- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
368 Courses in Manchester
Lawful Intercept training course description Packet based networks require a different approach to Lawful Intercept (LI) than that used in circuit switched networks. This course focuses on what Lawful Interception and Data Retention (DR) means to communications service providers in the IP and NGN areas. The course assumes a basic knowledge of IP networking (i.e. DNS, TCP/UDP, IP, RTP) and the building of services on an IP platform (e.g. SIP, SDP, FTP, HTTP). The course first looks at the regulatory context for LI and DR and how this is translated to a practical architecture. What will you learn Recognise the legal and regulatory obligations to provide LI and DR. Identify the components of the handover architecture for each of LI and DR. Identify the preferred location of points of interception and points of retention in the IP network. Map intercepted material to handover protocols. Understand the data mapping defined in the available standards for both LI and DR. Lawful Intercept training course details Who will benefit: Technical and managerial staff needing to implement public networks. Prerequisites: TCP/IP Foundation Duration 1 day Lawful Intercept training course contents What is meant by LI and DR? Review of regulation: Data protection Directive; Data Retention Directive; RIPA. LI architectures Handover and Interception: ETSI standards ES 201 671 and TS 102 232. LI handover protocol IRI and CC handover; correlation; manual interfaces. DR architectures Handover of query results; points of retention. DR query command set Retrieval of retained records. Security concerns Operation privacy; target privacy; storage and transmission integrity. Implementation Identifying PoI and PoR for provided services. LI and DR wrap up Interaction with other services, storage obligations (volume, time, availability).

Assessing and Managing Cyber Security Risks for Essential Services Operators
By EnergyEdge - Training for a Sustainable Energy Future
About this Virtual Instructor Led Training (VILT) This 3 half-day Virtual Instructor Led Training (VILT) course will help participants grasp the idea of real-world risk management and how this relates to the cyber world. The VILT course will cover topics surrounding identifying cyber risks and vulnerabilities, guidance on applying administrative actions, and comprehensive solutions to ensure your organization is adequately secure and protected. The VILT course will guide participants on how to conduct a security risk assessment for their organization, and equip them with the skills to develop a risk compliance assessment plan as well as methods to develop risk management strategies which can improve their organization's security posture. The VILT course has at least a 30% hands-on approach through the use of Table Top Exercises. The VILT course will cover the following modules: Introduction to Risk Assessments (RA) Threat Actors and Their Motivations Threat and Risk Assessment Critical Controls Identification Maturity Assessment Treated Cyber Risk Profile Target Cyber Risk Profile and Strategy Target Audience The VILT course is intended for professionals responsible for organizational information and security system and those involved in operating and maintenance of critical information and IT network & sotware systems. Professionals who are designated as the Single Point of Accountability (SPoA) as well as system auditors will find this course useful. Course Level Basic or Foundation Training Methods The VILT course will be delivered online in 3 half-day sessions comprising 4 hours per day, with 2 x 10 minutes break per day, including time for lectures, discussion, quizzes and short classroom exercises. Course Duration: 3 half-day sessions, 4 hours per session (12 hours in total). This VILT course is delivered in partnership with ENGIE Laborelec. Trainer Your expert course leader is a is specialized in cybersecurity risk management. Before joining ENGIE, she worked for The National Cybersecurity Agency of France (ANSSI) based in Paris (France) and for Deloitte Belgium located in Zaventem (Belgium). She has been involved in cybersecurity projects focusing on the principle of protecting critical infrastructures. Her different experiences in Cyber Security, Anti-Money Laundering and Global Trade Compliance (including Export Control and Customs) gave her the opportunity to use methodologies tackling strategic, operational and financial control issues at all levels of an organization: people, business processes, IT applications and infrastructure, legal and regulatory compliance. She was an EBIOS Risk Manager (RM) trainer while she worked for the French government; EBIOS RM is the French method for assessing and treating digital risks. She also had the opportunity to represent France towards European institutions and other relevant stakeholders for topics related to cybersecurity risk management. POST TRAINING COACHING SUPPORT (OPTIONAL) To further optimise your learning experience from our courses, we also offer individualized 'One to One' coaching support for 2 hours post training. We can help improve your competence in your chosen area of interest, based on your learning needs and available hours. This is a great opportunity to improve your capability and confidence in a particular area of expertise. It will be delivered over a secure video conference call by one of our senior trainers. They will work with you to create a tailor-made coaching program that will help you achieve your goals faster. Request for further information about post training coaching support and fees applicable for this. Accreditions And Affliations

Microsoft security training course description A hands on training course focusing on security in the Microsoft environment. The course progresses from patch management onto the use of Microsoft security tools. Then server, desktop and network security are studied in the Microsoft environment. What will you learn Use Microsoft security tools. Secure Microsoft servers. Secure Microsoft desktops. Secure Microsoft networks. Microsoft security training course details Who will benefit: Technical server support staff. Technical desktop support staff. Technical network staff. Technical security staff. Prerequisites: Supporting Windows server 2016 Networking Microsoft systems. Duration 3 days Microsoft security training course contents Introduction Security threats, Microsoft defaults, admin accounts, security patches, patch management, patch tools. Hands on: Studying Microsoft defaults, applying security patches. Microsoft security tools Microsoft updates, WSUS, Inventory tool, baseline security analyser, URLscan, EventCombMT, Cipher security tool, Port reporter, PortQry. Tools hackers use. Hands on: Using Microsoft security tools. Server security Checklists, core server security, AD, Member server security, Domain controller security, Specific roles. Hands on Hardening Microsoft servers, security templates. Active Directory Admin authority in AD, group policy, trust and authentication. Desktop security Checklists, core client security, anti virus software, anti spyware software, firewalls, securing clients with AD, securing clients with group policy, software restriction policies. Hands on Securing Microsoft desktops. Network security Checklist, IP security, VPNs, PKI, certificate authorities, RAS, RRAS, IAS. Hands on: VPN configuration, IAS configuration. Monitoring Auditing, authorisation and logons, tracking, system monitoring, detecting attacks. Hands on: Monitoring Microsoft systems. Summary Microsoft security response centre, security advisories.

Securing UNIX systems training course description This course teaches you everything you need to know to build a safe Linux environment. The first section handles cryptography and authentication with certificates, openssl, mod_ssl, DNSSEC and filesystem encryption. Then Host security and hardening is covered with intrusion detection, and also user management and authentication. Filesystem Access control is then covered. Finally network security is covered with network hardening, packet filtering and VPNs. What will you learn Secure UNIX accounts. Secure UNIX file systems. Secure UNIX access through the network. Securing UNIX systems course details Who will benefit: Linux technical staff needing to secure their systems. Prerequisites: Linux system administration (LPIC-1) Duration 5 days Securing UNIX systems course contents Cryptography Certificates and Public Key Infrastructures X.509 certificates, lifecycle, fields and certificate extensions. Trust chains and PKI. openssl. Public and private keys. Certification authority. Manage server and client certificates. Revoke certificates and CAs. Encryption, signing and authentication SSL, TLS, protocol versions. Transport layer security threats, e.g. MITM. Apache HTTPD with mod_ssl for HTTPS service, including SNI and HSTS. HTTPD with mod_ssl to authenticate users using certificates. HTTPD with mod_ssl to provide OCSP stapling. Use OpenSSL for SSL/TLS client and server tests. Encrypted File Systems Block device and file system encryption. dm-crypt with LUKS to encrypt block devices. eCryptfs to encrypt file systems, including home directories and, PAM integration, plain dm-crypt and EncFS. DNS and cryptography DNSSEC and DANE. BIND as an authoritative name server serving DNSSEC secured zones. BIND as an recursive name server that performs DNSSEC validation, KSK, ZSK, Key Tag, Key generation, key storage, key management and key rollover, Maintenance and resigning of zones, Use DANE. TSIG. Host Security Host Hardening BIOS and boot loader (GRUB 2) security. Disable useless software and services, sysctl for security related kernel configuration, particularly ASLR, Exec-Shield and IP / ICMP configuration, Exec-Shield and IP / ICMP configuration, Limit resource usage. Work with chroot environments, Security advantages of virtualization. Host Intrusion Detection The Linux Audit system, chkrootkit, rkhunter, including updates, Linux Malware Detect, Automate host scans using cron, AIDE, including rule management, OpenSCAP. User Management and Authentication NSS and PAM, Enforce password policies. Lock accounts automatically after failed login attempts, SSSD, Configure NSS and PAM for use with SSSD, SSSD authentication against Active Directory, IPA, LDAP, Kerberos and local domains, Kerberos and local domains, Kerberos tickets. FreeIPA Installation and Samba Integration FreeIPA, architecture and components. Install and manage a FreeIPA server and domain, Active Directory replication and Kerberos cross-realm trusts, sudo, autofs, SSH and SELinux integration in FreeIPA. Access Control Discretionary Access Control File ownership and permissions, SUID, SGID. Access control lists, extended attributes and attribute classes. Mandatory Access Control TE, RBAC, MAC, DAC. SELinux, AppArmor and Smack. etwork File Systems NFSv4 security issues and improvements, NFSv4 server and clients, NFSv4 authentication mechanisms (LIPKEY, SPKM, Kerberos), NFSv4 pseudo file system, NFSv4 ACLs. CIFS clients, CIFS Unix Extensions, CIFS security modes (NTLM, Kerberos), mapping and handling of CIFS ACLs and SIDs in a Linux system. Network Security Network Hardening FreeRADIUS, nmap, scan methods. Wireshark, filters and statistics. Rogue router advertisements and DHCP messages. Network Intrusion Detection ntop, Cacti, bandwidth usage monitoring, Snort, rule management, OpenVAS, NASL. Packet Filtering Firewall architectures, DMZ, netfilter, iptables and ip6tables, standard modules, tests and targets. IPv4 and IPv6 packet filtering. Connection tracking, NAT. IP sets and netfilter rules, nftables and nft. ebtables. conntrackd Virtual Private Networks OpenVPN server and clients for both bridged and routed VPN networks. IPsec server and clients for routed VPN networks using IPsec-Tools / racoon. L2TP.

Securing Kubernetes training course description This course introduces concepts, procedures, and best practices to harden Kubernetes based systems and container-based applications against security threats. It deals with the main areas of cloud-native security: Kubernetes cluster setup, Kubernetes cluster hardening, hardening the underlying operating system and networks, minimizing microservices vulnerabilities, obtaining supply chain security as well as monitoring, logging, and runtime security. What will you learn Harden Kubernetes systems and clusters. Harden containers. Configure and use Kubernetes audit logs. Securing Kubernetes training course details Who will benefit: Technical staff working with Kubernetes Prerequisites: Kubernetes_for_engineers_course.htm Definitive Docker for engineers Duration 2 days Securing Kubernetes training course contents This course does not only deal with the daily security administration of Kubernetes-based systems but also prepares delegates for the official Certified Kubernetes Security Specialist (CKS) exams of the Cloud Native Computing Foundation (CNCF). Structure: 50% theory 50% hands on lab exercise Module 1: User and authorization management Users and service accounts in Kubernetes Authenticating users Managing authorizations with RBAC Module 2: Supply chain security Vulnerabilit checking for images Image validation in Kubernetes Reducing image footprint Secure image registries Module 3: Validating cluster setup and penetration testing Use CIS benchmark to review the security configuration of Kubernetes components. Modify the cluster components' configuration to match the CIS Benchmark. Penetration testing Kubernetes for known vulnerabilities. Module 4: System hardening Use kernel hardening tools Setup appropriate OS level security domains Container runtime sandboxes Limit network access Module 5: Monitoring and logging Configure Kubernetes audit logs Configure Audit Policies Monitor applications behaviour with Falco

CCNP training course description The Implementing and Operating Cisco Enterprise Network Core Technologies (ENCOR) v1.2 course provides the knowledge and skills needed to configure, troubleshoot, and manage enterprise wired and wireless networks. You'll learn to implement security principles within an enterprise network and how to overlay network design using solutions such as SDAccess and SD-WAN. Course content includes 3 days of self-study material. This course helps you prepare for the 350-401 Implementing Cisco Enterprise Network Core Technologies (ENCOR) exam What will you learn Configure, troubleshoot, and manage enterprise wired and wireless networks Implement security principles within an enterprise network Prepare you prepare to take the 350-401 Implementing Cisco Enterprise Network Core Technologies (ENCOR) exam CCNP training course details Who will benefit: Mid-level network engineers, Network administrators, Network support technicians, Help desk technicians. Prerequisites: Implementation of Enterprise LAN networks. Basic understanding of Enterprise routing and wireless connectivity, and Python scripting Duration 5 days CCNP training course content Cisco Enterprise Network Architecture: Access, distribution, core in the hierarchical network. Cisco Switching Paths: Switching mechanisms, TCAM, CAM, process switching, fast switching, and CEF. Implementing Campus LAN Connectivity: Troubleshoot L2 connectivity using VLANs and trunkingBuilding Redundant Switched Topology: STP Implementing Layer 2 Port Aggregation Troubleshoot link aggregation using Etherchannel EIGRP Implement and optimize OSPFv2/v3, including adjacencies, packet types, and areas, summarization, and route filtering for IPv4/v6 Implement EBGP interdomain routing, path selection, and single and dual-homed networkingImplementing Network Redundancy: HSRP and VRRP Implement static and dynamic NAT Virtualization Protocols and TechniquesVPNs and Interfaces: Overlay technologies such as VRF, GRE, VPN, and LISP Wireless Principles: RF, antenna characteristics, and wireless standards.Wireless Deployment: Models available, autonomous AP deployments and cloud-based designs within the centralized Cisco WLC architecture Wireless Roaming and Location ServicesWireless AP Operation: How APs communicate with WLCs to obtain software, configurations, and centralized managementWireless Client Authentication: EAP, WebAuth, and PSK wireless client authentication on a WLC. Troubleshoot wireless client connectivity issues using various available tools Troubleshoot networks using services such as NTP, SNMP, Cisco IP SLAs, NetFlow, and Cisco IOS EEM Explain network analysis and troubleshooting tools, which include show and debug commands, as well as best practices in troubleshootingMulticast Protocols: IGMP v2/v3, PIM DM/SM and RPs Introducing QoS: Concepts and features. Implementing Network Services: Secure administrative access for Cisco IOS devices using CLI access, RBAC, ACL, and SSH, and device hardening concepts to secure devices from less secure applications Using Network Analysis ToolsInfrastructure Security: Scalable administration using AAA and the local database, features and benefits Enterprise Network Security Architecture: VPNs, content security, logging, endpoint security, personal firewalls, and other security features. Automation and Assurance with Cisco DNA Center: Purpose, function, features, and workflow. Intent-Based Networking, for network visibility, proactive monitoring, and application experienceCisco SD-Access Solution: Nodes, fabric control plane, and data plane, VXLAN gatewaysCisco SD-WAN Solution: Components and features of Cisco SD-WAN solutions, including the orchestration, management, control, and data planesBasics of Python Programming: Python components and conditionals with script writing and analysis Network Programmability: NETCONF and RESTCONF APIs in Cisco DNA Center and vManage Labs: Investigate the CAM. Analyze CEF. Troubleshoot VLAN and Trunk Issues. Tuning STP and Configuring RSTP. Configure MSTP. Troubleshoot EtherChannel. Implement Multi-area OSPF. Implement OSPF Tuning. Apply OSPF Optimization. Implement OSPFv3. Configure and Verify Single-Homed EBGP. Implementing HSRP. Configure VRRP. Implement NAT. Configure and Verify VRF. Configure and Verify a GRE Tunnel. Configure Static VTI Point-to-Point Tunnels. Configure Wireless Client Authentication in a Centralized Deployment. Troubleshoot Wireless Client Connectivity Issues. Configure Syslog. Configure and Verify Flexible NetFlow. Configuring Cisco IOS EEM. Troubleshoot Connectivity and Analyze Traffic with Ping, Traceroute, and Debug. Configure and Verify Cisco IP SLAs. Configure Standard and Extended ACLs. Configure Control Plane Policing. Implement Local and Server-Based AAA. Writing and Troubleshooting Python Scripts. Explore JSON Objects and Scripts in Python. Use NETCONF Via SSH. Use RESTCONF with Cisco IOS XE.

Networking Microsoft Systems course description A hands-on course covering the network aspects of Microsoft systems. The course progresses from basic TCP/IP tools and configuration settings through to advanced security considerations finishing with an overview of Exchange and IIS. Hands on sessions are based on a choice of Windows Server 2003 or Windows 2000 server and Windows XP or Windows 2000 professional. Customised versions with other Microsoft platforms are also available. What will you learn Design networks with consideration for Microsoft issues such as logons. Design, configure and troubleshoot TCP/IP, DNS, WINS and DHCP. Configure security features such as PKI and IPSec. Describe the Windows TCP/IP implementation details. Networking Microsoft Systems course details Who will benefit: Anyone working with Microsoft systems. Prerequisites: TCP/IP foundation for engineers Supporting Windows ( XP or 2000 or 2003) Duration 5 days Networking Microsoft Systems course contents Configuring network cards PnP, resources, Ethernet cards, wireless cards, dial up networking, other cards, Ethernet settings, layer 2 QoS. Configuring and supporting IP Basic IP settings, advanced IP settings, advanced TCP settings, DrTCP and registry settings, security DHCP DHCP server, authorising the DHCP service, DHCP client, DHCP relays, Address pools, options, lease duration's, Integrating with DNS. Microsoft networking overview Workgroups and domains, Domain controllers, the logon process in a network, the role of Active Directory, synchronisation, protocol stacks and bindings. Accessing file and print resources Shared folders, permissions, network printers, browsing, NetBIOS, SMB. WINS Servers, clients, Client registration, renewing and releasing of names. NetBIOS node types. DNS1 Overview, Primary and secondary servers, DDNS, zones, resource records. The browser service Master, backup and other browser roles, elections, announcements, recovery from failure, Inter subnet browsing. TCP/IP implementation details Dead gateway detection, Multi homing, multicasting, MTU path discovery, registry settings, QOS and RSVP, Windows as a router, performance implications of Microsoft services. Internet Access Options, NAT, Firewall capabilities and Proxy server, Internet Authentication Service. Remote Access Installing, RAS servers. RAS process, protocols Security: PKI PPTP, L2TP, What is IPSec, configuring IPSec. Security: VPNs PPTP, L2TP, What is IPSec, configuring IPSec. Other Microsoft networking services & tools Netmeeting, instant messaging, white boarding, document collaboration, video conferencing Microsoft Exchange, IIS, Directory replication, SNMP, Net Monitor, integration with other platforms.

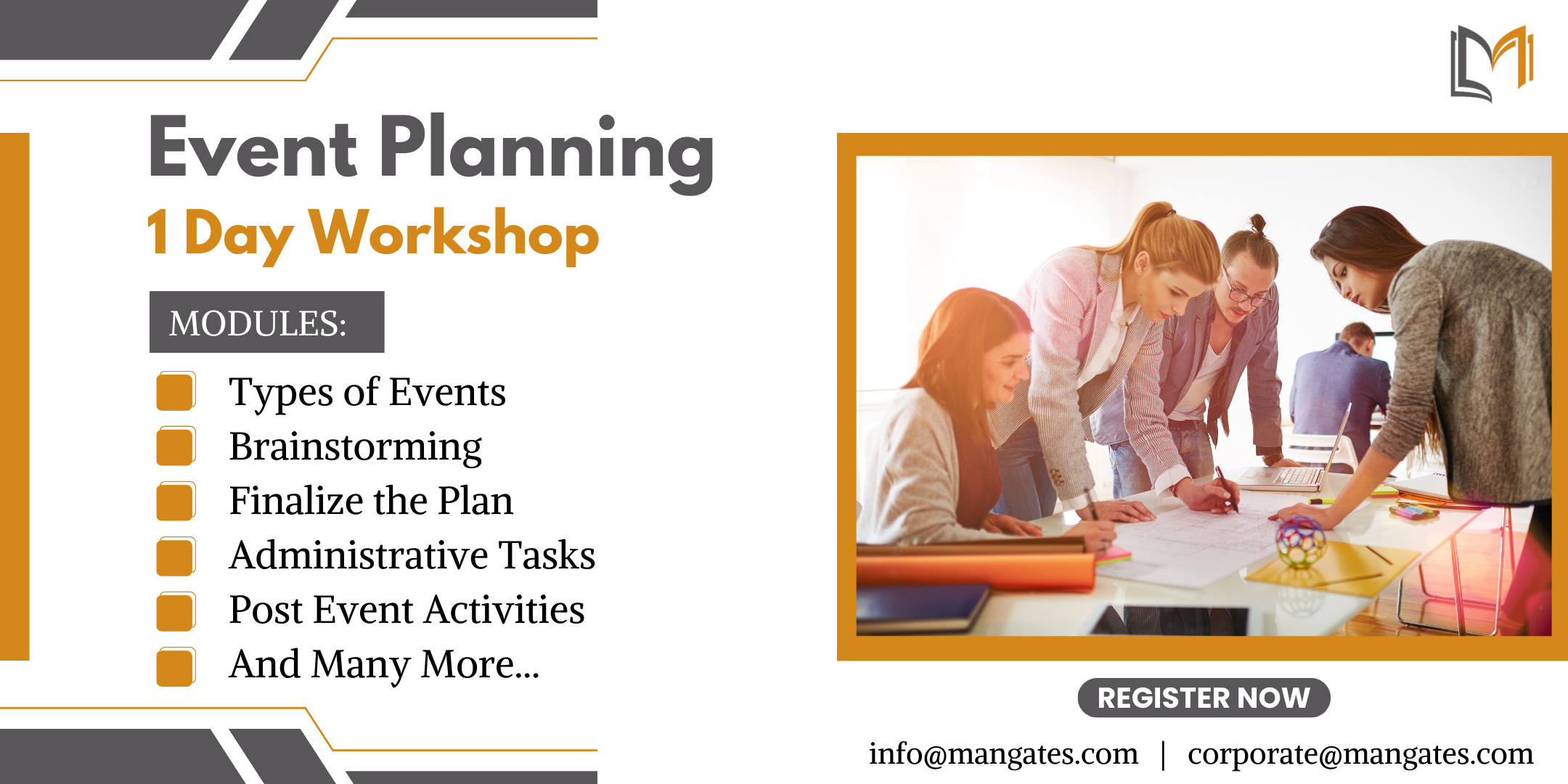
The Ultimate Guide to Event Planning - 1 Day Workshop in Bolton
By Mangates
Event Planning 1 Day Training in Bolton
LTE Architecture and Protocols course description This course provides a comprehensive tour of the LTE architecture along with services provided and the protocols used. What will you learn Describe the overall architecture of LTE. Explain the information flows through LTE. Describe the LTE security. Describe LTE mobility management. Recognise the next steps for LTE. LTE Architecture and Protocols course details Who will benefit: Anyone working with LTE. Prerequisites: Mobile communications demystified Duration 3 days LTE Architecture and Protocols course contents Introduction History, LTE key features. The 4G ITU process. The LTE 3GPP specifications. Specifications. System Architecture LTE hardware architecture. UE architecture and capabilities. E-UTRAN and eNB. EPC, MME functions, SGW, PGW and PCRF. System interfaces and protocol stacks. Example information flows. Dedicated and default bearers. EMM, ECM, RRC state diagrams. Radio transmission and reception OFDMA, SC-FDMA, MIMO antennas. Air interface protocol stack. Logical, transport and physical channels. Frame and slot structure, the resource grid. Resource element mapping of the physical channels and signals. Cell acquisition, data transmission and random access. MAC, RLC, PDCP protocols. LTE spectrum allocation. Power-on procedures Network and cell selection. RRC connection establishment. Attach procedure, including IP address allocation and default bearer activation. LTE detach procedure. Security in LTE networks LTE security features, identity confidentiality, ciphering and integrity protection. Architecture of network access security in LTE. Secure key hierarchy. Authentication and key agreement procedure. Security mode command procedure. Network domain security architecture. Security associations using IKE and IPSec. Mobility management RRC_IDLE, RRC_CONNECTED. Cell reselection, tracking area updates. Measurement reporting. X2 and S1 based handovers. Interoperation with UMTS, GSM and non-3GPP technologies such as cdma2000. QoS, policy control and charging QoS in LTE, EPS bearers, service data flows and packet flows. The architecture and signalling procedures for policy and charging control. Data transport using GPRS, differentiated services and MPLS. Offline and online charging in LTE. Delivery of voice and text messages over LTE Difficulties and solutions for Voice over LTE. Architecture and call setup procedures for circuit switched fallback. Architecture, protocols and call setup procedures in IP multimedia subsystem. Enhancements in release 9 LTE location services. Multimedia broadcast / multicast service and MBSFN. Cell selection, commercial mobile alert service. LTE Advanced and release 10 Impact of carrier aggregation on LTE air interface. Enhanced MIMO processing on uplink and downlink. Relaying. Release 11 and beyond. OAM and self organising networks Operation, administration, maintenance and provisioning for LTE. Self-configuration of base station parameters. Fractional frequency re-use, inter-cell interference co-ordination. Self-optimisation of base station procedures. Self-healing to detect and recover from faults.

Search By Location
- Security Courses in London
- Security Courses in Birmingham
- Security Courses in Glasgow
- Security Courses in Liverpool
- Security Courses in Bristol
- Security Courses in Manchester
- Security Courses in Sheffield
- Security Courses in Leeds
- Security Courses in Edinburgh
- Security Courses in Leicester
- Security Courses in Coventry
- Security Courses in Bradford
- Security Courses in Cardiff
- Security Courses in Belfast
- Security Courses in Nottingham
