- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
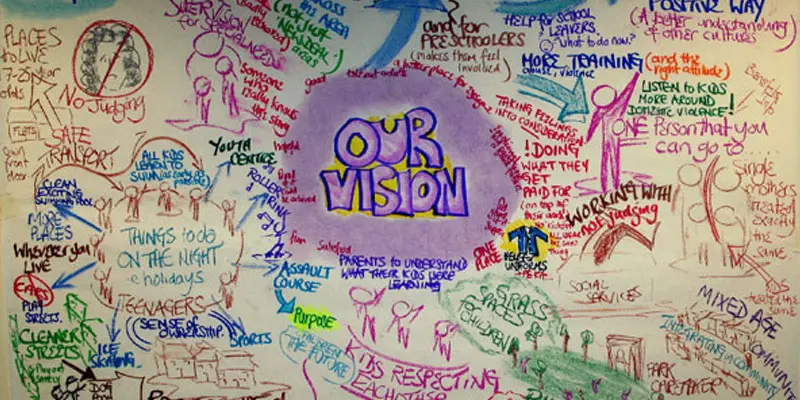
WORKING WITH PARENTS AND CARERS
By Inclusive Solutions
In this practical and engaging workshop there is input on building an effective team around a child, problem solving as a team, improving communication and handling conflict. Communication with parents, problem solving and collaborating is explored. Empathy with parents who are ‘labelled’ is encouraged. Course Category Parents and Carers Description In this practical and engaging workshop there is input on building an effective team around a child, problem solving as a team, improving communication and handling conflict. Communication with parents, problem solving and collaborating is explored. Empathy with parents who are ‘labelled’ is encouraged. A key aspect of this day is ‘reframing’ how we think about the most difficult, hard to work with parents who attract many labels. Participants soon discover that they are more similar than they realise to those labelled ‘others’. The day gives those present opportunities to reflect on their attitudes and practice in relation to parents who are different. Practical ideas for joint problem solving and active engagement are fully explored. Testimonials “Made me more aware of how to approach parents and carers” “It (the conference) couldn’t have been improved. All the speakers were good” “I’ll have a more positive approach to welcoming people” “It will encourage us as practitioners to listen and think a little more. Learning Objectives Increased confidence in working with parents Access to a wider range of practical and thoughtful strategies when collaborating with parents and carers Deeper understanding of core values surrounding inclusion of disabled children in collaboration with parents and carers Opportunity to reflect on professional attitudes and behaviour towards parents with a focus on labelling and stigmatisation New skills and processes to make joint work successful Who Is It For ? Early Years and School based Practitioners Children Centre Staff Heads and Deputies SENCOs Advanced Skills Teachers Primary and secondary teachers Local Authority Support Services Social Workers Health Workers Course Content The course answers the questions: Why is this parent impossible to work with? Where do I begin to communicate with some parents? How can I collaborate with parents and carers to include high profile children or young people? Best delivered over the course of a full day we will cover: The importance of WELCOME Labelling and reframing: Setting the tone: Reframing language to describe parents Providing parents with insights about children’s behaviour using stories Circle of Courage as applied to parents Circles of Support The Intentional Building of Relationships Not doing it alone – The Importance of Teams in developing inclusive practice Problem solving: Circles of Adults/Solution Circles Community Guides If you liked this you may like: COMMUNITY CIRCLES
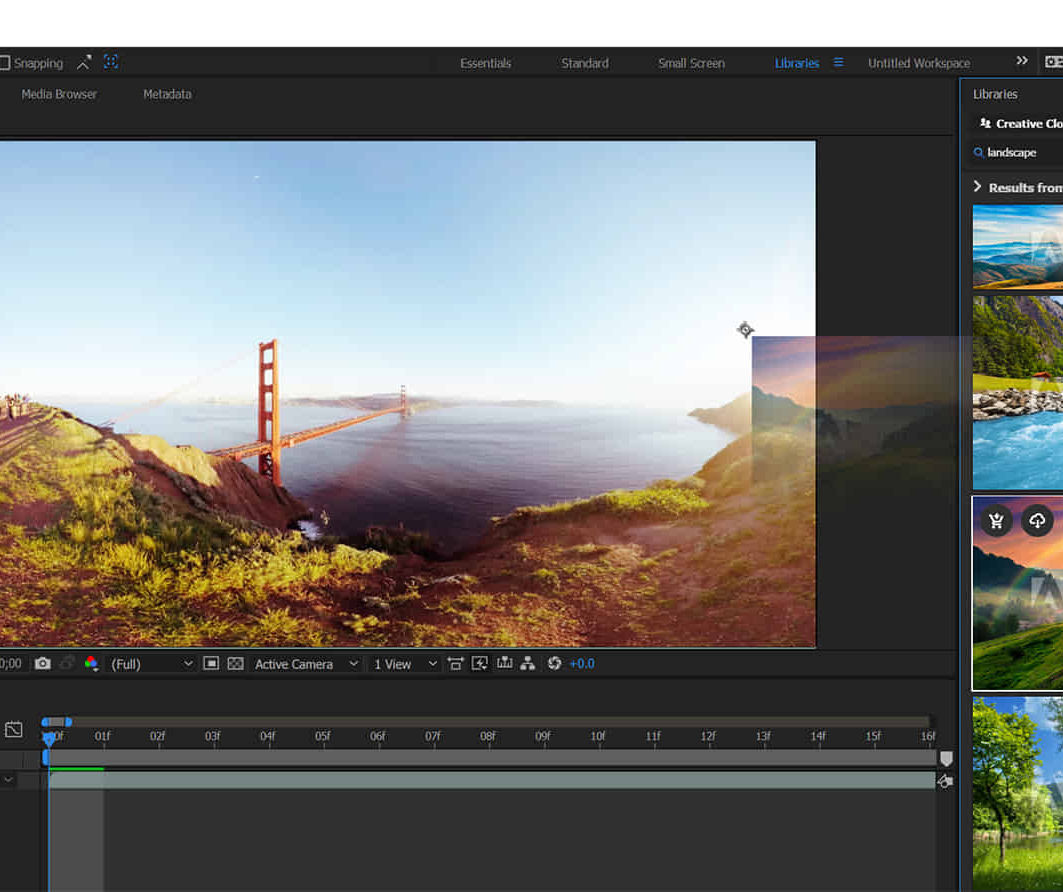
Adobe After Effects Fast-Track Course (Live Online)
By ATL Autocad Training London
Adobe After Effects Fast-Track Course (Live Online) through our comprehensive course, beginners, intermediate, and advanced learners. Perfect your skills at the top Training Centre in the UK. Dive into motion graphics and animation with hands-on training led by expert tutors ensuring a practical and interactive learning experience. Click here for more info: Website Duration: 5 hours Approach: Personalized 1-on-1sessions and Customized content. Schedule: Select your preferred hour from Monday to Saturday between 9 am and 7 pm. Adobe After Effects Essentials (5-hour course) Session 1: Introduction to After Effects (1 hour) Overview of After Effects and its applications in motion graphics and visual effects. Understanding the workspace and interface. Importing and organizing assets for seamless workflow. Creating projects and compositions. Session 2: Animation Basics (1.5 hours) Working with layers: Adding, editing, and arranging layers in the timeline. Keyframe animation: Introduction to keyframes and creating simple animations. Motion paths: Manipulating motion paths for dynamic animations. Easing motion: Applying ease in and ease out to smoothen animations. Animation presets: Utilizing built-in presets for efficient animation. Session 3: Effects and Compositing (1.5 hours) Applying effects: Adding visual effects to layers and compositions. Compositing techniques: Understanding blending modes and layer styles. Masking and track mattes: Using masks to control the visibility of layers and apply effects. Motion tracking: Applying tracking data to objects in a scene. Session 4: Text and Shape Animation (1 hour) Text animation: Creating and animating text layers with different styles. Shape layers: Introduction to shape layers and their applications. Animating shapes: Using shape layers to create dynamic animations. Session 5: Final Project and Exporting (1 hour) Applying all the learned techniques to create a final motion graphics project. Refining the project and adding finishing touches. Understanding export settings and rendering the final output. Read the usefull Blogs https://realanimationworks.com/government-funded-interior-design-courses-in-london-your-path-to-creative-excellence/ Upon completing the Adobe After Effects Essentials course, participants will: Master the Interface: Understand After Effects' layout, tools, and key functionalities, gaining confidence in navigating the software. Animation Proficiency: Gain expertise in animating images, videos, and text layers using keyframes, easing techniques, and smooth transitions. Effects Application: Learn to apply, customize, and animate various visual effects, enhancing the overall visual appeal of multimedia projects. Masking and Precision Editing: Master the art of creating and animating masks for detailed and accurate editing, enabling seamless integration of visual elements. Advanced Compositing Skills: Explore advanced compositing techniques for combining multiple elements seamlessly, achieving professional-level visual integration. Export and Rendering Mastery: Understand export settings, ensuring optimal video quality for diverse output formats. Learn the art of efficient rendering for polished final products. Certificate of Completion: Receive a certificate validating the successful completion of the course, showcasing newfound skills to potential employers or clients. Practical Knowledge: Acquire practical insights and techniques applicable to real-world projects, ensuring the ability to create visually captivating multimedia content independently. Lifetime Learning Support: Benefit from lifetime email support, enabling continuous learning and assistance with any post-course queries or challenges. After Effects CC Training: From Novices to Experts Immerse yourself in the world of motion graphics and VFX with our Adobe Certified After Effects Courses, suitable for total novices and experts alike. Learn to create captivating motion graphics, smooth animations, and stunning special effects in a professional environment. Choose from four learning options: London Classroom: Attend in-person sessions 1-2-1 in our dynamic studio. Live Online Classes: Join interactive classes from the comfort of your home or office. Bespoke Training: Tailor the course to your specific needs and preferences. Whichever path you select, all options cover the same lesson plan delivered by our Certified Professional Trainers. Rest assured, your learning experience is fully supported by our 100% Satisfaction Guarantee. Personalized After Effects Training: Tailored for You! Custom one-on-one sessions, in-person or online. Work with your files, learn at your pace. Expert trainers in London. Team training available. Benefits: Unlimited post-course support via phone/email. Access to training materials and a handbook. Free pre-course consultation. Achieve impressive results: create captivating videos, animated logos, and more. Master cinematic effects and enhance your visual storytelling skills.
Cloud Operations on AWS
By Nexus Human
Duration 3 Days 18 CPD hours This course is intended for System administrators and operators who are operating in the AWS Cloud Informational technology workers who want to increase the system operations knowledge. Overview Identify the AWS services that support the different phases of Operational Excellence, an AWS Well-Architected Framework pillar Manage access to AWS resources using AWS accounts and organizations and AWS Identity and Access Management (IAM) Maintain an inventory of in-use AWS resources by using AWS services, such as AWS Systems Manager, AWS CloudTrail, and AWS Config Develop a resource deployment strategy using metadata tags, Amazon Machine Images (AMIs), and AWS Control Tower to deploy and maintain an AWS cloud environment Automate resource deployment by using AWS services, such as AWS CloudFormation and AWS Service Catalog Use AWS services to manage AWS resources through CloudOps lifecycle processes, such as deployments and patches Configure a highly available cloud environment that uses AWS services, such as Amazon Route 53 and Elastic Load Balancing, to route traffic for optimal latency and performance Configure AWS Auto Scaling and Amazon EC2 Auto Scaling to scale out your cloud environment based on demand Use Amazon CloudWatch and associated features, such as alarms, dashboards, and widgets, to monitor your cloud environment Manage permissions and track activity in your cloud environment by using AWS services, such as AWS CloudTrail and AWS Config Deploy your resources to an Amazon Virtual Private Cloud (Amazon VPC), establish necessary connectivity to your Amazon VPC, and protect your resources from disruptions of service State the purpose, benefits, and appropriate use cases for mountable storage in your AWS Cloud environment Explain the operational characteristics of object storage in the AWS Cloud, including Amazon Simple Storage Service (Amazon S3) and Amazon S3 Glacier Build a comprehensive cost model to help gather, optimize, and predict your cloud costs by using services such as AWS Cost Explorer and the AWS Cost & Usage Report This course teaches systems operators and anyone performing cloud operations functions how to manage and operate automatable and repeatable deployments of networks and systems on AWS. You will learn about cloud operations functions, such as installing, configuring, automating, monitoring, securing, maintaining, and troubleshooting these services, networks, and systems. The course also covers specific AWS features, tools, and best practices related to these functions. Prerequisites Successfully completed the AWS Technical Essentials course Background in either software development or systems administration Proficiency in maintaining operating systems at the command line, such as shell scripting in Linux environments or cmd/PowerShell in Windows Basic knowledge of networking protocols (TCP/IP, HTTP) 1 - Introduction to Cloud Operations on AWS What is Cloud Operations AWS Well-Architected Framework AWS Well-Architected Tool 2 - Access Management AWS Identity and Access Management (IAM) Resources, accounts, and AWS Organizations 3 - System Discovery Methods to interact with AWS services Tools for automating resource discovery Inventory with AWS Systems Manager and AWS Config Hands-On Lab: Auditing AWS Resources with AWS Systems Manager and AWS Config 4 - Deploy and Update Resources Cloud Operations in deployments Tagging strategies Deployment using Amazon Machine Images (AMIs) Deployment using AWS Control Tower 5 - Automate Resource Deployment Deployment using AWS CloudFormation Deployment using AWS Service Catalog Hands-On Lab: Infrastructure as Code 6 - Manage Resources AWS Systems Manager Hands-On Lab: Operations as Code 7 - Configure Highly Available Systems Distributing traffic with Elastic Load Balancing Amazon Route 53 8 - Automate Scaling Scaling with AWS Auto Scaling Scaling with Spot Instances Managing licenses with AWS License Manager 9 - Monitor and Maintain System Health Monitoring and maintaining healthy workloads Monitoring AWS infrastructure Monitoring applications Hands-On Lab: Monitor Applications and Infrastructure 10 - Data Security and System Auditing Maintaining a strong identity and access foundation Implementing detection mechanisms Automating incident remediation 11 - Operate Secure and Resilient Networks Building a secure Amazon Virtual Private Cloud (Amazon VPC) Networking beyond the VPC 12 - Mountable Storage Configuring Amazon Elastic Block Store (Amazon EBS) Sizing Amazon EBS volumes for performance Using Amazon EBS snapshots Using Amazon Data Lifecycle Manager to manage your AWS resources Creating backup and data recovery plans Configuring shared file system storage Hands-On Lab: Automating with AWS Backup for Archiving and Recovery 13 - Object Storage Deploying Amazon Simple Storage Service (Amazon S3) Managing storage lifecycles on Amazon S3 14 - Cost Reporting, Alerts, and Optimization Gaining AWS cost awareness Using control mechanisms for cost management Optimizing your AWS spend and usage Hands-On Lab: Capstone lab for CloudOps Additional course details: Nexus Humans Cloud Operations on AWS training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the Cloud Operations on AWS course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

Security Engineering on AWS
By Nexus Human
Duration 3 Days 18 CPD hours This course is intended for This course is intended for security engineers, security architects, and information security professionals. Overview Identify security benefits and responsibilities of using the AWS Cloud Build secure application infrastructures Protect applications and data from common security threats Perform and automate security checks Configure authentication and permissions for applications and resources Monitor AWS resources and respond to incidents Capture and process logs Create and configure automated and repeatable deployments with tools such as AMIs and AWS CloudFormation This course demonstrates how to efficiently use AWS security services to stay secure in the AWS Cloud. The course focuses on the security practices that AWS recommends for enhancing the security of your data and systems in the cloud. The course highlights the security features of AWS key services including compute, storage, networking, and database services. You will also learn how to leverage AWS services and tools for automation, continuous monitoring and logging, and responding to security incidents. Prerequisites We recommend that attendees of this course have: Working knowledge of IT security practices and infrastructure concepts Familiarity with cloud computing concepts Completed AWS Security Essentials and Architecting on AWS courses 1 - Security on AWS Security in the AWS cloud AWS Shared Responsibility Model Incident response overview DevOps with Security Engineering 2 - Identifying Entry Points on AWS Identify the different ways to access the AWS platform Understanding IAM policies IAM Permissions Boundary IAM Access Analyzer Multi-factor authentication AWS CloudTrail 3 - Security Considerations: Web Application Environments Threats in a three-tier architecture Common threats: user access Common threats: data access AWS Trusted Advisor 4 - Application Security Amazon Machine Images Amazon Inspector AWS Systems Manager 5 - Data Security Data protection strategies Encryption on AWS Protecting data at rest with Amazon S3, Amazon RDS, Amazon DynamoDB Protecting archived data with Amazon S3 Glacier Amazon S3 Access Analyzer Amazon S3 Access Points 6 - Securing Network Communications Amazon VPC security considerations Amazon VPC Traffic Mirroring Responding to compromised instances Elastic Load Balancing AWS Certificate Manager 7 - Monitoring and Collecting Logs on AWS Amazon CloudWatch and CloudWatch Logs AWS Config Amazon Macie Amazon VPC Flow Logs Amazon S3 Server Access Logs ELB Access Logs 8 - Processing Logs on AWS Amazon Kinesis Amazon Athena 9 - Security Considerations: Hybrid Environments AWS Site-to-Site and Client VPN connections AWS Direct Connect AWS Transit Gateway 10 - Out-Of-Region Protection Amazon Route 53 AWS WAF Amazon CloudFront AWS Shield AWS Firewall Manager DDoS mitigation on AWS 11 - Security Considerations: Serverless Environments Amazon Cognito Amazon API Gateway AWS Lambda 12 - Threat Detection and Investigation Amazon GuardDuty AWS Security Hub Amazon Detective 13 - Secrets Management on AWS AWS KMS AWS CloudHSM AWS Secrets Manager 14 - Automation and Security by Design AWS CloudFormation AWS Service Catalog 15 - Account Management and Provisioning on AWS AWS Organizations AWS Control Tower AWS SSO AWS Directory Service

SC-200T00 Microsoft Security Operations Analyst
By Nexus Human
Duration 4 Days 24 CPD hours This course is intended for The Microsoft Security Operations Analyst collaborates with organizational stakeholders to secure information technology systems for the organization. Their goal is to reduce organizational risk by rapidly remediating active attacks in the environment, advising on improvements to threat protection practices, and referring violations of organizational policies to appropriate stakeholders. Responsibilities include threat management, monitoring, and response by using a variety of security solutions across their environment. The role primarily investigates, responds to, and hunts for threats using Microsoft Sentinel, Microsoft Defender for Cloud, Microsoft 365 Defender, and third-party security products. Since the Security Operations Analyst consumes the operational output of these tools, they are also a critical stakeholder in the configuration and deployment of these technologies. Learn how to investigate, respond to, and hunt for threats using Microsoft Sentinel, Microsoft Defender for Cloud, and Microsoft 365 Defender. In this course you will learn how to mitigate cyberthreats using these technologies. Specifically, you will configure and use Microsoft Sentinel as well as utilize Kusto Query Language (KQL) to perform detection, analysis, and reporting. The course was designed for people who work in a Security Operations job role and helps learners prepare for the exam SC-200: Microsoft Security Operations Analyst. Prerequisites Basic understanding of Microsoft 365 Fundamental understanding of Microsoft security, compliance, and identity products Intermediate understanding of Windows 10 Familiarity with Azure services, specifically Azure SQL Database and Azure Storage Familiarity with Azure virtual machines and virtual networking Basic understanding of scripting concepts. 1 - Introduction to Microsoft 365 threat protection Explore Extended Detection & Response (XDR) response use cases Understand Microsoft Defender XDR in a Security Operations Center (SOC) Explore Microsoft Security Graph Investigate security incidents in Microsoft Defender XDR 2 - Mitigate incidents using Microsoft 365 Defender Use the Microsoft Defender portal Manage incidents Investigate incidents Manage and investigate alerts Manage automated investigations Use the action center Explore advanced hunting Investigate Microsoft Entra sign-in logs Understand Microsoft Secure Score Analyze threat analytics Analyze reports Configure the Microsoft Defender portal 3 - Protect your identities with Microsoft Entra ID Protection Microsoft Entra ID Protection overview Detect risks with Microsoft Entra ID Protection policies Investigate and remediate risks detected by Microsoft Entra ID Protection 4 - Remediate risks with Microsoft Defender for Office 365 Automate, investigate, and remediate Configure, protect, and detect Simulate attacks 5 - Safeguard your environment with Microsoft Defender for Identity Configure Microsoft Defender for Identity sensors Review compromised accounts or data Integrate with other Microsoft tools 6 - Secure your cloud apps and services with Microsoft Defender for Cloud Apps Understand the Defender for Cloud Apps Framework Explore your cloud apps with Cloud Discovery Protect your data and apps with Conditional Access App Control Walk through discovery and access control with Microsoft Defender for Cloud Apps Classify and protect sensitive information Detect Threats 7 - Respond to data loss prevention alerts using Microsoft 365 Describe data loss prevention alerts Investigate data loss prevention alerts in Microsoft Purview Investigate data loss prevention alerts in Microsoft Defender for Cloud Apps 8 - Manage insider risk in Microsoft Purview Insider risk management overview Create and manage insider risk policies Investigate insider risk alerts Take action on insider risk alerts through cases Manage insider risk management forensic evidence Create insider risk management notice templates 9 - Investigate threats by using audit features in Microsoft Defender XDR and Microsoft Purview Standard Explore Microsoft Purview Audit solutions Implement Microsoft Purview Audit (Standard) Start recording activity in the Unified Audit Log Search the Unified Audit Log (UAL) Export, configure, and view audit log records Use audit log searching to investigate common support issues 10 - Investigate threats using audit in Microsoft Defender XDR and Microsoft Purview (Premium) Explore Microsoft Purview Audit (Premium) Implement Microsoft Purview Audit (Premium) Manage audit log retention policies Investigate compromised email accounts using Purview Audit (Premium) 11 - Investigate threats with Content search in Microsoft Purview Explore Microsoft Purview eDiscovery solutions Create a content search View the search results and statistics Export the search results and search report Configure search permissions filtering Search for and delete email messages 12 - Protect against threats with Microsoft Defender for Endpoint Practice security administration Hunt threats within your network 13 - Deploy the Microsoft Defender for Endpoint environment Create your environment Understand operating systems compatibility and features Onboard devices Manage access Create and manage roles for role-based access control Configure device groups Configure environment advanced features 14 - Implement Windows security enhancements with Microsoft Defender for Endpoint Understand attack surface reduction Enable attack surface reduction rules 15 - Perform device investigations in Microsoft Defender for Endpoint Use the device inventory list Investigate the device Use behavioral blocking Detect devices with device discovery 16 - Perform actions on a device using Microsoft Defender for Endpoint Explain device actions Run Microsoft Defender antivirus scan on devices Collect investigation package from devices Initiate live response session 17 - Perform evidence and entities investigations using Microsoft Defender for Endpoint Investigate a file Investigate a user account Investigate an IP address Investigate a domain 18 - Configure and manage automation using Microsoft Defender for Endpoint Configure advanced features Manage automation upload and folder settings Configure automated investigation and remediation capabilities Block at risk devices 19 - Configure for alerts and detections in Microsoft Defender for Endpoint Configure advanced features Configure alert notifications Manage alert suppression Manage indicators 20 - Utilize Vulnerability Management in Microsoft Defender for Endpoint Understand vulnerability management Explore vulnerabilities on your devices Manage remediation 21 - Plan for cloud workload protections using Microsoft Defender for Cloud Explain Microsoft Defender for Cloud Describe Microsoft Defender for Cloud workload protections Enable Microsoft Defender for Cloud 22 - Connect Azure assets to Microsoft Defender for Cloud Explore and manage your resources with asset inventory Configure auto provisioning Manual log analytics agent provisioning 23 - Connect non-Azure resources to Microsoft Defender for Cloud Protect non-Azure resources Connect non-Azure machines Connect your AWS accounts Connect your GCP accounts 24 - Manage your cloud security posture management? Explore Secure Score Explore Recommendations Measure and enforce regulatory compliance Understand Workbooks 25 - Explain cloud workload protections in Microsoft Defender for Cloud Understand Microsoft Defender for servers Understand Microsoft Defender for App Service Understand Microsoft Defender for Storage Understand Microsoft Defender for SQL Understand Microsoft Defender for open-source databases Understand Microsoft Defender for Key Vault Understand Microsoft Defender for Resource Manager Understand Microsoft Defender for DNS Understand Microsoft Defender for Containers Understand Microsoft Defender additional protections 26 - Remediate security alerts using Microsoft Defender for Cloud Understand security alerts Remediate alerts and automate responses Suppress alerts from Defender for Cloud Generate threat intelligence reports Respond to alerts from Azure resources 27 - Construct KQL statements for Microsoft Sentinel Understand the Kusto Query Language statement structure Use the search operator Use the where operator Use the let statement Use the extend operator Use the order by operator Use the project operators 28 - Analyze query results using KQL Use the summarize operator Use the summarize operator to filter results Use the summarize operator to prepare data Use the render operator to create visualizations 29 - Build multi-table statements using KQL Use the union operator Use the join operator 30 - Work with data in Microsoft Sentinel using Kusto Query Language Extract data from unstructured string fields Extract data from structured string data Integrate external data Create parsers with functions 31 - Introduction to Microsoft Sentinel What is Microsoft Sentinel? How Microsoft Sentinel works When to use Microsoft Sentinel 32 - Create and manage Microsoft Sentinel workspaces Plan for the Microsoft Sentinel workspace Create a Microsoft Sentinel workspace Manage workspaces across tenants using Azure Lighthouse Understand Microsoft Sentinel permissions and roles Manage Microsoft Sentinel settings Configure logs 33 - Query logs in Microsoft Sentinel Query logs in the logs page Understand Microsoft Sentinel tables Understand common tables Understand Microsoft Defender XDR tables 34 - Use watchlists in Microsoft Sentinel Plan for watchlists Create a watchlist Manage watchlists 35 - Utilize threat intelligence in Microsoft Sentinel Define threat intelligence Manage your threat indicators View your threat indicators with KQL 36 - Connect data to Microsoft Sentinel using data connectors Ingest log data with data connectors Understand data connector providers View connected hosts 37 - Connect Microsoft services to Microsoft Sentinel Plan for Microsoft services connectors Connect the Microsoft Office 365 connector Connect the Microsoft Entra connector Connect the Microsoft Entra ID Protection connector Connect the Azure Activity connector 38 - Connect Microsoft Defender XDR to Microsoft Sentinel Plan for Microsoft Defender XDR connectors Connect the Microsoft Defender XDR connector Connect Microsoft Defender for Cloud connector Connect Microsoft Defender for IoT Connect Microsoft Defender legacy connectors 39 - Connect Windows hosts to Microsoft Sentinel Plan for Windows hosts security events connector Connect using the Windows Security Events via AMA Connector Connect using the Security Events via Legacy Agent Connector Collect Sysmon event logs 40 - Connect Common Event Format logs to Microsoft Sentinel Plan for Common Event Format connector Connect your external solution using the Common Event Format connector 41 - Connect syslog data sources to Microsoft Sentinel Plan for syslog data collection Collect data from Linux-based sources using syslog Configure the Data Collection Rule for Syslog Data Sources Parse syslog data with KQL 42 - Connect threat indicators to Microsoft Sentinel Plan for threat intelligence connectors Connect the threat intelligence TAXII connector Connect the threat intelligence platforms connector View your threat indicators with KQL 43 - Threat detection with Microsoft Sentinel analytics What is Microsoft Sentinel Analytics? Types of analytics rules Create an analytics rule from templates Create an analytics rule from wizard Manage analytics rules 44 - Automation in Microsoft Sentinel Understand automation options Create automation rules 45 - Threat response with Microsoft Sentinel playbooks What are Microsoft Sentinel playbooks? Trigger a playbook in real-time Run playbooks on demand 46 - Security incident management in Microsoft Sentinel Understand incidents Incident evidence and entities Incident management 47 - Identify threats with Behavioral Analytics Understand behavioral analytics Explore entities Display entity behavior information Use Anomaly detection analytical rule templates 48 - Data normalization in Microsoft Sentinel Understand data normalization Use ASIM Parsers Understand parameterized KQL functions Create an ASIM Parser Configure Azure Monitor Data Collection Rules 49 - Query, visualize, and monitor data in Microsoft Sentinel Monitor and visualize data Query data using Kusto Query Language Use default Microsoft Sentinel Workbooks Create a new Microsoft Sentinel Workbook 50 - Manage content in Microsoft Sentinel Use solutions from the content hub Use repositories for deployment 51 - Explain threat hunting concepts in Microsoft Sentinel Understand cybersecurity threat hunts Develop a hypothesis Explore MITRE ATT&CK 52 - Threat hunting with Microsoft Sentinel Explore creation and management of threat-hunting queries Save key findings with bookmarks Observe threats over time with livestream 53 - Use Search jobs in Microsoft Sentinel Hunt with a Search Job Restore historical data 54 - Hunt for threats using notebooks in Microsoft Sentinel Access Azure Sentinel data with external tools Hunt with notebooks Create a notebook Explore notebook code

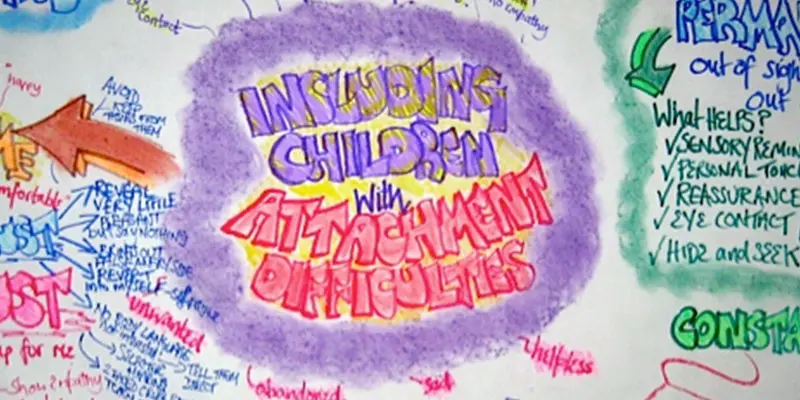
ATTACHMENT DIFFICULTIES: INCLUDING CHILDREN
By Inclusive Solutions
This is a practical ‘non medical’ day for front line practitioners working with children and young people with serious attachment issues arising from loss, trauma and abuse. We look at what Psychology may help us in our understanding of children who have faced issues with love and attachment. Splitting, handling projected feelings, constancy and permanence are explored. Online Course now available via Teachable Platform – Understanding Attachment Learn at your own pace… lots of text and video support Course Category Meeting emotional needs Behaviour and Relationships Inclusion Teaching and Learning Description This is a practical ‘non medical’ day for front line practitioners working with children and young people with serious attachment issues arising from loss, trauma and abuse. Drawing from the international research and literature and our own experience over many years as educational psychologists of the challenges of children with major social and emotional needs, we will explore together what the best practice can and could look like. We explore the language of attachment and outline very practical classroom strategies. We look at what Psychology may help us in our understanding of children who have faced issues with love and attachment. We explore the feelings of being on a desolate island of relational poverty or to imagine swimming with sharks. We explore the themes of violence, anxiety and experience of being a victim as young people grow older. We look at telling lies and explore how we can respectfully understand this. We reveal the new and innovative compass of vulnerability – the cognitive errors to which some are much more vulnerable. We look at triggers, self regulation and unpack a range of strategies. Transference and counter transference are examined along with splitting, handling projected feelings, constancy and permanence. We explore what young people with these difficulties really need from us. We also spend time looking at the emotional impact on practitioners working with children with such needs and what helps at an personal and team level. We can all do something – we do not have to wait for expert therapists to arrive! Testimonials Very moving presentation I will always try and think behind the behaviour now It had a huge impact on all levels We all seem to need it Belonging and feelings are so important Very user friendly Excellent! Learning Objectives Increased confidence regarding developing inclusive practice for children with serious attachment needs in mainstream schools Simple understandable explanation of attachment understood Access to a wider range of practical strategies to impact on social and behavioural needs Deeper understanding of core values surrounding inclusion of emotionally disabled children Opportunity to reflect on professional attitudes and behaviour towards parents and pupils with complex emotional needs New skills, scripts and processes to make inclusion successful Who Is It For ? Practitioners working in schools and other settings with children and young people of all ages Key workers Teaching Assistants with support roles Heads and deputies SENCOs Advanced skills teachers Primary and secondary classroom teachers Parents Local authority support services Course Content The course explores the questions : How can we start to develop an understanding of children with attachment needs? What is the true impact of loss, trauma and abuse? What else can we do to go about including high profile children or young people with challenging emotional needs? What useful psychological constructs can we use to guide us? This course also explores practical strategies and language for key adults rebuilding relationships with individual pupils. This is a participative day that aims to be explorative and practical. Opportunities to develop empathy with the children of concern will be created.
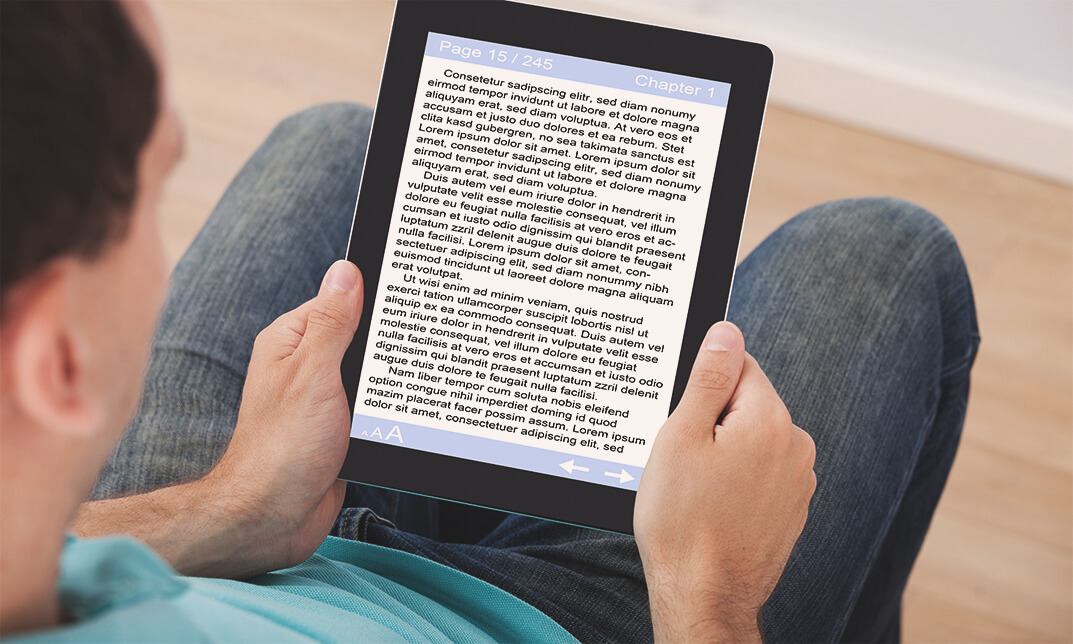
E-Book Product Creation Course
By iStudy UK
Do you want to do business with online information items? DO you want to offer services like Udemy or Coursera? This course will guide you the techniques and procedures of making a successful information product. Course Description: Creating your online product does not take a month or year. This course will help you to make your online product quickly. If you want to make your first online product but do not know from where to start, this course will guide you. You can create many information products within 24 hours. The course will show you the paths of making information product quickly with an innovative idea. By the end of the course, you will learn the simple approaches to make eBooks, instructing programs, enrollment programs, video courses, online courses, articles, reports and much more. Course Highlights E-Book Product Creation Course is an award winning and the best selling course that has been given the CPD Certification & IAO accreditation. It is the most suitable course anyone looking to work in this or relevant sector. It is considered one of the perfect courses in the UK that can help students/learners to get familiar with the topic and gain necessary skills to perform well in this field. We have packed E-Book Product Creation Course into 8 modules for teaching you everything you need to become successful in this profession. To provide you ease of access, this course is designed for both part-time and full-time students. You can become accredited in just 6 hours, 45 minutes hours and it is also possible to study at your own pace. We have experienced tutors who will help you throughout the comprehensive syllabus of this course and answer all your queries through email. For further clarification, you will be able to recognize your qualification by checking the validity from our dedicated website. Why You Should Choose E-Book Product Creation Course Lifetime access to the course No hidden fees or exam charges CPD Accredited certification on successful completion Full Tutor support on weekdays (Monday - Friday) Efficient exam system, assessment and instant results Download Printable PDF certificate immediately after completion Obtain the original print copy of your certificate, dispatch the next working day for as little as £9. Improve your chance of gaining professional skills and better earning potential. Who is this Course for? Business people, entrepreneurs who want to do business with the online information product. New online marketers. Individuals who want to do online business. E-Book Product Creation Course is CPD certified and IAO accredited. This makes it perfect for anyone trying to learn potential professional skills. As there is no experience and qualification required for this course, it is available for all students from any academic backgrounds. Requirements Our E-Book Product Creation Course is fully compatible with any kind of device. Whether you are using Windows computer, Mac, smartphones or tablets, you will get the same experience while learning. Besides that, you will be able to access the course with any kind of internet connection from anywhere at any time without any kind of limitation. Career Path You will be ready to enter the relevant job market after completing this course. You will be able to gain necessary knowledge and skills required to succeed in this sector. All our Diplomas' are CPD and IAO accredited so you will be able to stand out in the crowd by adding our qualifications to your CV and Resume. How To Start To Write An Ebook 01:00:00 Creative Ways To Attract Buyers For Your Product 01:00:00 How To Effectively Draft The Table Of Content Of Your Book 01:00:00 Writing Content Yourself versus Outsourcing 01:00:00 Best Ways To Outsource 01:00:00 Who Should You Hire To Create Your Product 00:30:00 Benefits Of A Long Term Working Relationship With The People You Outsource To 01:00:00 Wrapping Up 00:15:00 Mock Exam Final Exam
Description Explore the ways of combining various business opportunities to a cohesive successful multiple-business with the International Accredited Business Online Course course. The course teaches you the skills and strategies to put an online multi-business together. You will learn how to amalgamate diverse business opportunities to a successful and achievable 'Multi-business'. The methods of engaging your customers and the procedures of managing combined income streams will be explained in the course. Moreover, the course shows you the process of application and other formalities that you need to follow for running a multi-business without dropping balls and being overwhelmed by stress. Apart from these, the course will help you to find a profitable niche and guides you to set up your goals. The ways of producing multiple products and selling them into multiple platforms, monitoring l changes and progress, and the ways of tying up all the new income streams together into one manageable multi-business will be illustrated in the course. Finally, the system of building and promoting your multi-business using free and low costs tools will be explained. By the end of the course, you will gain a general understanding of the various structures of multiple income streams. Assessment: This course does not involve any MCQ test. Students need to answer assignment questions to complete the course, the answers will be in the form of written work in pdf or word. Students can write the answers in their own time. Once the answers are submitted, the instructor will check and assess the work. Certification: After completing and passing the course successfully, you will be able to obtain an Accredited Certificate of Achievement. Certificates can be obtained either in hard copy at a cost of £39 or in PDF format at a cost of £24. Who is this Course for? International Accredited Business Online Course is certified by CPD Qualifications Standards and CiQ. This makes it perfect for anyone trying to learn potential professional skills. As there is no experience and qualification required for this course, it is available for all students from any academic background. Requirements Our International Accredited Business Online Course is fully compatible with any kind of device. Whether you are using Windows computer, Mac, smartphones or tablets, you will get the same experience while learning. Besides that, you will be able to access the course with any kind of internet connection from anywhere at any time without any kind of limitation. Career Path After completing this course you will be able to build up accurate knowledge and skills with proper confidence to enrich yourself and brighten up your career in the relevant job market. Introduction Introduction to The Online Multi-Business Master Plan Course 00:03:00 Aims of this course 00:06:00 Course Structure 00:02:00 Online Business Models Online Business Models Overview 00:01:00 Business Models- Udemy 00:04:00 Business Models- Fiverr 00:04:00 Business Models- Amazon KDP 00:04:00 Business Models- Createspace 00:04:00 Business Models- Other Platforms 00:05:00 Your Multi-Business Website Your Multi-Business Website 00:04:00 Getting Started Create, Re-purpose, Repeat 00:04:00 Pick a Niche 00:12:00 Google Keyword Planner Overview 00:02:00 Pick a Platform 00:09:00 Plan, Plan & Test 00:03:00 Earn Your First Dollar 00:06:00 What if you fail- 00:02:00 Build your Systems 00:07:00 Automate and Outsource 00:03:00 Re-purpose and Repeat 00:08:00 Putting it all together 00:04:00 Promoting Your Multi-Business Promoting Your Multi-Business 00:06:00 The Complete Online Multi-Business Master Plan The Complete Online Multi-Business Master Plan 00:11:00 Essential Tools Paypal Overview 00:01:00 Fiverr Overview 00:03:00 MailChimp Overview 00:03:00 Conclusion Finally 00:02:00 Order Your Certificate and Transcript Order Your Certificates and Transcripts 00:00:00

AUTISM – UNDERSTANDING AND INCLUDING PEOPLE OF ALL AGES
By Inclusive Solutions
In this practical workshop session we will explore ways of including people who have been labelled as being on the autism spectrum. The session will be values based and practical and will aim to allow the sharing of experiences and good practice as well promoting innovative approaches to inclusion through the design of best practice. Online Course now available via Teachable Platform – Understanding Movement Differences Learn at your own pace… lots of text and video support Course Category Autism and Communication Inclusion Parents and Carers Behaviour and Relationships Description In this practical workshop session we will explore ways of including people who have been labelled as being on the autism spectrum. The session will be values based and practical and will aim to allow the sharing of experiences and good practice as well promoting innovative approaches to inclusion through the design of best practice. Family perspectives and experiences will also be explored. This is not a ‘medical model’ day on autism. Our motto for the day is ‘People do things for a Reason (and the reason isn’t autism).’ We make full use of first hand accounts of the experience of autism – the autobiographies – to deepen participants’ understanding of what it means to be labelled ‘autistic’ “We are all much more simply human than otherwise, be we happy and successful, contented and detached, miserable and disordered, or whatever.”HARRY STACK SULLIVAN Testimonials ‘Very respectful of people on the spectrum.’ ‘Really gave me an idea of how people feel.’ ‘Ways of reaching a person not a condition.’CLAIRE Learning Objectives Increased confidence regarding including autistic people Access to a wider range of practical strategies to impact on communication and behaviour issues Deeper understanding of core values surrounding inclusion New skills and processes to strengthen the inclusion of autistic people Who Is It For? Social Care workers Personal Assistants Early years and school based practitioners Heads and deputies Guidance staff Learning support teams SENCOs Primary and secondary teachers Parents Brothers and sisters Local authority support services Community workers and carers Course Content The course answers the questions : What is autism? How do we go about including autistic people? What does autism have to do with me? Key themes include: Movement differences Strategies for Facilitating Communication Supports and Accommodations for Sensory Sensitivities Developing Friendships and Peer Support School and Family Partnerships Learning to Listen Positive Behavioural Supports

Special Executive Master's Programme in Operations Management
4.9(261)By Metropolitan School of Business & Management UK
Special Executive Masters Programme (S.E.M.P) This programme is geared at enhancing professionals' careers. The SEMP is an encapsulated Senior Management Programmes are short certificate modules designed for anyone who would benefit from more in-depth business knowledge delivered in a short and intensive programme What makes us different? We are a world class business school located in the heart of London, Dubai, Islamabad and Lagos. We are one of the fastest growing British business schools with a stylish blended learning model that is both online and on campus. Learn more about the programme Special Executive Master's Programme in Operations Management Course Overview The MSBM Special Executive Masters Programmes (SEMP) allows you to update your skills, develop new skills, and explore and develop interests in a wide range of topics. These courses can be taken as personal or professional development and may enhance your employability. The encapsulated Senior Executive Programme in Operations Management is for high-performance managers and directors who work in critical roles using available resources to effectively produce products and services in a way that satisfies the customers. The Programme is also useful for managers and directors who need an intensive course to cover the key areas that drive success and profit in everyday business operations. Course Details Mode of Study Using Web-based technology, this program provides self-paced, individualized instruction that can be taken anywhere and anytime an individual has access to a computer and the Internet. This Programme is suitable for successful professionals or specialists in the private, public, or voluntary sectors who have new management responsibilities and need to quickly expand their management knowledge. This Programme serves as a refresher course for those who have had their Masters a long time ago and need quick reminders and professional/ academic updates while it serves as a primer for those very experienced Professionals who never made time out for their masters yet they require the academic and practical relevance of this master’s experience. It is a short executive training that runs online for 3 months. Candidates will run 2 months of active lectures and series of assignments and 1 month for their dissertation. Upon successful completion of the Programme, candidates will be awarded a Continuing Professional Development (CPD) certificate in the specific Programme they have completed. What is a CPD Course? Continuing Professional Development (CPD) is the means by which professionals maintain and enhance their knowledge and skills. The world is constantly moving at a very fast pace so undertaking CPD is essential to support a professional in his/her current role as well as helping them with career progression. CPD is all about upgrading knowledge, skills, and capabilities to remain effective and compliant. A CPD course is an investment that you make in yourself. It’s a way of planning your development that links learning directly to practice. CPD can help you keep your skills and knowledge up to date and prepare you for greater responsibilities. It can boost your confidence, strengthen your professional credibility, and help you become more creative in tackling new challenges. Is the SEMP Operations Management Programme right for me? If you want to reduce the amount of investment that is necessary to produce the required type and quality of products and services; increase the effective capacity of your operation; provide the basic capacity for future innovation; build a solid base of operations skills and knowledge within the business, and have the drive to uphold vision which would take your current role to the next level in order to distinguish yourself as a truly high- performance manager, then this is just the right Programme for you. Why SEMP Operations Management? In recent years there has been a lot of talk about competitive advantage, something that every business seeks. Many debates more specifically focus on how operations management can deliver a competitive advantage in a different environment. When enrolled for this Programme, you will gain a complete and thorough grounding in the four major concepts of competitive advantage in operations management which are: Cost Leadership Short delivery times Flexibility Reliability By the end of three months, you will have worked through several case studies, have access to numerous online academic materials, and also have received directions from the best business trainers in the business world today. Who Should Enroll in This Online Certificate Program? The SEMP Operations Management Programme is designed for entry-level managers, up to mid-level managers, senior managers, or directors who are in a general management role or fast approaching such position and are seeking an opportunity to obtain a richer, deeper understanding of management skills. The reasons were given by previous students for taking the online Programme include: Personal career development Promotion to generalist’ roles from functional specialization Guiding my company to profitability Contributing to the growth of my organization Personal recommendations by online alumni students A ‘taster’ before embarking upon an academic Masters Programme Broadening of business expertise for those from public and non-profit making organizations. A good Programme for people without previous University, Polytechnic or College degrees. Accreditation The content of this course has been independently certified as conforming to universally accepted Continuous Professional Development (CPD) guidelines. Entry Requirements There are no strict entry requirements for this course. Work experience will be added advantage to understanding the content of the course. Workshops This is a self-study programme with unlimited tutor support. You will never be more than a message or phone call away from our tutors. Visa Requirements There are no Visa Requirements for this Programme as it's as Online Course.
