- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
25252 Courses delivered Online
This half-day Suicide First Aid Lite training course gives learners the knowledge and tools to understand that suicide is one of the most preventable deaths and some basic skills can help someone with thoughts of suicide stay safe from their thoughts and stay alive.
Introduction to Logistics and Supply Chain Management
By Online Training Academy
Are you ready to delve into the dynamic world of logistics and supply chain management? Our comprehensive course is designed to equip you with the essential knowledge and skills to excel in this critical field. Whether you're new to logistics or looking to enhance your existing expertise, this course is your gateway to mastering the fundamentals. Key Features: CPD Certified Free Certificate from Reed CIQ Approved Developed by Specialist Lifetime Access In this course, learners delve into the world of managing goods and materials effectively. They start by understanding the concept of inventory and its significance in supply chains. The course covers the processes of receiving and validating inventory, ensuring goods are correctly accounted for upon arrival. Setting up a warehouse is explored, highlighting how layout and organization impact efficiency. Learners also discover methods for identifying demand, crucial for planning and meeting customer needs. The outbound process, focusing on shipping goods to customers, is detailed, emphasizing timely and accurate order fulfillment. Maintaining inventory accuracy is stressed throughout, teaching techniques to prevent discrepancies. Finally, learners explore the key players in logistics and supply chains, understanding the roles and interactions that ensure smooth operations. This course equips learners with practical knowledge essential for effective management within logistics and supply chain environments. Course Curriculum Module 01: What is Inventory Module 02: The Receiving Process and Validating Inventory Module 03: Setting up the Warehouse Module 04: Identifying Demand Module 05: The Outbound Process Module 06: Maintaining Inventory Accuracy Module 07: Key Players Learning Outcomes: Define inventory and its role in supply chain management efficiency. Describe procedures for receiving and verifying incoming inventory accurately. Outline steps involved in warehouse setup and layout optimization. Analyze methods for forecasting and identifying customer demand patterns. Explain the process of preparing and shipping orders to customers. Implement techniques to ensure ongoing accuracy of inventory records. CPD 10 CPD hours / points Accredited by CPD Quality Standards Introduction to Logistics and Supply Chain Management 49:51 1: Module 01: What is Inventory 11:34 2: Module 02: The Receiving Process and Validating Inventory 04:35 3: Module 03: Setting up the Warehouse 05:48 4: Module 04: Identifying Demand 05:36 5: Module 05: The Outbound Process 07:19 6: Module 06: Maintaining Inventory Accuracy 06:16 7: Module 07: Key Players 07:43 8: CPD Certificate - Free 01:00 Who is this course for? Individuals interested in logistics and supply chain management principles. Professionals seeking foundational knowledge in inventory management practices. Students aiming to understand warehouse operations and inventory control. Entry-level employees in retail or distribution sectors. Managers looking to enhance their understanding of supply chain logistics. Career path Warehouse Manager Inventory Control Coordinator Logistics Analyst Supply Chain Coordinator Procurement Officer Distribution Manager Certificates Digital certificate Digital certificate - Included Reed Courses Certificate of Completion Digital certificate - Included Will be downloadable when all lectures have been completed.

Introduction to Logistics and Supply Chain Management
By Online Training Academy
Are you ready to delve into the dynamic world of logistics and supply chain management? Our comprehensive course is designed to equip you with the essential knowledge and skills to excel in this critical field. Whether you're new to logistics or looking to enhance your existing expertise, this course is your gateway to mastering the fundamentals. Key Features: CPD Certified Free Certificate from Reed CIQ Approved Developed by Specialist Lifetime Access In this course, learners delve into the world of managing goods and materials effectively. They start by understanding the concept of inventory and its significance in supply chains. The course covers the processes of receiving and validating inventory, ensuring goods are correctly accounted for upon arrival. Setting up a warehouse is explored, highlighting how layout and organization impact efficiency. Learners also discover methods for identifying demand, crucial for planning and meeting customer needs. The outbound process, focusing on shipping goods to customers, is detailed, emphasizing timely and accurate order fulfillment. Maintaining inventory accuracy is stressed throughout, teaching techniques to prevent discrepancies. Finally, learners explore the key players in logistics and supply chains, understanding the roles and interactions that ensure smooth operations. This course equips learners with practical knowledge essential for effective management within logistics and supply chain environments. Course Curriculum Module 01: What is Inventory Module 02: The Receiving Process and Validating Inventory Module 03: Setting up the Warehouse Module 04: Identifying Demand Module 05: The Outbound Process Module 06: Maintaining Inventory Accuracy Module 07: Key Players Learning Outcomes: Define inventory and its role in supply chain management efficiency. Describe procedures for receiving and verifying incoming inventory accurately. Outline steps involved in warehouse setup and layout optimization. Analyze methods for forecasting and identifying customer demand patterns. Explain the process of preparing and shipping orders to customers. Implement techniques to ensure ongoing accuracy of inventory records. CPD 10 CPD hours / points Accredited by CPD Quality Standards Introduction to Logistics and Supply Chain Management 49:51 1: Module 01: What is Inventory 11:34 2: Module 02: The Receiving Process and Validating Inventory 04:35 3: Module 03: Setting up the Warehouse 05:48 4: Module 04: Identifying Demand 05:36 5: Module 05: The Outbound Process 07:19 6: Module 06: Maintaining Inventory Accuracy 06:16 7: Module 07: Key Players 07:43 8: CPD Certificate - Free 01:00 Who is this course for? Individuals interested in logistics and supply chain management principles. Professionals seeking foundational knowledge in inventory management practices. Students aiming to understand warehouse operations and inventory control. Entry-level employees in retail or distribution sectors. Managers looking to enhance their understanding of supply chain logistics. Career path Warehouse Manager Inventory Control Coordinator Logistics Analyst Supply Chain Coordinator Procurement Officer Distribution Manager Certificates Digital certificate Digital certificate - Included Reed Courses Certificate of Completion Digital certificate - Included Will be downloadable when all lectures have been completed.
Specialised techniques and skills associated with neonatal and paediatric blood draws Nationally Recognised Qualification OCN Accredited - Level 3 (advanced) CPD Accredited - The CPD Certification Service Follow-on from Introduction to Phlebotomy Course Complements our Advanced Phlebotomy Course (Level 4 - FDSc level) Expand your horizons and add new skills Covers neonates, infants and child draws Legal framework and consenting Download a certificate on completion of your online course FOLLOWS ON FROM INTRODUCTION TO PHLEBOTOMY COURSE BUT ALSO OPEN TO ALL APPLICANTS

Lead Disaster Recovery Manager
By Training Centre
After mastering all the necessary concepts of Disaster Recovery processes, you can sit for the exam and gain the "Certified Lead Disaster Recovery Manager' credential. By holding this Certificate, you will be able to demonstrate that you have the practical knowledge and professional capabilities to support and lead Disaster Recovery teams in implementing Disaster Recovery strategies based on best practices. About This Course Learning objectives Acknowledge the correlation between Disaster Recovery, Business Continuity Management, Information Security and other IT areas and frameworks Master the concepts, approaches, methods and techniques used for the implementation and effective management of a Disaster Recovery Plan Learn how to interpret the ICT Disaster Recovery strategies in the specific context of an organization Learn how to support an organization to effectively plan, implement, manage, monitor and maintain DR services based on best practices Acquire the expertise to advise an organization in implementing an effective Disaster Recovery Plan based on best practices Educational approach This training is based on both theory and best practices used in the implementation and management of a DR plan Lecture sessions are illustrated with examples based on case studies Practical exercises are based on a case study which includes role playing and discussions Practice tests are similar to the Certification Exam Course Content Day 1: Introduction to Disaster Recovery and initiation of a DR plan Day 2: Risk Mitigation Strategies and Disaster Recovery Planning Day 3: Disaster Recovery facilities, services, recovery sites, response and activation Day 4: DRP testing, monitoring, measurement and continuous improvement; the examination Accreditation Prerequisites A foundational understanding of Disaster Recovery Services and knowledge of management principles, concepts and strategies. Assessment The exam for this course consists of 12 essay type questions, to be completed within the 150 minute timeframe and achieving the 70% pass mark. Exam results are provided within 24 hours. What's Included? Certification fees are included on the exam price Training material containing over 450 pages of information and practical examples will be distributed A participation certificate of 31 CPD (Continuing Professional Development) credits will be issued In case of exam failure, you can retake the exam within 12 months for free Provided by This course is Accredited by NACS and Administered by the IECB. Who Should Attend? Information Security Managers Incident Managers Helpdesk Managers Executives with Governance concerns

Autodesk 3ds max Project based Training 1-2-1 Live online or Face to Face.
By Real Animation Works
3ds max face to face training customised and bespoke. Live online or Face to Face.

Boost Your Career By Enrolling In This Cycling Bundle To Overcome Your Challenges! Get a Free 1 QLS Endorsed Certificate Course with 10 Additional CPD QS Accredited Bundle Courses In A Single Payment. If you wish to gain a solid and compact knowledge of Cycling and boost your career, then take a step in the right direction with this industry-standard, comprehensive Cycling bundle of courses, which are well organised. This Cycling bundle package includes 1 Premium, The Quality Licence Scheme-endorsed course, 10 additional CPDQS Accredited Certificate courses, with expert assistance, and a FREE courses assessment included. Learn a range of in-demand technical skills to help you progress in your career with 12 months of unlimited access to this bundle of courses. If you enrol in this Cycling package, you will not be charged any extra fees. This Cycling Bundle Package includes: Course 01: Certificate in Cycling Training at QLS Level 3 10 Additional CPD QS Accredited Premium Courses - Course 01: Bicycle Maintenance Course Course 02: Performance Cycling Course 03: Fitness & Endurance Training Course 04: Fitness and Muscle Building Training Course 05: Health and Fitness: Diet and Workout Course 06: Dieting For Weight Loss Course 07: Nutrition: Boosting Immunity System Course 08: Vegetarian Diet Course 09: Personal Development Coach Online Course Course 10: Sports First Aid Success becomes a lot simpler with this Cycling bundle package, which allows you to monetise your skills. This Cycling bundle is appropriate for both part-time and full-time students, and it can be completed at your own pace. This premium Cycling bundle of courses helps your professional development by receiving an endorsement from the Quality Licence Scheme and CPDQS Accredited Certificate. You'll be able to practice in your own time and speed. The course materials for Cycling are designed by experts, and you can access them. easily from any of your smartphones, laptops, PCs, tablets, etc. Master the skills. You need to arm yourself with the necessary qualities and explore your career opportunities in relevant sectors. Why Prefer This Bundle? You will receive a completely free certificate from the Quality Licence Scheme. Option to receive 10 additional certificates accredited by CPD QS Get a free student ID card! (£10 postal charge will be applicable for international delivery) Engaging voiceover and visual elements for your convenience. Complete the bundle at your own pace. Free assessments and immediate results. 24/7 tutor support. Take a step toward a brighter future! Course 01: Certificate in Cycling Training at QLS Level 3 Module 01: How to Buy a Cycle Module 02: Fitting and Accessories Module 03: Road Skills Module 04: Cycling in the Real World Module 05: Cycle Maintenance Module 06: Getting the Most Out of Cycling Assessment Process You have to complete the assignment questions given at the end of the course and score a minimum of 60% to pass each exam. Our expert trainers will assess your assignment and give you feedback after you submit the assignment. You will be entitled to claim a certificate endorsed by the Quality Licence Scheme after you have completed all of the Certificate in Cycling Training at QLS Level 3 exams. CPD 220 CPD hours / points Accredited by CPD Quality Standards Who is this course for? This bundle is perfect for highly motivated people who want to improve their technical skills and prepare for the career they want! Requirements No prior background or expertise is required. Career path The bundle aims to help you get the job or even the long-awaited promotion of your dreams.

Leading Cross-Cultural Virtual Teams: In-House Training
By IIL Europe Ltd
Leading Cross-Cultural Virtual Teams: In-House Training High-performing teams are a must in this world of intense competition and higher expectations. Global virtual teaming has become a necessity as organizations become increasingly distributed and suppliers and clients actively engage in joint projects. Teams work across geographical and organizational boundaries to deliver solutions and services to global users where distance and differences, both geographic and cultural, amplify the effect of issues and factors that are relatively straightforward when managing a team of people in the same location. This course delivers practical concepts and techniques that participants will start using immediately on their global projects. What you will Learn At the end of this program, you will be able to: Define relationships among foundational concepts (leadership and three dimensions of diversity) and explain their potential impacts on project performance Describe key components of successful project leadership and build selected Transformational Leadership skills Prepare to convert project challenges stemming from personal or cultural diversity into potential competitive advantage Implement selected best practices to meet key challenges facing virtual project teams Foster and grow an environment that supports continued success for CCVTs Foundation Concepts Basic definitions Critical success factors for leading cross-cultural virtual teams (CCVTs) A roadmap to success for leading CCVTs Leadership Excellence in Any Project Environment Leading effectively in a global environment Transformational leadership The four components of Transformational Leadership Leveraging Personal Diversity Overview of personal diversity Mind styles The theory of multiple intelligences Connecting Transformational Leadership and personal diversity Embracing Cultural Diversity Introduction to cultural intelligence The impact of culture Cultural Dimensions Theory The Culture Map Managing Virtual Diversity Overview of virtual diversity Virtual time management Virtual processes and technology Virtual leadership Creating an Environment for Success Supporting a cross-cultural virtual-team (CCVT-) friendly environment Building a foundation of trust Developing a team charter Recap and review Summary and Next Steps Personal action plan

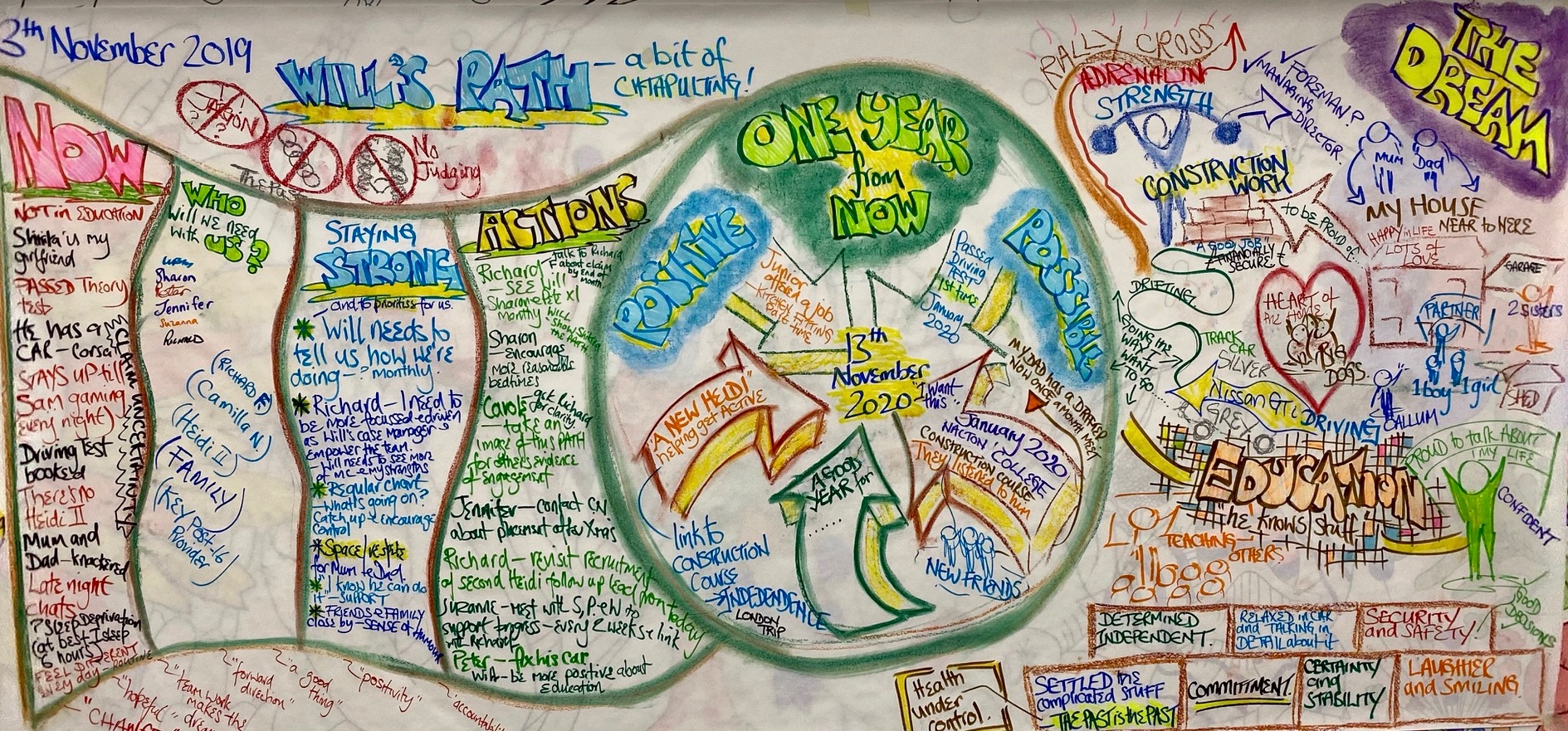
Person Centred Planning in Action
By Inclusive Solutions
An hour long educational and inspirational introduction to person centred planning in action
Certified ScrumMaster: Virtual In-House Training
By IIL Europe Ltd
Certified ScrumMaster®: Virtual In-House Training This course covers Scrum and the principles and tools required to be an effective ScrumMaster. You will come away with a good understanding of the Scrum framework and the underlying principles required to make effective decisions regarding the application of Scrum to different situations. At the end of the course, you will receive membership to the Scrum Alliance for two years and, following completion of an online test, will become a Scrum Alliance Certified ScrumMaster®. Our Certified Scrum Trainers pay the initial, two-year membership fee for each student who successfully completes our Certified ScrumMaster® course. This membership fee also covers the cost of the CSM Test. A link to the test will be sent to you following your course. The CSM test has a passing score of 37 out of 50 questions within a 60-minute timeframe. You will have two attempts within 90 days after you receive your welcome e-mail to pass the test at no cost. After two attempts or 90 days, you will be charged $25 for each additional attempt. What you will Learn At the end of this program, you will be able to: Provide a clear understanding of the fundamental principles of Scrum Use the principles, practices, and tools required to be an effective ScrumMaster Make effective decisions regarding the application of the Scrum framework to different situations, including: Practical, project-proven practices The essentials for getting a project off on the right foot How to write user stories and structure your product backlog How to help both new and experienced teams be more successful How to successfully scale Scrum Tips and tricks from the instructor's many years of using Scrum in a wide variety of environments Getting Started Introduction Course structure Course goals and objectives Agile Principles and Scrum Overview Agile Principles Lean Principles Process control models Incremental and Iterative development Shifting the focus on product management Overview of the Scrum process The Team Dedicated cross-functional teams T-shaped people Sprint Planning Team capacity Facilitating the Sprint Planning meeting The Sprint backlog Sprint Burndown chart Scrum Roles and Responsibilities The team and building effective teams ScrumMaster responsibilities Product Owner responsibilities The Scrum project community What happens to traditional roles in Scrum? Scrum Meetings Daily Scrum Reviews Retrospectives Product Backlog and User Stories Product backlog characteristics User stories Getting your first backlog Getting backlog items ready Slicing User stories Estimation for Forward Planning Why comparative estimation works Planning poker Affinity estimation Release Planning and Tracking Progress Velocity Release planning Tracking release progress Scaling Scrum Scrum of Scrums Scaling the product backlog Scaling across a program and business areas Distributed teams
