- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
Lean Six Sigma Yellow Belt Certification Program: On-Demand
By IIL Europe Ltd
Lean Six Sigma Yellow Belt Certification Program: On-Demand This course is designed to instill an in-depth understanding of Lean Six Sigma and a clear sense of what is required to define high-impact improvement projects, establish Lean Six Sigma measurements, and complete Lean Six Sigma projects using the systematic and proven Define, Measure, Analyze, Improve, and Control (DMAIC) methodology. This course is designed to instill an in-depth understanding of Lean Six Sigma and a clear sense of what is required to define high-impact improvement projects, establish Lean Six Sigma measurements, and complete Lean Six Sigma projects using the systematic and proven Define, Measure, Analyze, Improve, and Control (DMAIC) methodology. Participants will learn basic tools and techniques of Lean Six Sigma and those who pass a thirty-question exam (70% or above) will become a Certified Lean Six Sigma Yellow Belt. This course is delivered through four 3-hour online sessions. What you Will Learn You'll learn how to: Establish the structure that supports and sustains Lean Six Sigma Quality Identify and calculate key Lean Six Sigma Measurements (Sigma, DPMO, and Yield) Select successful, high-impact projects that match strategic objectives Document, measure, and improve key processes using the DMAIC (Define, Measure, Analyze, Improve, and Control) Methodology Utilize data-based thinking to make key business decisions Introduction to the Fundamentals and Vision of Lean Six Sigma Lean Six Sigma's focus on the customer, on quality, and on results The costs of poor quality Critical factors to consider when deploying Lean Six Sigma Lean Six Sigma as a process improvement methodology Lean Six Sigma metrics Why do it - ROI and payback for Lean Six Sigma Business Process Management Critical Lean Six Sigma roles and responsibilities Main aspects of managing the organizational change Project selection Metrics of Lean Six Sigma and the DMAIC Model How to strategically align business metrics and projects within an organization How to identify and measure quality characteristics which are critical to customers What does the customer (internal or external) really want from our products and services? Establishing appropriate teams and setting those teams up to be successful What defines a good measurement system? How are we doing (learning the secret to measuring the right things, right)? How to improve output measures by understanding and measuring the process Where are there defects (how to properly select and scope high-impact projects)? Where is the process broken (the Lean Six Sigma version of root cause analysis)? How to determine the process efficiency, or value add, of a process The appropriate use of quality tools Understanding the concept of variation and how to reduce knee-jerk reactions How to achieve breakthrough results for any key measure How can we ensure the identified improvements will be sustainable (the basics of process control)?

RFID training course description This training course focuses on the technologies used in Radio Frequency Identification (RFID). What will you learn Describe the RFID architecture. Design RFID systems. Evaluate tag types. Recognise common RFID problems. RFID training course details Who will benefit: RFID technologists and system engineers. Prerequisites: RF fundamentals. Duration 2 days RFID training course contents What is RFID? Review of RF basics, what is RFID, RFID history, RFID base system architecture, frequency bands used by RFID, comparison with barcodes. RFID applications Supply chain, asset tracking, theft reduction, retail, access control, tolls. Tags Tag features, types of tag, passive and active, chips, read only, read write, affixing tags, selecting location to affix a tag, tag orientation and location, tag stacking, impact of rate of movement, tag data formats. Interrogators/readers Interrogation zones, interrogator types, antennas, read distance tests, multiple interrogators, synchronisation, dense interrogator environment issues. RFID peripherals. Standards and regulations Global regulatory requirements, regional regulatory requirements, ISO, ETSI, FCC, EPC, safety regulations/issues. Testing and troubleshooting Read rate problems, improperly tagged items, tag failure. RFID system design Antenna types, interference, antenna location and spacing, how many antennas? How many interrogators? tag types, grounding considerations, cabling, site diagrams.

This half-day workshop delivered face-to-face or online is designed for anyone in your organisation that wants to become a Neurodiversity Champion - someone who wants to educate and change the way that Neurodiversity is viewed in the workplace.

Essential 5G training course description This course is designed to give delegates an explanation of the technologies and interworking requirements of the next generation of cellular communications. It is not a definitive set of descriptions but a possibility of the final deployment. we will investigate the 10 pillars for 5G which will include various Radio Access Technologies that are required to interwork smoothly. We will look at the 4G Pro features and other RATs. What will you learn List the ten pillars of 5G deployment. Describe the 5G Internet. Explain virtualization and RAT virtulization. Describe Software Defined Networks (SDN). Explain carrier aggregation. Describe the mobile cloud. Explain an overall picture of 5G architecture. Essential 5G training course details Who will benefit: Anyone looking for an understanding of the technologies and interworking requirements of the next generation of cellular communications. Prerequisites: None. Duration 3 days Essential 5G training course contents Drivers for 5G 5G Road Map, 10 Pillars of 5G, evolving RATs, oSON, MTCm, mm-wave, backhaul, EE, new spectrum, spectrum sharing, RAN virtualisation. 4G LTE Advanced MIMO technology in release 8, Downlink & uplink MIMO R8, MIMO technology in LTE advanced, Downlink 8-layer SU-MIMO, Downlink MU-MIMO, Uplink MU-MIMO, Uplink transmit diversity, Coordinated multi-point operation (CoMP), Independent eNB & remote base station configurations, Downlink CoMP. ICIC & eICIC ICIC, Homogeneous to heterogeneous network evolution, Introduction to eICIC, Macro-pico scenario, Macro-femto scenario, Time orthogonal frequencies. Almost Blank Subframe (ABS). Carrier aggregation Component carriers (CC), CC aggregation deployments, Intra-band contiguous solutions, Intra-band non-contiguous solutions, Inter-band non-contiguous solutions, CA bandwidth classes, Aggregated transmission bandwidth configurations (ATBC), Possible carrier aggregation configs. eIMTA TDD UL-DL reconfig. for traffic adaptation, Reconfig. mechanisms, Interference mitigation schemes, Dynamic & flexible resource allocation. 5G architectures 5G in Europe, horizon 2020 framework, 5G infrastructure PPP, METIS project, 5G in North America, academy research, company R&D, 5G specifications. The 5G internet High-level view of Cloud Services, The Internet of Things & context awareness, Network reconfiguration & virtualization support, server proliferation, how VMs fix underutilised server problem, enter the hypervisor, why are VM such a big deal? SDN, evolution of the data centre network, high availability, low latency, scalability, security, cost model explodes, service-oriented API. OpenFlow switches, OpenFlow controllers, how SDN works. The big picture, pulling it all together, why the network had to change, how SDN & NFV tie together. Evolutionary approach to the internet, architectures for distributed mobility management, MEDIEVAL & MEDIVO projects, a clean slate approach, mobility first architecture. VNet, INM, NetInf, ForMux, MEEM. Generic Path (GP) & anchorless mobility (AM), Quality of Service support, network resource provisioning, resourcing inside a network. IntServ, RSVP, DiffServ, CoS. Emerging approach for resource over- provisioning, example use case architecture for scalable resource control scenarios in the 5G internet. Integrating SDN/NFV for efficient resource over-reservation control, control information repository, service admission control policies, network resource provisioning, control enforcement functions, network configurations & operations. Small cells for 5G Average spectral efficiency evolution, WiFi & Femto cells, Capacity limits. Achievable gains with densifications, multi-antenna techniques, small cells. Mobile data demand, approach & methodology, subscriber density and traffic demand projections to 2020. Demand versus capacity, global mobile data traffic increase modelling, country level backhaul traffic projections, Small cell challenges, backhaul, spectrum, automation. Cooperation for next gen wireless networks Diversity & relaying strategies, cooperation & network coding, ARQ & MAC protocols, NCCARQ & PRCSMA packet exchange, Physical layer impact on MAC protocol analysis, NCCARQ overview, PHY layer impact, Case study on NCCARQ. Mobile clouds Mobile cloud, Mobile cloud enablers, mobile user domain, wireless technologies, WWAN WLAN and WPAN range, Bluetooth, IEEE.802.15.4 & software stacks, infrared, near field communications (NFC). Network coding, store & forward vs compute & forward, linear network coding, random linear coding. Security for 5G communications Potential 5G communication systems architectures, Security issues & challenges. Mobile malware attacks targeting the UE, 5G mobile botnets, access networks, attacks on 4G networks, C-RNTI & packet sequence number based UE location tracking, false buffer status reports attacks, message insertion attacks, HeNB attacks, physical attacks, credential attacks, configuration and protocol attacks, attacks on MON, user data & identity attacks, mobile operator's core network, DDoS attacks targeting MON, signalling amplification, HSS saturation, external IP networks.

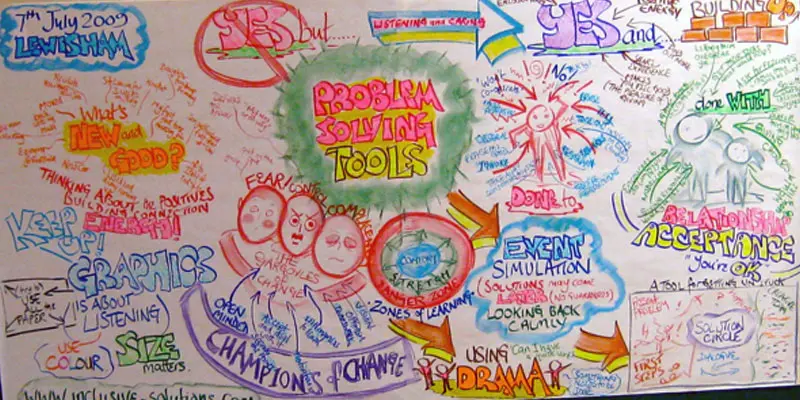
PROBLEM SOLVING TOOLS AND TECHNIQUES
By Inclusive Solutions
In this practical workshop session we will explore ways of problem solving around complex situations. The session will be practical and will aim to allow the sharing of experiences and good practice as well promoting innovative approaches to problem solving around systemic, organisational as well as individual inclusion issues. Course Category Behaviour and Relationships Visioning and Problem Solving Description ‘The question is not should they be here anymore. Now it’s how can we figure out how best to include them?’ In this practical workshop session we will explore ways of problem solving around complex situations. The session will be practical and will aim to allow the sharing of experiences and good practice as well promoting innovative approaches to problem solving around systemic, organisational as well as individual inclusion issues. Behaviour problems, relationship challenges and personnel dilemmas can all be worked on with these team oriented problem solving processes. We will introduce participants to a range of powerful effective approaches for them to choose from back in their own workplaces. Testimonials A great day – going away buzzing with ideas Excellent! Inspirational! Informative! Learning Objectives Increased confidence regarding problem solving around inclusion in mainstream settings Access to a wider range of practical strategies and techniques to impact on communication, realtionship, learning and behaviour issues Learn new problem solving processes Who Is It For ? Early Years and School based Practitioners Heads and Deputies Guidance staff Learning Support teams SENCOs Primary and secondary teachers Parents Local Authority Support Services Community workers and carers Course Content The course answers the questions : How can we work out how to include this child best? Is there a more structured way to run this meeting? Can we explore the emotional impact the person is having on us and still agree strategies? How can I get unstuck from this problem? The day will cover: Solution Circles Solution Focused approaches Synectics – using analogies and out of the box creativity Circles of Adults Using Imagination to solve problems If you liked this course you may well like: CIRCLES OF ADULTS
Cyber Incident Response for Business Professionals
By Mpi Learning - Professional Learning And Development Provider
This course covers incident response methods and procedures are taught in alignment with industry frameworks such as US-CERT's NCISP (National Cyber Incident Response Plan), and Presidential Policy Directive (PPD) 41 on Cyber Incident Coordination Policy.

ICA Specialist Certificate in Corporate Governance
By International Compliance Association
ICA Specialist Certificate in Corporate Governance - Course Overview Corporate governance is a key driver in delivering the right outcomes for organisations and helping them to meet corporate objectives. Regulators view effective corporate governance mechanisms as good indicators of a firm's culture of compliance because good governance is likely to indicate good internal culture. This online course will help you: get to grips with the purpose, key success factors and risks associated with governance understand the impact of good governance on the success of organisational strategies assess and design frameworks that serve your firm's objectives and improve performance evaluate the impact of the digital revolution on governance and future developments ICA Specialist Certificates, awarded in association with Alliance Manchester Business School, the University of Manchester, will help you quickly gain actionable knowledge to boost your confidence and credibility. Upon successful completion of this course, students will be awarded the ICA Certificate in Corporate Governance and will be entitled to use the designation -Spec.Cert(CorpGov) The function and purpose of the organisation The governance of regulated enterprise and the purpose of the Board of Directors The importance, impact and opportunity of organisational culture Conflict management in the organisation Organisational structure, hierarchy and policy frameworks Communication strategy Internal control and influence power Broad-base governance - beyond the balance sheet The digital revolution and its influence on governance Governance - a never ending story

Data Protection (GDPR) Practitioner Certificate - live, online
By Computer Law Training
GDPR Practitioner

NCSP ISO 27001 Specialist
By IIL Europe Ltd
The NCSP® ISO 27001 Specialist accredited (APMG International), certified (NCSC/GCHQ-UK), and recognized (DHS-CISA-USA) certification course teaches Digital Business, Operational Stakeholders, Auditors, and Risk Practitioners a Fast-Track approach to adopting and adapting the ISO 27001 controls in the context of a NIST Cybersecurity Framework program.This course looks at the impact of adapting a principled approach to an enterprise risk management framework to better support cybersecurity decisions within the context of the selected informative reference. It guides participants on the best approach to adapt, implement, and operate (AIO) a comprehensive cybersecurity program that integrates into existing organizational capabilities and incorporates the selected Informative Reference. NCSP® ISO 27001 Specialist introduces the integration of typical enterprise capabilities with cybersecurity from the perspective of the selected cybersecurity informative reference. The overall approach places these activities into systems thinking context by introducing the Service Value Management System composed of three aspects, governance, assurance, and the Z-X Model. With this in place, the course presents the approach to adapt, implement, operate, and improve the organizational cybersecurity posture that builds on the application of the FastTrack™ presented in the NCSP Practitioner. The NIST Cybersecurity Professional (NCSP®) program is the industry's first accredited certification training program that teaches organizations how to build a Digital Value Management Overlay System capable of leveraging the NIST Cybersecurity Framework to deliver the secure, digital business outcomes expected by executives, government regulators, and legal advisors.

