- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
26457 Courses delivered Online
Customer Experience is the New Battleground
By IIL Europe Ltd
Customer Experience is the New Battleground A positive customer experience is critical to a company's brand and, ultimately, its bottom line. With the proliferation of technology and devices, the customer has become smarter and more powerful.

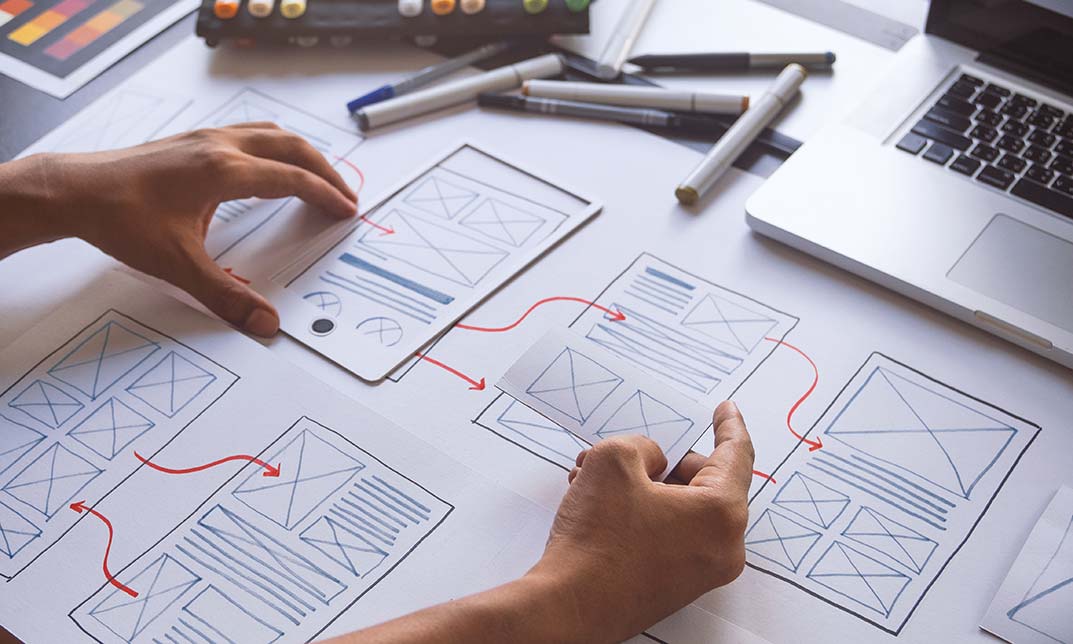
Register on the Basic to Advanced UX Design today and build the experience, skills and knowledge you need to enhance your professional development and work towards your dream job. Study this course through online learning and take the first steps towards a long-term career. The course consists of a number of easy to digest, in-depth modules, designed to provide you with a detailed, expert level of knowledge. Learn through a mixture of instructional video lessons and online study materials. Receive online tutor support as you study the course, to ensure you are supported every step of the way. Get a digital certificate as a proof of your course completion. The Basic to Advanced UX Design course is incredibly great value and allows you to study at your own pace. Access the course modules from any internet-enabled device, including computers, tablet, and smartphones. The course is designed to increase your employability and equip you with everything you need to be a success. Enrol on the now and start learning instantly! What You Get With This Course Receive a digital certificate upon successful completion of the course Get taught by experienced, professional instructors Study at a time and pace that suits your learning style Get instant feedback on assessments 24/7 help and advice via email or live chat Get full tutor support on weekdays (Monday to Friday) Course Design The course is delivered through our online learning platform, accessible through any internet-connected device. There are no formal deadlines or teaching schedules, meaning you are free to study the course at your own pace. You are taught through a combination of- Video lessons Online study supplies Assignment Certificate of Achievement After the successful completion of the final assessment, you will receive a CPD-accredited certificate of achievement. The PDF certificate is for 9.99, and it will be sent to you immediately after through e-mail. You can get the hard copy for 15.99, which will reach your doorsteps by post. Method of Assessment In order to ensure the Quality Licensing scheme endorsed and CPD acknowledged certificate, learners need to score at least 60% pass marks on the assessment process. After submitting assignments, our expert tutors will evaluate the assignments and give feedback based on the performance. After passing the assessment, one can apply for a certificate. Who is this course for? The course is ideal for those who already work in this sector or are aspiring professionals. This course is designed to enhance your expertise and boost your CV. Learn key skills and gain a professional qualification to prove your newly-acquired knowledge. Course Content Unit 01: UX/UI Course Introduction Learn UX/UI Course Overview 00:05:00 Section Overview 00:04:00 UX vs UI 00:04:00 UX/UI Designer Marketplace 00:05:00 Overview of UX Roles 00:06:00 Unit 02: Introduction to the Web Industry Web Industry Section Overview 00:03:00 The Phases of Web Development 00:13:00 Designer Responsibilities (working in a team) 00:09:00 Roles & Descriptions (working in a team) 00:05:00 Agile Approach To Project Management 00:12:00 Scrum - Flexible Framework 00:06:00 Project Management Apps 00:13:00 XD Lesson - Introduction 00:13:00 Unit 03: Foundations of Graphic Design Graphic Design Section Overview 00:02:00 The Psychology of Color 00:13:00 Color Wheel & Color Schemes 00:06:00 Working with Fonts 00:10:00 Working With Icons 00:04:00 XD Lesson - Tools, Object Manipulation and Components 00:13:00 XD Lesson - Font Styles and Artboard Settings 00:07:00 Graphic Design Software Tools 00:03:00 Adobe XD lesson 4 - Icons & Vector Graphics 00:14:00 Unit 04: UX Design (User Experience Design) UX Design Section Overview 00:04:00 What is User Experience Design? (UX) 00:09:00 UX Design Process 00:03:00 The UX Analysis Process 00:08:00 Working with User Profiles 00:03:00 Understanding User Pain Points 00:03:00 XD Lesson 5 Class Project: Сompetitive Analysis 00:10:00 Developing a Persona Part 1 00:05:00 Developing a Persona Part 2 00:05:00 Customer Journey 00:04:00 Customer Journey vs Sales Funnel 00:04:00 3 Phases of a Sales Funnel 00:07:00 4 Stages of a Sales Funnel 00:06:00 Macro/Micro Conversions 00:05:00 Stages of Market Sophistication 00:06:00 Lead Generation Funnel 00:06:00 Digital Product Sales Funnel 00:05:00 7 Principles of Influence 00:12:00 Age Based Influence Triggers 00:06:00 Gender Influence Triggers 00:06:00 Interest Based Marketing 00:04:00 Understanding User Flow 00:08:00 XD Lesson 6 Class Project: Userflow - Your first UX deliverable 00:07:00 Working with Story Boards 00:05:00 XD Lesson 7 Class Project: Crafting a Story board 00:09:00 Working with Moodboards 00:04:00 XD Lesson 8 Class Project: Creating Moodboard 00:11:00 Sitemap & Information Architecture 00:07:00 XD Lesson - Class Project: App Architecture 00:09:00 Low and Hi Fidelity Wireframes 00:03:00 XD Lesson - Class Project: Login Screen Wireframe Using Material Design 00:08:00 Working with Prototypes 00:04:00 XD Lesson - Class Project: Home Screen Wireframe and Linking 00:07:00 XD Lesson - Class Project: Adding Interaction to Wireframes 00:10:00 Testing and Evaluating 00:11:00 UX Deliverables 00:03:00 UX Design Conclusion 00:01:00 Unit 05: UI Design (User Interface Design) UI Design Section Overview 00:03:00 UI Design Overview 00:03:00 Types of Interfaces 00:10:00 Landing Pages Overview 00:10:00 XD Lesson - Using Grids in XD 00:08:00 XD Lesson - Single Card design 00:13:00 UI Controls 00:07:00 UI Navigational Components 00:12:00 Header Design Overview 00:07:00 XD Lesson - Mobile & Desktop: Header Design 00:10:00 XD Lesson - Mobile & Desktop: Dropdown Design 00:06:00 Common Layouts Overview 00:08:00 XD Lesson - Common Layouts 00:07:00 Mobile & Desktop Footer Design Overview 00:07:00 XD Lesson - Mobile & Desktop: Footer Design 00:06:00 Mobile & Desktop Button Design Overview 00:05:00 XD Lesson - Mobile & Desktop: Button Design 00:10:00 XD Lesson - Mobile & Desktop: Input Design 00:07:00 Mobile & Desktop Filter Search Bar Design Overview 00:06:00 Adobe XD Lesson - Mobile & Desktop: Filter Design 00:07:00 Adobe XD Lesson - Mobile & Desktop: Search Design 00:03:00 UI Kit Overview 00:05:00 Adobe XD Lesson - Desktop and Mobile: UI Kit 00:06:00 Microinteractions Overview 00:05:00 Adobe XD lesson - Microinteractions 00:07:00 Unit 06: Optimization Optimization Section Overview 00:02:00 Feedback Review & Getting Referrals 00:04:00 'Above the Fold' Rule 00:04:00 Adobe XD lesson - Designing a Powerful Above the Fold 00:08:00 Using Analytics For Optimization 00:05:00 Heat Maps & Element Placements 00:04:00 Crafting A Usability Report Overview 00:08:00 Adobe XD lesson - Crafting Reports in XD 00:20:00 Unit 07: Starting a Career in UX/UI Design Careers in UX/UI Section Overview 00:06:00 Your Daily Productivity Hub 00:14:00 How To Start Freelancing 00:08:00 Client Consulting 00:04:00 Building a Brand 00:10:00 Personal Branding 00:07:00 The Importance of Having a Website 00:08:00 Creating a Logo 00:05:00 Step by Step Website Setup 00:17:00 UI Templates 00:06:00 Logo Templates 00:04:00 Creating a Business Email 00:06:00 Networking Do's and Don'ts 00:04:00 Top Freelance Websites 00:05:00 UX/UI Project Scope Questions 00:10:00 Laser Focus & Productivity Tools 00:06:00 The Places to Find UX Jobs 00:05:00

Professional Diploma in UX Design
By UX Design Institute
Become a Certified User Experience Professional Build a career in UX with the world’s only university credit-rated online UX course. Acquire the mindset, the skills and the confidence that make UX designers so valuable. A rewarding and meaningful career awaits. Why become a UX designer? Be in demand UX is a high-growth sector. The demand for UX designers far outstrips the supply of qualified professionals. Get well paid UX designers are highly paid. The average entry-level salary for a UX designer in the United Kingdom is £35,465 (PayScale, 2019) Love your job UX designers make an impact. They solve real-world problems using an exciting mix of research, design, technology and psychology. Study method Online, self-paced Duration 6 months Access to content 12 months Qualification Level 8 Diploma - User Experience Design Awarded by Glasgow Caledonian University Regulated by SQA Additional info Exam(s) / assessment(s) is included in price Tutor is available to students Description Duration: 6 months Get certified in six months following a flexible, structured learning path. Delivery: Online The course is delivered entirely online, including video modules, mentor-led webinars and support. Assessment: 2-hour exam Before getting certified, you'll be assessed during a two-hour exam taken online. Outcomes for you Think like a UX designer; adopt the mindset that sets them apart Showcase your knowledge with a portfolio of project work Speak with the confidence that comes from a true, deep understanding of UX Advance your career with job-ready skills Complete a university credit-rated course, valued by employers globally Become a Certified UX Professional Learn with us We’ve worked hard to design the best possible online learning experience for you. As well as an unmatched syllabus, our approach includes: Projects & portfolio Learn by doing with a series of real-world projects ideal for your UX portfolio. Mentors & webinars Be guided by our hand-picked, world-class mentors during monthly webinars. Structure & support Stay motivated with a structured programme supported by fellow students and our customer success team. What you’ll learn We’ve put together a university credit-rated curriculum that’s deep, rigorous and covers everything you need to know to become a certified UX professional and turbocharge your career. Module 01 - Introduction to UX design Module 02 - User research Module 03 - User goals Module 04 - Structure and navigation Module 05 - Interactions Module 06 - Design principles Module 07 - Design patterns Module 08 - Mobile Module 09 - Workflows Module 10 - Prototyping and handover Module 11 - AI and UX Module 12 - Creating your portfolio Module 13 - Career guidance Hub Tutorials for Figma Projects and portfolio - Projects that build into a portfolio Exam - 2-hour final exam Requirements Background You don’t need experience in design or technology to enrol in our courses, although having one or both is a definite bonus. Our students come from a diverse array of backgrounds, including project management, development, graphic design, product management, business analysis and so on. Commitment You do need to be motivated and committed. We set a high bar. Studying for one of our professional qualifications requires a certain amount of time, energy and focus. Our team will be there to support you along every step of the way but success will come as a result of your own diligence. Career path The average salary for entry level user experience designers is £28,000 The average salary for user experience designers with 1-5 years experience ranges from £29,000 to £50,000 The average salary for user experience managers/leads is £80,000 Information from LinkedIn Salary Reports, based on real jobs listings.

September 2025 Fundamentals Organisation & Relationship Systems Coaching Training
By CRR UK
CRRUK equips professionals with the concepts, skills and tools to build conscious, intentional relationships, and to coach relationship systems of any size.

Customer service just isn’t enough. Customer experience is where the secret to success lies. Build a loyal and fruitful customer base by learning how to design frictionless processes and build empathetic and solution-focused services with our bespoke courses, which include: Customer service vs customer experience The changing nature of customers and how to stay ahead Customer needs vs customer expectations How our behaviour affects those around us and how to use the power of influence Communicating with customers positively and effectively Moments that matter Building trust and integrity What to do when things go wrong

Essentials in UX and HCD Management (CPUX-M)
By Bunnyfoot
This one-day course introduces the field of user experience and provides an excellent entry point to our other specialised training courses. UX processes and practices have become a central component of product design, service design and web design.

Customer / User Research Methods
By Bunnyfoot
This one-day course introduces the field of user experience and provides an excellent entry point to our other specialised training courses. UX processes and practices have become a central component of product design, service design and web design.
Usability Testing
By Experience Thinkers
Gain robust techniques for obtaining feedback from end users throughout product design, and learn how to identify new opportunities for design improvement.
Information Architecture
By Experience Thinkers
Create a well-structured pathway to optimized content by understanding how information architecture applies to user experience design.