- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
3114 Management courses in King's Lynn delivered Live Online
CompTIA Data+
By Nexus Human
Duration 5 Days 30 CPD hours Overview Mining data Manipulating data Visualizing and reporting data Applying basic statistical methods Analyzing complex datasets while adhering to governance and quality standards throughout the entire data life cycle CompTIA Data+ is an early-career data analytics certification for professionals tasked with developing and promoting data-driven business decision-making. CompTIA Data+ gives you the confidence to bring data analysis to life. As the importance for data analytics grows, more job roles are required to set context and better communicate vital business intelligence. Collecting, analyzing, and reporting on data can drive priorities and lead business decision-making. 1 - Identifying Basic Concepts of Data Schemas Identify Relational and Non-Relational Databases Understand the Way We Use Tables, Primary Keys, and Normalization 2 - Understanding Different Data Systems Describe Types of Data Processing and Storage Systems Explain How Data Changes 3 - Understanding Types and Characteristics of Data Understand Types of Data Break Down the Field Data Types 4 - Comparing and Contrasting Different Data Structures, Formats, and Markup Languages Differentiate between Structured Data and Unstructured Data Recognize Different File Formats Understand the Different Code Languages Used for Data 5 - Explaining Data Integration and Collection Methods Understand the Processes of Extracting, Transforming, and Loading Data Explain API/Web Scraping and Other Collection Methods Collect and Use Public and Publicly-Available Data Use and Collect Survey Data 6 - Identifying Common Reasons for Cleansing and Profiling Data Learn to Profile Data Address Redundant, Duplicated, and Unnecessary Data Work with Missing Value Address Invalid Data Convert Data to Meet Specifications 7 - Executing Different Data Manipulation Techniques Manipulate Field Data and Create Variables Transpose and Append Data Query Data 8 - Explaining Common Techniques for Data Manipulation and Optimization Use Functions to Manipulate Data Use Common Techniques for Query Optimization 9 - Applying Descriptive Statistical Methods Use Measures of Central Tendency Use Measures of Dispersion Use Frequency and Percentages 10 - Describing Key Analysis Techniques Get Started with Analysis Recognize Types of Analysis 11 - Understanding the Use of Different Statistical Methods Understand the Importance of Statistical Tests Break Down the Hypothesis Test Understand Tests and Methods to Determine Relationships Between Variables 12 - Using the Appropriate Type of Visualization Use Basic Visuals Build Advanced Visuals Build Maps with Geographical Data Use Visuals to Tell a Story 13 - Expressing Business Requirements in a Report Format Consider Audience Needs When Developing a Report Describe Data Source Considerations For Reporting Describe Considerations for Delivering Reports and Dashboards Develop Reports or Dashboards Understand Ways to Sort and Filter Data 14 - Designing Components for Reports and Dashboards Design Elements for Reports and Dashboards Utilize Standard Elements Creating a Narrative and Other Written Elements Understand Deployment Considerations 15 - Understand Deployment Considerations Understand How Updates and Timing Affect Reporting Differentiate Between Types of Reports 16 - Summarizing the Importance of Data Governance Define Data Governance Understand Access Requirements and Policies Understand Security Requirements Understand Entity Relationship Requirements 17 - Applying Quality Control to Data Describe Characteristics, Rules, and Metrics of Data Quality Identify Reasons to Quality Check Data and Methods of Data Validation 18 - Explaining Master Data Management Concepts Explain the Basics of Master Data Management Describe Master Data Management Processes Additional course details: Nexus Humans CompTIA Data Plus (DA0-001) training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the CompTIA Data Plus (DA0-001) course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

Leading SAFe: Virtual In-House Training
By IIL Europe Ltd
Leading SAFe®: Virtual In-House Training During this course, attendees gain the knowledge necessary to lead a Lean-Agile enterprise by using the Scaled Agile Framework® (SAFe®) and its underlying principles derived from Lean, systems thinking, Agile development, product development flow, and DevOps. Participants in the class gain insights into mastering business agility to thrive in competitive markets. They discuss how to establish team and technical agility and organize and re-organize around the flow of value. Attendees also learn and practice the skills to support and execute PI Planning events and coordinate multiple Agile Release Trains (ARTs). Class participants will explore the importance of adopting a customer-centric mindset and Design-Thinking approach to Agile Product Delivery. Learners will also understand how to implement a Lean Portfolio Management function within their enterprise. What you will Learn After attending this class, attendees should be able to: Lead the transformation to business agility with SAFe® Become a Lean-Agile leader Understand customer needs Design Thinking Enable Agile Product delivery Implement Lean Portfolio Management Thrive in the digital age with business agility Become a Lean-Agile leader Establish Team and Technical Agility Build solutions with Agile Product Delivery Explore Lean Portfolio Management Lead the change Become a Certified SAFe® Agilist

Managing Stress and Building Resilience: In-House Training
By IIL Europe Ltd
Managing Stress and Building Resilience: In-House Training Stress has an impact on all of us at some point in our professional lives. Learning how to manage stress and build resilience will result in higher professional productivity, better health, and more sustainable living habits. It will also help us create a physical - and emotional - work-life balance. In this one-day workshop, you will learn practical solutions to sustain behavior change that can positively impact your life on both a professional and personal level. When you are able to reduce the level of negative stress that affects you, your performance improves, along with your health and happiness. The objective of this course is therefore not only to create awareness around emotional well-being in a work context, but also to help participants create a better overall balance between the investment they make in their personal and professional lives. This course covers how our perceptions affect our beliefs and how our beliefs affect our actions. You will learn a host of stress-reduction techniques, while exploring your own stress triggers and responses. Highly interactive, the sessions cover a blend of theory, discussions, and exercises. You will explore concepts with fellow participants within a safe environment where skills and habits can be developed, sharpened, and improved. What You Will Learn At the end of this program, you will be able to: Identify what stress feels like and what the typical symptoms and reactions are to stress Analyze your own responses to stressful events and the consequences of those reactions Organize your work structure to reduce stress and build resilience Recognize activities that drain you and those that give you energy Generate relief from stressful events Cultivate a mindset of resilience Better manage your time, work commitments, and personal boundaries in order to be most effective at your job Getting Started What is stress? Beliefs and thinking errors Work-life balance Drainers and energizers Stress reduction techniques Time management Summary and Next Steps

Conflict Resolution Skills: In-House Training
By IIL Europe Ltd
Conflict Resolution Skills: In-House Training Many organizations have assumed that workplace conflict is always destructive. So, they have often believed that conflict is best dealt with by managers or even via policies and procedures. After all, conflict creates workplace stress and leads to many performance problems, generating very real organizational costs! However, savvy organizations have embraced the fact that when conflict is understood and harnessed, it can be leveraged to add value to teams and even enhance performance. With the right knowledge, skills, training, and practice, conflict can be productive and make organizations better! In this highly interactive course, learners will discover the connection between individual conflict response and team-empowering conflict resolution skills. Participants will explore conflict's visceral dynamics and the nuanced behaviors we individually engage in to communicate and respond to conflict. Learners will apply techniques for transforming unproductive conflict responses into productive ones. Additionally, learners will use a systematic method that prepares them to objectively dissect real-world conflict, while practicing many strategies for resolving it. They will also develop proactive conflict approach plans, which they can transfer back to their own workplaces. What you will Learn At the end of this program, you will be able to: Recognize the organizational costs of conflict Explain our physical and mental responses to conflict Communicate proactively and effectively with different types of people during conflict Replace unproductive conflict responses with productive ones Use the Conflict Resolution Diagram (CRD) process and conflict resolution approaches Relate team stages of development to shifts in conflict Develop a proactive conflict approach for your organization Create a conflict resolution plan for a real-world scenario Getting Started Introductions and social agreements Course goal and objectives Opening activities Conflict Facilitation Readiness Conflict responses and perceptions Conflict basics Conflict and organizations Dynamics of conflict Conflict Styles and Communication A look at the color energies model Conflict through the color energies and DiSC® lens Communication with opposite color energies Individual Response to Conflict The anatomy of conflict Recognizing unproductive conflict responses 4 steps to productive conflict Choosing productive conflict responses Team Performance and Conflict High-performing team relationships Conflict and project team performance Conflict Resolution Diagram (CRD) and process Conflict Facilitation - Preparation Recognizing context and stakeholder needs Using team conflict resolution approaches Preparing for Crucial Conversations® Conflict Facilitation - Clarity Exposing assumptions and biases Defining the conflict and using the CRD Conflict Facilitation - Action Proactive conflict management Conflict facilitation practice Summary and Next Steps Review Personal action plans

ISO 14001 Internal Auditor
By Training Centre
The IECB ISO 14001 Internal Auditor training course enables you to acquire the necessary competencies to conduct effective environmental management system (EMS) audits by applying widely recognized audit principles, procedures, and techniques. About This Course This training course combines the requirements of ISO/IEC 17021-1, the recommendations of ISO 19011, and other best practices of auditing and integrates them into a comprehensive methodology which enables you to effectively plan and conduct ISO 14001 conformity assessment audits. In addition to providing a solid theoretical foundation, this training course adopts a practical approach by incorporating examples, exercises, and quizzes that help you practice the most important aspects of conformity assessment audits, such as the interpretation of ISO 14001 requirements in the context of an audit, the application of auditing principles and methods, the utilization of approaches to evidence collection and verification, leading an audit team, drafting nonconformity reports, and preparing the final audit report. After completing the training course, you can sit for the exam. After passing the exam, you gain the 'Certified ISO 14001 Lead Auditor' credential, which validates your professional expertise and demonstrates that you have the knowledge and skills to audit environmental management systems that are based on the requirements of ISO 14001. Learning objectives By the end of this training course, the participants will be able to: Explain the foundational concepts and principles of an environmental management system (EMS) based on ISO 14001 Interpret the ISO 14001 requirements for an EMS from the perspective of an auditor Evaluate the EMS conformity to ISO 14001 requirements, in accordance with the foundational audit concepts and principles Plan, conduct, and close an ISO 14001 compliance audit, in accordance with ISO/IEC 17021-1 requirements, ISO 19011 guidelines, and other best practices of auditing Manage an ISO 14001 audit programme Educational approach This training course is participant centred and: Elaborates theories, approaches, and best practices used in EMS audits Provides practical exercises which are based on scenarios inspired by real-life events Encourages interaction between the trainer and participants by means of questions and suggestions Provides quizzes consisting of stand-alone and scenario-based questions, tailored to prepare the participants for the certification exam Course overview Module 1 Foundational principles and concepts of an environmental management system Module 2 Environmental management system requirements Module 3 Foundational audit concepts and principles Module 4 Preparing an ISO 14001 audit Module 5 Conducting an ISO 14001 audit Module 6 Closing an ISO 14001 audit Module 7 Operating an ISO 14001 audit programme Course Agenda Day 1: Introduction to the environmental management system (EMS) and ISO 14001 Day 2: Audit principles and the preparation for and initiation of an audit Day 3: On-site audit activities, Closing of the audit and the Certification exam Provided by This course is Accredited by NACSand Administered by the IECB Accreditation Assessment All candidates at official training courses are tested throughout their course with quizzes and exercises, in combination with a final exam held on the last day of the course. Both elements are a part of the overall score. For this course, the final exam constitutes a 10 question essay type exam which should be completed within 125 minutes. A passing score is achieved at 70%. Self-study candidates can purchase an exam voucher from our Store. Exam results are returned within 24 hours, with successful candidates receiving both a digital badge and a Certificate of Achievement Prerequisites In order to fully benefit from this training course, participants should have an understanding of environmental concepts, ISO 14001, and audit principles. What's Included? Refreshments & Lunch (Classroom courses only) Course Slide Deck Official Study Guides CPD Certificate The Exam Who Should Attend? The ISO 14001 Internal Auditor training course is intended for: Auditors seeking to conduct internal EMS audits Managers or consultants seeking to master the EMS audit process Individuals responsible for maintaining conformity to the requirements of ISO 14001 in an organization Technical experts seeking to prepare for EMS audits Expert advisors in environmental management

Complete Python training course description Python is an agile, robust, expressive, fully objectoriented, extensible, and scalable programming language. It combines the power of compiled languages with the simplicity and rapid development of scripting languages. This course covers Python from the very basics of 'hello world!' through to object oriented programming and advanced topics such as multi threading. Hands on follows all the major sections in order to reinforce the theory. What will you learn Read Python programs. Write Python programs. Debug Python programs. Use Python's objects and memory model as well as its OOP features. Complete Python programming training course details Who will benefit: Anyone wishing to learn Python. Prerequisites: None. Duration 5 days Complete Python programming training course contents Welcome to Python: What is Python? Origins, features. Downloading and installing Python, Python manuals, comparing Python, other implementations. Getting started: Program output, the print statement, "hello world!", Program input, raw_input(), comments, operators, variables and assignment, numbers, strings, lists and tuples, dictionaries, indentation, if statement, while Loop, for loop. range(), list comprehensions. Files, open() and file() built-in functions. Errors and exceptions. Functions, Classes, Modules, useful functions. Python basics: Statements and syntax, variable assignment, identifiers, basic style guidelines, memory management, First Python programs, Related modules/developer tools. Python Objects: Other built-in types, Internal Types, Standard type operators, Standard type built-in functions, Categorizing standard types, Unsupported types. Numbers: Integers, Double precision floating point numbers, Complex numbers, Operators, Built-in and factory functions, Other numeric types. Sequences: strings, lists, and tuples: Sequences, Strings, Strings and operators, String-only operators, Built-in functions, String built-in methods, Special features of strings, Unicode, Summary of string highlights, Lists, Operators, Built-in functions, List type built-in methods, Special features of lists, Tuples, Tuple operators and built-in functions, Tuples special features, Copying Python objects and shallow and deep copies. Mapping and set types: Mapping Type: dictionaries and operators, Mapping type built-in and factory functions, Mapping type built-in methods, Dictionary keys, Set types, Set type operators, Built-in functions, Set type built-in methods. Conditionals and loops: If, else and elif statements, Conditional expressions, while, for, break, continue and pass statements, else statement . . . take two, Iterators and iter(), List comprehensions, Generator expressions. Files and input/output: File objects, File built-in functions [open() and file()], File built-in methods and attributes, Standard files, Command-line arguments, File system, File execution, Persistent storage modules. Errors and exceptions: What are exceptions? Detecting and handling exceptions, Context management, Exceptions as strings, Raising exceptions, Assertions, Standard exceptions, Creating Exceptions, Why exceptions, Exceptions and the sys module. Functions: Calling, creating and passing functions, formal arguments, variable-length arguments, functional programming, Variable scope, recursion, generators. Modules: Modules and files, Namespaces, Importing modules, Module import features, Module built-in functions, Packages, Other features of modules. Object-Oriented Programming (OOP): Classes, Class attributes, Instances, Instance attributes, Binding and method invocation, Static methods and class methods, Composition, Sub-classing and derivation, Inheritance, Built-in functions for classes, and other objects, Customizing classes with special methods, Privacy, Delegation, Advanced features of new-style classes (Python 2.2+), Related modules and documentation. Execution environment: Callable and code Objects, Executable object statements and built-in functions, Executing other programs. 'Restricted' and 'Terminating' execution, operating system interface. Regular expressions: Special symbols and characters, REs and Python, Regular expressions example. Network programming: Sockets: communication endpoints, Network programming in Python, SocketServer module, Twisted framework introduction. Internet client programming: What are internet clients? Transferring files, Network news, E-mail. Multithreaded Programming: Threads and processes Python, threads, and the global interpreter lock, The thread and threading Modules. GUI programming: Tkinter and Python programming, Tkinter Examples, Brief tour of other GUIs. Web programming: Web surfing with Python: creating simple web clients, Advanced Web clients, CGI: helping web servers process client data, Building CGI applications, Using Unicode with CGI, Advanced CGI, Web (HTTP) Servers. Database programming: Python database application programmer's interface (DB-API), ORMs. Miscellaneous Extending Python by writing extensions, Web Services, programming MS Office with Win32 COM, Python and Java programming with Jython.

Cloud Operations on AWS
By Nexus Human
Duration 3 Days 18 CPD hours This course is intended for System administrators and operators who are operating in the AWS Cloud Informational technology workers who want to increase the system operations knowledge. Overview Identify the AWS services that support the different phases of Operational Excellence, an AWS Well-Architected Framework pillar Manage access to AWS resources using AWS accounts and organizations and AWS Identity and Access Management (IAM) Maintain an inventory of in-use AWS resources by using AWS services, such as AWS Systems Manager, AWS CloudTrail, and AWS Config Develop a resource deployment strategy using metadata tags, Amazon Machine Images (AMIs), and AWS Control Tower to deploy and maintain an AWS cloud environment Automate resource deployment by using AWS services, such as AWS CloudFormation and AWS Service Catalog Use AWS services to manage AWS resources through CloudOps lifecycle processes, such as deployments and patches Configure a highly available cloud environment that uses AWS services, such as Amazon Route 53 and Elastic Load Balancing, to route traffic for optimal latency and performance Configure AWS Auto Scaling and Amazon EC2 Auto Scaling to scale out your cloud environment based on demand Use Amazon CloudWatch and associated features, such as alarms, dashboards, and widgets, to monitor your cloud environment Manage permissions and track activity in your cloud environment by using AWS services, such as AWS CloudTrail and AWS Config Deploy your resources to an Amazon Virtual Private Cloud (Amazon VPC), establish necessary connectivity to your Amazon VPC, and protect your resources from disruptions of service State the purpose, benefits, and appropriate use cases for mountable storage in your AWS Cloud environment Explain the operational characteristics of object storage in the AWS Cloud, including Amazon Simple Storage Service (Amazon S3) and Amazon S3 Glacier Build a comprehensive cost model to help gather, optimize, and predict your cloud costs by using services such as AWS Cost Explorer and the AWS Cost & Usage Report This course teaches systems operators and anyone performing cloud operations functions how to manage and operate automatable and repeatable deployments of networks and systems on AWS. You will learn about cloud operations functions, such as installing, configuring, automating, monitoring, securing, maintaining, and troubleshooting these services, networks, and systems. The course also covers specific AWS features, tools, and best practices related to these functions. Prerequisites Successfully completed the AWS Technical Essentials course Background in either software development or systems administration Proficiency in maintaining operating systems at the command line, such as shell scripting in Linux environments or cmd/PowerShell in Windows Basic knowledge of networking protocols (TCP/IP, HTTP) 1 - Introduction to Cloud Operations on AWS What is Cloud Operations AWS Well-Architected Framework AWS Well-Architected Tool 2 - Access Management AWS Identity and Access Management (IAM) Resources, accounts, and AWS Organizations 3 - System Discovery Methods to interact with AWS services Tools for automating resource discovery Inventory with AWS Systems Manager and AWS Config Hands-On Lab: Auditing AWS Resources with AWS Systems Manager and AWS Config 4 - Deploy and Update Resources Cloud Operations in deployments Tagging strategies Deployment using Amazon Machine Images (AMIs) Deployment using AWS Control Tower 5 - Automate Resource Deployment Deployment using AWS CloudFormation Deployment using AWS Service Catalog Hands-On Lab: Infrastructure as Code 6 - Manage Resources AWS Systems Manager Hands-On Lab: Operations as Code 7 - Configure Highly Available Systems Distributing traffic with Elastic Load Balancing Amazon Route 53 8 - Automate Scaling Scaling with AWS Auto Scaling Scaling with Spot Instances Managing licenses with AWS License Manager 9 - Monitor and Maintain System Health Monitoring and maintaining healthy workloads Monitoring AWS infrastructure Monitoring applications Hands-On Lab: Monitor Applications and Infrastructure 10 - Data Security and System Auditing Maintaining a strong identity and access foundation Implementing detection mechanisms Automating incident remediation 11 - Operate Secure and Resilient Networks Building a secure Amazon Virtual Private Cloud (Amazon VPC) Networking beyond the VPC 12 - Mountable Storage Configuring Amazon Elastic Block Store (Amazon EBS) Sizing Amazon EBS volumes for performance Using Amazon EBS snapshots Using Amazon Data Lifecycle Manager to manage your AWS resources Creating backup and data recovery plans Configuring shared file system storage Hands-On Lab: Automating with AWS Backup for Archiving and Recovery 13 - Object Storage Deploying Amazon Simple Storage Service (Amazon S3) Managing storage lifecycles on Amazon S3 14 - Cost Reporting, Alerts, and Optimization Gaining AWS cost awareness Using control mechanisms for cost management Optimizing your AWS spend and usage Hands-On Lab: Capstone lab for CloudOps Additional course details: Nexus Humans Cloud Operations on AWS training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the Cloud Operations on AWS course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

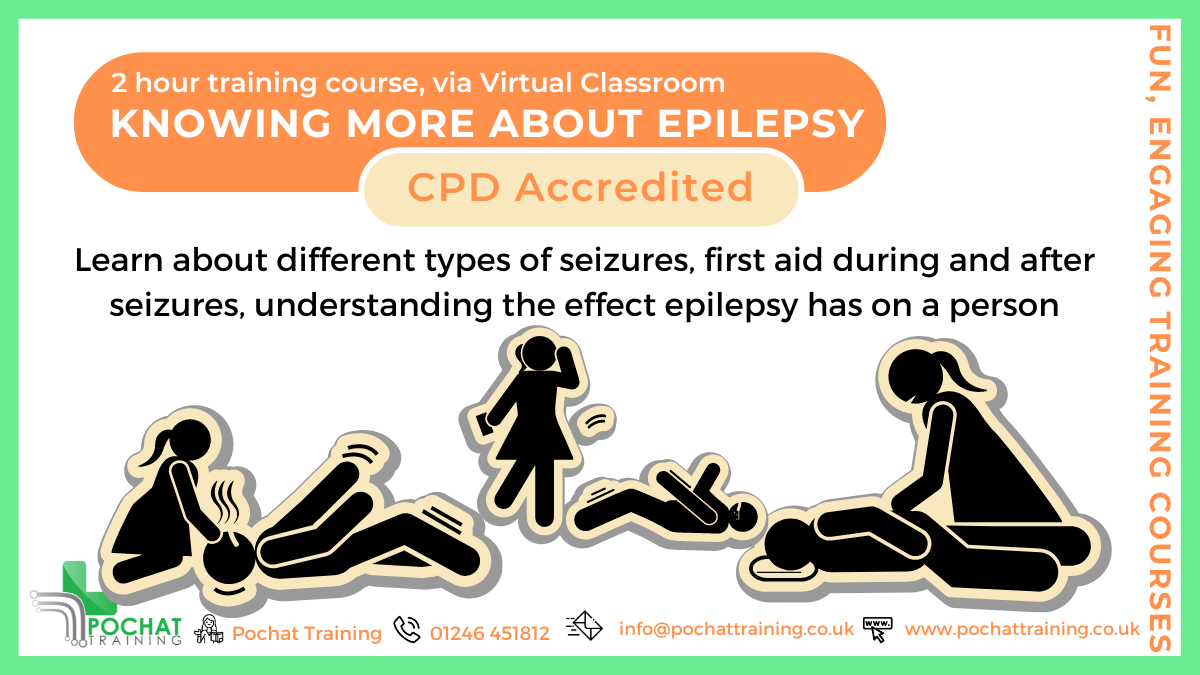
CPD Accredited, Interactive Short Course 2 hr session This training session gives a good introduction to epilepsy How can you best understand and help those affected with different types of seizures Great for those who have contact with people with epilepsy, such as family and friends, those working in education and afterschool clubs, sports and good CPD for nurses Course Contents: What is Epilepsy The different types of seizures Keeping someone safe while they're having a seizure Understand how having epilepsy affects someone's life Great for teachers and TAs in schools, for those working in care or community events, and those close to people with epilepsy Benefits of this Short Course: Epilepsy is one of the most common neurological conditions In the UK, there are over 600,000 people with a diagnosis of epilepsy That is about 1 in 103 people, or 1 child or young person in every 3 classrooms Every year, 1000 people in the UK die due to their epilepsy Help avoid unnecessary suffering or even death by knowing what to do to help while they're having an epileptic seizure, and keep them safe
EC-Council Certified Ethical Hacker (CEH) v12
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for The Certified Ethical Hacking v12 course will significantly benefit security officers, auditors, security professionals, site administrators, and anyone who is concerned about the integrity of the network infrastructure. Overview Information security controls, laws, and standards. Various types of footprinting, footprinting tools, and countermeasures. Network scanning techniques and scanning countermeasures Enumeration techniques and enumeration countermeasures Vulnerability analysis to identify security loopholes in the target organization?s network, communication infrastructure, and end systems. System hacking methodology, steganography, steganalysis attacks, and covering tracks to discover system and network vulnerabilities. Different types of malware (Trojan, Virus, worms, etc.), system auditing for malware attacks, malware analysis, and countermeasures. Packet sniffing techniques to discover network vulnerabilities and countermeasures to defend against sniffing. Social engineering techniques and how to identify theft attacks to audit human-level vulnerabilities and social engineering countermeasures. DoS/DDoS attack techniques and tools to audit a target and DoS/DDoS countermeasures. Session hijacking techniques to discover network-level session management, authentication/authorization, and cryptographic weaknesses and countermeasures. Webserver attacks and a comprehensive attack methodology to audit vulnerabilities in webserver infrastructure, and countermeasures. Web application attacks, comprehensive web application hacking methodology to audit vulnerabilities in web applications, and countermeasures. SQL injection attack techniques, injection detection tools to detect SQL injection attempts, and countermeasures. Wireless encryption, wireless hacking methodology, wireless hacking tools, and Wi-Fi security tools. Mobile platform attack vector, android vulnerability exploitations, and mobile security guidelines and tools. Firewall, IDS and honeypot evasion techniques, evasion tools and techniques to audit a network perimeter for weaknesses, and countermeasures. Cloud computing concepts (Container technology, serverless computing), the working of various threats and attacks, and security techniques and tools. Penetration testing, security audit, vulnerability assessment, and penetration testing roadmap. Threats to IoT and OT platforms and defending IoT and OT devices. Cryptography ciphers, Public Key Infrastructure (PKI), cryptography attacks, and cryptanalysis tools. CEH provides an in-depth understanding of ethical hacking phases, various attack vectors, and preventative countermeasures. It will teach you how hackers think and act maliciously so you will be better positioned to setup your security infrastructure and defend against future attacks. An understanding of system weaknesses and vulnerabilities helps organizations strengthen their system security controls to minimize the risk of an incident. CEH was built to incorporate a hands-on environment and systematic process across each ethical hacking domain and methodology, giving you the opportunity to work towards proving the required knowledge and skills needed to achieve the CEH credential. You will be exposed to an entirely different posture toward the responsibilities and measures required to be secure. Now in its 12th version, CEH continues to evolve with the latest operating systems, tools, tactics, exploits, and technologies. 1 - Introduction to Ethical Hacking Information Security Overview Cyber Kill Chain Concepts Hacking Concepts Ethical Hacking Concepts Information Security Controls Information Security Laws and Standards 2 - 2 - Foot-printing and Reconnaissance Footprinting Concepts Footprinting through Search Engines Footprinting through Web Services Footprinting through Social Networking Sites Website Footprinting Email Footprinting Who is Footprinting DNS Footprinting Network Footprinting Footprinting through Social Engineering Footprinting Tools Footprinting Countermeasures 3 - Scanning Networks Network Scanning Concepts Scanning Tools Host Discovery Port and Service Discovery OS Discovery (Banner Grabbing/OS Fingerprinting) Scanning Beyond IDS and Firewall Draw Network Diagrams 4 - Enumeration Enumeration Concepts NetBIOS Enumeration SNMP Enumeration LDAP Enumeration NTP and NFS Enumeration SMTP and DNS Enumeration Other Enumeration Techniques Enumeration Countermeasures 5 - Vulnerability Analysis Vulnerability Assessment Concepts Vulnerability Classification and Assessment Types Vulnerability Assessment Solutions and Tools Vulnerability Assessment Reports 6 - System Hacking System Hacking Concepts Gaining Access Escalating Privileges Maintaining Access Clearing Logs 7 - Malware Threats Malware Concepts APT Concepts Trojan Concepts Virus and Worm Concepts Fileless Malware Concepts Malware Analysis Countermeasures Anti-Malware Software 8 - Sniffing Sniffing Concepts Sniffing Technique: MAC Attacks Sniffing Technique: DHCP Attacks Sniffing Technique: ARP Poisoning Sniffing Technique: Spoofing Attacks Sniffing Technique: DNS Poisoning Sniffing Tools Countermeasures Sniffing Detection Techniques 9 - Social Engineering Social Engineering Concepts Social Engineering Techniques Insider Threats Impersonation on Social Networking Sites Identity Theft Countermeasures 10 - Denial-of-Service DoS/DDoS Concepts DoS/DDoS Attack Techniques BotnetsDDoS Case Study DoS/DDoS Attack Tools Countermeasures DoS/DDoS Protection Tools 11 - Session Hijacking Session Hijacking Concepts Application Level Session Hijacking Network Level Session Hijacking Session Hijacking Tools Countermeasures 12 - Evading IDS, Firewalls, and Honeypots IDS, IPS, Firewall, and Honeypot Concepts IDS, IPS, Firewall, and Honeypot Solutions Evading IDS Evading Firewalls IDS/Firewall Evading Tools Detecting Honeypots IDS/Firewall Evasion Countermeasures 13 - Hacking Web Servers Web Server Concepts Web Server Attacks Web Server Attack Methodology Web Server Attack Tools Countermeasures Patch Management Web Server Security Tools 14 - Hacking Web Applications Web Application Concepts Web Application Threats Web Application Hacking Methodology Web API, Webhooks, and Web Shell Web Application Security 15 - SQL Injection SQL Injection Concepts Types of SQL Injection SQL Injection Methodology SQL Injection Tools Evasion Techniques Countermeasures 16 - Hacking Wireless Networks Wireless Concepts Wireless Encryption Wireless Threats Wireless Hacking Methodology Wireless Hacking Tools Bluetooth Hacking Countermeasures Wireless Security Tools 17 - Hacking Mobile Platforms Mobile Platform Attack Vectors Hacking Android OS Hacking iOS Mobile Device Management Mobile Security Guidelines and Tools 18 - IoT and OT Hacking IoT Hacking IoT Concepts IoT Attacks IoT Hacking Methodology IoT Hacking Tools Countermeasures OT Hacking OT Concepts OT Attacks OT Hacking Methodology OT Hacking Tools Countermeasures 19 - Cloud Computing Cloud Computing Concepts Container Technology Serverless Computing Cloud Computing Threats Cloud Hacking Cloud Security 20 - Cryptography Cryptography Concepts Encryption Algorithms Cryptography Tools Public Key Infrastructure (PKI) Email Encryption Disk Encryption Cryptanalysis Countermeasures Additional course details: Nexus Humans EC-Council Certified Ethical Hacker (CEH) v.12 training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the EC-Council Certified Ethical Hacker (CEH) v.12 course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

ISO 45001 Internal Auditor
By Training Centre
ISO 45001 is the first global occupational health and safety management system standard that replaces OHSAS 18001. The IECB Certified ISO 45001 Lead Auditor training course helps in developing the necessary skillset to perform occupational health and safety management system (OH&S MS) audits by applying widely recognized audit principles, procedures, and methods. About This Course This training course has been developed to reflect the importance of an effective internal audit. It strengthens your knowledge and skills to plan and carry out an OH&S MS audit in compliance with the guidelines for auditing management systems provided in ISO 19011 and the certification process described in ISO/IEC 17021-1. The exercises provided for this training course are designed to help you practice the most important aspects of an OH&S MS audit: ISO 45001 requirements, auditing principles, tools and techniques used to obtain evidence, leading a team of auditors, conducting interviews with auditees, reviewing documented information, drafting nonconformity reports, and preparing the final audit report. The successful completion of the training course is followed by an exam. If you pass the exam, you gain the 'Certified ISO 45001 Internal Auditor' credential, which validates your professional capabilities and demonstrates your ability to audit an OH&S MS based on ISO 45001. Learning objectives By the end of this training course, the participants will be able to: Explain the foundational concepts and principles of an occupational health and safety management system (OH&S MS) based on ISO 45001 Interpret the ISO 45001 requirements for an OH&S MS from the perspective of an auditor Evaluate the OH&S MS conformity to ISO 45001 requirements, in accordance with the foundational audit concepts and principles Plan, conduct, and close an ISO 45001 internal audit, in accordance with ISO/IEC 17021-1 requirements, ISO 19011 guidelines, and other best practices of auditing Manage an ISO 45001 internal audit programme Educational approach This training course is participant centred and contains: Theories, best practices used in occupational health and safety management auditing Lecture sessions, which are illustrated with practical exercises based on a case study that includes role-playing and discussions Interactions, made between participants by means of questions and suggestions Quizzes, which are a simulation and preview of the certification exam Course Overview Module 1 Foundational principles and concepts of an occupational health and safety management system Module 2 ISO 45001 requirements for an OH&S MS - Clauses 4 to 10 Module 3 Foundational audit concepts and principles Module 4 Preparing for an ISO 45001 audit Module 5 Conducting an internal ISO 45001 audit Module 6 Closing an ISO 45001 audit Module 7 Managing an ISO 45001 internal audit programme Course Agenda Day 1: Introduction to OH&S MS and ISO 45001 Day 2: Audit principles and the preparation for and initiation of an audit Day 3: On-site audit activities and closing the audit, as well as the Certification exam Accreditation Assessment All candidates at official training courses are tested throughout their course with quizzes and exercises, in combination with a final exam held on the last day of the course. Both elements are a part of the overall score. For this course, the final exam constitutes a 10 question essay type exam which should be completed within 125 minutes. A passing score is achieved at 70%. Self-study candidates can purchase an exam voucher from our Store. Exam results are returned within 24 hours, with successful candidates receiving both a digital badge and a Certificate of Achievement Prerequisites The main requirements for participating in this training course are: a foundational understanding of ISO 45001 and a comprehensive knowledge of audit principles. Provided by This course is Accredited by NACSand Administered by the IECB What's Included? Refreshments & Lunch (Classroom courses only) Course Slide Deck Official Study Guides CPD Certificate The Exam Who Should Attend? Auditors interested in performing OH&S MS internal audits Managers or consultants interested in advancing their knowledge of the OH&S MS audit process Internal auditors and individuals responsible for maintaining conformity to the requirements of ISO 45001 Technical experts interested in preparing for an OH&S MS audit Expert advisors in occupational health and safety management
