- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
Writing Clear Business Communication: In-House Training
By IIL Europe Ltd
Writing Clear Business Communication: In-House Training This program is about learning about the writing process and covers the full spectrum of documents used when corresponding in the workplace. The ability to write effectively comes naturally to some people, but for the vast majority, it is a task often approached with a mixture of trepidation and dread. Effective writing seldom, if ever, 'magically materializes' on the spot. In reality, it is most often the product of planning, writing, and rewriting. This is why writing is called a process; it must go through a series of steps before it is clear and complete. This program is about learning about the writing process and covers the full spectrum of documents used when corresponding in the workplace. The ability to write effectively comes naturally to some people, but for the vast majority, it is a task often approached with a mixture of trepidation and dread. However, the ability to communicate in the written word, for whatever purpose, is an important part of our working and personal lives and can have a direct impact on our ability to persuade, gain commitment or agreement and enhance understanding. Good writing sounds like talking on paper, which is why this program is focused on getting the message across and achieving the desired results using the 'keep it simple and direct' approach. What you Will Learn At the end of this program, you will be able to: Write effective e-mails, letters, memos, and reports Clearly articulate the message Achieve desired results from correspondence Organize content for maximum impact Format for enhanced understanding Choose the appropriate communication medium for each document Revise documents to increase clarity and impact Foundations Concepts Business writing as a form of professional communication How business writing compares to other forms of writing Characteristics of good business writing Challenges with business writing The Project Environment Business writing in the project environment The concept of art, science, and optics of business writing Art Economy Precision Action Music Personality Science Purpose, simple, compound, and complex sentence structures Techniques to engage the reader Point of view: tone, attitude, and humor Organization: opening, body, and closing Support and coherence Optics Visual optics Sound optics Feel optics Effective optics Efficient optics Email Formal vs. informal emails Suggestions for improving email communication Instant and text messaging Reports Common types of reports created Formatting of reports Guidelines for meeting minutes Contracts Types of contracts Common agreements Procurement documents Templates, Forms, and Checklists Templates Forms Checklists Other Formatting Good Documentation Practices Good documentation practices Data integrity in business communication

Advanced RF training course description This course provides a follow on to our popular RF fundamentals course for those that need to know more. What will you learn Explain RF propagation Describe the importance of transmission lines in RF systems. Recognise the issues in RF systems. Describe transmission measurements. Advanced RF training course details Who will benefit: Those working with RF systems. Prerequisites: RF fundamentals. Duration 3 days Advanced RF training course contents RF propagation The Electromagnetic Spectrum, Electromagnetic Radiation, Spherical Wave Front, The Space Wave, Receive Antenna below the Horizon, Bending the Space Wave , Surface Wave Path, Tilting of Surface Wave, Conductivity, Layers of the Atmosphere, Variations of the Ionosphere, Variations caused by Solar Activity, Multi Hop Transmission, Classification of Radio Waves, Fading, Fading Reduction, Free Space Path Loss, Shadowing of Radio Wave, Signal Levels after Shadowing, Radio Waves as Wavelets, Fresnel Zone. Transmission Lines Transmission Line Construction, Primary Line Constants, 'T' Networks, Input Impedence, Lossless Unbalanced Line, Standing Waves, Open Circuit / Short Circuit Termination, Short Circuit Standing Waves, Open Circuit Standing Waves, Voltage Standing Wave Pattern, Short Circuit Termination, Open Circuit Termination, The Directional Coupler, Effect of E and M Coupling, Practical Reflectometer. Antenna Theory The Open Circuit Line, Dipole V/I Distribution, Polar Diagram, Power Pattern ½ Wave Dipole, Half Wave Dipole, Vehicle Mount, Centre Fed Whip Antenna, Antenna Beamwidth, The Yagi Array, Uda Yagi array, Antenna Characteristics, 6 Element Yagi Polar Diagram, Log Periodic Antenna, Helical Antenna. Microwave Dish Array, Typical Microwave Dish Antenna. Transmission Measurements Transmission Measurements, Effective Isotropic Radiated Power, Fade Margin. Noise Noise in Communications, Noise Voltage Equivalent Circuit. Satellite Communications Satellite Communications, Large Earth Station, The Satellite Payload, Geo Stationary Orbit, Basic Orbits, VSAT Terminal, Iridium Phone, The Space Segment, Satellite Footprint, Typical System Hardware. Mobile Communications Mobile Evolution, The Path to UMTS, Technologies Bit Rate and Mobility, Systems and Specifications, Wireless Networks, Diffraction, Multi Path Propagation, Loss Models, GSM Architecture, OSI Model - GSM, OSI Reference Model, OSI Layers.

4G training course description This course is designed to give the delegate an understanding of the technologies used within a 3G UMTS mobile network. During the course we will investigate the UMTS air interface and the use of Wideband-Code Division Multiple Access (WCDMA) to facilitate high speed data access, together with HSPA to offer mobile broadband services. We will describe the use of soft handover rather than hard handover procedures and soft capacity sharing. The course includes a brief exploration of the UMTS protocol stack and the use of PDP Context and QoS support features. What will you learn Explain the 3G UMTS architecture. Describe the role of a Drifting & Serving RNC. Explain the use of ARQ & HARQ for mobile broadband. Describe how IMS integrates into the architecture. Describe the use of Media Gateway Controllers. Identify the temporary identities used within 3G UMTS. 4G training course details Who will benefit: Anyone working within the telecommunications area, especially within the mobile environment. Prerequisites: Mobile communications demystified Telecommunications Introduction Duration 2 days 4G training course contents LTE Introduction The path to LTE, 3GPP. LTE to LTE advanced. LTE Architecture The core, Access, roaming. Protocols: User plane, Control plane. Example information flows. Bearer management. Spectrum allocation. LTE technologies Transmission, reception, OFDMA, multiple antenna, MIMO. LTE Air interface Air interface protocol stack. Channels, Resource Grid, cell acquisition. Up and downlink controls. Layer 2 protocols. Cell acquisition Power on, selecting networks and cells. RRC connection. Attach procedure. Mobility management Roaming, RRC_IDLE, RRC_CONNECTED, cell reselection, handover, interoperation with UMTS and GSM networks. Voice and text IMS, QoS, policy and charging.

Autism Awareness
By Prima Cura Training
This course explores Autism and the current body of thinking and knowledge around Autistic Spectrum Disorders. This enables learners to consider how to adapt their practice with useful strategies to better support an individual with autism.

LTE training course description This course is designed to give the delegate an understanding of the technologies used within a 3G UMTS mobile network. During the course we will investigate the UMTS air interface and the use of Wideband-Code Division Multiple Access (WCDMA) to facilitate high speed data access, together with HSPA to offer mobile broadband services. We will describe the use of soft handover rather than hard handover procedures and soft capacity sharing. The course includes a brief exploration of the UMTS protocol stack and the use of PDP Context and QoS support features. What will you learn Explain the 3G UMTS architecture. Describe the role of a Drifting & Serving RNC. Explain the use of ARQ & HARQ for mobile broadband. Describe how IMS integrates into the architecture. Describe the use of Media Gateway Controllers. Identify the temporary identities used within 3G UMTS. LTE training course details Who will benefit: Anyone working within the telecommunications area, especially within the mobile environment. Prerequisites: Mobile communications demystified Telecommunications Introduction Duration 2 days LTE training course contents LTE Introduction The path to LTE, 3GPP. LTE to LTE advanced. LTE Architecture The core, Access, roaming. Protocols: User plane, Control plane. Example information flows. Bearer management. Spectrum allocation. LTE technologies Transmission, reception, OFDMA, multiple antenna, MIMO. LTE Air interface Air interface protocol stack. Channels, Resource Grid, cell acquisition. Up and downlink controls. Layer 2 protocols. Cell acquisition Power on, selecting networks and cells. RRC connection. Attach procedure. Mobility management Roaming, RRC_IDLE, RRC_CONNECTED, cell reselection, handover, interoperation with UMTS and GSM networks. Voice and text IMS, QoS, policy and charging.

CWSP training course description A hands-on training course concentrating solely on WiFi security with an emphasis on the delegates learning the necessary knowledge and skills to pass the CWSP exam. The course progresses from simple authentication, encryption and key management onto in depth coverage of 802.X and EAP along with many other security solutions such as access control, intrusion prevention and secure roaming. What will you learn Demonstrate the threats to WiFi networks. Secure WiFi networks. Configure: WPA2 RADIUS 802.1x EAP Pass the CWSP exam. CWSP training course details Who will benefit: Technical network staff. Technical security staff. Prerequisites: Certified Wireless Network Associate. Duration 5 days CWSP training course contents WLAN Security overview Standards, security basics, AAA, 802.11 security history. Hands on WLAN connectivity. Legacy 802.11 security Authentication: Open system, shared key. WEP. VPNs. MAC filters. SSID segmentation, SSID cloaking. Hands on Analysing 802.11 frame exchanges, viewing hidden SSIDs. Encryption Basics, AES, TKIP, CCMP, WPA, WPA2. Hands on Decrypting 802.11 data frames. 802.11 layer 2 authentication 802.1X: Supplicant, Authenticator, Authentication server. Credentials. Legacy authentication. EAP, Weak EAP protocols, Strong EAP protocols: EAP -PEAP, EAP-TTLS, EAP-TLS, EAP-FAST. Hands on Analysing 802.1X/EAP frames. 802.11 layer 2 dynamic key generation Robust Security Network. Hands on Authentication and key management. SOHO 802.11 security WPA/WPA2 personal, Preshared Keys, WiFi Protected Setup (WPS). Hands on PSK mapping. WLAN security infrastructure DS, Autonomous APs, WLAN controllers, split MAC, mesh, bridging, location based access control. Resilience. Wireless network management system. RADIUS/LDAP servers, PKI, RBAC. Hands on 802.1X/EAP configuration. RADIUS configuration. 802.11 Fast secure roaming History, RSNA, OKC, Fast BSS transition, 802.11k. Hands on Roaming. Wireless security risks Rogue devices, rogue prevention. Eavesdropping, DOS attacks. Public access and hotspots. Hands on Backtrack. WiFi security auditing Layer 1 audit, layer 2 audit, pen testing. WLAN security auditing tools. WiFi security monitoring Wireless Intrusion Detection and Prevention Systems. Device classification, WIDS/WIPS analysis. Monitoring. 802.11w. Hands on Laptop spectrum analysers. VPNs, remote access, guest access Role of VPNs in 802.11, remote access, hotspots, captive portal. Wireless security policies General policy, functional policy, recommendations.

Network virtualization training course description This course covers network virtualization. It has been designed to enable network engineers to recognise and handle the requirements of networking Virtual Machines. Both internal and external network virtualization is covered along with the technologies used to map overlay networks on to the physical infrastructure. Hands on sessions are used to reinforce the theory rather than teach specific manufacturer implementations. What will you learn Evaluate network virtualization implementations and technologies. Connect Virtual Machines with virtual switches. Explain how overlay networks operate. Describe the technologies in overlay networks. Network virtualization training course details Who will benefit: Engineers networking virtual machines. Prerequisites: Introduction to virtualization. Duration 2 days Network virtualization training course contents Virtualization review Hypervisors, VMs, containers, migration issues, Data Centre network design. TOR and spine switches. VM IP addressing and MAC addresses. Hands on VM network configuration Network virtualization What is network virtualization, internal virtual networks, external virtual networks. Wireless network virtualization: spectrum, infrastructure, air interface. Implementations: Open vSwitch, NSX, Cisco, others. Hands on VM communication over the network. Single host network virtualization NICs, vNICs, resource allocation, vSwitches, tables, packet walks. vRouters. Hands on vSwitch configuration, MAC and ARP tables. Container networks Single host, network modes: Bridge, host, container, none. Hands on Docker networking. Multi host network virtualization Access control, path isolation, controllers, overlay networks. L2 extensions. NSX manager. OpenStack neutron. Packet walks. Distributed logical firewalls. Load balancing. Hands on Creating, configuring and using a distributed vSwitch. Mapping virtual to physical networks VXLAN, VTEP, VXLAN encapsulation, controllers, multicasts and VXLAN. VRF lite, GRE, MPLS VPN, 802.1x. Hands on VXLAN configuration. Orchestration vCenter, vagrant, OpenStack, Kubernetes, scheduling, service discovery, load balancing, plugins, CNI, Kubernetes architecture. Hands on Kubernetes networking. Summary Performance, NFV, automation. Monitoring in virtual networks.

LTE Architecture and Protocols course description This course provides a comprehensive tour of the LTE architecture along with services provided and the protocols used. What will you learn Describe the overall architecture of LTE. Explain the information flows through LTE. Describe the LTE security. Describe LTE mobility management. Recognise the next steps for LTE. LTE Architecture and Protocols course details Who will benefit: Anyone working with LTE. Prerequisites: Mobile communications demystified Duration 3 days LTE Architecture and Protocols course contents Introduction History, LTE key features. The 4G ITU process. The LTE 3GPP specifications. Specifications. System Architecture LTE hardware architecture. UE architecture and capabilities. E-UTRAN and eNB. EPC, MME functions, SGW, PGW and PCRF. System interfaces and protocol stacks. Example information flows. Dedicated and default bearers. EMM, ECM, RRC state diagrams. Radio transmission and reception OFDMA, SC-FDMA, MIMO antennas. Air interface protocol stack. Logical, transport and physical channels. Frame and slot structure, the resource grid. Resource element mapping of the physical channels and signals. Cell acquisition, data transmission and random access. MAC, RLC, PDCP protocols. LTE spectrum allocation. Power-on procedures Network and cell selection. RRC connection establishment. Attach procedure, including IP address allocation and default bearer activation. LTE detach procedure. Security in LTE networks LTE security features, identity confidentiality, ciphering and integrity protection. Architecture of network access security in LTE. Secure key hierarchy. Authentication and key agreement procedure. Security mode command procedure. Network domain security architecture. Security associations using IKE and IPSec. Mobility management RRC_IDLE, RRC_CONNECTED. Cell reselection, tracking area updates. Measurement reporting. X2 and S1 based handovers. Interoperation with UMTS, GSM and non-3GPP technologies such as cdma2000. QoS, policy control and charging QoS in LTE, EPS bearers, service data flows and packet flows. The architecture and signalling procedures for policy and charging control. Data transport using GPRS, differentiated services and MPLS. Offline and online charging in LTE. Delivery of voice and text messages over LTE Difficulties and solutions for Voice over LTE. Architecture and call setup procedures for circuit switched fallback. Architecture, protocols and call setup procedures in IP multimedia subsystem. Enhancements in release 9 LTE location services. Multimedia broadcast / multicast service and MBSFN. Cell selection, commercial mobile alert service. LTE Advanced and release 10 Impact of carrier aggregation on LTE air interface. Enhanced MIMO processing on uplink and downlink. Relaying. Release 11 and beyond. OAM and self organising networks Operation, administration, maintenance and provisioning for LTE. Self-configuration of base station parameters. Fractional frequency re-use, inter-cell interference co-ordination. Self-optimisation of base station procedures. Self-healing to detect and recover from faults.

M.D.D M.D.D SOCIAL ANXIETY COURSE PACKAGE (SELF IMPROVEMENT)
4.9(27)By Miss Date Doctor Dating Coach London, Couples Therapy
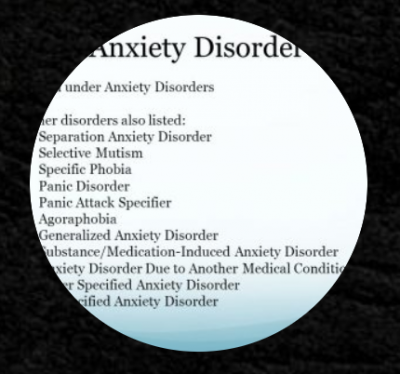
Social anxiety test Emotional intelligence training Self-regulation training Self-improvement coaching Confidence building Social skills OCD Resolving social phobia Addressing intense anxiety issues Social anxiety disorder Addressing issues in the anxiety spectrum Exposure hierarchy therapy Objective goals Guidance and support Addressing pain points Social anxiety disorder exercises Homework and self-help guide (dating advice and relationship advice optional) 6 sessions https://relationshipsmdd.com/product/m-d-d-social-anxiety-course-package/
Search By Location
- Spectrum Courses in London
- Spectrum Courses in Birmingham
- Spectrum Courses in Glasgow
- Spectrum Courses in Liverpool
- Spectrum Courses in Bristol
- Spectrum Courses in Manchester
- Spectrum Courses in Sheffield
- Spectrum Courses in Leeds
- Spectrum Courses in Edinburgh
- Spectrum Courses in Leicester
- Spectrum Courses in Coventry
- Spectrum Courses in Bradford
- Spectrum Courses in Cardiff
- Spectrum Courses in Belfast
- Spectrum Courses in Nottingham
