- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
18128 Courses delivered Online
Alarm Installation Course
By Hi-Tech Training
The Alarm Installation Course is designed to teach participants how to install an intruder alarm system in domestic, commercial or industrial premises. The Alarm Installation Course simulates the practical installation of many different alarm control panels. The course is designed to equip students with the skills and expertise to competently install a wide variety of Alarm systems on the market.

Embark on an essential journey with 'Resuscitation and Life Support: Vital Skills and Techniques.' Life is unpredictable, but possessing the aptitude to respond to dire emergencies can make all the difference. From understanding the fundamentals of resuscitation to mastering advanced cardiovascular life support, this course covers the spectrum. Seamlessly blending knowledge with technique, the curriculum not only prepares you for challenging moments but also nurtures the guardian in you. Learning Outcomes Comprehend the foundational principles of resuscitation and life support. Recognise and mitigate risks to maximise prevention. Execute both basic and advanced life support techniques. Demonstrate proficiency in airway management and defibrillation. Provide holistic post-resuscitation care, ensuring patient stability and recovery. Why choose this Resuscitation and Life Support: Vital Skills and Techniques course? Unlimited access to the course for a lifetime. Opportunity to earn a certificate accredited by the CPD Quality Standards after completing this course. Structured lesson planning in line with industry standards. Immerse yourself in innovative and captivating course materials and activities. Assessments are designed to evaluate advanced cognitive abilities and skill proficiency. Flexibility to complete the Resuscitation and Life Support: Vital Skills and Techniques Course at your own pace, on your own schedule. Receive full tutor support throughout the week, from Monday to Friday, to enhance your learning experience. Who is this Resuscitation and Life Support: Vital Skills and Techniques course for? Medical students and nursing trainees eager to strengthen their clinical skills. First responders aiming to refresh and update their life-saving techniques. Hospital staff seeking comprehensive training in resuscitation. Health educators passionate about teaching life-saving measures. Any individual motivated to equip themselves with emergency response capabilities. Career path Emergency Medical Technician (EMT): £21,000 - £35,000 Resuscitation Officer: £31,000 - £45,000 Paramedic: £24,000 - £38,000 Clinical Nurse Specialist in Cardiac Care: £30,000 - £47,000 Critical Care Physician: £62,000 - £105,000 Advanced Life Support Instructor: £25,000 - £40,000 Prerequisites This Resuscitation and Life Support: Vital Skills and Techniques does not require you to have any prior qualifications or experience. You can just enrol and start learning.This Resuscitation and Life Support: Vital Skills and Techniques was made by professionals and it is compatible with all PC's, Mac's, tablets and smartphones. You will be able to access the course from anywhere at any time as long as you have a good enough internet connection. Certification After studying the course materials, there will be a written assignment test which you can take at the end of the course. After successfully passing the test you will be able to claim the pdf certificate for £4.99 Original Hard Copy certificates need to be ordered at an additional cost of £8. Course Curriculum Module 01: Introduction to Resuscitation and Basic Life Support Introduction to Resuscitation and Basic Life Support 00:13:00 Module 02: Prevention and Preparation Prevention and Preparation 00:14:00 Module 03: Basic and Advanced Life Support Basic and Advanced Life Support 00:14:00 Module 04: Advanced Cardiovascular Life Support (ACLS) Advanced Cardiovascular Life Support (ACLS) 00:12:00 Module 05: Airway Management Airway Management 00:13:00 Module 06: Defibrillation Defibrillation 00:14:00 Module 07: Post-Resuscitation Care Post-Resuscitation Care 00:14:00

Overview This course is designed to evaluate the financial statement, budget and making an effective decision. It will help to understand Discounted Cash Flow and its techniques, applications of financial statements and decision-making process. In this programme, you will challenge representatives to learn how to make use of financial statements to assess the strategic or financial performance of an organization. It will help to understand DCF Discounted Cash Flow techniques along with their apps for financial making decisions and making use of ratios in order to identify the major areas of concern. Find out the elements like weaker financial signals, major success factors, and robust financial signals within your own industry. It Projects future performance assuredly through real-world budgeting.

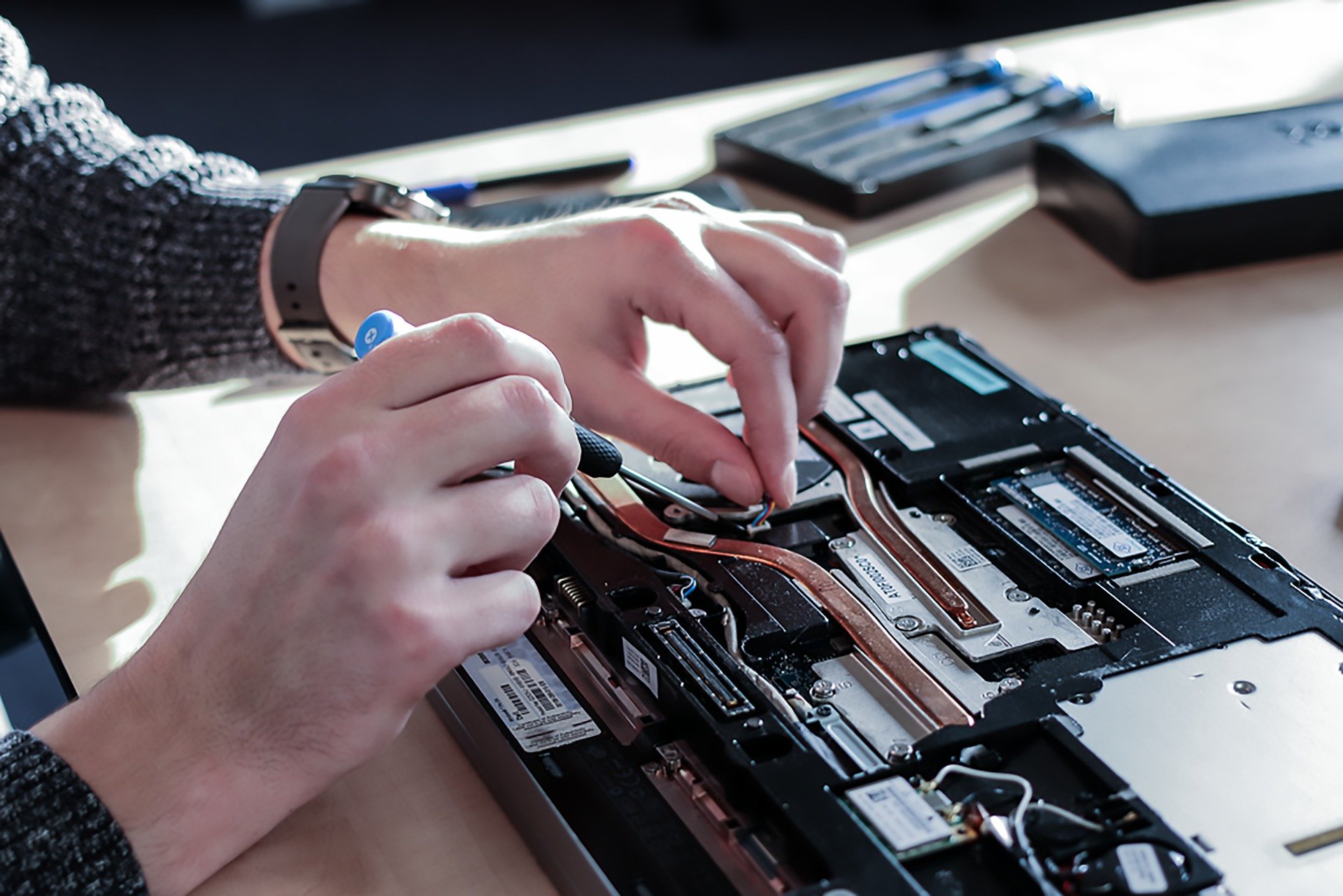
Computer Maintenance and Repair Course
By Hi-Tech Training
The Computer Maintenance & Repair Technician course aims to enable participants to diagnose and repair system level faults in computer-based systems at the foundation level.
Windows PowerShell training course description This course is intended for IT Professionals who are already experienced in general Windows Server and Windows Client administration, and who want to learn more about using Windows PowerShell for administration. No prior experience with any version of Windows PowerShell, or any scripting language, is assumed. This course is also suitable for IT Professionals already experienced in server administration, including Exchange Server, SharePoint Server, SQL Server, System Center, and others. What will you learn Work with Windows PowerShell pipeline. Query system information by using WMI and CIM. Work with variables, arrays, and hash tables. Write advanced scripts in Windows PowerShell. Administer remote computers. Use advanced Windows PowerShell techniques. Windows PowerShell training course details Who will benefit: IT professionals. Prerequisites: Supporting Windows Server Duration 5 days Windows PowerShell training course contents Getting started with Windows PowerShell Overview and background of Windows PowerShell, Understanding command syntax, Finding commands. Hands on Configuring Windows PowerShell console & ISE application. Hands on Finding and running basic commands, Using the About files. Cmdlets for administration Active Directory administration cmdlets, Network configuration cmdlets, Other server administration cmdlets. Hands on Windows Administration. Creating and managing Active Directory objects, Configuring network settings on Windows Server, Creating a web site. Working with the Windows PowerShell pipeline Understanding the pipeline, Selecting, sorting, and measuring objects, Filtering objects out of the pipeline, enumerating objects in the pipeline, Sending pipeline data as output. Hands on Using the pipeline. Selecting, sorting, and displaying data. Hands on Filtering objects. Hands on Enumerating objects. Hands on Sending output to a file. Exporting user information to a file. Understanding how the pipeline works Passing the pipeline data, Advanced considerations for pipeline data. Hands on Working with pipeline parameter binding. Predicting pipeline behaviour. Using PSProviders and PSDrives Using PSProviders, Using PSDrives. Hands on Using PSProviders and PSDrives Creating files and folders on a remote computer, Creating a registry key for your future scripts, Create a new Active Directory group. Querying system information by using WMI and CIM Understanding WMI and CIM, Querying data by using WMI and CIM, Making changes with WMI/CIM. Hands on Working with WMI and CIM. Querying information by using WMI, Querying information by using CIM, Invoking methods. Working with variables, arrays, and hash tables Manipulating variables, arrays and hash tables. Hands on Working with variables, Using arrays, Using hash tables. Basic scripting Introduction to scripting, Scripting constructs, Importing data from files. Hands on Basic scripting. Setting a script, Processing an array with a ForEach loop, Processing items by using If statements, Creating a random password, Creating users based on a CSV file. Advanced scripting Accepting user input, Overview of script documentation, Troubleshooting and error handling, Functions and modules. Hands on Accepting data from users. Querying disk information from remote computers, Updating the script to use alternate credentials, Documenting a script. Hands on Implementing functions and modules. Creating a logging function, Adding error handling to a script, Converting a function to a module. Administering Remote Computers Using basic Windows PowerShell remoting, Using advanced Windows PowerShell remoting techniques, Using PSSessions. Hands on Using basic remoting. Enabling remoting on the local computer, Performing one-to-one remoting, Performing one-to-many remoting. Hands on Using PSSessions. Using implicit remoting, Managing multiple computers. Using background jobs and scheduled jobs Using background jobs, Using scheduled jobs. Hands on Using background jobs and scheduled jobs. Starting and managing jobs, Creating a scheduled job. Using advanced Windows PowerShell techniques Creating profile scripts, Using advanced techniques. Hands on Practicing advanced techniques. Creating a profile script, Verifying the validity of an IP address, Reporting disk information, Configuring NTFS permissions, Creating user accounts with passwords from a CSV file. Hands on Practicing script development (optional)

Professional Certificate in Understanding the Investment Appraisal Techniques in London 2024
4.9(261)By Metropolitan School of Business & Management UK
This course is designed to enable the learner to analyse and appraise investment options using different investment appraisal techniques. The learner will also be able to understand the costing system involved in investment decisions and generally prevalent in the business environment. After the successful completion of this lecture, you will be able to understand the following: The concept of investment. The motives of investment. The meaning of the money market and its various functions. Understand the various instrument of the money market. The concept of the Costing System. The various types of costing systems. The different classification of cost. Various cost control of systems. Calculation of cumulative cost variance. The various strategies of pricing policy. VIDEO - Course Structure and Assessment Guidelines Watch this video to gain further insight. Navigating the MSBM Study Portal Watch this video to gain further insight. Interacting with Lectures/Learning Components Watch this video to gain further insight. Understanding the Investment Appraisal Techniques Self-paced pre-recorded learning content on this topic. Quiz: Understanding The Investment Appraisal Techniques Put your knowledge to the test with this quiz. Read each question carefully and choose the response that you feel is correct. All MSBM courses are accredited by the relevant partners and awarding bodies. Please refer to MSBM accreditation in about us for more details. There are no strict entry requirements for this course. Work experience will be added advantage to understanding the content of the course. The certificate is designed to enhance the knowledge of the learner in the field. This certificate is for everyone eager to know more and gets updated on current ideas in their respective field. We recommend this certificate for the following audience. CEO, Director, Manager, Supervisor Learning and Development Manager Finance Manager Investment Manager/specialist Market behaviour Specialist Operations Manager Team Lead Average Completion Time 2 Weeks Accreditation 1 CPD Hour Level Advanced Start Time Anytime 100% Online Study online with ease. Unlimited Access 24/7 unlimited access with pre-recorded lectures. Low Fees Our fees are low and easy to pay online.

Dive into the multifaceted world of pest control with 'Pest Control Techniques: Effective Solutions for Pest Management'. With escalating concerns about pests threatening our homes, agriculture, and environment, this comprehensive course offers a deep dive into the principles of managing these threats. Delve into a curriculum, richly designed with modules ranging from understanding the anatomy of various pests to the intricacies of pesticide formulations. Furthermore, this course takes a responsible approach, not just instructing you on how to handle pests, but ensuring you understand the environmental repercussions of your actions and the UK's pest control regulations. The course's structure ensures that learners obtain an all-encompassing understanding. Start with the basics in the introductory module, before navigating the myriad types of pests and exploring in-depth the solutions to counter them. By the end of your journey, you'll not only know how to manage pests but will do so with the environment's well-being and the laws of the land in mind. Learning Outcomes Gain an understanding of the diverse world of pests and their anatomy. Acquire knowledge about various pesticide formulations, both liquid and dry. Learn about the different methods of pest management, including IPM. Understand the environmental consequences linked with pest control. Become proficient in the UK's regulations concerning pest control. Why buy this Pest Control Techniques: Effective Solutions for Pest Management? Unlimited access to the course for forever Digital Certificate, Transcript, student ID all included in the price Absolutely no hidden fees Directly receive CPD accredited qualifications after course completion Receive one to one assistance on every weekday from professionals Immediately receive the PDF certificate after passing Receive the original copies of your certificate and transcript on the next working day Easily learn the skills and knowledge from the comfort of your home Certification After studying the course materials of the Pest Control Techniques: Effective Solutions for Pest Management there will be a written assignment test which you can take either during or at the end of the course. After successfully passing the test you will be able to claim the pdf certificate for £5.99. Original Hard Copy certificates need to be ordered at an additional cost of £9.60. Who is this Pest Control Techniques: Effective Solutions for Pest Management course for? Individuals interested in beginning a career in pest management. Gardeners seeking knowledge on safe and effective pest control methods. Farmers aiming to enhance their pest management techniques for better yields. Homeowners looking for effective ways to protect their homes from pests. Environmental enthusiasts keen to understand the balance between pest control and ecological impact. Prerequisites This Pest Control Techniques: Effective Solutions for Pest Management does not require you to have any prior qualifications or experience. You can just enrol and start learning.This Pest Control Techniques: Effective Solutions for Pest Management was made by professionals and it is compatible with all PC's, Mac's, tablets and smartphones. You will be able to access the course from anywhere at any time as long as you have a good enough internet connection. Career path Pest Control Officer: £18,000 - £25,000 per annum. Agricultural Consultant: £25,000 - £40,000 per annum. Horticulturist Specialist: £20,000 - £30,000 per annum. Environmental Impact Assessor: £30,000 - £45,000 per annum. Plant Pathologist: £28,000 - £35,000 per annum. Pesticide Product Developer: £32,000 - £50,000 per annum Course Curriculum Module 01: Introduction to Pest Control Introduction to Pest Control 00:12:00 Module 02: Different Types of Pests Different Types of Pests 00:16:00 Module 03: Insects and Mites Anatomy and Prevention Insects and Mites Anatomy and Prevention 00:15:00 Module 04: Weeds Control Weeds Control 00:12:00 Module 05: Pesticide Formulations (Liquid and Dry) Pesticide Formulations (Liquid and Dry) 00:19:00 Module 06: Pesticide Formulations and Adjuvants Pesticide Formulations and Adjuvants 00:15:00 Module 07: Plant Diseases and Disorders Plant Diseases and Disorders 00:14:00 Module 08: Pest Management Methods and IPM Pest Management Methods and IPM 00:19:00 Module 09: Pesticide Application Pesticide Application 00:17:00 Module 10: Environmental Impacts of Pest control Environmental Impacts of Pest control 00:14:00 Module 11: Regulations of Pest Control in the UK Regulations of Pest Control in the UK 00:16:00

Advanced Sales & Marketing Techniques for ESL Teachers
By The Teachers Training
Advanced Sales & Marketing Techniques for ESL Teachers is yet another 'Teacher's Choice' course from Teachers Training for a complete understanding of the fundamental topics. You are also entitled to exclusive tutor support and a professional CPD-accredited certificate in addition to the special discounted price for a limited time. Just like all our courses, this Advanced Sales & Marketing Techniques for ESL Teachers and its curriculum have also been designed by expert teachers so that teachers of tomorrow can learn from the best and equip themselves with all the necessary skills. Consisting of several modules, the course teaches you everything you need to succeed in this profession. The course can be studied part-time. You can become accredited within 1 hour studying at your own pace. Your qualification will be recognised and can be checked for validity on our dedicated website. Why Choose Teachers Training Some of our features are: This is a dedicated website for teaching 24/7 tutor support Interactive Content Affordable price Courses accredited by the UK's top awarding bodies 100% online Flexible deadline Entry Requirements No formal entry requirements. You need to have: Passion for learning A good understanding of the English language numeracy and IT Desire for entrepreneurship over the age of 16. Assessment The assessment is straightforward, you need to complete the assignment questions that will be provided to you at the end of the course, you can complete the assignment anytime you want. After you complete and submit your assignment, our tutors will assess your assignment and give you feedback if needed. After your assignment has been assessed and you have passed, you will be qualified and will be able to apply for a course completion certificate. Certification CPD Certification from The Teachers Training Successfully completing the MCQ exam of this course qualifies you for a CPD-accredited certificate from The Teachers Training. You will be eligible for both PDF copy and hard copy of the certificate to showcase your achievement however you wish. You can get your digital certificate (PDF) for £4.99 only Hard copy certificates are also available, and you can get one for only £10.99 You can get both PDF and Hard copy certificates for just £12.99! The certificate will add significant weight to your CV and will give you a competitive advantage when applying for jobs. Sales & Marketing Marketing Strategy 00:08:00 Keeping Students Satisfied for Repeat Business 00:05:00 Creating a Unique & Awesome Curriculum 00:06:00 How to Guarantee Success 00:08:00 Understanding the Business Analyzing the Business Model 00:15:00 Having an Efficient Business System 00:07:00 How to Launch on a Shoe String Budget 00:06:00

Simple Strategies to Reduce Stress
By IIL Europe Ltd
Simple Strategies to Reduce Stress Stress can affect your ability to think clearly and rationally and to perform well. This session aims to help you better deal with stress by sharing key insights and strategies to reduce stress and optimize your work-life balance, particularly as we all cope with the consequences of COVID-19.The session will also address the biology of belonging and how we have been affected by this over the past year. Learn coping techniques to deal with a different way of working and living Recognize the symptoms and causes of stress Discover simple stress busting techniques to manage & reduce the effects of stress in your life Create a simple personal plan to rise above stress for a healthier & more productive lifestyle

EC-Council Computer Hacking Forensic Investigator (CHFI) v10.0
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for The CHFI course will benefit: Police and other laws enforcement personnel Defense and Military personnel e-Business Security professionals Systems administrators Legal professionals Banking, Insurance and other professionals Government agencies Overview At the end of this course, you will possess the skills needed to: Understand the fundamentals of computer forensics Understand the computer forensic investigation process Describe in detail different types of hard disks and file systems Understand data acquisition and duplication Counteract anti-forensic techniques Leverage forensic skills in Windows, Linux, and Mac Investigate web attacks Understand dark web forensics Deploy forensic techniques for databases, cloud, and networks Investigate email crimes including malware Perform forensics in mobile and IoT environments Every crime leaves a digital footprint, and you need the skills to track those footprints. In this course, students will learn to unravel these pieces of evidence, decode them and report them. From decoding a hack to taking legal action against the perpetrators, they will become an active respondent in times of cyber-breaches. Computer Forensics in Today?s World 1.1. Understand the Fundamentals of Computer Forensics 1.2. Understand Cybercrimes and their Investigation Procedures 1.3. Understand Digital Evidence 1.4. Understand Forensic Readiness, Incident Response and the Role of SOC (Security Operations Center) in Computer Forensics 1.5. Identify the Roles and Responsibilities of a Forensic Investigator 1.6. Understand the Challenges Faced in Investigating Cybercrimes 1.7. Understand Legal Compliance in Computer Forensics Computer Forensics Investigation Process 2.1. Understand the Forensic Investigation Process and its Importance 2.2. Understand the Pre-investigation Phase 2.3. Understand First Response 2.4. Understand the Investigation Phase 2.5. Understand the Post-investigation Phase Understanding Hard Disks and File Systems 3.1. Describe Different Types of Disk Drives and their Characteristics 3.2. Explain the Logical Structure of a Disk 3.3. Understand Booting Process of Windows, Linux and Mac Operating Systems 3.4. Understand Various File Systems of Windows, Linux and Mac Operating Systems 3.5. Examine File System Using Autopsy and The Sleuth Kit Tools 3.6 Understand Storage Systems 3.7. Understand Encoding Standards and Hex Editors 3.8. Analyze Popular File Formats Using Hex Editor Data Acquisition and Duplication 4.1. Understand Data Acquisition Fundamentals 4.2. Understand Data Acquisition Methodology 4.3. Prepare an Image File for Examination Defeating Anti-forensics Techniques 5.1. Understand Anti-forensics Techniques 5.2. Discuss Data Deletion and Recycle Bin Forensics 5.3. Illustrate File Carving Techniques and Ways to Recover Evidence from Deleted Partitions 5.4. Explore Password Cracking/Bypassing Techniques 5.5. Detect Steganography, Hidden Data in File System Structures, Trail Obfuscation, and File Extension Mismatch 5.6. Understand Techniques of Artifact Wiping, Overwritten Data/Metadata Detection, and Encryption 5.7. Detect Program Packers and Footprint Minimizing Techniques 5.8. Understand Anti-forensics Countermeasures Windows Forensics 6.1. Collect Volatile and Non-volatile Information 6.2. Perform Windows Memory and Registry Analysis 6.3. Examine the Cache, Cookie and History Recorded in Web Browsers 6.4. Examine Windows Files and Metadata 6.5. Understand ShellBags, LNK Files, and Jump Lists 6.6. Understand Text-based Logs and Windows Event Logs Linux and Mac Forensics 7.1. Understand Volatile and Non-volatile Data in Linux 7.2. Analyze Filesystem Images Using The Sleuth Kit 7.3. Demonstrate Memory Forensics Using Volatility & PhotoRec 7.4. Understand Mac Forensics Network Forensics 8.1. Understand Network Forensics 8.2. Explain Logging Fundamentals and Network Forensic Readiness 8.3. Summarize Event Correlation Concepts 8.4. Identify Indicators of Compromise (IoCs) from Network Logs 8.5. Investigate Network Traffic 8.6. Perform Incident Detection and Examination with SIEM Tools 8.7. Monitor and Detect Wireless Network Attacks Investigating Web Attacks 9.1. Understand Web Application Forensics 9.2. Understand Internet Information Services (IIS) Logs 9.3. Understand Apache Web Server Logs 9.4. Understand the Functionality of Intrusion Detection System (IDS) 9.5. Understand the Functionality of Web Application Firewall (WAF) 9.6. Investigate Web Attacks on Windows-based Servers 9.7. Detect and Investigate Various Attacks on Web Applications Dark Web Forensics 10.1. Understand the Dark Web 10.2. Determine How to Identify the Traces of Tor Browser during Investigation 10.3. Perform Tor Browser Forensics Database Forensics 11.1. Understand Database Forensics and its Importance 11.2. Determine Data Storage and Database Evidence Repositories in MSSQL Server 11.3. Collect Evidence Files on MSSQL Server 11.4. Perform MSSQL Forensics 11.5. Understand Internal Architecture of MySQL and Structure of Data Directory 11.6. Understand Information Schema and List MySQL Utilities for Performing Forensic Analysis 11.7. Perform MySQL Forensics on WordPress Web Application Database Cloud Forensics 12.1. Understand the Basic Cloud Computing Concepts 12.2. Understand Cloud Forensics 12.3. Understand the Fundamentals of Amazon Web Services (AWS) 12.4. Determine How to Investigate Security Incidents in AWS 12.5. Understand the Fundamentals of Microsoft Azure 12.6. Determine How to Investigate Security Incidents in Azure 12.7. Understand Forensic Methodologies for Containers and Microservices Investigating Email Crimes 13.1. Understand Email Basics 13.2. Understand Email Crime Investigation and its Steps 13.3. U.S. Laws Against Email Crime Malware Forensics 14.1. Define Malware and Identify the Common Techniques Attackers Use to Spread Malware 14.2. Understand Malware Forensics Fundamentals and Recognize Types of Malware Analysis 14.3. Understand and Perform Static Analysis of Malware 14.4. Analyze Suspicious Word and PDF Documents 14.5. Understand Dynamic Malware Analysis Fundamentals and Approaches 14.6. Analyze Malware Behavior on System Properties in Real-time 14.7. Analyze Malware Behavior on Network in Real-time 14.8. Describe Fileless Malware Attacks and How they Happen 14.9. Perform Fileless Malware Analysis - Emotet Mobile Forensics 15.1. Understand the Importance of Mobile Device Forensics 15.2. Illustrate Architectural Layers and Boot Processes of Android and iOS Devices 15.3. Explain the Steps Involved in Mobile Forensics Process 15.4. Investigate Cellular Network Data 15.5. Understand SIM File System and its Data Acquisition Method 15.6. Illustrate Phone Locks and Discuss Rooting of Android and Jailbreaking of iOS Devices 15.7. Perform Logical Acquisition on Android and iOS Devices 15.8. Perform Physical Acquisition on Android and iOS Devices 15.9. Discuss Mobile Forensics Challenges and Prepare Investigation Report IoT Forensics 16.1. Understand IoT and IoT Security Problems 16.2. Recognize Different Types of IoT Threats 16.3. Understand IoT Forensics 16.4. Perform Forensics on IoT Devices
