- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
1783 Courses in Manchester
Snobby Dogs Salon Assistant Stylist Course
By Snobby Dogs Academy Ltd
This course is designed to provide a basic introduction to dog grooming, it is the building blocks for an excellent career in dog grooming providing both the practical skills and the theory behind dog grooming Dog Grooming Assistants course gives you the basic skills you need to start working in a dog grooming environment under supervision. THE COURSE WILL COVER Correct handling and lifting of dogs Health checking of a dog Basic first aid Preparing and grooming dogs prior to bathing Bathing and cleaning dogs Drying dogs and preparing their coats for styling De-shedding techniques Introduction to basic styling Scissoring foot shapes Nail and ear care Cleaning and maintaining equipment used for grooming Maintain the cleanliness and bio security of the animal care working environment in-line with health and safety Guidance in client relations and salon management Students will receive all course materials and it is recommended that students bring along a camera for before and after photographs as well as pens, high-lighters and notepads. It is highly recommended that upon completion of this course, you continue onto completing the 20 Day Commercial Stylist Course. As you will have already completed 8 days of training, we can offer you a fantastic discount on the remaining 12 days of training and it includes a Pet First Aid course and certificate. See below for full details.

Acrylic Painting Workshop - Autumn Toadstools with Helen of Evendawn Arts
5.0(82)By Phoenix Pottery and Art Studio
Join Helen of Evendawn Arts for this lovely seasonal Workshop. With a full drawing provided on speciality acrylic paper , there’s no need to worry about drawing your own toadstool. This frees you to simply paint this glowing autumnal scene. There will be some warm up practices first - trying different brushes and tools - and this will also be the time for mixing the paint colours for your project. You’ll have step by step guidance all the way through this painting, so you can relax and and have fun creating this beautiful seasonal picture. All levels of experience welcome including complete beginners. ( age 14 upwards) please don’t forget to bring something to carry home your finished project. A lidded tray or box would do. Acrylic paints are permanent when dried, so please wear appropriate clothing. Aprons are available or bring your own. Price includes all paints/materials.

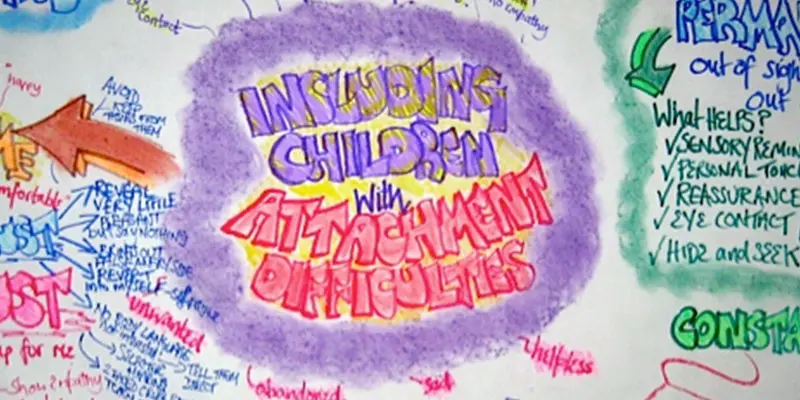
ATTACHMENT DIFFICULTIES: INCLUDING CHILDREN
By Inclusive Solutions
This is a practical ‘non medical’ day for front line practitioners working with children and young people with serious attachment issues arising from loss, trauma and abuse. We look at what Psychology may help us in our understanding of children who have faced issues with love and attachment. Splitting, handling projected feelings, constancy and permanence are explored. Online Course now available via Teachable Platform – Understanding Attachment Learn at your own pace… lots of text and video support Course Category Meeting emotional needs Behaviour and Relationships Inclusion Teaching and Learning Description This is a practical ‘non medical’ day for front line practitioners working with children and young people with serious attachment issues arising from loss, trauma and abuse. Drawing from the international research and literature and our own experience over many years as educational psychologists of the challenges of children with major social and emotional needs, we will explore together what the best practice can and could look like. We explore the language of attachment and outline very practical classroom strategies. We look at what Psychology may help us in our understanding of children who have faced issues with love and attachment. We explore the feelings of being on a desolate island of relational poverty or to imagine swimming with sharks. We explore the themes of violence, anxiety and experience of being a victim as young people grow older. We look at telling lies and explore how we can respectfully understand this. We reveal the new and innovative compass of vulnerability – the cognitive errors to which some are much more vulnerable. We look at triggers, self regulation and unpack a range of strategies. Transference and counter transference are examined along with splitting, handling projected feelings, constancy and permanence. We explore what young people with these difficulties really need from us. We also spend time looking at the emotional impact on practitioners working with children with such needs and what helps at an personal and team level. We can all do something – we do not have to wait for expert therapists to arrive! Testimonials Very moving presentation I will always try and think behind the behaviour now It had a huge impact on all levels We all seem to need it Belonging and feelings are so important Very user friendly Excellent! Learning Objectives Increased confidence regarding developing inclusive practice for children with serious attachment needs in mainstream schools Simple understandable explanation of attachment understood Access to a wider range of practical strategies to impact on social and behavioural needs Deeper understanding of core values surrounding inclusion of emotionally disabled children Opportunity to reflect on professional attitudes and behaviour towards parents and pupils with complex emotional needs New skills, scripts and processes to make inclusion successful Who Is It For ? Practitioners working in schools and other settings with children and young people of all ages Key workers Teaching Assistants with support roles Heads and deputies SENCOs Advanced skills teachers Primary and secondary classroom teachers Parents Local authority support services Course Content The course explores the questions : How can we start to develop an understanding of children with attachment needs? What is the true impact of loss, trauma and abuse? What else can we do to go about including high profile children or young people with challenging emotional needs? What useful psychological constructs can we use to guide us? This course also explores practical strategies and language for key adults rebuilding relationships with individual pupils. This is a participative day that aims to be explorative and practical. Opportunities to develop empathy with the children of concern will be created.
Auditing Computerised Systems
By Research Quality Association
Course Information Join our comprehensive three-day programme designed as an invaluable external training opportunity for auditors, audit programme managers, and individuals subject to audits. This course is tailored to foster a deep understanding and cultivate essential skills for auditing the validation of computer systems intended for GxP environments (GLP, GCP, GMP, GDP, GPvP). Commencing with an overview of regulatory prerequisites and the system life cycle, the course swiftly transitions to focus on the pragmatic aspects of auditing computer system validation. Experience a blend of presentations, interactive discussions, and immersive practical workshops throughout the duration of the course. Delegates will benefit from practical examples of how to understand the framework of applicable regulations and guidance. Apply risk management techniques to audit planning Plan and conduct computerised system audits Assess system validation documentation to verify compliance Evaluate data integrity and security issues Prepare for regulatory inspection. The course is structured to encourage delegates to: Discuss and develop ideas Solve specific problems Understand the vulnerabilities of computerised systems Learn how to create a compliance checklist Link system development with good business practice. Is this course for you? Auditors Audit programme managers Individuals subject to audits. Tutors Tutors will be comprised of (click the photos for biographies): Nichola Stevens Director and Principal Consultant, Nuncius Compliance Solutions Ltd Barry McManus Consultancy Partner, Empowerment Quality Engineering Ltd Programme Please note timings may be subject to alteration. Day 1 09:00 Welcome and Introductions 09:45 Why We Validate and Regulatory Trends 10:30 Break 10:45 Audit Overview, High Level Process and Scheduling 11:30 System Lifecycle 12:30 Lunch 13:15 Exercise 1 - Audit Scheduling 14:45 Exercise 1 - Feedback 15:15 Break 15:30 Validation Deliverables 16:30 Risk Assessments 17:30 Close of Day 1 Day 2 09:00 Supplier Assessment 10:30 Break 10:45 Exercise 2 - Planning a Supplier Audit 12:00 Exercise 2 - Feedback 12:30 Lunch 13:15 Exercise 3 - Auditing a Computerised System Validation Package 15:30 Break 15:45 Exercise 3 - Feedback 16:30 Change Control 17:15 Close of Day Day 3 09:00 Infrastructure Qualification 09:45 Maintaining a Validated State - Operational Processes 11:00 Break 11:15 Exercise 4 - Auditing Systems in Operational Use 12:45 Lunch 13:30 Exercise 4 - Feedback 14:15 Exercise 5 - Auditing Trail Review 15:30 Break 15:45 Exercise 5 - Feedback 16:15 Course Objectives Summary and Any Additional Questions 16:45 Close of Course Extra Information Face-to-face course Course Material Course material will be available in PDF format for delegates attending this course. The advantages of this include: Ability for delegates to keep material on a mobile device Ability to review material at any time pre and post course Environmental benefits – less paper being used per course. The material will be emailed in advance of the course and RQA will not be providing any printed copies of the course notes during the training itself. Delegates wishing to have a hard copy of the notes should print these in advance to bring with them. Alternatively delegates are welcome to bring along their own portable devices to view the material during the training sessions. Remote course Course Material This course will be run completely online. You will receive an email with a link to our online system, which will house your licensed course materials and access to the remote event. Please note this course will run in UK timezone. The advantages of this include: Ability for delegates to keep material on a mobile device Ability to review material at any time pre and post course Environmental benefits – less paper being used per course Access to an online course group to enhance networking. You will need a stable internet connection, a microphone and a webcam. CPD Points 19 Points Development Level Develop

Introduction to Computer Systems Validation
By Research Quality Association
Course Information Join our comprehensive three-day training programme tailored for individuals seeking a foundational grasp of computerised system validation. This course equips participants with essential knowledge to effectively validate systems within their respective organisations for utilisation in GxP (GLP, GCP, GMP, GDP, and GPvP) environments. Attendees will also gain proficiency in auditing validated computerised systems, ensuring compliance with pertinent GxP regulations. Commencing with an overview of regulatory prerequisites and the system life cycle, the course transitions into practical aspects, centered around validating computerised systems and conducting subsequent audits. Engage in a dynamic blend of presentations, interactive discussions, and hands-on practical workshops throughout the course. This course will provide delegates with an understanding of the computerised system validation process, including: Definition of end user requirements Risk management, including supplier assessment and techniques for audit planning Validation planning and reporting Linking system development with good business practices Formal testing and qualification Understanding of data integrity and security issues How to assess system validation documentation to verify compliance. Is this course for you? IT professionals new to implementing computerised systems into regulated environments Quality professionals who monitor or audit computerised systems System owners, end users, tester and project staff. Tutors Tutors will be comprised of (click the photos for biographies): Nichola Stevens Director and Principal Consultant, Nuncius Compliance Solutions Ltd Barry McManus Consultancy Partner, Empowerment Quality Engineering Ltd Programme Please note timings may be subject to alteration. Day 1 09:00 Welcome, Introduction and Course Objectives 09:45 Why Validate? Regulations and Guidance on Computerised System Validation Overview of the regulations and guidance applicable to CSV and their key expectations. 10:30 Break 10:45 The System Lifecycle The concept of the SLC and the key outputs from it. 12:00 Lunch 12:45 The Validation Process The approach to validation for different system types and a look at some of the key deliverables. 14:00 Project Introduction 14:15 Exercise 1 - User Requirements Capturing, agreeing and documenting the user requirements for a system. 15:15 Break 15:30 Exercise 1 - Feedback 16:00 Risk Management Risk management and its impact on validation. Identifying the deliverables required. Then group discussion on risk assessment for three systems. 17:00 Questions and Answers Answers to any outstanding questions from Day 1. 17:15 Close of Day Day 2 09:00 Supplier Assessment The different approaches to supplier assessment and the things to be considered when assessing a supplier. 10:15 Exercise 2 - Supplier Assessment Planning a vendor audit with a focus on the key validation deliverables. 11:00 Break 11:15 Exercise 2 - Feedback 11:45 Test Overview and Test Planning The different test phases, the purpose of each test phase and things to be considered when planning and reporting testing. 12:45 Lunch 13:30 Test Overview and Test Planning Continued. 14:15 Test Script Design, Execution and Review What a good test script looks like and the key things to consider when creating, executing and reviewing a test script. 15:30 Break 15:45 Exercise 3 - Creating a Test Script Create a test script based on user requirements created on Day 1. 17:15 Close of Day Day 3 09:00 Exercise 3 Feedback 09:30 Infrastructure Configuration and Qualification 10:30 Break 10:45 Validation Reporting Overview of the Validation Report and what should be included in it. 11:15 Maintaining the Validated State The procedures and records needed to ensure the system remains fit for purpose. 12:30 Lunch 13:15 Change Control Key concepts related to making changes to validated systems. 14:00 Data Integrity and Security How can we assure the integrity and security of our data. 15:15 Break 15:30 Course Objectives Summary and Panel Discussion A round up of key learning from the course. 17:00 Close of Course Extra Information Face-to-face course Course Material Course material will be available in PDF format for delegates attending this course. The advantages of this include: Ability for delegates to keep material on a mobile device Ability to review material at any time pre and post course Environmental benefits – less paper being used per course. The material will be emailed in advance of the course and RQA will not be providing any printed copies of the course notes during the training itself. Delegates wishing to have a hard copy of the notes should print these in advance to bring with them. Alternatively delegates are welcome to bring along their own portable devices to view the material during the training sessions. Remote course Course Material This course will be run completely online. You will receive an email with a link to our online system, which will house your licensed course materials and access to the remote event. Please note this course will run in UK timezone. The advantages of this include: Ability for delegates to keep material on a mobile device Ability to review material at any time pre and post course Environmental benefits – less paper being used per course Access to an online course group to enhance networking. You will need a stable internet connection, a microphone and a webcam. CPD Points 19 Points Development Level Develop

Microsoft Active Directory course description A thorough understanding of this system is essential for anyone managing enterprise MS networks. Essential theory is complimented with a high level of hands on practice allowing delegates to observe the idiosyncrasies of Active Directory and Group Policy at first hand. Delegates learn the fundamental theory of AD and progress onto building a multi-domain network in the classroom. The course includes troubleshooting methods, and essential maintenance procedures. This course is designed to teach you the skills needed for day to day management of these technologies. What will you learn Install AD on multiple PCs. Use the tools to create and manage objects. Create appropriate group policies to restrict selected user's desktops and network access. Install DNS to support Active Directory without loosing Internet Connectivity. Maintain and troubleshoot AD problems Backup Active Directory. Microsoft Active Directory course details Who will benefit: Technical staff working with AD based networks. Prerequisites: Supporting Windows server. Duration 3 days Microsoft Active Directory course contents Introduction to Active Directory Network authentication methods, Active Directory defined, AD naming conventions, network management with AD, AD structures: Domains, Organisational Units, Forests & Trees, Sites, The Global Catalogue. Windows 2003 new features, installing AD. Hands on Installing an AD network. Windows overview Management methods Server management tools, installing the additional tools, Terminal Server: Administration mode, Administrator accounts in AD, Local Security Policy. Hands on Install the management tools, Management using Terminal Services. Creating & Managing Objects (a quick look) AD management tools, AD users and computers, Creating & managing OUs, User Accounts and groups, controlling access to AD objects, moving objects, Publishing resources, locating objects in AD, delegating authority. Hands on Creating a control OU structure and delegating authority. Introduction to Group Policies What are Group Policies? Where Group Policy data is stored, security, Group Policy flow. Hands on Implementing Group Policies Working with Group Policies Local security templates, administrative templates, scripts, folder redirection, software deployment. Hands on Scripts, redirecting the start menu, creating a secure, robust desktop environment. Implementing DNS DNS basics, troubleshooting, implementing DNS zones. Hands on Building a unified DNS solution. Maintaining and managing the AD database AD support tools, database internal structure, replication, replication tools, Single Operations Masters, tools for maintenance, maintenance techniques, Backing up AD, Directory Services restore mode, NTDSUtil, Authoritative & non-authoritative restoration, rebuilding. Hands on NTDSUtil.

RF fundamentals training course description Radio Frequency engineering is an important yet often overlooked area in today's wireless world. This course provides a grounding in RF theory and practice for wireless, cellular and microwave systems. What will you learn Explain the basics of RF. Describe RF propagation and antenna principles. Calculate propagation losses and link budgets. Test RF systems. RF fundamentals training course details Who will benefit: Those working with wireless, cellular and microwave systems. Prerequisites: None. Duration 2 days RF fundamentals training course contents What is RF? Definition of RF, RF wave characteristics: Frequency, wavelength, power, phase, impedance, RF history, radio signals, frequency bands, safety issues, legal issues. RF systems Microwaves, cellular/mobile RF, WLANs, other fixed wireless networks, basic RF components. Hands on Building a basic WLAN network. RF system components Transmitters: Antennas: Isotropic, Dipole, how antennas achieve gain. Modulation Schemes, bandwidth, AM, FM, FSK, PSK, QAM, QPSK, interference, performance. Hands on Interference and performance. Multiple access schemes FDMA, CDMA, TDMA, CSMA/CA. Wireless systems Cellular (GSM, UMTS), Wifi, WiMax, others: GPS, DBS, RFID, radar, Bluetooth. Hands on cellular. Spread Spectrum technologies Spread spectrum benefits and disadvantages, how it works, Direct Sequence, Frequency Hopping, hybrids. RF propagation Models, link budget, Smith chart, RF matching with the Smith chart. cell capacity, tradeoffs: power vs. bandwidth, free space, reflection, diffraction, multipath cancellation, propagation prediction and measurement tools. Hands on Smith charts. RF testing Why power rather than voltage/current, units of power, dB and dBm power conversions. Test equipment: signal generators, power meters, network analysers, spectrum analysers. RF test setups: return loss, insertion loss. Hands on RF testing.

SAFe Agile Software Engineering: In-House Training
By IIL Europe Ltd
SAFe® Agile Software Engineering: In-House Training The introduction of Lean-Agile and DevOps principles and practices into software engineering has sparked new skills and approaches that help organizations deliver higher-quality, software-centric solutions faster and more predictably. This workshop-oriented course explores foundational principles and practices and how continuous flow of value delivery and built-in quality are enabled by XP technical practices, Behavioral-Driven Development (BDD), and Test-Driven Development (TDD). Attendees will learn proven practices to detail, model, design, implement, verify, and validate stories in the SAFe® Continuous Delivery Pipeline, as well as the practices that build quality into code and designs. Attendees will also explore how software engineering fits into the larger solution context and understand their role in collaborating on intentional architecture and DevOps. What you will Learn To perform the role of a SAFe® Agile Software Engineer, you should be able to: Define Agile Software Engineering and the underlying values, principles, and practices Apply the Test-First principle to create alignment between tests and requirements Create shared understanding with Behavior-Driven Development (BDD) Communicate with Agile modeling Design from context for testability Build applications with code and design quality Utilize the test infrastructure for automated testing Collaborate on intentional architecture and emergent design Apply Lean-Agile principles to optimize the flow of value Create an Agile Software Engineering plan Introduction to Agile Software Engineering Connecting Principles and Practices to Built-in Quality Accelerating Flow Applying Intentional Architecture Thinking Test-First Discovering Story Details Creating a Shared Understanding with Behavior-Driven Development (BDD) Communicating with Models Building Systems with Code Quality Building Systems with Design Quality Implementing with Quality

Personalised training for users of Dragon Professional Individual or Dragon Home.
By Neil Sleight
A step-by-step guide for Dragon users.

Neurodiversity Workshop Retaining: Reward, Change, Communication
By Mpi Learning - Professional Learning And Development Provider
A four-hour workshop on how to retain your talented Neurodiverse colleagues and ensure equality in employment opportunities.

Search By Location
- work Courses in London
- work Courses in Birmingham
- work Courses in Glasgow
- work Courses in Liverpool
- work Courses in Bristol
- work Courses in Manchester
- work Courses in Sheffield
- work Courses in Leeds
- work Courses in Edinburgh
- work Courses in Leicester
- work Courses in Coventry
- work Courses in Bradford
- work Courses in Cardiff
- work Courses in Belfast
- work Courses in Nottingham