup technique for flawless bridal makeup. Monolid eye makeup Protruding eye makeup Hooded eye makeup. Downturned eye makeup. How to select the correct style of lashes for different eye shapes. How to make small eyes look bigger. Different lip shapes and how to correct them. Ombre lips. How to make lips look bigger. Arabic makeup Cut crease makeup Double cut crease makeup Floating cut crease makeup Glitter cut crease makeup Day 4, Makeup : Photographic makeup technique. How to make your client look more than 2 tones lighter than their natural skin tone without skin looking grey or ashy. Dos and Don’ts of baking. Sweatproof / waterproof makeup. How to set makeup for hot weather and destination weddings in hot countries such as Dubai, etc. Glass skin technique and products. Nude lipstick for different skin tones. 3D eye makeup How to customise / change foundation colour for different skin tones. Makeup products for dark skin tones Mature ladies makeup techniques and products. Marketing and social media. How to organise your own photoshoots. Advice and tips on photography to showcase your work. European bridal makeup Day 5, Hairstyling : Health and Safety including safety practices for covid-19. Importance of using correct PPE. Advice on purchasing mannequins for further practice after the course. How to wash the mannequins hair and which products to use. How to apply for trade cards for specialist hair products. Must have hair products, high end and cheaper alternatives. Must have tools for hairstyling, high end and cheaper alternatives. What advice to give clients for prepping hair. How to conduct trials. How to prepare and conduct bookings. Customer care. How to avoid customer scams. Phone consultations. Which hair pieces required for different hairstyles and where to purchase. Different types of padding required for different hairstyles. How to make your own padding. Traditional bridal bun. How to create different designs on a bridal bun. How to section hair. How to create a vintage fringe with side parting. How to backcomb correctly. Half up half down. Layered vintage fringe with middle parting. Messy Plait. Low messy / curly bun. How to change one hairstyle into another to save time for clients with multiple bookings. How to pop synthetic hair. Different types of pins. How to secure jewellery where padding has been used in the hairstyle. How to secure the dupatta where padding has been used in the hairstyle. Day 6, Hairstyling : Side bun 1. Side bun 2. Greek braid 1. Greek braid 2. Structured bun. Simple curls (barrel or ringlet). Hollywood waves. How to prep hair. Products required to create different textures for different hairstyles. Textured updo. Messy updo. Textured updo. Messy updo. Textured fringe. How to curl synthetic hair. Mermaid hair. How to make curls last longer. Sleek bun. Sleek low bun. How to secure jewellery when no padding has been used for the hairstyle. How to secure the dupatta when no padding has been used for the hairstyle. Day 7, Hairstyling : French braid. Fishtail braid. Boho pull through braid. Textured plait. How to create extra long plaits for asian brides. Solutions for thinning hair. How to create volume for fine hair and medium thickness hair. Backcombing to create volume. How to apply clip-in hair extensions. Boho frech braid updo. French braid bridal updo. French twist. Textured hairstyle for the and / or short hair. Plaited fringe. Dutch twist braid. Dutch braid. Day 8, Hairstyling : Textured High Bun / Top Knot Low Textured Bun Textured Low Bun with Pulled Lines 3D Curls Half Up Half Down Textured Low Curly Bun Introduction to Russian / textured hairstyling. How to prep Hair for Russian Hairstyles. Products and tools required for Russian Hairstyling. How to create Texture for Russian Hairstyles. How to create lines for Russian Hairstyles. Different types of padding for Russian Hairstyling. Correct way to crimp hair. Correct way to backcomb hair. Optional Day 9, Photoshoot You will receive professionally edited images for your portfolio to kick start your new career. The model, photographer, jewellery and outfit are all provided. The tutor is present to provide guidance with the hairstyle and makeup thus reinforcing all that has been learnt on the course. Photoshoots take place on Tuesdays, Wednesdays, and Thursdays following the end of the hair and makeup course. The Photoshoot is Evidence of the Students Achievement The students portfolio work is strictly the students work only i.e. the student has done all the makeup, all the hairstyle, and all the jewellery and outfit setting by themselves at the end of the course without any physical help from the tutor or anyone from her team. Many other teaching establishments pass off pictures as students work whereas the tutor or helper usually do all the hairstyling, and dupatta and jewellery setting themselves, and the student only does the makeup, and in some instances makeup by the student is done on only half the face, whereas the tutor has done makeup on the other half. The whole point of doing a hair and makeup course should be so that the student can complete total hair and makeup looks by themselves by the end of the course without any further help. Course Benefits The Advanced Bridal Hair and Makeup Course teaches students to confidently style hair and apply makeup on asian, middle eastern and European brides and party guests for different functions. You will learn about hair and makeup products and tools. You will be able to offer your clients different styles of makeup both bold and subtle. You will be taught how to deal with clients with different features and skin tones (including dark skin tones). You are taught advanced bridal makeup techniques on the fourth day of the course. We teach you how to create several hairstyles from one basic foundation. We also show you how to transform one hairstyle into another within minutes. You will learn how to prep different hair textures. Students are taught a huge range of hairstyles including advanced bridal hairstyles. On the eighth day of the course students are taught how to create some Russian hairstyles and the latest textured hairstyles.You will gain a detailed knowledge of techniques and products both high end and cheaper brands. You will be able to start your business as a professional hair and makeup artist without wasting money on unnecessary products and equipment. Successful completion of the course rewards students with 3 accredited certificates: Asian Bridal Makeup, Asian Bridal Hairstyling, and Professional Standards for Therapists. Thus enabling students to apply for makeup discount schemes, and gain access to specialised tools and products from trade only companies for professional hairstylists. This course is designed to maximise the success of your business and earning potential. We teach you not just the current makeup trends and hairstyles but also the types of looks and hairstyles expected to be in demand in the near future. We are probably the only training academy offering students advice and tips on how to create their own portfolio to suit their budget. Fees & Enrolment for Advanced Bridal Course Class Size: All courses are limited to a maximum of 3 students per class. Each student receives plenty of individual attention in all aspects of learning to fully benefit from the course. Course Location: Slough, near Heathrow, Hounslow and Southall. Easily accessible by road (Junction 5 of M4) and train (Slough Station – Elizabeth Line (London Underground) and National Rail (15 minutes from Paddington station, central London)). Course Timings: 10am – 5pm Course Fee: £1595 for 8 Days without photoshoot or £2400 for 9 Days with photoshoot Course Dates are below. If these dates are not suitable then we may be able to accommodate provided we have 1-2 months advance notice, please ask. (Refreshments and lunch is provided free of charge)
BSc (Hons) Early Childhood Studies Top-Up - Inclusive of Level 4 and 5 Pathway Diploma
By School of Business and Technology London
Getting Started The BSc in Early Childhood Studies programme provides a comprehensive education on child development, education, and care. It equips students with the knowledge and skills necessary to work effectively with young children and their families in various educational and childcare settings. This programme establishes a strong foundation for early childhood education and advocacy careers. The BSc (Hons) Early Childhood Studies programme delivers a dynamic educational experience for students aspiring to engage in early childhood education and development. This undergraduate degree programme strongly emphasises comprehending the critical stages of early childhood, spanning from infancy to primary school age. It delves into the multitude of factors that influence a child's growth and learning. Throughout the programme, students are exposed to a wide array of topics, including child psychology, early education pedagogy, child health and well-being, and the socio-cultural influences on early childhood development. The curriculum is thoughtfully crafted to nurture a deep understanding of the unique needs and challenges faced by young children and their families, equipping graduates with the knowledge and skills necessary to impact the field positively. Anglia Ruskin University's BSc (Hons) Early Childhood Studies programme offers a supportive learning environment with experienced faculty and access to cutting-edge research. Graduates from this programme are well-prepared for a diverse range of career opportunities in early childhood education, social services, child advocacy, and more. It serves as a solid foundation for individuals passionate about nurturing and shaping the future of our youngest learners. The programme comprises two phases; the first is the Qualifi Level 4 and 5 Diploma in Early Learning and Childcare, awarded by Qualifi and delivered by the School of Business and Technology London. The second phase is the BSc (Hons) in Early Childhood Studies Top Up, awarded and delivered 100% online by Anglia Ruskin University. At Anglia Ruskin University, you will study through Canvas, a world-class online Learning Management System (LMS), accessed from your phone, pc or tablet at home or on the move. Canvas provides instant access to study materials, forums, and support from tutors and classmates, as well as enabling easy submission of your assignments. After successfully completing your studies, you'll be invited to attend a graduation ceremony on campus at Anglia Ruskin University. If attending the ceremony in person is not possible, we'll arrange to send your certificate to you. School of Business and Technology London partners with Chestnut Education Group to promote this programme. About Awarding Body Anglia Ruskin University began in 1858 as the Cambridge School of Art founded by William Beaumont. It was then merged with the Cambridge shire College of Arts and Technology and the Essex Institute of Higher Education and was renamed Anglia Polytechnic. It was then given university status in 1992 and renamed Anglia Ruskin University in 2005. The university has campuses in the UK (Cambridge, Chelmsford, London and Peterborough), as well as they are partnered with institutions around the world including Berlin, Budapest, Trinidad, Singapore and Kuala Lumpur. Assessment Assignments and Project No examinations Entry Requirements A Level or Equivalent Minimum 1 Year of experience in Early Learning and Childcare. Further, candidates are also required to demonstrate their English language proficiency. Learners must request before enrolment to interchange unit(s) other than the preselected units shown in the SBTL website because we need to make sure the availability of learning materials for the requested unit(s). SBTL will reject an application if the learning materials for the requested interchange unit(s) are unavailable. Learners are not allowed to make any request to interchange unit(s) once enrolment is complete. Structure Phase 1 - Qualifi Level 4 and 5 Diploma in Early Learning and Childcare Programme structure Level 4 The Qualifi Level 4 Diploma in Early Learning and Childcare comprises 9 units. To obtain the Diploma, learners must complete all mandatory units, earning 34 credits. Additionally, they should select at least 6 credits from the optional units. A total of 40 credits is necessary for Diploma completion, along with at least 30 hours of teaching practice. Mandatory units: Child development and enabling children to learn Reference No: J/650/0974 Credit: 9 || TQT: 90 This unit aims to equip learners with a comprehensive understanding of diverse early years pedagogical approaches influencing holistic learning in babies and children aged from birth to five years. It delves into local statutory planning and monitoring requisites. Learners will also explore leadership, mentoring, and managerial skills. The unit emphasises comprehending how babies and young children learn and translating theory into practical application. Additionally, it examines developmental disparities, the potential for developmental delays, the impacts of transitions, and how children learn in various environments. It empowers learners with proficiency in utilising observation, Assessment, and planning to foster children's development. To demonstrate their assimilated knowledge, learners must integrate it into their day-to-day responsibilities with children aged from birth to five years and document practice modifications in their setting via a portfolio. Physical activity and nutrition co-ordination (PANCo) in early years Reference No: K/650/0975 Credit: 6 || TQT: 60 In this unit, learners will grasp the advantages of physical activity and the significance of a balanced diet for the health and well-being of babies, children, and their families. They should consider statutory framework mandates and national, local, and international initiatives, advice, and perspectives relevant to health and well-being. Supporting children with additional needs Reference No: J/650/0992 Credit: 4 || TQT: 40 This unit endeavours to enhance the leadership and management capabilities of the Special Educational Needs Coordinator (SENCO) in effectively guiding best practices for children with Special Educational Needs and Disabilities (SEND) and their families. Partnership working in early years settings Reference No: L/650/0976 Credit: 6 || TQT: 60 This unit seeks to assist learners in comprehending the legal obligations associated with collaborating with families. It emphasises the positive impact of effective partnerships with other professionals on the well-being and development of babies and children. Learners will also delve into the varied needs of families and strategise ways to surmount potential obstacles to successful partnership working. Implementing and evaluating change through a research project Reference No: M/650/0977 Credit: 6 || TQT: 60 This unit mandates learners to devise, execute, and assess change about a chosen theme, accomplished through a modest research endeavour. Learners will also grasp the ethical considerations integral to research. The chosen theme, subject to agreement with the assessor, enables learners to introspect on their practices, employ current research to propose enhancements within their setting, put these proposals into action, and report on their outcomes. Legal requirements in Childcare Reference No: R/650/0978 Credit: 3 || TQT: 30 This unit encompasses the necessary knowledge and understanding regarding health and safety, equality and inclusion, the Welfare Requirements of the Early Years Foundation Stage, Employment Rights, and Special Educational Needs, including Looked Children. It also addresses the preparations for Ofsted inspections, the formulation of policies and procedures, and the utilisation of information to oversee the quality of the setting's practices. Optional Units Assessing and planning for children's changing developmental needs Reference No: T/650/0979 Credit: 6 || TQT: 60 This unit's objective is to equip learners with the knowledge, comprehension, and skills required to conduct observations for assessing and planning for children's evolving developmental needs over an extended duration, commonly referred to as a longitudinal study. The study is to be conducted over six months. Caring for babies Reference No: D/650/0980 Credit: 6 || TQT: 60 This unit fosters the knowledge, understanding, and skills necessary to care for infants aged 0-18 months. Caring for children through play out of school Reference No: F/650/0981 Credit: 6 || TQT: 60 This unit aims to cultivate the knowledge, understanding, and skills required to provide care for children and young people outside of regular school hours and during school holidays. Level 5 The Qualifi Level 5 Diploma in Early Learning and Childcare comprises 10 units. To attain the diploma, learners must finish all mandatory units for 96 credits. Additionally, they must select a minimum of 24 credits from optional units. In total, a minimum of 120 credits must be achieved, along with 100 hours of teaching practice. Mandatory units: Management of children's care Reference No: H/650/0982 Credit: 20 || TQT: 200 This unit aims to provide learners comprehensive knowledge and comprehension of theories, principles, and models pertinent to early learning and childcare. Learners will apply these concepts, deepening their grasp of communication and Assessment in this context. The unit will additionally encompass the utilisation of theories and models for specialised curriculum development and the application of theories and models for reflective practice. Children's well-being and resilience Reference No: J/650/0983 Credit: 26 || TQT: 260 This unit strives to equip learners with the knowledge, understanding, and skills essential for comprehending and nurturing children's well-being and resilience. This encompasses appreciating each child as an individual and ensuring inclusive treatment for all. Positive behaviour in early years Reference No: K/650/0984 Credit: 20 || TQT: 200 This unit's objective is to give learners the necessary knowledge, understanding, and skills for formulating and executing strategies and policies to promote positive behaviour in children. Child development and communication skills in early years Reference No: L/650/0985 Credit: 30 || TQT: 300 This unit aims to enhance learners' comprehension of the anticipated trajectory of children's development and the factors that impact it. Specifically, it seeks to deepen learners' understanding of how children's communication skills progress from birth to 7 years old. OPTIONAL UNITS Managing children's holistic development in early years Reference No: M/650/0986 Credit: 16 || TQT: 160 The goal of this unit is to enable learners to effectively strategise and oversee the comprehensive development of children, tailored to their specific requirements. Learners will assess strategies for enhancing literacy and numeracy and implement theoretical approaches in their professional practice. Developing children's literacy skills Reference No: R/650/0987 Credit: 16 || TQT: 160 This unit aims to empower learners to foster children's literacy skills. Developing children's mathematical skills Reference No: T/650/0988 Credit: 8 || TQT: 80 This unit aims to enable learners to enhance children's mathematical skills. Safeguarding in early years Reference No: Y/650/0989 Credit: 16 || TQT: 160 This unit aims to cultivate learners' comprehension of the role and extent of safeguarding in early years education and the policies and procedures for enacting safeguarding protocols. Health and safety in the early years Reference No: F/650/0990 Credit: 8 || TQT: 80 This unit aims to foster learners' knowledge and comprehension of the early years education's pertinent health and safety prerequisites. It further aims to equip them with the capability to implement policies and processes related to health and safety. Special Educational Needs and Disability (SEND) in early years Reference No: H/650/0991 Credit: 8 || TQT: 80 This unit seeks to enhance the learner's knowledge and comprehension of the legislation about children with Special Educational Needs and Disabilities (SEND) and the measures in place to address additional needs in early years education. Phase 2 - BSc (Hons) in Early Childhood Studies Programme structure Early Childhood Leadership and Management Children's Rights Interdisciplinary Perspectives Leading Change in Early Childhood Contexts Early Childhood Graduate Competencies Undergraduate Major Project Delivery Methods The programme comprises two phases; the first is the Qualifi Level 4 and 5 Diploma in Early Learning and Childcare, awarded by Qualifi and delivered by the School of Business and Technology London. The School of Business and Technology London offers flexible learning methods, including online and blended learning, allowing students to choose the mode of study that suits their preferences and schedules. The programme is self-paced and facilitated through an advanced Learning Management System. Students can easily interact with tutors through the SBTL Support Desk Portal System for course material discussions, guidance, assistance, and assessment feedback on assignments. School of Business and Technology London provides exceptional support and infrastructure for online and blended learning. Students benefit from dedicated tutors who guide and support them throughout their learning journey, ensuring a high level of assistance. The second phase is the BSc (Hons) in Early Childhood Studies Top Up, awarded and delivered 100% online by Anglia Ruskin University. At Anglia Ruskin University, you will study through Canvas, a world-class online Learning Management System (LMS), accessed from your phone, pc or tablet at home or on the move. Canvas provides instant access to study materials, forums, and support from tutors and classmates, as well as enabling easy submission of your assignments. After successfully completing your studies, you'll be invited to attend a graduation ceremony on campus at Anglia Ruskin University. If attending the ceremony in person is not possible, we'll arrange to send your certificate to you. School of Business and Technology London partners with Chestnut Education Group to promote this programme. Resources and Support School of Business & Technology London is dedicated to offering excellent support on every step of your learning journey. School of Business & Technology London occupies a centralised tutor support desk portal. Our support team liaises with both tutors and learners to provide guidance, assessment feedback, and any other study support adequately and promptly. Once a learner raises a support request through the support desk portal (Be it for guidance, assessment feedback or any additional assistance), one of the support team members assign the relevant to request to an allocated tutor. As soon as the support receives a response from the allocated tutor, it will be made available to the learner in the portal. The support desk system is in place to assist the learners adequately and streamline all the support processes efficiently. Quality learning materials made by industry experts is a significant competitive edge of the School of Business & Technology London. Quality learning materials comprised of structured lecture notes, study guides, practical applications which includes real-world examples, and case studies that will enable you to apply your knowledge. Learning materials are provided in one of the three formats, such as PDF, PowerPoint, or Interactive Text Content on the learning portal. How does the Online Learning work at SBTL? We at SBTL follow a unique approach which differentiates us from other institutions. Indeed, we have taken distance education to a new phase where the support level is incredibly high.Now a days, convenience, flexibility and user-friendliness outweigh demands. Today, the transition from traditional classroom-based learning to online platforms is a significant result of these specifications. In this context, a crucial role played by online learning by leveraging the opportunities for convenience and easier access. It benefits the people who want to enhance their career, life and education in parallel streams. SBTL's simplified online learning facilitates an individual to progress towards the accomplishment of higher career growth without stress and dilemmas. How will you study online? With the School of Business & Technology London, you can study wherever you are. You finish your program with the utmost flexibility. You will be provided with comprehensive tutor support online through SBTL Support Desk portal. How will I get tutor support online? School of Business & Technology London occupies a centralised tutor support desk portal, through which our support team liaise with both tutors and learners to provide guidance, assessment feedback, and any other study support adequately and promptly. Once a learner raises a support request through the support desk portal (Be it for guidance, assessment feedback or any additional assistance), one of the support team members assign the relevant to request to an allocated tutor. As soon as the support receive a response from the allocated tutor, it will be made available to the learner in the portal. The support desk system is in place to assist the learners adequately and to streamline all the support process efficiently. Learners should expect to receive a response on queries like guidance and assistance within 1 - 2 working days. However, if the support request is for assessment feedback, learners will receive the reply with feedback as per the time frame outlined in the Assessment Feedback Policy.

MSc Project Management Top-Up- Inclusive of Level 7 Pathway Diploma
By School of Business and Technology London
Getting Started The MSc Project Management programme is designed to show people from any discipline or degree how to manage projects. This program aims to identify, develop and perform essential skills and techniques needed for expertise in Project Management. The programme focuses on enhancing graduate and practicing engineers' knowledge and skills in relevant management skills, principles, and procedures. This course equips students with the skills and knowledge necessary to contribute to project management research significantly. The programme comprises two phases; the first is the Qualifi Level 7 Diploma in Business Strategy, awarded by Qualifi and delivered by the School of Business and Technology London. The second phase is the MSc Project Management Top-Up, awarded and delivered 100% online by Anglia Ruskin University. At Anglia Ruskin University, you will study through Canvas, a world-class online Learning Management System (LMS), accessed from your phone, pc or tablet at home or on the move. Canvas provides instant access to study materials, forums, and support from tutors and classmates, as well as enabling easy submission of your assignments. After successfully completing your studies, you'll be invited to attend a graduation ceremony on campus at Anglia Ruskin University. If attending the ceremony in person is not possible, we'll arrange to send your certificate to you. School of Business and Technology London partners with Chestnut Education Group to promote this programme. About Awarding Body Anglia Ruskin University began in 1858 as the Cambridge School of Art founded by William Beaumont. It was then merged with the Cambridge shire College of Arts and Technology and the Essex Institute of Higher Education and was renamed Anglia Polytechnic. It was then given university status in 1992 and renamed Anglia Ruskin University in 2005. The university has campuses in the UK (Cambridge, Chelmsford, London and Peterborough), as well as they are partnered with institutions around the world including Berlin, Budapest, Trinidad, Singapore and Kuala Lumpur. Assessment Assignments and Project No examinations Entry Requirements A bachelor's degree Applicant without a bachelor's degree but holding significant managerial experience will be considered for entry on a case-by-case basis. Further, candidates are also required to demonstrate their English language proficiency. Learners must request before enrolment to interchange unit(s) other than the preselected units shown in the SBTL website because we need to make sure the availability of learning materials for the requested unit(s). SBTL will reject an application if the learning materials for the requested interchange unit(s) are unavailable. Learners are not allowed to make any request to interchange unit(s) once enrolment is complete. Structure Phase 1 - Qualifi Level 7 Diploma in Business Strategy Programme Structure Mandatory Units Unit 703: Strategic Marketing Unit code: M/506/9074 TQT :150 Credit :15 This unit will explore the fundamental models, techniques, and theories that form the marketing foundation and can contribute to achieving strategic objectives. Additionally, it will impart learners with a critical comprehension of the marketing function within intricate organizations. Unit 704: Finance for Managers Unit code: D/506/9071 TQT :150 Credit :15 The focus of this unit is to assist learners in comprehending and effectively utilizing financial information and data. This unit holds significance for learners as it underpins informed decision-making. Unit 705: Strategic Direction Unit code: D/506/9068 TQT :150 Credit :15 This unit will delve into an organization's strategic aims and objectives, emphasizing their importance in establishing direction and gauging success and progress. Furthermore, the unit will examine how various strategic options may prompt the organization to alter its course. Unit 706: Strategic Planning Unit code: Y/506/9070 TQT :150 Credit :15 This unit focuses on the importance of the strategic planning process in crafting suitable strategies and creating a plan that garners support from stakeholders and other organizational leaders. Additionally, the unit addresses the critical evaluation of the program and its subsequent success. Unit 707: Creative and Innovative Management Unit code: H/618/0795 TQT :150 Credit :15 This unit equips the learner with the knowledge to acknowledge the significance of creative and innovative management concepts for organizations, as well as the skills to put this understanding into practice effectively. Unit 708: Managing Corporate Responsibility in the Wider Business Environment Unit code: K/618/0796 TQT :100 Credit :10 This unit offers the learner insight into how legislation and global integration impact the decisions, policies, processes, and activities carried out by organizations. Specialism Units GENERAL MANAGEMENT SPECIALISM Unit 701: Research Method Unit code: Y/506/9133 TQT :200 Credit :20 The objective of this unit is to enhance the learner's knowledge and comprehension of academic practices and research methodologies. It employs a problem-based learning approach to cultivate practical proficiency in areas relevant to educational practice and research within business and management. Unit 702: Development as a Strategic Manager Unit code: J/506/9064 TQT :150 Credit :15 This unit seeks to foster organizational and self-awareness in learners. It establishes the groundwork for a self-critical and reflective approach to personal development, which is crucial for learners operating at a strategic level. Additionally, it considers broader organizational and environmental factors, recognizing their role as contributors to the overall strategic success of both the individual and the organization. HUMAN RESOURCES MANAGEMENT SPECIALISM Unit 709: Contemporary Human Resource Management Unit code: Y/615/3304 TQT :100 Credit :10 The objective of this unit is to empower learners with the capacity to comprehend and assess the influence of internal and external environmental factors on organizational strategy and people management. Additionally, it aims to enable the learner to analyze various organizational contexts and devise strategies to address these ecological forces while recognizing the role of HR professionals in contributing to this process. Unit 710: Resourcing, Talent Management and Development Unit code: K/615/3307 TQT :150 Credit :15 This unit aims to cultivate proficiency in comprehending and analyzing employment markets and demographic trends to devise and execute effective, ethical, and fitting strategies for resourcing, retention, talent management, and development. Additionally, it will explore the potential and constraints of learning and talent development policies and procedures in shaping and attaining objectives at the national, organizational, group, and individual levels. Learners will evaluate the pivotal role of HRM professionals in formulating, implementing, and assessing strategic planning pertinent to employee resourcing, talent management, and development. Unit 711: Performance Management Unit code: M/615/3308 TQT :100 Credit :10 The objective of this unit is to empower learners with the knowledge to grasp the key factors that impact employee performance across all levels within an organisation and how these factors can be effectively managed. Additionally, it aims to equip learners with the understanding to create and execute suitable HR practices and strategies aligned with Performance Management. FINANCE SPECIALISM Unit 712: Business Finance Unit code: R/618/8634 TQT :100 Credit :10 This unit seeks to enhance students' knowledge and comprehension of management accounting techniques tailored for small businesses. It also introduces students to applying management accounting information in effectively managing small companies through planning, organizing, executing, and controlling activities. Unit 713: International Financial Management Unit code: Y/618/8635 TQT :150 Credit :15 This module fosters students' comprehension and expertise in investments beyond national boundaries. It delves into matters that transcend domestic economies, encompassing the handling of foreign currencies and addressing international economic and cultural disparities. As a result, this module provides students with the skills needed to navigate the intricate realm of international finance. Unit 709: Contemporary Human Resource Management Unit code: Y/615/3304 TQT :100 Credit :10 The objective of this unit is to empower learners with the capacity to comprehend and assess the influence of internal and external environmental factors on organizational strategy and people management. Additionally, it aims to enable the learner to analyze various organizational contexts and devise strategies to address these ecological forces while recognizing the role of HR professionals in contributing to this process. MARKETING SPECIALISM Unit 714: Customer Growth Marketing Unit code: D/618/8636 TQT :100 Credit :10 The primary objective of this module is to conduct a critical examination of the tools and methods employed to achieve successful customer growth across various contexts. Through this, students will cultivate an essential grasp of the factors that shape consumer behaviour and assess relevant literature and theories elucidating consumer motivation and customer relationships. Additionally, students will be able to scrutinize an organization's marketing strategy and showcase the implementation of crucial concepts, elements, and tools within the business environment. Unit 715: Advanced Strategic Marketing Unit code: H/618/8637 TQT :150 Credit :15 The Marketing Strategy module builds upon the pre-existing knowledge that students and practitioners have regarding marketing principles. It aims to empower candidates to suggest strategic approaches to emerging market trends. It encourages them to contemplate the repercussions of marketing and its interplay with other facets of the organization. Unit 709: Contemporary Human Resource Management Unit code: Y/615/3304 TQT :100 Credit :10 The objective of this unit is to empower learners with the capacity to comprehend and assess the influence of internal and external environmental factors on organizational strategy and people management. Additionally, it aims to enable the learner to analyze various organizational contexts and devise strategies to address these ecological forces while recognizing the role of HR professionals in contributing to this process. PROJECT MANAGEMENT SPECIALISM Unit 716: Planning, Controlling and Leading a Project Unit code: K/618/8638 TQT :150 Credit :15 This unit is designed to acquaint learners with the practical aspects of initiating and overseeing a project. Additionally, it will familiarize them with the unique challenges of project management in the global business landscape. The unit encourages critical thinking about project management, viewing it as a complex, process-driven cultural system that is continually evolving through the collaborative efforts of high-performing teams. With an increasing number of firms engaging in project development and management activities, acquiring a sound understanding of efficient project management becomes crucial. Learners will delve into the roles and responsibilities of project team members and examine various levels of management skills, placing special emphasis on success factors, monitoring, and control. Unit 717: Procurement Risk and Contract Management Unit code: M/618/8639 TQT :100 Credit :10 The objective of this unit is to empower students with a comprehensive understanding of the fundamental principles of procurement. It emphasizes the significance of recognizing and mitigating risks associated with procurement and contract management. Additionally, learners will cultivate a critical appreciation for the various legislative frameworks that play a crucial role in procurement and explore frameworks for assessing risks within the procurement context. Unit 718: Advanced Project and Logistics Management Unit code: H/618/8640 TQT :100 Credit :10 The goal of this unit is to enable the learner to grasp the concepts of portfolio management and its related characteristics. It will also delve into the significance of having a Project Management Office, exploring the stages of establishing an effective PMO. Additionally, learners will assess the supply chain ecosystem and evaluate IT frameworks suitable for managing the complexities of logistics and the supply chain. Phase 2 - MSc Project Management Top-Up Programme Structure Project Management Systems Project Management Techniques Dissertation (Major Project) Delivery Methods The programme comprises two phases; the first is the Qualifi Level 7 Diploma in Business Strategy, awarded by Qualifi and delivered by the School of Business and Technology London. The School of Business and Technology London offers flexible learning methods, including online and blended learning, allowing students to choose the mode of study that suits their preferences and schedules. The program is self-paced and facilitated through an advanced Learning Management System. Students can easily interact with tutors through the SBTL Support Desk Portal System for course material discussions, guidance, assistance, and assessment feedback on assignments. School of Business and Technology London provides exceptional support and infrastructure for online and blended learning. Students benefit from dedicated tutors who guide and support them throughout their learning journey, ensuring a high level of assistance. The second phase is the MSc Project Management Top-Up, awarded and delivered 100% online by Anglia Ruskin University. At Anglia Ruskin University, you will study through Canvas, a world-class online Learning Management System (LMS), accessed from your phone, pc or tablet at home or on the move. Canvas provides instant access to study materials, forums, and support from tutors and classmates, as well as enabling easy submission of your assignments. After successfully completing your studies, you'll be invited to attend a graduation ceremony on campus at Anglia Ruskin University. If attending the ceremony in person is not possible, we'll arrange to send your certificate to you. School of Business and Technology London partners with Chestnut Education Group to promote this programme. Resources and Support School of Business & Technology London is dedicated to offering excellent support on every step of your learning journey. School of Business & Technology London occupies a centralised tutor support desk portal. Our support team liaises with both tutors and learners to provide guidance, assessment feedback, and any other study support adequately and promptly. Once a learner raises a support request through the support desk portal (Be it for guidance, assessment feedback or any additional assistance), one of the support team members assign the relevant to request to an allocated tutor. As soon as the support receives a response from the allocated tutor, it will be made available to the learner in the portal. The support desk system is in place to assist the learners adequately and streamline all the support processes efficiently. Quality learning materials made by industry experts is a significant competitive edge of the School of Business & Technology London. Quality learning materials comprised of structured lecture notes, study guides, practical applications which includes real-world examples, and case studies that will enable you to apply your knowledge. Learning materials are provided in one of the three formats, such as PDF, PowerPoint, or Interactive Text Content on the learning portal. How does the Online Learning work at SBTL? We at SBTL follow a unique approach which differentiates us from other institutions. Indeed, we have taken distance education to a new phase where the support level is incredibly high.Now a days, convenience, flexibility and user-friendliness outweigh demands. Today, the transition from traditional classroom-based learning to online platforms is a significant result of these specifications. In this context, a crucial role played by online learning by leveraging the opportunities for convenience and easier access. It benefits the people who want to enhance their career, life and education in parallel streams. SBTL's simplified online learning facilitates an individual to progress towards the accomplishment of higher career growth without stress and dilemmas. How will you study online? With the School of Business & Technology London, you can study wherever you are. You finish your program with the utmost flexibility. You will be provided with comprehensive tutor support online through SBTL Support Desk portal. How will I get tutor support online? School of Business & Technology London occupies a centralised tutor support desk portal, through which our support team liaise with both tutors and learners to provide guidance, assessment feedback, and any other study support adequately and promptly. Once a learner raises a support request through the support desk portal (Be it for guidance, assessment feedback or any additional assistance), one of the support team members assign the relevant to request to an allocated tutor. As soon as the support receive a response from the allocated tutor, it will be made available to the learner in the portal. The support desk system is in place to assist the learners adequately and to streamline all the support process efficiently. Learners should expect to receive a response on queries like guidance and assistance within 1 - 2 working days. However, if the support request is for assessment feedback, learners will receive the reply with feedback as per the time frame outlined in the Assessment Feedback Policy.

Master of Laws (LLM) Top-Up
By School of Business and Technology London
Getting Started The University of Lancashire offers a comprehensive Master of Laws (LLM) Top-Up programme meticulously designed to provide a deep and specialised legal education. Renowned for its rigorous curriculum and distinguished faculty, this programme is the preferred choice for experienced professionals and aspiring lawyers seeking to enhance their expertise. Law is a fast-changing and increasingly complex area impacting most professional, commercial and regulatory work aspects. You also don't need a legal background to study the (LLM) Master of Laws. The programme is designed for professionals seeking to expand their knowledge and advance their careers. You'll critically evaluate areas of law and the way they operate in the domestic, European, and international contexts. Through your dissertation, you'll develop critical analytical and research skills that will serve you well in any legal setting. The extensive e-law library facility of UCLAN offers you access to many legal and academic sources from within and outside the jurisdiction, providing you with the resources you need to succeed in your studies. Additionally, you'll be able to enhance your employability skills by gaining additional qualifications in alternative dispute resolution, specifically international arbitration and mediation. With a graduation ceremony held on campus grounds, you'll have the opportunity to celebrate your achievements with your peers, professors, and family members. Don't miss out on this exciting opportunity to take your legal career to the next level. The Master of Laws (LLM) Top-Up, awarded and delivered by the University of Central Lancashire through distance learning. School of Business and Technology London partners with Chestnut Education Group to promote this programme. About Awarding Body Founded in 1828, the University of Central Lancashire is a public university based in Preston, Lancashire, England. Today, UCLAN is one of the largest in the United Kingdom, with a student and staff community of nearly 38,000. At present, the University has academic partners in all regions of the globe, and it is on a world stage that the first-class quality of its education was first recognised. In 2010, UCLAN became the first UK modern Higher Education institution to appear in the QS World University Rankings. In 2018, the Centre for World University Rankings estimated Central Lancashire to be in the top 3.7 per cent of all global universities, highlighting the growth the University has made in offering students real-world learning experiences and reflecting the University's extensive pool of academic talent. Ranked in the top 7% of universities worldwide. Student Communities from more than 100 countries WES Recognised Qualifi is a UK Government (Ofqual.gov.uk) regulated awarding organisation and has developed a reputation for supporting relevant skills in a range of job roles and industries, including Leadership, Enterprise and Management, Hospitality and catering, Health and Social Care, Business Process Outsourcing and Public Services. Qualifi is also a signatory to BIS international commitments of quality. The following are the key facts about Qualifi. Regulated by Ofqual.gov.uk World Education Services (WES) Recognised Assessment Major Project No examinations Entry Requirements Level 7 Postgraduate Diploma in Law or equivalent Aspiring candidates who do not fulfil the above criterion but have sufficient managerial experience can undergo evaluation for an Advanced Entry. If English is not your first language, you will be expected to demonstrate a certificated level of proficiency of at least IELTS 6.5 (Academic level) or equivalent English Language qualification. Learners must request before enrolment to interchange unit(s) other than the preselected units shown in the SBTL website because we need to make sure the availability of learning materials for the requested unit(s). SBTL will reject an application if the learning materials for the requested interchange unit(s) are unavailable. Learners are not allowed to make any request to interchange unit(s) once enrolment is complete. Structure Master of Laws (LLM) Top-Up Programme Structure Dissertation Module Delivery Methods The Master of Laws (LLM) Top-Up, awarded and delivered by the University of Central Lancashire through distance learning. The University of Central Lancashire (UCLan) offers a range of distance learning options for students who require the flexibility to study remotely. These options include online courses, blended learning, and supported distance learning. UCLan's distance learning courses are designed to provide students with the same high-quality education as on-campus courses, with access to resources such as video lectures, online discussion forums, and interactive assessments. The University also provides a range of support services for distance learning students, including academic support, technical support, and access to the University's library and online resources. Resources and Support School of Business & Technology London is dedicated to offering excellent support on every step of your learning journey. School of Business & Technology London occupies a centralised tutor support desk portal. Our support team liaises with both tutors and learners to provide guidance, assessment feedback, and any other study support adequately and promptly. Once a learner raises a support request through the support desk portal (Be it for guidance, assessment feedback or any additional assistance), one of the support team members assign the relevant to request to an allocated tutor. As soon as the support receives a response from the allocated tutor, it will be made available to the learner in the portal. The support desk system is in place to assist the learners adequately and streamline all the support processes efficiently. Quality learning materials made by industry experts is a significant competitive edge of the School of Business & Technology London. Quality learning materials comprised of structured lecture notes, study guides, practical applications which includes real-world examples, and case studies that will enable you to apply your knowledge. Learning materials are provided in one of the three formats, such as PDF, PowerPoint, or Interactive Text Content on the learning portal. How does the Online Learning work at SBTL? We at SBTL follow a unique approach which differentiates us from other institutions. Indeed, we have taken distance education to a new phase where the support level is incredibly high.Now a days, convenience, flexibility and user-friendliness outweigh demands. Today, the transition from traditional classroom-based learning to online platforms is a significant result of these specifications. In this context, a crucial role played by online learning by leveraging the opportunities for convenience and easier access. It benefits the people who want to enhance their career, life and education in parallel streams. SBTL's simplified online learning facilitates an individual to progress towards the accomplishment of higher career growth without stress and dilemmas. How will you study online? With the School of Business & Technology London, you can study wherever you are. You finish your program with the utmost flexibility. You will be provided with comprehensive tutor support online through SBTL Support Desk portal. How will I get tutor support online? School of Business & Technology London occupies a centralised tutor support desk portal, through which our support team liaise with both tutors and learners to provide guidance, assessment feedback, and any other study support adequately and promptly. Once a learner raises a support request through the support desk portal (Be it for guidance, assessment feedback or any additional assistance), one of the support team members assign the relevant to request to an allocated tutor. As soon as the support receive a response from the allocated tutor, it will be made available to the learner in the portal. The support desk system is in place to assist the learners adequately and to streamline all the support process efficiently. Learners should expect to receive a response on queries like guidance and assistance within 1 - 2 working days. However, if the support request is for assessment feedback, learners will receive the reply with feedback as per the time frame outlined in the Assessment Feedback Policy.

“Music is the movement of sound to reach the soul for the education of its virtue.” - Plato Our Singing and Audition Masterclass is one of the highlights of the Academy, and an incredible learning opportunity for anyone looking to improve their singing, get started in musical theatre, and perfect audition pieces in order to start attending casting calls or applying to drama schools. The 2-day Masterclass is taught by two amazing tutors: Kath Harman - Kath studied Professional Dance and Musical Theatre at the Urdang Academy in London, and her career highlights include performing with Dua Lipa at the Brit Awards, and travelling the world with Carnival Cruise Line. Emma Hatton - Emma graduated from LSMT and her big break came in 2009 when she made her West End debut - originating the role of Donna in Dreamboats and Petticoats. Following this triumph, she was cast in We Will Rock You as an understudy for the roles of Scarmouche and Meat. Emma has also played Elphaba in Wicked and has a variety of other on-stage credits. Whatever your experience level, this brilliant course will help you break out of your comfort zone in a supportive environment and walk away with an audition toolkit that you can use to start applying to further education or working in the industry. If you have questions about how industry auditions work, Kath and Emma can demystify the process! While the focus of this course is musical theatre, you can choose to work on songs outside of this genre if you like. Please note: Prior to starting the course, we ask all students to submit two songs they would like to work on to In2Drama's Musical Associate Simon Fraser, who will accompany you on piano during the course. If you’re unsure what songs to pick, don’t worry! Reach out to us at admin@in2drama.com when you make your booking and we can help you choose the best songs for your voice and audition goals. HEADSHOTS AND SHOWREELS While taking part in this masterclass, you will have the chance to purchase optional headshots and a showreel to showcase your talents. Our team will help you capture the very best bits of your performances and a brilliant headshot that you can use to apply for future castings and opportunities. When booking the Summer Academy, you can add a showreel to your booking if you choose. WHEN AND WHERE? The Singing and Audition Masterclass takes place in Cranleigh Arts Centre, around 20 minutes from Guildford. The venue has a professional theatre, a sprung dance floor for choreography sessions, dressing rooms, and lots of great areas for filming and multimedia activities, so it's the perfect spot for our aspiring performers to learn in. Thursday 25th - Friday 26th July 2024 In2Drama is split into two groups for age related focus 11-15 year olds: 9am - 12pm 16-21 year olds: 1pm - 4pm Presentation: 4.30pm - 5pm

Ofqual Regulated Level 5 TEFL Course
By Westminster College London
Study Ofqual Regulated Level 5 TEFL Course online in your own pace and receive an internationally recognised qualification.

Search By Location
- london Courses in London
- london Courses in Birmingham
- london Courses in Glasgow
- london Courses in Liverpool
- london Courses in Bristol
- london Courses in Manchester
- london Courses in Sheffield
- london Courses in Leeds
- london Courses in Edinburgh
- london Courses in Leicester
- london Courses in Coventry
- london Courses in Bradford
- london Courses in Cardiff
- london Courses in Belfast
- london Courses in Nottingham

