- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
ADO.NET training course description This ADO.net training course is designed to enable developers to use the toolset provided with.NET for data access including ADO.net objects, data controls, designers and interoperability with earlier ADO objects. The course is applicable for those using C# or VB.NET with ADO.NET What will you learn Retrieve and manipulate data using Microsoft's ADO.NET library. Work with the ADO.NET object model. Update data, including handling stored procedures, parameters, and return value. Search, sort and filter data. Leverage the power of XML. ADO.NET training course details Who will benefit: Programmers working with ADO.Net. Prerequisites: Effective programming with VB.NET or Concise introduction to C# Duration 2 days ADO.NET training course contents Introducing ADO.Net Traditional Data Access Architecture. ADO.Net Disconnected Data Access Architecture. Different components of ADO.Net. A review of basic SQL queries SQL SELECT Statement. SQL INSERT Statement. SQL UPDATE Statement. SQL DELETE Statement. Common data access tasks with ADO.Net Accessing Data using ADO.Net. Defining the connection string. Defining a Connection. Defining the command or command string. Defining the Data Adapter. Creating and filling the DataSet. A Demonstration Application The Interface. Loading the table. Filling the controls on the Form. Navigating through the records. Updating Data Steps for updating the table. Building the Application. Loading the table and displaying data in the form's controls. Initialising Commands. Adding Parameters to the commands. The ToggleControls() method of our application. Editing (or Updating) Records. Event Handler for the Save Button. Event Handler for the Cancel Button. Inserting Records. Deleting a Record. Using Stored Procedures Sample Stored Procedures. UPDATE Stored Procedure. INSERT Stored Procedure. DELETE Stored Procedure. SELECT Stored Procedure. Using Stored Procedures with ADO.Net.

Disciplined Agile Scrum Master (DASM): In-House Training
By IIL Europe Ltd
Disciplined Agile Scrum Master (DASM): In-House Training Is your team treading water using waterfall? Do you feel trapped in an agile framework? Would you like to find solutions to the problems you've been wrestling with? Are you looking for ways to enhance your team's agility? Break free from your old ways by choosing a way of working that fits your team's context. Find strategies to improve your processes and strengthen your team with the Disciplined Agile® tool kit. Disciplined Agile Scrum Master is a nine-lesson, instructor-led course that shows you how to use Disciplined Agile (DA™) to improve your team's way of working. In just two days, you will become familiar with foundational agile and lean practices that DA supports, practice using the tool kit to solve problems, and learn how to build high-performance teams. Filled with activities, animations, supplemental reading, and more, this course will prepare you to take the Disciplined Agile Scrum Master (DASM) exam and, equally important, start using Disciplined Agile immediately. #BBD0E0 » What You Will Learn After the completion of this course, you will be able to: Apply foundational agile and lean practices in your own team setting Describe what business agility is and how it is core to value proposition of Disciplined Agile® Describe the significance of the Disciplined Agile mindset Define the DA™ principles, promises, and guidelines and how they set Disciplined Agile apart from other frameworks Explain how people are organized into DA teams Define the primary DA roles and how they each are key to the success of a self-organizing agile team Explain how to help your team work well together using the Lean principle of 'respect people' Analyze your team's context to make better process-related decisions Select the best-fit DA life cycles for your teams Apply the five DA steps of choosing your team's way of working (WoW) Apply the relevant agile and lean techniques to successfully initiate your team Apply the relevant agile and lean techniques to support your team producing business value Apply the relevant agile and lean techniques to support your team releasing their work into production Apply the relevant agile and lean techniques to support your team on an ongoing basis Recognize when to be resilient List and define the principles of Lean Significance of the Disciplined Agile® Mindset Business agility and how it is core to value proposition of Disciplined Agile Eight DA principles and how they are core to what sets Disciplined Agile apart from other agile frameworks Which situations each of the DA™ life cycles is best applied DA Practice of choosing a team's way of working (WoW) Foundations of Agile How people are organized into DA teams Primary DA roles and how they each are key to the success of a self-organizing agile team Help your team work well together (Lean principle 'Respect people') Inception phase and why it is important DA tool kit to tailor your way of working within a select phase according to context Agile techniques and ceremonies relevant to Inception Construction phase and why it is important Agile techniques and ceremonies that take place during Construction Eliminate Waste and Build Quality (Lean principles) Deliver Value Quickly (Lean principle) Transition phase and why it is important Ongoing phase and why it is important Learn Pragmatically (Lean principle) Elements of the process blade (onion) diagram Principles of Lean When to be resilient Benefits of explicit workflow Kaizen loops and PDSA techniques for continuous improvement Options for cross-team learning: "community of practice" and "center of excellence"

Scrum Product Owner Exam Prep: In-House Training
By IIL Europe Ltd
Scrum Product Owner Exam Prep: In-House Training This workshop prepares you for the Scrum.org PSPO™ I certification. A voucher for the exam and the access information you will need to take the exam will be provided to you via email after you have completed the course. NOTE: If you have participated in any of IIL's other Scrum workshops, you can bypass this program and focus on reading/studying the Scrum Guide and taking practice exams from Scrum.org The Product Owner is responsible for maximizing the value of the product and the work of the Development Team. The Product Owner must be knowledgeable, available, and empowered to make decisions quickly in order for an Agile project to be successful. The Product Owner's key accountability is the Product Backlog. Managing, maintaining, and evolving the Product Backlog involves: Establishing a clear vision that engages the Development Team and stakeholders Clearly expressing Product Backlog items Ordering the items in the Product Backlog to best achieve the vision and goals Ensuring that the Product Backlog is visible, transparent, and clear to all Working with the Development Team throughout the project to create a product that fits the customer's need The Professional Scrum Product Owner™ I (PSPO I) certificate is a Scrum.org credential that enables successful candidates to demonstrate a fundamental level of Scrum mastery. PSPO I credential holders demonstrate an intermediate understanding of the Scrum framework, and how to apply it to maximize the value delivered with a product. They will exhibit a dedication to continued professional development, and a high level of commitment to their field of practice. Scrum.org does not require that you take their own sponsored or any preparatory training. However, training can facilitate your preparation for this credential. And this course is based on IIL's Scrum Product Owner Workshop, which is aligned with The Scrum Guide™. It will provide you with the information you need to pass the exam and IIL will make the arrangements for your online exam. You will be provided with an exam code and instructions, so that you can take the exam at your convenience, any time you are ready after the course. Passwords have no expiration date, but they are valid for one attempt only. See additional exam details on the next page. What you will Learn You'll learn how to: Successfully prepare for the Scrum.org PSPO I exam Identify the characteristics of a successful Product Owner Create a powerful vision statement Apply techniques to understand your customers and the market Manage and engage stakeholders Write effective user stories with acceptance criteria Utilize techniques to visualize and prioritize the Product Backlog Participate in the 5 Scrum events as the Product Owner Understand the Product Owner's role in closing a Scrum project Getting Started Introductions Workshop orientation Exam prep preview Fundamentals Recap Agile Manifesto, values, and mindset Product Owner characteristics Good vs. great Product Owner Product Ownership Product ownership Project vision Understand your customers and market Personas Stakeholder management and engagement The Product Backlog User Stories and Acceptance Criteria Preparing User Stories for a Sprint The Product Backlog Visualizing the Product Backlog Product Backlog Prioritization Technical Debt Sprint Planning and Daily Standups Sprint Planning Planning Poker Team Engagement Daily Standups Sprint Review, Retrospectives, and Closing Sprint Reviews Key Agile Patterns Retrospectives Closing the Project Summary and Next Steps Review of course goals, objectives, and content Exam prep next steps

Total PHP training course description PHP provides for the creation of dynamic web sites. This hands on training course looks at programming with PHP with an emphasis of building dynamic websites. Forms, state management and database integration are all covered with practicals used throughout the course to reinforce theory sessions. What will you learn Create dynamic web sites using PHP. Write PHP programs. Debug PHP programs. Examine existing code and determine its function. Total PHP training course details Who will benefit: Anyone creating dynamic web sites. Prerequisites: Software development fundamentals Duration 3 days Total PHP training course contents What is PHP? PHP history, dynamic web pages, how PHP works, alternatives to PHP. Downloading and installing PHP. Installing MySQL, installing Apache, platform issues. A first PHP web page A basic PHP script, PHP page structure. PHP comments. Integrating PHP and HTML. PHP forms HTML forms, taking values from forms. PHP and HTML Page inputs, environment inputs. phpinfo(), other form elements, sticky fields, generalised code, tables, forms, form elements, style sheets, JavaScript. Variables operators and expressions Expressions, data types, assignments, scope, constants, HTTP environment variables, getting data from forms using variables. Operators Arithmetic, logical, relational, Boolean, others. Control statements Conditional: if, else, elseif, switch. Loops: while, do while, for, break, continue, exit. Functions Built in functions, declaration, arguments, scope, loading functions from other files, defaulting parameters, call by value/ name. Arrays Indexes, array initialisation, array manipulation, multi dimensional arrays, array functions. String handling What is a string, string functions, matching, extraction, replacement. String operations, cleansing, sprintf, formatting web pages, strops and others, splitting strings, REs. PHP and databases Database structure, Database APIs, MySQL, Creating tables, Editing tables, simple SQL queries using PHP, building HTML tables using SQL queries, SQL injection, security issues, error handling. File I/O Opening, reading, writing files. Permissions, ownership, locking, directories. PHP, cookies and sessions State, Cookie properties, setting cookies, retrieving cookies, expiring/deleting cookies. Sessions, session variables, session IDs. PHP and email Emailing from servers, attachments. Objects OOP, PHP classes, constructors, instances.

ASP.Net training course description Our hands on ASP.NET training course that will teach students how to create a simple ASP.NET application that delivers dynamic content to the web. The course is applicable for those using C# or VB.NET with ASP.NET. What will you learn Create a web form with server controls Separate page code from content with code-behind pages, page controls, and components. Display dynamic data from a data source by using ADO.NET and data binding. Debug ASP.NET pages by using trace. ASP.Net training course details Who will benefit: Programmers working with ASP.NET. Prerequisites: HTML5 development fundamentals VBNet_course.htm or C++ programming foundation Duration 3 days ASP.Net training course contents Working with ASP.NET Introducing ASP.NET. Creating web forms. Adding ASP.NET code to a page. Handling page events. Using Web Controls Web controls and HTML controls compared. Using intrinsic controls. Using input validation controls. Introduction to user controls. Using trace in ASP.NET pages Overview of tracing. Trace information. Page-level trace and application-level trace. Separating code from content Advantages of partitioning an ASP.NET page. Creating and using code-behind pages. Creating and using components and classes. Inheritance of classes. Interfaces. Using ADO .NET to access data Accessing text files. Overview of ADO .NET Connecting to a data source. Accessing data with DateSets. Using DataViews. Accessing data with DataReaders. Using XML data with a DataSet. Creating an ASP.NET Web Application Requirements of a web application. Sharing information between pages. Securing an ASP.NET application. Web services. Creating a simple web service using Visual Studio.NET Calling a web service using Visual Studio.NET

Complete Ruby programming training course description This course starts with a quick-start session and then explains the language in detail from the bottom up. Hands on sessions follow all the major sessions to reinforce the theory. What will you learn Read Ruby programs. Write Ruby programs. Debug Ruby programs. Complete Ruby programming training course details Who will benefit: Anyone wishing to program in Ruby. Prerequisites: Software development fundamentals Duration 3 days Complete Ruby programming training course contents Introduction A tour of Ruby, Try Ruby, A suduko solver in Ruby. The Structure and execution of Ruby Lexical structure, Syntactic structure, Files structure, Program encoding, Program execution. Datatypes and objects Numbers, text, Arrays, Hashes, Ranges, Symbols, True, false, and nil, Objects. Expressions and operators Literals and keyword literals, Variable references, Constant references, Method invocations, Assignments, Operators. Statements and control structures Conditionals, loops, Iterators and enumerable objects, Blocks, Altering flow control, Exceptions and exception handling, BEGIN and END, Threads, fibres and continuations. Methods, Procs, Lambdas and closures Defining simple methods, Method names, Methods and parentheses, Method arguments, Procs and lambdas, Closures, Method objects, Functional programming. Classes and modules Defining a simple class, Method visibility: public, protected, privates, Subclassing and inheritance, Object creation and initialization, Modules, Loading and requiring modules, Singleton methods and Eigenclass, Method lookup, Constant lookup. Reflection and metaprogramming Types, classes and modules, Evaluating strings and blocks, Variables and constants, Methods, Hooks, Tracing, ObjectSpace and GV, Custom control structures, Missing methods and missing constants, Dynamically creating methods, Alias chaining. The Ruby platform Strings, Regular expressions, Numbers and Math, Dates and times, Collections, Files and directories, Input/output, Networking, Threads and concurrency. The Ruby environment Invoking the Ruby interpreter, The Top-level environment, Practical extraction and reporting shortcuts, Calling the OS, Security.

Software development training course description This three-day MTA Training course helps you prepare for Microsoft Technology Associate Exam 98-361, and build an understanding of these topics: Core programming, Object-Oriented programming, general software development, web applications, desktop applications, and databases. This course leverages the same content as found in the Microsoft Official Academic Course (MOAC) for this exam. What will you learn Describe core programming. Explain Object Oriented programming. Describe general software development. Describe Web applications. Describe desktop applications. Explain how databases work. Software development training course details Who will benefit: Anyone looking to learn the fundamentals of software. Prerequisites: None. Duration 3 days Software development training course contents Core programming Computer storage and data types How a computer stores programs and the instructions in computer memory, memory stacks and heaps, memory size requirements for the various data storage types, numeric data and textual data. Computer decision structures Various decision structures used in all computer programming languages; If decision structures; multiple decision structures, such as Ifâ¦Else and switch/Select Case; reading flowcharts; decision tables; evaluating expressions. Handling repetition For loops, While loops, Do...While loops and recursion. Understand error handling Structured exception handling. Object-oriented programming Classes Properties, methods, events and constructors; how to create a class; how to use classes in code. Inheritance Inheriting the functionality of a base class into a derived class. Polymorphism Extending the functionality in a class after inheriting from a base class, overriding methods in the derived class. Encapsulation Creating classes that hide their implementation details while still allowing access to the required functionality through the interface, access modifiers. General software development Application life cycle management Phases of application life cycle management, software testing. Interpret application specifications Application specifications, translating them into prototypes, code, select appropriate application type and components. Algorithms and data structures Arrays, stacks, queues, linked lists and sorting algorithms; performance implications of various data structures; choosing the right data structure. Web applications Web page development HTML, CSS, JavaScript. ASP.NET web application development Page life cycle, event model, state management, client-side versus server-side programming. Web hosting Creating virtual directories and websites, deploying web applications, understanding the role of Internet Information Services. Web services Web services that will be consumed by client applications, accessing web services from a client application, SOAP, WSDL. Desktop applications Windows apps UI design guideline categories, characteristics and capabilities of Store Apps, identify gestures. Console-based applications Characteristics and capabilities of console- based applications. Windows Services Characteristics and capabilities of Windows Services. Databases Relational database management systems Characteristics and capabilities of database products, database design, ERDs, normalisation concepts. Database query methods SQL, creating and accessing stored procedures, updating and selecting data. Database connection methods Connecting to various types of data stores, such as flat file; XML file; in-memory object; resource optimisation.

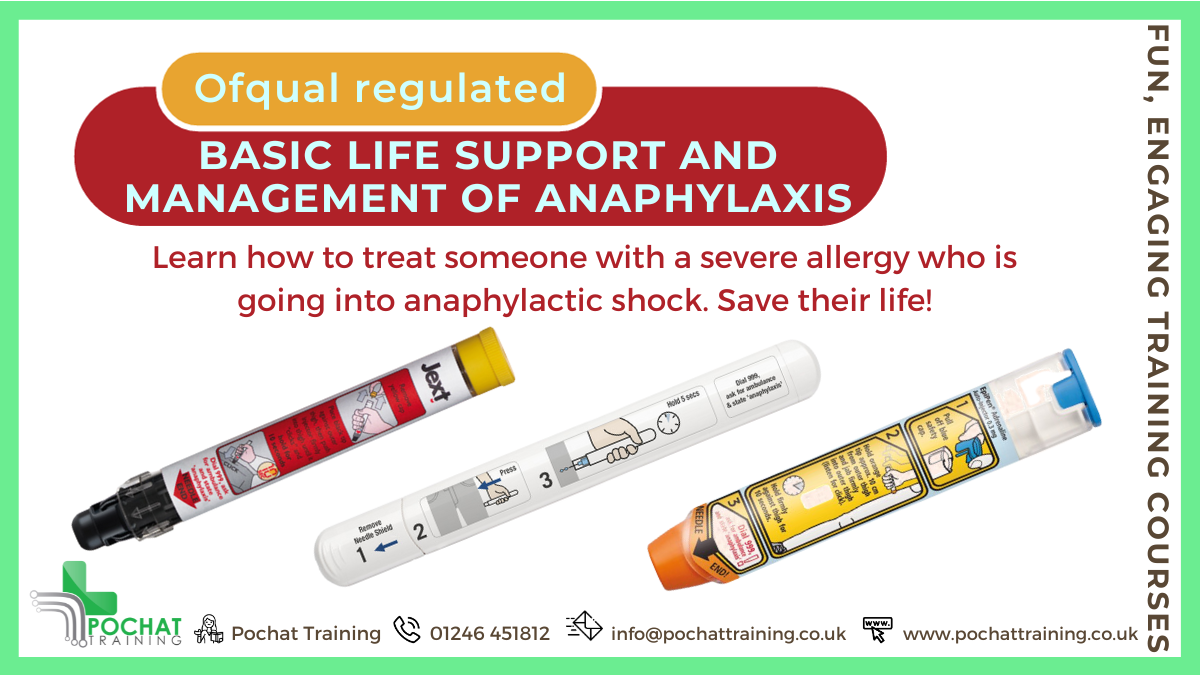
QA Level 2 Award In Basic Life Support And Management Of Anaphylaxis (RQF) Half day course Gives learners the knowledge and skills to save someone who is in anaphylactic shock Also covers how to prevent this happening in the first place Also available as a bolt-on to certain other courses Course Contents: Incident and Casualty Management Managing an Unresponsive Casualty Recovery Position The Chain of Survival CPR Signs and Symptoms of Anaphylaxis Treatment of Anaphylaxis Medication Use of Adrenaline Auto-Injectors Benefits of this course: Anaphylaxis is a severe and life-threatening allergic reaction, which requires immediate medical attention Did you know that in 2014 there were over 4,000 hospital admissions for anaphylactic shock in England? Every year, the number of those suffering from anaphylaxis is increasing. This makes it very important for people to know what to do when encountering someone who is having an anaphylactic shock This QA Level 2 Award in Basic Life Support and Management of Anaphylaxis (RQF) course has been designed for those who have a specific responsibility at work, at home or as a volunteer, to provide basic life support and manage anaphylaxis when dealing with an emergency Successful applicants will be able to recognise the signs and symptoms of anaphylaxis and will be equipped with the vital skills needed to administer safe, prompt and effective treatment. This includes practising with adrenaline auto-injectors. Accredited, Ofqual regulated qualification: Our Basic Life Support and Management of Anaphylaxis training course is a nationally recognised, Ofqual regulated qualification accredited by Qualsafe Awards.This means that you can be rest assured that your Basic Life Support and Management of Anaphylaxis Certificate fulfils the legal requirements and is a very good way to make sure you and your employees are trained in Management of Anaphylaxis..The Ofqual Register number for this course is 603/2548/3
CWSP training course description A hands-on training course concentrating solely on WiFi security with an emphasis on the delegates learning the necessary knowledge and skills to pass the CWSP exam. The course progresses from simple authentication, encryption and key management onto in depth coverage of 802.X and EAP along with many other security solutions such as access control, intrusion prevention and secure roaming. What will you learn Demonstrate the threats to WiFi networks. Secure WiFi networks. Configure: WPA2 RADIUS 802.1x EAP Pass the CWSP exam. CWSP training course details Who will benefit: Technical network staff. Technical security staff. Prerequisites: Certified Wireless Network Associate. Duration 5 days CWSP training course contents WLAN Security overview Standards, security basics, AAA, 802.11 security history. Hands on WLAN connectivity. Legacy 802.11 security Authentication: Open system, shared key. WEP. VPNs. MAC filters. SSID segmentation, SSID cloaking. Hands on Analysing 802.11 frame exchanges, viewing hidden SSIDs. Encryption Basics, AES, TKIP, CCMP, WPA, WPA2. Hands on Decrypting 802.11 data frames. 802.11 layer 2 authentication 802.1X: Supplicant, Authenticator, Authentication server. Credentials. Legacy authentication. EAP, Weak EAP protocols, Strong EAP protocols: EAP -PEAP, EAP-TTLS, EAP-TLS, EAP-FAST. Hands on Analysing 802.1X/EAP frames. 802.11 layer 2 dynamic key generation Robust Security Network. Hands on Authentication and key management. SOHO 802.11 security WPA/WPA2 personal, Preshared Keys, WiFi Protected Setup (WPS). Hands on PSK mapping. WLAN security infrastructure DS, Autonomous APs, WLAN controllers, split MAC, mesh, bridging, location based access control. Resilience. Wireless network management system. RADIUS/LDAP servers, PKI, RBAC. Hands on 802.1X/EAP configuration. RADIUS configuration. 802.11 Fast secure roaming History, RSNA, OKC, Fast BSS transition, 802.11k. Hands on Roaming. Wireless security risks Rogue devices, rogue prevention. Eavesdropping, DOS attacks. Public access and hotspots. Hands on Backtrack. WiFi security auditing Layer 1 audit, layer 2 audit, pen testing. WLAN security auditing tools. WiFi security monitoring Wireless Intrusion Detection and Prevention Systems. Device classification, WIDS/WIPS analysis. Monitoring. 802.11w. Hands on Laptop spectrum analysers. VPNs, remote access, guest access Role of VPNs in 802.11, remote access, hotspots, captive portal. Wireless security policies General policy, functional policy, recommendations.

Securing Linux systems training course description This course teaches you everything you need to know to build a safe Linux environment. The first section handles cryptography and authentication with certificates, openssl, mod_ssl, DNSSEC and filesystem encryption. Then Host security and hardening is covered with intrusion detection, and also user management and authentication. Filesystem Access control is then covered. Finally network security is covered with network hardening, packet filtering and VPNs. What will you learn Secure Linux accounts. Secure Linux file systems. Secure Linux access through the network. Securing Linux systems training course details Who will benefit: Linux technical staff needing to secure their systems. Prerequisites: Linux system administration (LPIC-1) Duration 5 days Securing Linux systems training course contents Cryptography Certificates and Public Key Infrastructures X.509 certificates, lifecycle, fields and certificate extensions. Trust chains and PKI. openssl. Public and private keys. Certification authority. Manage server and client certificates. Revoke certificates and CAs. Encryption, signing and authentication SSL, TLS, protocol versions. Transport layer security threats, e.g. MITM. Apache HTTPD with mod_ssl for HTTPS service, including SNI and HSTS. HTTPD with mod_ssl to authenticate users using certificates. HTTPD with mod_ssl to provide OCSP stapling. Use OpenSSL for SSL/TLS client and server tests. Encrypted File Systems Block device and file system encryption. dm-crypt with LUKS to encrypt block devices. eCryptfs to encrypt file systems, including home directories and, PAM integration, plain dm-crypt and EncFS. DNS and cryptography DNSSEC and DANE. BIND as an authoritative name server serving DNSSEC secured zones. BIND as an recursive name server that performs DNSSEC validation, KSK, ZSK, Key Tag, Key generation, key storage, key management and key rollover, Maintenance and resigning of zones, Use DANE. TSIG. Host Security Host Hardening BIOS and boot loader (GRUB 2) security. Disable useless software and services, sysctl for security related kernel configuration, particularly ASLR, Exec-Shield and IP / ICMP configuration, Exec-Shield and IP / ICMP configuration, Limit resource usage. Work with chroot environments, Security advantages of virtualization. Host Intrusion Detection The Linux Audit system, chkrootkit, rkhunter, including updates, Linux Malware Detect, Automate host scans using cron, AIDE, including rule management, OpenSCAP. User Management and Authentication NSS and PAM, Enforce password policies. Lock accounts automatically after failed login attempts, SSSD, Configure NSS and PAM for use with SSSD, SSSD authentication against Active Directory, IPA, LDAP, Kerberos and local domains, Kerberos and local domains, Kerberos tickets. FreeIPA Installation and Samba Integration FreeIPA, architecture and components. Install and manage a FreeIPA server and domain, Active Directory replication and Kerberos cross-realm trusts, sudo, autofs, SSH and SELinux integration in FreeIPA. Access Control Discretionary Access Control File ownership and permissions, SUID, SGID. Access control lists, extended attributes and attribute classes. Mandatory Access Control TE, RBAC, MAC, DAC. SELinux, AppArmor and Smack. etwork File Systems NFSv4 security issues and improvements, NFSv4 server and clients, NFSv4 authentication mechanisms (LIPKEY, SPKM, Kerberos), NFSv4 pseudo file system, NFSv4 ACLs. CIFS clients, CIFS Unix Extensions, CIFS security modes (NTLM, Kerberos), mapping and handling of CIFS ACLs and SIDs in a Linux system. Network Security Network Hardening FreeRADIUS, nmap, scan methods. Wireshark, filters and statistics. Rogue router advertisements and DHCP messages. Network Intrusion Detection ntop, Cacti, bandwidth usage monitoring, Snort, rule management, OpenVAS, NASL. Packet Filtering Firewall architectures, DMZ, netfilter, iptables and ip6tables, standard modules, tests and targets. IPv4 and IPv6 packet filtering. Connection tracking, NAT. IP sets and netfilter rules, nftables and nft. ebtables. conntrackd Virtual Private Networks OpenVPN server and clients for both bridged and routed VPN networks. IPsec server and clients for routed VPN networks using IPsec-Tools / racoon. L2TP.

Search By Location
- IT Courses in London
- IT Courses in Birmingham
- IT Courses in Glasgow
- IT Courses in Liverpool
- IT Courses in Bristol
- IT Courses in Manchester
- IT Courses in Sheffield
- IT Courses in Leeds
- IT Courses in Edinburgh
- IT Courses in Leicester
- IT Courses in Coventry
- IT Courses in Bradford
- IT Courses in Cardiff
- IT Courses in Belfast
- IT Courses in Nottingham