- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
83 Courses in Belfast
Security+ training course description A hands on course aimed at getting delegates successfully through the CompTia Security+ examination. What will you learn Explain general security concepts. Describe the security concepts in communications. Describe how to secure an infrastructure. Recognise the role of cryptography. Describe operational/organisational security. Security+ training course details Who will benefit: Those wishing to pass the Security+ exam. Prerequisites: TCP/IP foundation for engineers Duration 5 days Security+ training course contents General security concepts Non-essential services and protocols. Access control: MAC, DAC, RBAC. Security attacks: DOS, DDOS, back doors, spoofing, man in the middle, replay, hijacking, weak keys, social engineering, mathematical, password guessing, brute force, dictionary, software exploitation. Authentication: Kerberos, CHAP, certificates, usernames/ passwords, tokens, biometrics. Malicious code: Viruses, trojan horses, logic bombs, worms. Auditing, logging, scanning. Communication security Remote access: 802.1x, VPNs, L2TP, PPTP, IPsec, RADIUS, TACACS, SSH. Email: S/MIME, PGP, spam, hoaxes. Internet: SSL, TLS, HTTPS, IM, packet sniffing, privacy, Javascript, ActiveX, buffer overflows, cookies, signed applets, CGI, SMTP relay. LDAP. sftp, anon ftp, file sharing, sniffing, 8.3 names. Wireless: WTLS, 802.11, 802.11x, WEP/WAP. Infrastructure security Firewalls, routers, switches, wireless, modems, RAS, PBX, VPN, IDS, networking monitoring, workstations, servers, mobile devices. Media security: Coax, UTP, STP, fibre. Removable media. Topologies: Security zones, DMZ, Intranet, Extranet, VLANs, NAT, Tunnelling. IDS: Active/ passive, network/host based, honey pots, incident response. Security baselines: Hardening OS/NOS, networks and applications. Cryptography basics Integrity, confidentiality, access control, authentication, non-repudiation. Standards and protocols. Hashing, symmetric, asymmetric. PKI: Certificates, policies, practice statements, revocation, trust models. Key management and certificate lifecycles. Storage: h/w, s/w, private key protection. Escrow, expiration, revocation, suspension, recovery, destruction, key usage. Operational/Organisation security Physical security: Access control, social engineering, environment. Disaster recovery: Backups, secure disaster recovery plans. Business continuity: Utilities, high availability, backups. Security policies: AU, due care, privacy, separation of duties, need to know, password management, SLAs, disposal, destruction, HR policies. Incident response policy. Privilege management: Users, groups, roles, single sign on, centralised/decentralised. Auditing. Forensics: Chain of custody, preserving and collecting evidence. Identifying risks: Assets, risks, threats, vulnerabilities. Role of education/training. Security documentation.

CWDP training course description The CWDP course consists of instructor-led training applicable to the design of wireless LANs using the latest technologies including 802.11n and 802.11ac. The course goes in-depth into the design process and provides attendees with the knowledge needed to plan, deploy and test modern 802.11-based networks. It also prepares students for the CWDP examination. Students who complete the course will acquire the necessary skills for preparing, planning performing and documenting site surveys and wireless LAN design procedures. What will you learn Design enterprise WiFi networks. Select appropriate antennas and Access points. Perform site surveys. Describe the security requirements required for enterprise networks. Test, validate and troubleshoot installations. CWDP training course details Who will benefit: Anyone looking for the skills to analyze, troubleshoot, and optimize any enterprise level Wi-Fi network, no matter which brand of equipment your organization deploys. Anyone looking to become a CWNP. Prerequisites: CWNA Duration 5 days CWDP training course contents WLAN design overview Importance of good design, Impact of bad design, Design process, Design skills, Design toolkit. Requirements analysis Pre-planning, Customer interaction, Requirements gathering, Discovering existing systems, Documenting the environment, Defining constraints, Creating documentation. Designing for clients and applications Client Device types, Application types, Application-specific design, High density design issues. Designing for industry Standard corporate networks, Industry-specific designs, Government, Healthcare, Hospitality, Retail, Public hotspots, Transportation, Mobile offices, Outdoor and mesh, Remote networks and branch offices, Last-miles / ISP and bridging. Vendor selection processes Defining vendor issues, Operational planes, Design models, Understanding architectures. Radio Frequency (RF) planning RF spectrum, RF behaviors, Modulation and coding schemes, RF accessories, Throughput factors. WLAN hardware selection Antennas, 802.11n and antennas, Choosing Aps, Powering Aps. Site surveys Site survey tools, Site survey preparation, Predictive site surveys, Manual site surveys, Site survey principles and processes. Designing for Quality of Service (QoS) QoS overview, QoS application points, Roaming support. Designing for security Bad security, Authentication solutions, Encryption solutions, Security best practices, Intrusion prevention. Installation testing, validation and troubleshooting Network health status, Troubleshooting and validation process, Troubleshooting and validation tools, Common problems. Hands-on lab exercises Hands-on labs depend on the audience and can include use of: Spectrum analyzers, Protocol analyzers, Site Survey software, Diagramming software, Various wireless access points, Various wireless adapters and antennas.

M.D.D I LET MY PARTNERS TREAT ME BADLY PACKAGE (SINGLES)
4.9(27)By Miss Date Doctor Dating Coach London, Couples Therapy
Confidence Training Emotional Intelligence Training Dating Coach Support Daily Social skills examination Dating history analysis Red flag Training and Dating Coach Self-assessment and analysis Insecurities and pinpoint dating issues and problems 4 weeks of coaching Overview of dating skills Dating advice for singles https://relationshipsmdd.com/product/i-let-my-partners-treat-me-badly-package/

Management of Risk (M_o_R) Foundation: In-House Training
By IIL Europe Ltd
Management of Risk (M_o_R®) Foundation: In-House Training This M_o_R® Foundation course prepares learners to demonstrate knowledge and comprehension of the four elements of the M_o_R framework: Principles, Approach, Processes, Embedding and Reviewing and how these elements support corporate governance. The M_o_R Foundation Course is also a prerequisite for the M_o_R Practitioner qualification. What you will Learn At the end of the M_o_R Foundation course, participants will gain competencies in and be able to: Describe the key characteristics of risk and the benefits of risk management List the eight M_o_R Principles List and describe the use of the key M_o_R Approach documents Create Probability and Impact scales Define and distinguish between risks and issues Create a Risk Register Create a Stakeholder map Identify the key roles in risk management Use the key techniques and describe specialisms in risk management Undertake the M_o_R Foundation examination Introduction Introduction to the M_o_R course What is a risk? What is risk management? Why is risk management so important? Basic risk definitions The development of knowledge about risk management Corporate governance and internal control Where and when should risk management be applied? M_o_R Principles The purpose of M_o_R principles Aligns with objectives Fits the context Engages stakeholders Provides clear guidance Informs decision-making Facilitates continual improvement Creates a supportive culture Achieves measurable value Risk management maturity models M_o_R Approach Relationship between the documents Risk management policy Risk management process guide Risk management strategy Risk register Issue register Risk response plan Risk improvement plan Risk communications plan M_o_R Process Common process barriers Identify contexts Identify the risks Assess estimate Assess evaluate Plan Implement Communication throughout the process M_o_R Perspectives Strategic perspective Program perspective Project perspective Operational perspective Risk Specialisms Business continuity management Incident and crisis management Health and Safety management Financial risk management Environmental risk management Reputational risk management Contract risk management

OSPF training course description A detailed hands on examination of OSPF. Hands on sessions are used to reinforce the theory rather than teach specific manufacturer equipment. The course starts with a recap of reading routing tables and then jumps straight in with simple OSPF configuration. OSPF features are then studied and configured before moving onto how OSPF works within an area. Multi area OSPF is then studied before looking at OSPF operation in detail by analysing OSPF packets. Finally areas are covered again in more detail followed by troubleshooting. What will you learn Design OSPF networks. Design IP addressing schemes suitable for route summarisation. Troubleshoot OSPF networks. Describe the operation of OSPF. OSPF training course details Who will benefit: Technical staff working with OSPF. Prerequisites: TCP/IP Foundation for engineers Duration 3 days OSPF training course contents Basic routing and OSPF Reading routing tables, routing protocols, What is OSPF? Process IDs, passive interfaces. Hands on Simple OSPF configuration. OSPF History of OSPF, metrics, costs, convergence, Distance Vector vs. Link state routing protocols, IGPs, classless, OSPF features, load sharing, per packet/destination, OSPF authentication. Hands on Configuring OSPF features. OSPF within an area How OSPF works, LSDB, LSDB benefits and disadvantages, LSA types, Type 1 and 2, LSA propagation, router IDs, hellos, configuring hellos, the exchange protocol. Hands on Investigating OSPF structures. Areas Scalability, why areas? Area IDs, area 0, ABRs, ABR resilience, areas & LSDBs, areas & LSAs, Type 3 LSAs, virtual links. Hands on Multi area OSPF. Redistribution Multiple routing protocols, common scenarios, routing distance, External LSAs, E1 and E2. Type 4 LSAs. OSPF and default routes. Hands on Configuring static route redistribution. Route aggregation Route summarisation. How to aggregate, ABR summarisation, ASBR summarisation. Hands on OSPF address summarisation. OSPF packet formats OSPF packets, protocol stack, OSPF stages, packet flows, packet types, the OSPF header, multicasts, Hello, DDB, LS request, LS update, LS ACK, LSA header, LSA formats, neighbours, neighbour states, DRs, adjacencies, BDRs, DR election. Hands on Analysing OSPF packets, troubleshooting. OSPF network types BMA, NBMA, Point to point links. Hands on Configuring OSPF over Frame Relay. OSPF stub areas LSA types, area types, area architecture, stub areas, default routes, benefits and disadvantages of stub areas, TSSAs, NSSAs, Type 7 LSAs. Hands on Stub and TSSA configuration. The OSPF MIB SNMP overview, MIB 2, the OSPF MIB, OSPF MIB groups, useful objects, OSPF traps. Hands on the OSPF MIB. troubleshooting. Summary RFCs, OSPF design guidelines. OSPF variants (appendix) OSPF on demand, MOSPF, multicast overview, Type 6 LSAs, OSPF for IPv6 (OSPFv3).

An Understanding of Gastrostomy Tube Care and Safe Use
By Guardian Angels Training
Gain comprehensive knowledge and practical skills for safe gastrostomy tube care with our course. Learn techniques, considerations, and patient care.

Management of Value (MoV) Practitioner: In-House Training
By IIL Europe Ltd
Management of Value (MoV®) Practitioner: In-House Training This interactive MoV® Practitioner course provides a modular and case-study-driven approach to learning Management of Value (MoV). The core knowledge is structured and comprehensive; and well-rounded modules cover the methodology and various techniques. A case study is used to help appreciate the relevance of MoV in its practical application. What you will Learn The MoV Practitioner Course prepares you for the MoV Practitioner exam. Individuals certified at the MoV Practitioner level will be able to: Apply Management of Value (MoV) principles, processes and techniques, and advocate the benefits of this application appropriately to the senior Management. Develop a plan of MoV activities for the whole lifecycle of small and large projects and programs. Plan an MoV study, tailoring it to particular projects or programs and developing practical study or workshop handbooks as required. Understand and articulate value in relation to organizational objectives. Prioritize value drivers using function analysis and use these to demonstrate how value might be improved. Quantify monetary and non-monetary value using the Value Index, Value Metrics and the Value for Money ratio. Describe and comment on the application of various techniques relevant to MoV. Monitor improvements in value realized throughout a project lifecycle and capture learning which can be transferred to future projects. Offer suggestions and guidance about embedding MoV into an organization, including policy issues, undertake a health check, assess maturity and competence, and provide guidance on typical roles and responsibilities. Understand and articulate the use of MoV within other Best Management Practice methods and its contributions to them Benefits of Taking This Course Upon successful completion of this course, you will be able to: Organise and contribute constructively to a Management of Value (MoV) Study Demonstrate a knowledge of MoV principles, processes, approach, and environment Analyse a company, programme or project to establish its organisational value includes identification and weighting of Value Drivers Pass the AXELOS Practitioner Examination Function Analysis Customer FAST Diagram Value Tree Development Weighting Attributes Paired Comparisons Developing a Value Profile Developing a Value Index Value for Money Ratio Stimulating Innovation Value Engineering Option Evaluation and Selection Evaluation Matrix Value and Value for Money Timing and Planning Teams and Stakeholders MoV in the Organization Integrating with Best Management Practice Relationship between Process and Approach

NEBOSH Health and Safety Management for Construction (UK) is guided by legislation but focussed on best practice. With an emphasis on practical application, successful learners will be able to: • Recognise, assess and control a range of common construction hazards • Develop safe systems of work • Take part in incident investigations • Advise on the roles, competencies and duties under construction legislation • Positively influence health and safety culture • Confidently challenge unsafe behaviours • Help manage contractors.
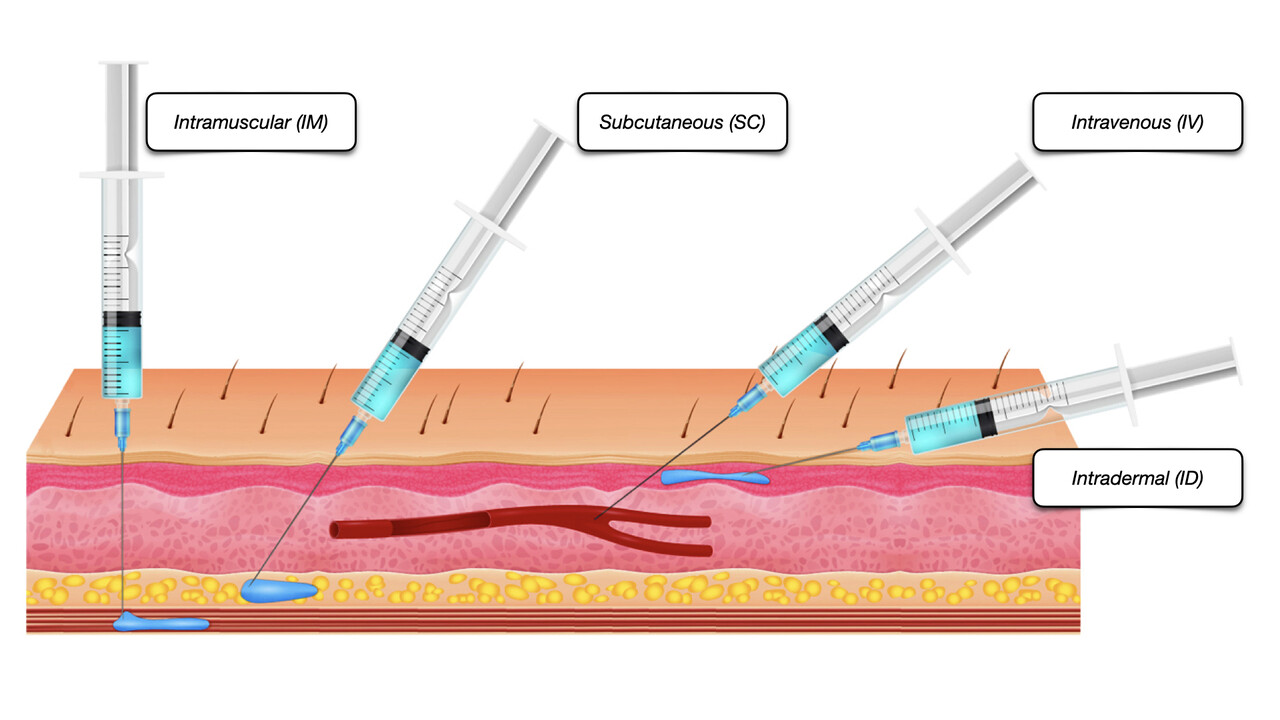
An Understanding of Injectable LHRH agonists
By Guardian Angels Training
Gain comprehensive knowledge on injectable LHRH agonists with our course. Learn about mechanisms, clinical applications, administration techniques, and more.
Search By Location
- Examination Courses in London
- Examination Courses in Birmingham
- Examination Courses in Glasgow
- Examination Courses in Liverpool
- Examination Courses in Bristol
- Examination Courses in Manchester
- Examination Courses in Sheffield
- Examination Courses in Leeds
- Examination Courses in Edinburgh
- Examination Courses in Leicester
- Examination Courses in Coventry
- Examination Courses in Bradford
- Examination Courses in Cardiff
- Examination Courses in Belfast
- Examination Courses in Nottingham