- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
SC-100T00 Microsoft Cybersecurity Architect
By Nexus Human
Duration 4 Days 24 CPD hours This course is intended for This course is for experienced cloud security engineers who have taken a previous certification in the security, compliance and identity portfolio. Specifically, students should have advanced experience and knowledge in a wide range of security engineering areas, including identity and access, platform protection, security operations, securing data, and securing applications. They should also have experience with hybrid and cloud implementations. Beginning students should instead take the course SC-900: Microsoft Security, Compliance, and Identity Fundamentals. This is an advanced, expert-level course. Although not required to attend, students are strongly encouraged to have taken and passed another associate level certification in the security, compliance and identity portfolio (such as AZ-500, SC-200 or SC-300) before attending this class. This course prepares students with the expertise to design and evaluate cybersecurity strategies in the following areas: Zero Trust, Governance Risk Compliance (GRC), security operations (SecOps), and data and applications. Students will also learn how to design and architect solutions using zero trust principles and specify security requirements for cloud infrastructure in different service models (SaaS, PaaS, IaaS). Prerequisites Highly recommended to have attended and passed one of the associate level certifications in the security, compliance and identity portfolio (such as AZ-500T00 Microsoft Azure Security Technologies, SC-200T00: Microsoft Security Operations Analyst, or SC-300T00: Microsoft Identity and Access Administrator.) Advanced experience and knowledge in identity and access, platform protection, security operations, securing data and securing applications. Experience with hybrid and cloud implementations. 1 - Introduction to Zero Trust and best practice frameworks Zero Trust initiatives Zero Trust technology pillars part 1 Zero Trust technology pillars part 2 2 - Design solutions that align with the Cloud Adoption Framework (CAF) and Well-Architected Framework (WAF) Define a security strategy Cloud Adoption Framework secure methodology Design security with Azure Landing Zones The Well-Architected Framework security pillar 3 - Design solutions that align with the Microsoft Cybersecurity Reference Architecture (MCRA) and Microsoft cloud security benchmark (MCSB) Design solutions with best practices for capabilities and controls Design solutions with best practices for attack protection 4 - Design a resiliency strategy for common cyberthreats like ransomware Common cyberthreats and attack patterns Support business resiliency Ransomware protection Configurations for secure backup and restore Security updates 5 - Case study: Design solutions that align with security best practices and priorities Case study description Case study answers Conceptual walkthrough Technical walkthrough 6 - Design solutions for regulatory compliance Translate compliance requirements into a security solution Address compliance requirements with Microsoft Purview Address privacy requirements with Microsoft Priva Address security and compliance requirements with Azure policy Evaluate infrastructure compliance with Defender for Cloud 7 - Design solutions for identity and access management Design cloud, hybrid and multicloud access strategies (including Azure AD) Design a solution for external identities Design modern authentication and authorization strategies Align conditional access and Zero Trust Specify requirements to secure Active Directory Domain Services (AD DS) Design a solution to manage secrets, keys, and certificates 8 - Design solutions for securing privileged access The enterprise access model Design identity governance solutions Design a solution to secure tenant administration Design a solution for cloud infrastructure entitlement management (CIEM) Design a solution for privileged access workstations and bastion services 9 - Design solutions for security operations Design security operations capabilities in hybrid and multicloud environments Design centralized logging and auditing Design security information and event management (SIEM) solutions Design solutions for detection and response Design a solution for security orchestration, automation, and response (SOAR) Design security workflows Design threat detection coverage 10 - Case study: Design security operations, identity and compliance capabilities Case study description Case study answers Conceptual walkthrough Technical walkthrough 11 - Design solutions for securing Microsoft 365 Evaluate security posture for collaboration and productivity workloads Design a Microsoft 365 Defender solution Design configurations and operational practices for Microsoft 365 12 - Design solutions for securing applications Design and implement standards to secure application development Evaluate security posture of existing application portfolios Evaluate application threats with threat modeling Design security lifecycle strategy for applications Secure access for workload identities Design a solution for API management and security Design a solution for secure access to applications 13 - Design solutions for securing an organization's data Design a solution for data discovery and classification using Microsoft Purview Design a solution for data protection Design data security for Azure workloads Design security for Azure Storage Design a security solution with Microsoft Defender for SQL and Microsoft Defender for Storage 14 - Case study: Design security solutions for applications and data Case study description Case study answers Conceptual walkthrough Technical walkthrough 15 - Specify requirements for securing SaaS, PaaS, and IaaS services Specify security baselines for SaaS, PaaS, and IaaS services Specify security requirements for web workloads Specify security requirements for containers and container orchestration 16 - Design solutions for security posture management in hybrid and multicloud environments Evaluate security posture by using Microsoft Cloud Security Benchmark Design integrated posture management and workload protection Evaluate security posture by using Microsoft Defender for Cloud Posture evaluation with Microsoft Defender for Cloud secure score Design cloud workload protection with Microsoft Defender for Cloud Integrate hybrid and multicloud environments with Azure Arc Design a solution for external attack surface management 17 - Design solutions for securing server and client endpoints Specify server security requirements Specify requirements for mobile devices and clients Specify internet of things (IoT) and embedded device security requirements Secure operational technology (OT) and industrial control systems (ICS) with Microsoft Defender for IoT Specify security baselines for server and client endpoints Design a solution for secure remote access 18 - Design solutions for network security Design solutions for network segmentation Design solutions for traffic filtering with network security groups Design solutions for network posture management Design solutions for network monitoring 19 - Case study: Design security solutions for infrastructure Case study description Case study answers Conceptual walkthrough Technical walkthrough Additional course details: Nexus Humans SC-100T00 Microsoft Cybersecurity Architect training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the SC-100T00 Microsoft Cybersecurity Architect course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

The Agile PMO: Can It Really Exist?
By IIL Europe Ltd
The Agile PMO: Can It Really Exist? Does an Agile PMO really exist? Can it? How would it work? This session will answer these questions and bring together two seemingly opposing concepts. We'll go back to basics to understand the fundamental purpose of PMOs, and how they benefit projects and organizations. Once we recognize the overall mission and vision of an Agile PMO, we will design a PMO Charter that will show how it adds value. Finally, we'll discuss how to gain buy-in for such a critical function. This and other IIL Learning in Minutes presentations qualify for PDUs. Some titles, such as Agile-related topics may qualify for other continuing education credits such as SEUs, or CEUs. Each professional development activity yields one PDU for one hour spent engaged in the activity. Some limitations apply and can be found in the Ways to Earn PDUs section that discusses PDU activities and associated policies. Fractions of PDUs may also be reported. The smallest increment of a PDU that can be reported is 0.25. This means that if you spent 15 minutes participating in a qualifying PDU activity, you may report 0.25 PDU. If you spend 30 minutes in a qualifying PDU activity, you may report 0.50 PDU.

ITIL 4 Specialist: Drive Stakeholder Value: In-House Training
By IIL Europe Ltd
ITIL® 4 Specialist: Drive Stakeholder Value: In-House Training The ITIL® 4 Specialist: Drive Stakeholder Value module is part of the Managing Professional stream for ITIL 4. Candidates need to pass the related certification exam for working towards the Managing Professional (MP) designation. This course is based on the ITIL® 4 Specialist: Drive Stakeholder Value exam specifications from AXELOS. With the help of ITIL® 4 concepts and terminology, exercises, and examples included in the course, candidates acquire the relevant knowledge required to pass the certification exam. What You Will Learn The learning objectives of the course are based on the following learning outcomes of the ITIL® 4 Specialist: Drive Stakeholder Value exam specification: Understand how customer journeys are designed Know how to target markets and stakeholders Know how to foster stakeholder relationships Know how to shape demand and define service offerings Know how to align expectations and agree on details of services Know how to onboard and offboard customers and users Know how to act together to ensure continual value co-creation (service consumption / provisioning) Know how to realize and validate service value Customer Journey Purpose of the Module Purpose of Mastering the Customer Journey Touchpoints and Service Interactions Module Topics Mapping the Customer Journey Designing the Customer Journey Measuring and Improving the Customer Journey Customer Journey Step 1: Explore Purpose of the Module Purpose of the Explore Step Module Topics Understanding Service Consumers Understanding Service Providers Understanding and Targeting Markets Customer Journey Step 2: Engage Purpose of the Module Purpose of the Engage Step Aspects of Service Value Module Topics Service Relationship Types Building Service Relationships Building and Sustaining Trust and Relationships Analyzing Customer Needs Managing Suppliers and Partners Customer Journey Step 3: Offer Purpose of the Module Purpose of Shaping Demand and Service Offerings Module Topics Managing Demand and Opportunities Specifying and Managing Customer Requirements Designing Service Offerings and User Experience Selling and Obtaining Service Offerings Customer Journey Step 4: Agree Purpose of the Module Purpose of Aligning Expectations and Agreeing on Services Module Topics Agreeing on and Planning Value Co-Creation Negotiating and Agreeing on a Service Customer Journey Step 5: Onboard Purpose of the Module Purpose of Onboarding and Offboarding ITIL® Management Practices Module Topics Planning Onboarding Fostering Relationships with Users Providing User Engagement and Delivery Channels Enabling Users for Service Elevating Mutual Capabilities Offboarding Customer Journey Step 6: Co-create Purpose of the Module Purpose of Service Provision and Consumption Module Topics Service Mindset Ongoing Service Interactions Nurturing User Communities Customer Journey Step 7: Realize Purpose of the Module Measuring Service Value Purpose of Value Capturing and Customer Journey Improvement Realizing Service Value in Different Settings Module Topics Tracking Value Realization Assessing and Reporting Value Realization Evaluating Value Realization and Improving Customer Journeys Realizing Value for the Service Provider

IT Cyber Security Engineer – Job Ready Programme Enrol in Our IT Cyber Security Engineer – Job Ready Programme with Career Support! Gain access to 3,000+ online courses and earn Free Certificates to showcase your skills and boost your career potential. Step into the high-demand world of cyber security with a comprehensive programme designed for the UK job market. Master critical areas like penetration testing, secure cloud architecture, AI-powered threat detection, and GDPR compliance—skills that can lead to roles earning up to £95,000 a year. As UK businesses face £27 billion in cybercrime losses annually, the demand for skilled IT Cyber Security Engineers has never been greater. Whether you're changing careers or upskilling, this course equips you with in-demand expertise in threat intelligence, cryptography, and secure coding. Become the digital defence every company needs. Start your journey toward a resilient and rewarding career in cyber security today. Professional Diploma in IT Cyber Security Engineer – 25 Core Courses – Course 01: Cyber Security Online Course: DOSS and DDOS – Course 02: Cyber Security Training: Incident Handling & Response – Course 03: Security Threat Management – Course 04: Certified Information Security Manager (CISM) – Course 05: Certified Information Systems Security Professional (CISSP) – Course 06: CompTIA Advanced Security Practitioner (CASP) – Course 07: Computer Network Security Complete Training – Course 08: CyberSec First Responder: Threat Detection and Response [QLS Level 7] – Course 09: Bash Scripting and Shell Programming for Beginners – Course 10: Ethical Hacking Masterclass – Course 11: CompTIA PenTest+ Ethical Hacking Course – Course 12: BlackArch Linux: Ethical Hacking and Penetration Testing – Course 13: Ultimate Linux Security and Hardening Training – Course 14: The Complete Python Hacking Course: Beginner to Advanced! – Course 15: SQL Database Basics – Course 16: CompTIA Network+ Certification (N10-008) – Course 17: CompTIA A+ Core 1 (220-1101) Course – Course 18: CompTIA A+ Core 2 (220-1102) Course – Course 19: CompTIA Security+ (SY0-601) – Course 20: CompTIA Cloud+ CV0-002 Course – Course 21: Cisco CCENT/CCNA Interconnecting Cisco Networking Devices Part 1 – Course 22: Cisco CCNA Interconnecting Cisco Networking Devices Part 2 (ICND2) Training – Course 23: Cisco ASA Firewall Training with Step-by-Step Lab Workbook – Course 24: FortiGate Firewall Training Step-by-Step Lab Workbook – Course 25: Palo Alto Firewall Training with Step-by-Step Lab Workbook Job Readiness & Career Development Training (Complementary) – Course 01: Career Development Training – Course 02: Effective CV Writing – Course 03: CV Writing and Interview Tricks – Course 04: Ace the Interview – Interview Prep That Makes a Difference – Course 05: Job Search Skills – Course 06: Effective Communication Skills for Professionals – Course 07: Boost Your Confidence, Assertiveness – Course 08: Body Language Secrets – Course 09: Coaching and Mentoring – Course 10: Presentation Skills – Present like a Pro – Course 11: Public Speaking Course – Course 12: Project Management Training – Course 13: Leadership & Management – Course 14: Negotiation and Agreement Training – Course 15: Workplace Equality & Diversity – Course 16: Professional Development and Personal Well-being – Course 17: Emotional Intelligence and Human Behaviour – Course 18: Time Management: Step By Step Training – Course 19: Cross-Cultural Awareness – Course 20: Productivity Boosting – Course 21: Critical Thinking & Problem Solving – Course 22: Perfect LinkedIn Profile Creation – Course 23: Resume Writing Skills & Job Search With LinkedIn – Course 24: Email Writing – Course 25: Learn Microsoft Word, PowerPoint & Outlook In 90 Minutes!

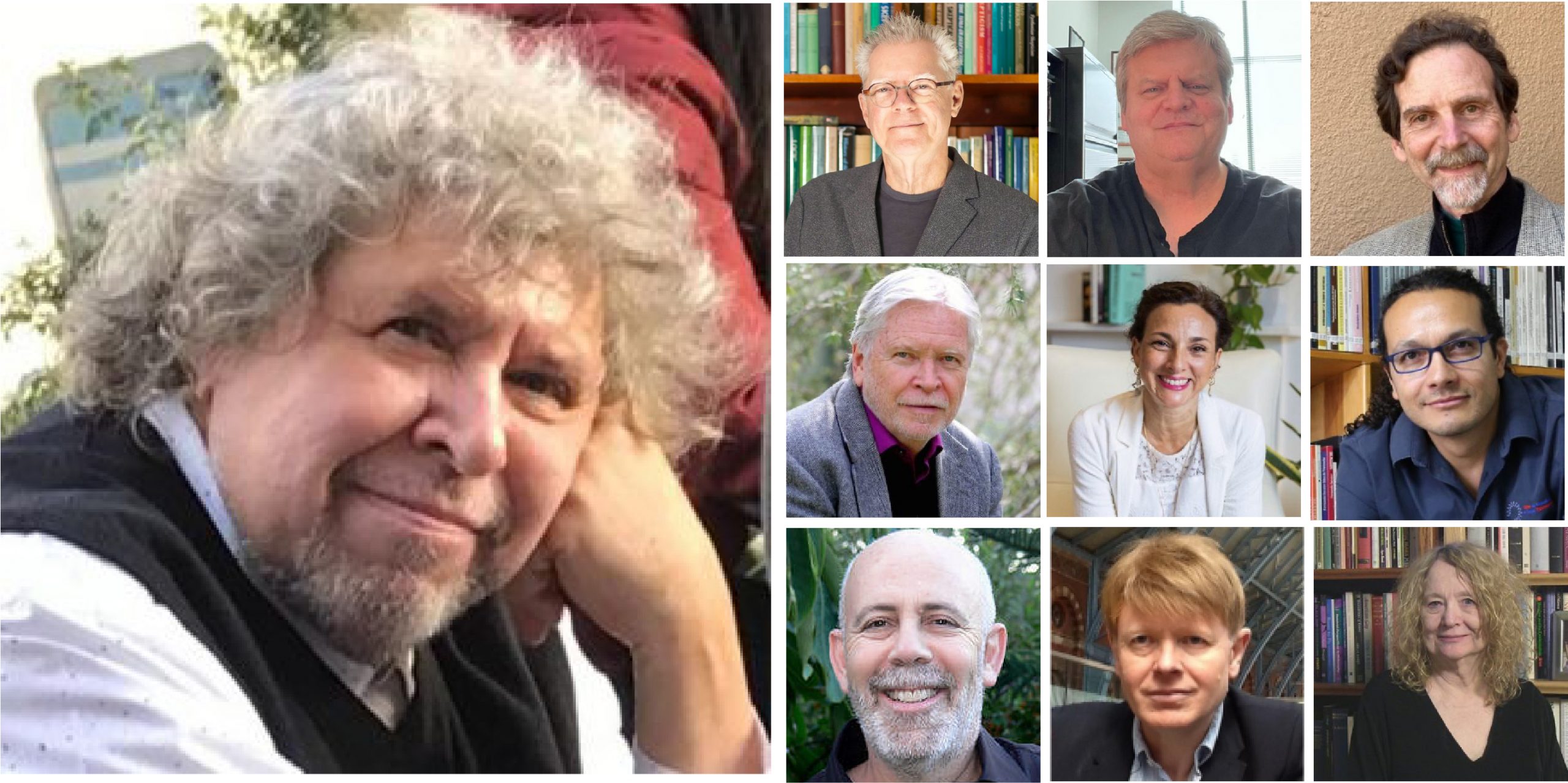
Existential Dialogues 2025: “In-Sanity, Who is Sane?” with Prof E. Spinelli
By Therapy Harley Street
Ten live dialogues between Prof Ernesto Spinelli and International Existential Therapists followed by an Experiential Study Group. A phenomenological approach to re-view psychopathology: We aim to explore the lived experiences of irregular perceptions of reality with an open mind. Each Saturday includes a live dialogue between Prof Ernesto Spinelli and an International Existential Therapist; a moment to share your thoughts and feelings with the teachers; and a final integration facilitated by Bárbara Godoy. This series of ten Dialogues set out to explore the multifaceted dimentions and complexities associated with Existential Therapies. It attempts to engage with various interpretations of insanity through the lens of patients' often painful, confounding, and deeply unsettling life experiences. TIMES AND DATES 2025 25 Jan. “Knots” with Prof. Ernesto Spinelli 2 Feb. “Healing” with Dr. Michael Guy Thompson 22 Mar. “Difference” with Dr. Todd DuBose 12 Apr. “Polarization” with Prof. Kirk Schneider 3 May “Character” with Prof. Robert Romanyshyn 21 Jun. “Opening” with Dr. Yaqui Martinez 19 Jul. “Meaning” with Dr. Jan Resnick 25 Oct. “Invention” with Dr. Betty Cannon 15 Nov. “Hallucination” with Prof. Simon du Plock 13 Dec. “Hysteria” with Bárbara Godoy Full course (including dialogues): £1260 (2 pm to 5 pm – UK time) Only Dialogues: £630 (2 pm to 3 pm – UK time) Venue: Online Zoom Read the full Programme here > Course Organised by:
55315: Introduction to SQL Databases
By Nexus Human
Duration 3 Days 18 CPD hours This course is intended for The primary audience for this course is people who are moving into a database role, or whose role has expanded to include database technologies. Developers that deliver content from SQL Server databases will also benefit from this material. Overview After completing this course, you will be able to: Describe key database concepts in the context of SQL Server Describe database languages used in SQL Server Describe data modelling techniques Describe normalization and denormalization techniques Describe relationship types and effects in database design Describe the effects of database design on performance Describe commonly used database objects This course is provided as an introductory class for anyone getting started with databases. It will be useful to programmers and other IT professionals whose job roles are expanding into database management. Students will learn fundamental database concepts through demonstrations and hands-on labs on a SQL Server instance. This material updates and replaces course Microsoft course 10985 which was previously published under the same title. Module 1: Introduction to databases Introduction to Relational Databases Other Databases and Storage Data Analysis SQL Server Database Languages Module 2: Data Modeling Data Modelling Designing a Database Relationship Modeling Module 3: Normalization Fundamentals of Normalization Normal Form Denormalization Module 4: Relationships Introduction to Relationships Planning Referential Integrity Module 5: Performance Indexing Query Performance Concurrency Module 6: Database Objects Tables Views Stored Procedures, Triggers and Functions

Overview Uplift Your Career & Skill Up to Your Dream Job - Learning Simplified From Home! Kickstart your career & boost your employability by helping you discover your skills, talents and interests with our special Recruitment: IT Basics for IT Recruiters Course. You'll create a pathway to your ideal job as this course is designed to uplift your career in the relevant industry. It provides professional training that employers are looking for in today's workplaces. The Recruitment: IT Basics for IT Recruiters Course is one of the most prestigious training offered at StudyHub and is highly valued by employers for good reason. This Recruitment: IT Basics for IT Recruiters Course has been designed by industry experts to provide our learners with the best learning experience possible to increase their understanding of their chosen field. This Recruitment: IT Basics for IT Recruiters Course, like every one of Study Hub's courses, is meticulously developed and well researched. Every one of the topics is divided into elementary modules, allowing our students to grasp each lesson quickly. At StudyHub, we don't just offer courses; we also provide a valuable teaching process. When you buy a course from StudyHub, you get unlimited Lifetime access with 24/7 dedicated tutor support. Why buy this Recruitment: IT Basics for IT Recruiters? Unlimited access to the course for forever Digital Certificate, Transcript, student ID all included in the price Absolutely no hidden fees Directly receive CPD accredited qualifications after course completion Receive one to one assistance on every weekday from professionals Immediately receive the PDF certificate after passing Receive the original copies of your certificate and transcript on the next working day Easily learn the skills and knowledge from the comfort of your home Certification After studying the course materials of the Recruitment: IT Basics for IT Recruiters there will be a written assignment test which you can take either during or at the end of the course. After successfully passing the test you will be able to claim the pdf certificate for £5.99. Original Hard Copy certificates need to be ordered at an additional cost of £9.60. Who is this course for? This Recruitment: IT Basics for IT Recruiters course is ideal for Students Recent graduates Job Seekers Anyone interested in this topic People already working in the relevant fields and want to polish their knowledge and skill. Prerequisites This Recruitment: IT Basics for IT Recruiters does not require you to have any prior qualifications or experience. You can just enrol and start learning.This Recruitment: IT Basics for IT Recruiters was made by professionals and it is compatible with all PC's, Mac's, tablets and smartphones. You will be able to access the course from anywhere at any time as long as you have a good enough internet connection. Career path As this course comes with multiple courses included as bonus, you will be able to pursue multiple occupations. This Recruitment: IT Basics for IT Recruiters is a great way for you to gain multiple skills from the comfort of your home. Course Curriculum Section 01: Introduction Introduction 00:02:00 Section 02: IT Fundamentals Server 00:08:00 What is hardware and software? 00:04:00 Project Life Cycle 00:06:00 Software Development Life Cycle 00:08:00 Section 03: IT Terms / basics Methodologies: Scrum, Agile, Kanban, Waterfall, Lean 00:09:00 CMS 00:04:00 API 00:04:00 Stacks 00:03:00 Native & Hybrid Native Apps 00:02:00 CI / CD / Deployment tools 00:04:00 Section 04: IT Positions CTO 00:13:00 IT Architects 00:08:00 Product Owner 00:12:00 Product Manager 00:06:00 PO vs Product Manager 00:04:00 Project Manager 00:13:00 Product Owner vs Project Manager vs Product Manager 00:07:00 Business Analysts 00:09:00 Business Intelligence Analyst 00:06:00 Data Engineer 00:05:00 Data Scientist 00:07:00 Data Engineer vs Data Scientist 00:07:00 Agile Coach 00:14:00 Scrum Master 00:08:00 Agile Coach vs Scrum Master 00:01:00 Frontend Developer 00:06:00 Backend Developer 00:06:00 Fullstack Developer 00:04:00 Developers: Frontend, Backend and Fullstack 00:02:00 iOS Developer 00:03:00 Android Developer 00:04:00 UX Designers 00:09:00 UI Design 00:08:00 UX vs UI Design: what is the difference? 00:04:00 QA Engineers and Testers 00:09:00 System Administrators+ 00:07:00 DevOps 00:05:00 SEO Specialists: who are they? 00:10:00 Section 05: IT Technologies Programming languages and frameworks Programming Languages and Frameworks. Introduction 00:01:00 Programming languages and frameworks 00:08:00 JavaScript 00:02:00 Java 00:03:00 Python 00:01:00 C 00:02:00 C# 00:02:00 C++ 00:03:00 SWIFT 00:02:00 Objective C 00:01:00 HTML 00:02:00 PHP 00:02:00 Ruby 00:02:00 SQL 00:02:00 Go 00:01:00 R 00:01:00 Section 06: IT Technologies: Databases Database 00:05:00 Types of Databases 00:07:00 Section 07: From Recruiter to Recruiter The day of an IT Recruiter 00:05:00 Key principles 00:03:00 Sourcing Tipps 00:03:00 Section 08: Bye-bye Thank you for taking part in this course! 00:01:00 Assignment Assignment - Recruitment: IT Basics for IT Recruiters 00:00:00

Network and Cyber Security Traineeship Program with Career Support & Money Back Guarantee
4.7(47)By Academy for Health and Fitness
Earn up to 85k as a 'Cyber Security Analyst' or Your 100% Money Back Are you concerned about the rising threat of cybercrime? In the UK alone, cyberattacks cost businesses an estimated £3.1 billion annually, and the demand for skilled cybersecurity professionals is booming. With an average salary of £45,000, a career in cybersecurity offers promising opportunities for those seeking stability and growth. Are you looking to join the high-demand field of cyber security and earn a handsome salary? Our Network and Cyber Security Traineeship Program is here to guide you all the way until you get the job you want. This Network and Cyber Security Traineeship Program is your all-in-one solution to learn cyber security from scratch and also secure a job in this exciting industry. With our unique blend of comprehensive courses and career support, your dream job is within reach. We understand the challenges of transitioning into a new field, which is why our program is tailored to guide you every step of the way - from mastering core skills to landing your first job as a Cyber Security Analyst. By choosing our Cyber Security Job Guarantee Programme, you're not just gaining skills; you're gaining a lifelong career partner. Our mission is simple - to be your trusted partner every step of the way, from training to employment. In addition to teaching you the technical skills you need, we will also provide you with career mentoring and support. We will help you build your resume, prepare for interviews, and land your dream job. We also have partnerships with many companies that are hiring Programmers, so we can help you get your foot in the door. If you are not happy with our service, we also offer a 100% money-back guarantee. So what are you waiting for? Enrol in our Cyber Security Job Guarantee Programme today and start your journey to become successful in Cyber Security field! Why Choose Us? So, what sets us apart from other programs? Let's dive into the exceptional benefits you'll experience when you join our Certified Cyber Security Job Guarantee Programme: Personalised Guidance: We believe in the power of individual attention. Our experienced mentors will provide one-on-one counselling sessions tailored to your specific needs. Whether you're a beginner or have some Cyber Security experience, we will guide you towards honing your skills and developing a strong foundation in Cyber Security. One-On-One Consultation: Gain invaluable insights and guidance from seasoned professionals who have thrived in the Cyber Security field. Our consultation sessions provide you with insider tips, tricks, and advice, empowering you to navigate the industry with confidence and expertise. Extensive Job Opportunities: We have established partnerships with numerous companies actively seeking Certified Cyber Security Job Guarantee Programme. Through our network, we'll connect you with exclusive job openings that are not easily accessible elsewhere. Interview Preparation: No more stress over unexpected interview questions. We provide you with access to a comprehensive database of potential interview questions curated over years of industry experience. Walk into your interviews confident, well-prepared, and ready to impress. Courses we will provide once you enrol in the program: Course 01: Cyber Security Programming Course 02: Cyber Security Advanced Training Course 03: Cyber Security Incident Handling and Incident Response Course 04: IT Support Technician Course 05: General Data Protection Regulation (GDPR) & Cyber Security Management Course 06: CompTIA Security+ (SY0-601) Course 07: CompTIA A+ (220-1001) Course 08: CompTIA A+ (220-1002) Course 09: Cloud Computing / CompTIA Cloud+ (CV0-002) Course 10: CompTIA CySA+ Cybersecurity Analyst (CS0-002) Course 11: CompTIA IT Fundamentals ITF+ (FCO-U61) Course 12: CompTIA Network+ Certification (N10-007) Course 13: Diploma in CompTIA Network+ Training at QLS Level 7 Course 14: CompTIA PenTest+ (Ethical Hacking) Course 15: Cisco ASA Firewall Training Course 16: Cryptography Course 17: IT Administration and Networking Course 18: IGCSE ICT: Network Essentials Course 19: Cyber Security Law Course 20: Cyber Security Awareness Training How Can We Offer Job Guarantees? HF Online provides consultancy, professional and educational services to many of the companies in the UK. During our intense exclusive training program, you will not just gain and complete the industry valuable certification but will gain industry experience as well, which is imperative to get your 1st job in the sector. The Network and Cyber Security Traineeship Program Programme is completed in 9 easy steps: Step 1: Enrol in the Programme Begin your exciting journey with us by enrolling in the Cyber Security Job Guarantee Programme. Complete your registration and make a secure online payment. Remember, we offer a 14-day money-back guarantee if you're not completely satisfied. After you enrol in the Program, you will get lifetime access to 20 Premium Courses related to Cyber Security Job Guarantee Programme. These courses will teach you the knowledge and skills required to become successful in Cyber Security field. Our customer service team will help you and keep in contact with you every step of the way. So you won't have to worry about a thing! Step 2: Initial One-On-One Counselling Session Once enrolled, you will be paired with a dedicated career mentor. Schedule your first one-on-one session to discuss your career aspirations, skills, experience, and any areas for potential growth. This conversation will shape your learning and development path. Step 3 - Certification upon Course Completion After learning from the courses, you must obtain certificates for each course. There will be exams for every course, and you have to pass them to get your certificate. To pass successfully, you must get 90% marks. Once you pass the exams, you will receive hardcopy certificates. These certificates will prove that you're an expert in the subject. Step 4: CV Revamping Our team of professionals will build you a compelling CV and LinkedIn profile. We'll ensure it presents your skills and qualifications effectively and is tailored to the needs and expectations of the programming/development industry. With these powerful tools in hand, you'll be fully prepared to tackle job interviews confidently. Step 5: Building Network and Submitting CV We understand the power of casting a wide net. We'll strategically submit your CV to various platforms and networks, expanding your reach and connecting you with valuable opportunities that align with your career goals. We will also make connections with many high-profile individuals and companies through your LinkedIn profile. Step 6: Interview Preparation With your CV ready, we'll move on to interview preparation. Gain exclusive access to our database of potential interview questions. Through simulated interviews with your mentor, you'll practice your responses and receive valuable feedback to further refine your skills. Step 7: Securing Job Interviews Leveraging our partnerships with leading companies, we'll secure job interviews for you. We'll ensure you get the opportunity to showcase your skills to potential employers and get the dream job you want. Step 8: Post-Interview Support Post-interview, we'll provide a debriefing session to reflect on your performance and identify areas of improvement for future interviews if necessary. Remember, our commitment extends until you land your dream job. Step 9: Celebrate Your New Job! Once you've secured your dream job in Cyber Security, it's time to celebrate! However, our support doesn't end there. We'll provide you with ongoing career advice to ensure you continue to thrive in your new role. We're excited to accompany you on this journey to success. Enrol today, and let's get started! Your path to a successful career in Cyber Security field begins with us. CPD 1000 CPD hours / points Accredited by CPD Quality Standards Who is this course for? This Cyber Security Job Guarantee Programme Course is suitable for: Beginners with no prior programming experience who are looking to enter the world of coding. Intermediate programmers who wish to expand their skills and explore Cyber Security's extensive usage. IT professionals seeking to diversify their skill sets and stay relevant in today's tech-driven market. Data analysts and scientists who want to leverage Cyber Security's powerful libraries for their data processing needs. Students and recent graduates looking to enhance their employability in the thriving tech industry. Entrepreneurs who wish to understand and utilise Cyber Security to automate tasks and analyse data for their businesses. Anyone with a keen interest in Cyber Security and a desire to delve into its applications in diverse fields like web development, data science, machine learning, and more. Requirements No experience required. Just enrol & start learning. Career path Cyber Security Analyst: £35,000 - £85,000 annually Incident Response Specialist: £40,000 - £90,000 annually IT Support Technician: £25,000 - £55,000 annually GDPR Compliance Officer: £30,000 - £70,000 annually Cloud Security Architect: £50,000 - £120,000 annually Ethical Hacker/Penetration Tester: £35,000 - £95,000 annually Network Security Engineer: £40,000 - £100,000 annually Certificates CPD Accredited e-Certificate Digital certificate - Included CPD Accredited Framed (Hardcopy) Certificate Hard copy certificate - Included Enrolment Letter Digital certificate - Included QLS Endorsed Hard Copy Certificate Hard copy certificate - Included Student ID Card Digital certificate - Included

DASA DevOps Fundamentals: Virtual In-House Training
By IIL Europe Ltd
DASA DevOps Fundamentals: Virtual In-House Training The DASA DevOps Fundamentals™ certification provides the core education necessary to build your DevOps vocabulary and understand its principles and practices. It's the ideal starting point for DevOps journeys, whether you're already familiar with working with Agile and/or DevOps teams or not. Faster software deployment, increased deployment frequency, and higher change success rate are only some of the visible outcomes of practicing DevOps. Organizations such as Netflix, Spotify, and Facebook are transforming IT by successfully implementing DevOps principles. But you don't have to be big to be a DevOps leader. Companies large and small, young and old, have smoothly made the transition and have the proof of success in their pockets. This course will inspire you to serve as a change champion by sharing and using what you learned, and continue to learn, about DevOps to lead and mentor others. A solid understanding of DevOps Fundamentals has helped numerous professionals and organizations how to approach a DevOps journey, not only from a tool and automation perspective but also looking in-depth at the softer side of things. This course provides learners with an extensive introduction to the core Agile DevOps principles. It covers all 12 key knowledge and skill competencies defined by DASA to ensure you acquire a solid knowledge of DevOps concepts and terminology. Multiple cases or scenarios, group discussions, and examples are included in the course to enhance your learning experience. What you will Learn DASA DevOps Fundamentals-certified professionals are able to: Explain the drivers responsible for the emergence of DevOps. Define and discuss the key concepts and principles of DevOps. List and explain the business benefits of DevOps and continuous delivery. Know how teams can translate DevOps principles into tangible practices. Learn about modern operations in a DevOps context. Explain the concepts of test automation, infrastructure automation, and build and deployment automation. Describe how DevOps relates to Lean and Agile methodologies. Get insight into the various organizational DevOps models and architectures. Identify how Cloud and Delivery pipeline automation optimizes and accelerates the ways of working. Discuss the critical success factors for DevOps transformation. Introducing DASA DevOps Fundamentals DASA DevOps Fundamentals An Introduction Case Study - Easy Journey Airways Building the DevOps Context DevOps Evolution Business Benefits of DevOps DASA DevOps Principles Goals and Measurements Knowing DevOps for Individuals T-Shape Profiles DevOps Capabilities by DASA DASA DevOps Certifications Getting Acquainted with DevOps Culture and Behavior Embracing a DevOps Culture Core Elements of a DevOps Culture Implementation of a DevOps Culture Understanding the Value of DevOps for Teams and Organizations Organizational Models Team Autonomy DevOps at Scale Getting Familiar with DevOps Management Practices ITSM Lean Agile Getting Familiar with DevOps Technical Practices Architecture Modern Infrastructure and Cloud Operations Enabling DevOps Team Performance Through Continuous Delivery and Automation Software Delivery Automation Concepts Continuous Delivery Core Concepts Continuous Delivery Automation Concepts Continuous Delivery Automation Focus Topics Measuring the Performance - The Next Steps Analyze the Current Situation Improve Incrementally

Wireshark 101 training course description Wireshark is a free network protocol analyser. This hands-on course focuses on troubleshooting networks using the Wireshark protocol analyser. The course concentrates on the product and students will gain from the most from this course only if they already have a sound knowledge of the TCP/IP protocols What will you learn Download and install Wireshark. Capture and analyse packets with Wireshark. Configure capture and display filters. Customise Wireshark. Troubleshoot networks using Wireshark. Wireshark 101 training course details Who will benefit: Technical staff looking after networks. Prerequisites: TCP/IP Foundation for engineers Duration 2 days Wireshark 101 training course contents What is Wireshark? Protocol analysers, Wireshark features, versions, troubleshooting techniques with Wireshark. Installing Wireshark Downloading Wireshark, UNIX issues, Microsoft issues, the role of winpcap, promiscuous mode, installing Wireshark. Wireshark documentation and help. Hands on Downloading and installing Wireshark. Capturing traffic Starting and stopping basic packet captures, the packet list pane, packet details pane, packet bytes pane, interfaces, using Wireshark in a switched architecture. Hands on Capturing packets with Wireshark. Troubleshooting networks with Wireshark Common packet flows. Hands on Analysing a variety of problems with Wireshark. Capture filters Capture filter expressions, capture filter examples (host, port, network, protocol), primitives, combining primitives, payload matching. Hands on Configuring capture filters. Working with captured packets Live packet capture, saving to a file, capture file formats, reading capture files from other analysers, merging capture files, finding packets, going to a specific packet, display filters, display filter expressions. Hands on Saving captured data, configuring display filters. Analysis and statistics with Wireshark Enabling/disabling protocols, user specified decodes, following TCP streams, protocol statistics, conversation lists, endpoint lists, I/O graphs, protocol specific statistics. Hands on Using the analysis and statistics menus. Command line tools Tshark, capinfos, editcap, mergecap, text2pcap, idl2eth. Hands on Using tshark. Advanced issues 802.11 issues, management frames, monitor mode, packet reassembling, name resolution, customising Wireshark. Hands on Customising name resolution.
