- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
SENCO - Special Education Needs Coordination
By Training Tale
This SENCO - Special Educational Needs Coordination is designed for those interested in or who are currently in a SENCO role in the early years setting. This Special Educational Needs Coordination qualification provides learners with a thorough understanding of the roles and responsibilities of the Special Educational Needs Coordinator in early years setting. Learn about the strategies and techniques for assisting children and their families and gain in-depth knowledge of SEN codes of practice. The purpose of this course is to help learners progress to further and higher education and develop new practical skills in health and social care. Learning Outcomes After completing this Special Educational Needs Coordination, the learner will be able to: Understand the roles and responsibilities of the Special Educational Needs Coordinator in the early years setting. Understand the strategies and techniques for supporting children and their families. Increase knowledge of SEN codes of practice. Why Choose Special Educational Needs Coordination Course from Us Self-paced course, access available from anywhere. Easy to understand, high-quality study materials. Course developed by industry experts. MCQ quiz after each module to assess your learning. Automated and instant assessment results. 24/7 support via live chat, phone call or email. Free PDF certificate as soon as completing the course. ***Courses are included in this SENCO - Special Educational Needs Coordination Bundle Course*** Course 01: SENCO - Special Educational Needs Coordination Course 02: Speech & Language Therapy Course 03: Autism Diploma Course Course 04: Nursery Nurse Course Course 05: Level 2 Diploma for the Early Years Practitioner Course 06: Level 2 Award in Support Work in Schools and Colleges Course 07: Level 2 Certificate in Understanding Children and Young People's Mental Health Course ***Other Benefits of this Bundle Course*** Free 7 PDF Certificate Access to Content - Lifetime Exam Fee - Totally Free Free Retake Exam [ Note: Free PDF certificate as soon as completing the course ] Detailed course curriculum Module 1: Roles and Responsibilities of the Special Educational Needs Coordinator in the Early Years Understand the principles, statutory guidance and legislation underpinning practice for children with Special Educational Needs and Disability (SEND) in an early years setting Understand the role of the Early Years Special Educational Needs Coordinator (SENCo) Understand partnership working for the Early Years SENCo Understand early identification and action for children with SEND Module 2: Strategies and Techniques for Supporting Children and Families Understand the graduated approach in an early years setting Understand English as an additional language (EAL) Understand Education, Health and Care (EHC) plans ------------------------- ***Speech & Language Therapy Course Curriculum Module 01: Speech & Language Therapy Module 02: Study of Communication Module 03: Components of Normal Speech-Language & Voice Module 04: Eating, Drinking and Swallowing Disorders ------------------------- ***Autism Diploma Course Course Curriculum Module 01: Introduction to Autism Spectrum Disorder (ASD) Module 02: Approaches to Helping People and Children with Autism Module 03: Diagnosis of Autism Module 04: Communication Module 05: Cognitive Styles and Functions in Autism Module 06: Autistic Behaviour Module 07: Organisation Systems with Autistic Individuals Module 08: Autism Awareness Module 09: Government Policies on Autism in England ------------------------- ***Nursery Nurse Course Course Curriculum Module 01: An Overview of Nursery Nurse Module 02: Recognizing Children's Growth and Development Module 03: Observation and Assessment of Children in Early Childhood Settings Module 04: How to Promote Equality, Diversity and Inclusive Practice in Early Years of Learning Module 05: Safeguarding and Protecting Young Children Module 06: Ensuring Health and Safety of Children in the Early Years Module 07: The Essence of Nutrition and Healthy Food for Children Module 08: Importance of Play and Learning in Children's Education Module 09: Ways of Working with Children Having Special Needs Module 10: Working in Partnership with Parents and Carers ------------------------- ***Level 2 Diploma for the Early Years Practitioner Course Curriculum Module 01: Roles and Responsibilities of the Early Years Practitioner Module 02: Health and Safety of Babies and Young Children in the Early Years Module 03: Equality, Diversity and Inclusive Practice in Early Years Settings Module 04: Safeguarding, Protection and Welfare of Babies and Young Children in Early Years Settings Module 05: Understand How to Support Children's Development Module 06: Support Care Routines for Babies and Young Children Module 07: Support the Planning and Delivery of Activities, Purposeful Play Opportunities and Educational Programmes Module 08: Promote Play in an Early Years Setting Module 09: Support Well-being of Babies and Young Children for Healthy Lifestyles Module 10: Support Babies and Young Children to be Physically Active Module 11: Support the Needs of Babies and Young Children with Special Educational Needs and Disability Module 12: Promote Positive Behaviour in Early Years Settings Module 13: Partnership Working in the Early Years Module 14: Support Children's Transition to School ------------------------- ***Level 2 Award in Support Work in Schools and Colleges Course Curriculum Module 01: Understand Schools and Colleges as Organisations Module 02: Understand Children and Young People's Development Module 03: Understand Communication and Professional Relationships with Children, Young People and Adults Module 04: Understand Children and Young People's Health and Safety Module 05: Safeguarding Children and Young People Module 06: Understand Equality, Diversity and Inclusion in Work with Children and Young People ------------------------- ***Level 2 Certificate in Understanding Children and Young People's Mental Health Course Course Curriculum Module 1: Understand Children and Young People's Mental Health in Context Module 2: Understand Factors Which May Affect Children and Young People's Mental Health Module 3: Understand Children and Young People's Mental Health Concerns Module 4: Understand the Impact of Children and Young people's Mental Health Concerns Module 5: Understand How to Support Children and Young People with Mental Health Concerns ------------------------- Assessment Method After completing each module of the Special Educational Needs Coordination, you will find automated MCQ quizzes. To unlock the next module, you need to complete the quiz task and get at least 60% marks. Once you complete all the modules in this manner, you will be qualified to request your certification. Certification After completing the MCQ/Assignment assessment for this SENCO, you will be entitled to a Certificate of Completion from Training Tale. It will act as proof of your extensive professional development. The certificate is in PDF format, which is completely free to download. A printed version is also available upon request. It will also be sent to you through a courier for £13.99. Who is this course for? This SENCO - Special Educational Needs Coordination is ideal for those already working in a SENCO role as part of their Early Years Practitioner role or interested in doing so. This course is also suitable for childminders. Requirements There are no specific requirements for this SENCO - Special Educational Needs Coordination because it does not require any advanced knowledge or skills. Students who intend to enrol in this Special Educational Needs Coordination must meet the following requirements: Good command of the English language Must be vivacious and self-driven Basic computer knowledge A minimum of 16 years of age is required Career path This SENCO - Special Educational Needs Coordination is appropriate for those who want to work in the following fields: Health and social care Childhood studies Community, youth and families Social work Early years Primary teaching Nursing Certificates Certificate of completion Digital certificate - Included

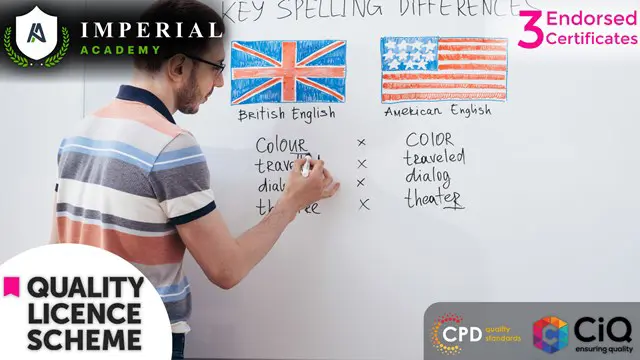
Functional Skills English, TEFL / TESOL with English Grammar
By Imperial Academy
3 QLS Endorsed Diploma | QLS Hard Copy Certificate Included | Plus 10 CPD Courses | Lifetime Access
Italian book club (October 2025)
By Tutor Ci
conversazione in italiano, gruppo di lettura in italiano. Italian book club

Functional Skills English Level 1 Online Course with Exam
By Lead Academy
Course Highlights: This qualification is equivalent to GCSE grade C or 4 Take the Exam from Home – Guaranteed Fast Track Results Exam Booking within 2 Working Days of Enrolment Remote Exam Online or Paper based both option available Course Duration: 55 hours Unlimited Access to Course Materials Get Free Mock Tests & Free Past Papers Extra 25% Time for people with Learning Difficulties NCFE, Pearson Edexcel, Open Awards and TQUK are all OFQUAL-regulated and nationally recognised The English Level 1 Course Overview Our expert-designed Functional Skills English Level 1 Course has smart learning options that provide the necessary knowledge and skills to excel in Functional Skills English. Whether you want to improve your literacy skills, our course is tailored to meet your specific needs and help you achieve your academic and career goals from the comfort of your home. You also get the opportunity to book Live 1:1 tutor support via Microsoft Teams. With interactive lessons, FREE mock tests, personalised feedback and remote exams, our English Level 1 Course ensures a comprehensive and engaging learning experience. Christmas Holiday Information For our remote invigilation service of Functional Skills qualifications, the last accepted booking will be on 19th December 2024. We will reopen for bookings from 3rd January 2025. Results Release For Open Awards: Any results from assessments taken after 30th November 2024 will be published after 2nd January 2025. For NCFE Exams: Results from assessments taken after 11th December 2024 will also be published after 2nd January 2025. Additionally, the period between 20th December 2024 and 2nd January 2025 will not be counted as “working days” for the result release timeframes. Please plan your assessment bookings accordingly. Our last results release prior to Christmas will be on 20th December 2024, with the next results release taking place on 3rd January 2025. Functional Skills Level 1 Course Details Exam Details Exam slots are available 24*7 from Monday to Sunday. If you are in a rush and would like to book your exam sooner, then you can book your remote online exam within 3 working days for Open Awards, 1 working day of enrolment for NCFE, 2 working days of enrolment for TQUK and within 7 working days for Pearson Edexcel. Please note the exam price advertised on the website for the Open Awards remote invigilation exam is applicable for weekdays (Monday to Friday between 9 am to 5 pm). If you would like to book the Open Awards remote invigilation exam at the weekend then there is an additional £25+Vat applicable. EXAM Booking & Results Details You can decide the exam date and place according to your convenience. Awarding Body Paper-Based Exam in Centre On-Screen Exam in Centre Remote Online Exam – From Home Results Edexcel Book within 15 days Book within 24 Hours Book within 7 working days Get results in 20 working days NCFE Book within 10 working days Book within 24 Hours Book within 2 working days Get results in only 7 days Open Awards N/A N/A Book within 2 working days Get results in only 16 working days TQUK Book within 7 working days Book within 24 Hours Book within 2 working days Get results in only 6 working days *Offline examinations will be held at our Swindon and London centres. Please get in touch with us for more information. The new assessment and result dates by NCFE is: (Only applicable if you are attending the exam in between the following assessment date). Delivery mode: On-screen and RI Assessment date to and from: 16/09/2024 – 25/10/2024 Results release: 01/11/2024 The new assessment and result dates by Open Awards is: (Only applicable if you are attending the exam in between the following assessment date). Delivery mode: Remote Assessment date to and from: 02/09/2024 – 13/09/2024 Results release: 11/10/2024 Assessment date to and from: 04/11/2024 – 15/11/2024 Results release: 13/12/2024 (Note that this only applies to the mentioned exam type and if you book the exam during the dates mentioned above. Also, this will not affect the schedule of the other exam types and results.) Difference between NCFE, Pearson Edexcel, Open Awards and TQUK NCFE, TQUK, Pearson Edexcel and Open Awards are OFQUAL-regulated and nationally recognised; however, the only difference lies in the exam booking and result turn-around time. You can book your remote online exam within 2 working days of enrolment for NCFE, within 7 working days for Pearson Edexcel, 2 working days of enrolment for TQUK and within 3 working days for Open Awards. You can get your NCFE results in 7 days, your Edexcel results in 20 working days, your TQUK results in 6 working days and your Open Awards results within 16 working days. Universities and apprenticeships accept all of the awarding bodies. This distinction allows learners to choose the awarding body that aligns best with their educational and career goals. Course Curriculum Unit 1: Speaking and Listening The speaking and listening section entails comprehensive learning and activities, including presenting and narrating skills, argument presentation techniques, and more. Unit 2: Reading Learn to read a text with the help of scanning, skimming, and detailed reading, and also, learn how to find organisational features' purpose from the text. Unit 3: Writing The writing part will cover English grammar, including punctuation, spelling, syntax, etc. enabling you to avoid all the writing errors and mistakes. How This Course Will Work? This Level 1 Functional Skills English course will help you build a solid foundation in mathematics. Throughout the course, it will provide you with various learning materials and activities to enhance your understanding of these subjects. Initial Assessment: To identify the current level of a student's abilities and recommend the appropriate course to enrol in upon completion. Diagnostic Assessment: Identifies skill gaps and produces an individual learning plan Learning Resources: Comprehensive video tutorials, practice quizzes & topic-based tests Progress Tracker: To record your progress in the course Free Mock Test: Access our free mock test facility for professional feedback and to prepare for the final exam. Entry Requirement This level 1 English qualification is available to all students of all academic backgrounds; no experience or previous qualifications are required. However, you will require a laptop/desktop computer and a good internet connection. Exam Structure The Pearson Edexcel, NCFE and Open Awards Functional Skills Qualification in English at Level 1 consist of 3 exams, these are Reading, Writing and Speaking, Listening and Communicating. Speaking, Listening and Communicating (SLC) Exam Awarding Body Duration Number of Marks Pearson Edexcel / NCFE / Open Awards / TQUK Up to 25 minutes Pass/Fail SLC Exam Pearson Edexcel / NCFE: Speaking, listening and communicating will asses through one 5-minute presentation and linked question and answer session in groups of three to five. Also, one 15-minute formal discussion together in groups of three to five learners is included. This exam happens via Microsoft Teams. SLC Exam Open Awards/ TQUK: Speaking, listening and communicating happen through one 10-minute presentation and linked question and answer session in groups of three to four. Also, one 10-minute formal discussion together in groups of three to five learners is included. This exam will be on Microsoft Teams. Reading Exam Awarding Body Duration Number of Marks Pass Mark Pearson Edexcel 75 minutes 35 65% NCFE 60 minutes 30 53% – 57% Open Awards 60 minutes 30 18 out of 30 TQUK 60 minutes 20 not fixed, varies paperwise Reading is evalute through a test consisting of multiple-choice, short open-response and medium open-response questions. Writing Exam Awarding Body Duration Number of Marks Pass Mark Pearson Edexcel 60 minutes 36 63% NCFE 60 minutes 44 57% – 61% Open Awards 60 minutes 60 36 out of 60. TQUK 60 minutes 54 not fixed, varies paperwise. Reading/Writing Exam Pass Mark: Learners should achieve the overall marks mentioned in the table to pass the reading exam. However, the awarding process will determine specifically where the pass mark sits for each assessment version. Therefore, the pass mark may vary between assessments. Recognised Accreditation This Functional Skills English Level 1 has been independently accredited by Pearson Edexcel, NCFE and Open Awards, also regulated by Ofqual. The Office of Qualifications and Examinations Regulation (Ofqual) is responsible for regulating qualifications, assessments, and examinations in England. Pearson Edexcel is the most prestigious awarding body, for an academic and vocational qualifications. Pearson Edexcel qualifications are regulated by Ofqual and recognised by universities and employers across the world. NCFE is a charity and awarding organisation that provides qualifications in England, Wales, and Northern Ireland. It is regulated by Ofqual in England and recognised in Wales and Northern Ireland. Open Awards is an awarding organisation that offers a wide range of qualifications across various sectors, including education, health and social care, and business. Their qualifications are regulated by Ofqual and are designed to meet the needs of learners and employers. Open Awards also works closely with educational institutions and employers to ensure their qualifications are relevant and up-to-date. TQUK is an awarding organisation approved by Ofqual and offers RQF courses in a variety of sectors. RQF courses have different credit values that can be applied to the National Credit Transfer System. TQUK accredits courses developed by industry experts and collaborates with organisations to ensure the quality and value of the courses provided. FAQs What are functional skills English level course 1 equivalent to? Level 1 English equals a GCSE Grade 1 to 3 or D-G. This means that achieving a Level 1 qualification in English demonstrates a basic understanding and practical application of the English language, including reading, writing, and communication skills. What is the Advanced course of Functional Skills English Level 1? The advanced course of functional skills English level 1 is the level 2 English course. In the advanced course, you will learn English in depth. Do Universities Accept Functional Skills Level 1? Some universities may approve the functional skills English level 1 as an alternative to GCSEs or other qualifications, it ultimately depends on the specific university and its admissions policies. Therefore, it's best to check with the university's requirements. However, most universities usually require a higher level of English proficiency, like Functional Skills English level2 GCSE Grade C/4 in English. How long are these Functional Skills Exams? Lead Academy's Pearson Edexcel and NCFE Qualifications in English Level 1 consist of internally marked speaking, listening, and communicating assessments and externally marked reading and writing assessments. The speaking and listening assessments include a 5-minute presentation and a 15-minute formal discussion in groups of three to five learners. The reading assessment lasts 75 minutes and consists of multiple-choice, short open-response, and medium open-response questions. The writing assessment, which includes tasks assessing spelling, punctuation, and grammar, lasts 60 minutes. Is English Functional Skills Level 1 difficult? Functional English skills Level 1 is generally less complicated than GCSE English. The exam focuses on basic language skills and communication, emphasizing practical, real-world applications. The exam is designed to be accessible to many learners, including those who may have struggled with traditional classroom-based learning. However, it still requires a good understanding and proficiency in English, so preparing and practicing in advance is essential. What is the Difference between Functional Skills and GCSE? A Functional skills course develops for the one who wants to learn Math, English, and ICT for individual achievement in the daily workplace. On the other hand, GCSE focuses on theories and tests your academic ability. How will I access the functional skills Maths level 1 course after payment? A confirmation email will be sent to your registered email after payment. Hereafter anytime, you can start your learning journey with Lead Academy. What is an Accredited course? The professional body approves the procedures if any e-learning platform claims its courses are accredited. What is the benefit of doing an accredited course? You will only realize the benefit of having an accredited certificate once you face the corporate world. As employees, job places, and more value the accredited certificate, you must own this certificate by doing the course with us. What are the system requirements for remote exam? For Pearson Edexcel and NCFE: To sit your assessment, you’ll need: A laptop/desktop with webcam and microphone; you can’t sit the assessment on a tablet or smartphone a good Wi-Fi connection – recommended minimum 1Mbit/s Upload, minimum 10Mbit/s Download. You MUST use google chrome browser for the exam, as this is recommended by the awarding body. A smartphone or tablet (Apple iOS 8.0 / Android 4.1 or higher) - this will be used to record you taking the assessment. A suitable environment - quiet room with no distractions The link for the assessment sent to your email; remember to check your spam/junk folder. You must activate Airplane mode on your smartphone however you need to be connected to Wi-Fi, so turn on Airplane mode then reactivate your Wi-Fi. Please familiarise yourself with the potential violations as these can potentially lead to the assessment being voided. Ensure ALL equipment is plugged in (including phone for the recording of sessions). Loss of power at any point could lead to the assessment being voided. You must brief other members of your household/workplace that you’re sitting an assessment, and they must not enter the room at any point. There is a 24-hour live chat function within the assessment software for technical support should you need it at any time. For Open Awards: In order to take your exam, you need to have the following equipment: A good quality laptop or PC with a minimum screen size of approx. 14” and minimum resolution of 1024 x 768. A stable internet connection with at least 3mbps. An integrated (i.e., fixed) webcam on your PC/ laptop or a portable webcam. If using a PC/ laptop with an integrated webcam, a reflective surface (e.g., a mirror) must be available. This will be used to show the invigilator the space immediately surrounding your screen and keyboard. A basic (non-scientific) calculator for maths assessments. You will have access to an on-screen calculator but may feel more comfortable using a separate calculator. Please note that all workings need to be added to the assessment platform if you use a separate calculator so that your workings can be marked. Plain paper. You will need to show this to your invigilator at the beginning of the exam to assure them that you do not have access to notes. A dictionary (where allowed). Supported Browsers Chrome: 34.0.1847 or above Microsoft Edge: Version 88.0.705.81 or newer Firefox: 31.0 or above Safari: 6.2 or above Safe Exam Browser 2.0.2 or above Please note: Chromebooks are not compatible with the Safe Exam Browser Browser settings Popups must be allowed. Guidance on how to do this below: Chrome Edge Firefox Safari For TQUK: Exam conditions All remote exams must take place in a controlled environment. Training Qualifications UK (TQUK) defines a controlled environment as a quiet, appropriate space conducive to the undertaking of a remotely invigilated exam. The environment must be: populated only by you, the learner, and no other parties well-lit to allow maximum webcam visibility free from distractions that may cause you to divert your attention away from the computer screen or move outside of the webcam’s viewing range free from notes and posters on the wall free from noise free from personal or sensitive material free from visual or physical access to supporting materials (such as educational texts) free from electronic devices, other than the computer used to undertake the exam. The space, as described above, must meet these requirements throughout the entire duration of the exam. If the exam conditions requirements are not met, the exam may be voided. If, for any reason, you are unable to undertake the exam in a space that meets these requirements, you should inform your training provider/recognised centre at the earliest opportunity and arrange your exam at a time when these conditions can be met. You must have a desktop or laptop computer that is equipped with a working webcam, a stable internet connection, and the Google Chrome web browser (available here). Requirements and guidance for materials: The following relates to materials within the controlled environment and must be followed to ensure compliance: Mobile phones and electronic devices, except for the computer you are using to undertake the exam, must be switched off and stored in an inaccessible location. Smartwatches and other wearable technological devices must be switched off and removed. Headphones must not be worn. Water must be stored in a clear glass or a clear bottle with the labels removed. No other food or drink is permitted. Second monitors are not permitted. Identification must be clearly presented to the camera at the start of an exam. If identification is not provided, or is unclear, at the start of the exam, this will result in the exam being voided. A room sweep must be completed at the start of an exam. If a room sweep is not completed, the exam will be voided. has context menu

Complete VB.Net training course description A hands on introduction to programming in Visual BASIC .Net. What will you learn Build Visual BASIC applications. Build simple components Debug Visual BASIC programs. Examine existing code and determine its function. Complete VB.Net training course details Who will benefit: Anyone wishing to program in Visual BASIC. Anyone wishing to build Windows based applications. Prerequisites: None although experience in another high level language would be useful. Duration 5 days Complete VB.Net training course contents Writing your first program Visual Studio, forms designer, running VB programs, the UI, properties, writing the code. Toolbox Controls Basic use, input controls, ActiveX controls. Menus and Dialog Boxes Menus, Dialog Box controls, event procedures. Visual Basic .NET variables and operators Variables, I/O, data types, constants, operators, Math Methods, precedence. Decision Structures and Loops and Timers Event-Driven programming, Ifâ¦Then, Select Case, Forâ¦Next Loops, Timer Control. Debugging Visual Basic .NET Programs Break Mode, watch & command windows. Structured Error Handling Try...Catch, Finally, Err Object, retry periods. Modules and Procedures Standard modules, public variables, procedures. Arrays and Collections to Manage Data Fixed-Size & dynamic Arrays, ReDim Preserve, object collections, Controls Collection. Text Files and String Processing Text Box object, Text String methods, sorting. Automating Office Applications Application objects, automation in VB, the Object Browser, the Process Component. Deploying Visual Basic .NET Applications Planning a deployment, ways to deploy an application, deployment projects, options. Managing Windows Forms Forms, positioning, manipulation, adding controls, organizing controls, Startup Object. Adding Graphics and Animation Effects System.Drawing namespace, coordinates, SystemPaint Event, animation, transparency. Inheriting Forms and Creating Base Classes Inheriting forms, inheritance picker, base classes and inheritance, classes in projects. Working with Printers PrintDocument class, Text Box object, Print Preview and Page Setup Dialog Boxes. Database programming with ADO.NET Databases, ADO.NET, Data Adapters, Datasets, Bound & Navigation Controls. Displaying database records, formatting DataGrid cells, updating the database. Displaying HTML Documents Using IE IE Object, Internet Controls, IE Events. Web Forms for Interactive Web Applications ASP.NET, Web Forms vs. Windows Forms, HTML controls, web applications, event procedures for web forms controls.

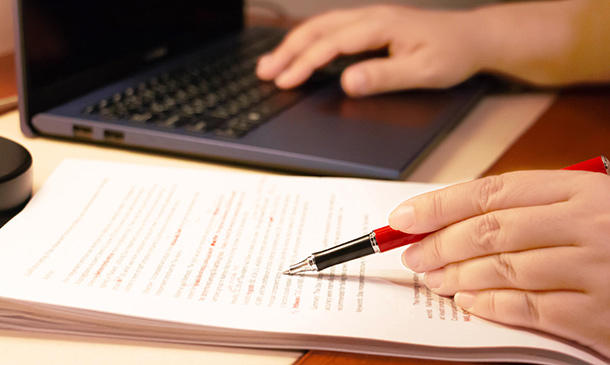
Embark on a literary voyage with our 'Proofreading, Copywriting & Creative Writing Complete Course'. Uncover the secrets behind flawless written content, from understanding proofreading basics to mastering the nuances of copy-editing. Whether it's refining words on paper or digitally, or discerning the art of language usage, this course promises to equip learners with the tools to produce impeccable content and carve a niche in the realm of professional writing. Learning Outcomes Understand and implement the foundational principles of proofreading and copy-editing. Apply style guides proficiently to ensure consistency in writing. Hone skills in spelling, grammar, and fact-checking to enhance content accuracy. Distinguish the differences and techniques of proofreading on various platforms. Grasp the essentials of finding rewarding work in the writing domain and charting one's professional growth. Why choose this Proofreading, Copywriting & Creative Writing Complete Course course? Unlimited access to the course for a lifetime. Opportunity to earn a certificate accredited by the CPD Quality Standards after completing this course. Structured lesson planning in line with industry standards. Immerse yourself in innovative and captivating course materials and activities. Assessments are designed to evaluate advanced cognitive abilities and skill proficiency. Flexibility to complete the Proofreading, Copywriting & Creative Writing Complete Course Course at your own pace, on your own schedule. Receive full tutor support throughout the week, from Monday to Friday, to enhance your learning experience. Who is this Proofreading, Copywriting & Creative Writing Complete Course course for? Aspiring writers keen to sharpen their proofreading and copy-editing abilities. Content creators desiring to elevate the quality of their written work. Individuals exploring a career transition into the writing industry. Professionals involved in publishing, keen to understand editing nuances. Freelancers looking to diversify their skill set and expand clientele. Career path Proofreader: £22,000 - £35,000 Copy-Editor: £24,000 - £40,000 Creative Writer: £20,000 - £50,000 Content Strategist: £30,000 - £55,000 Editorial Assistant: £18,000 - £28,000 Freelance Writer: Varied based on projects and clientele Prerequisites This Proofreading, Copywriting & Creative Writing Complete Course does not require you to have any prior qualifications or experience. You can just enrol and start learning.This Proofreading, Copywriting & Creative Writing Complete Course was made by professionals and it is compatible with all PC's, Mac's, tablets and smartphones. You will be able to access the course from anywhere at any time as long as you have a good enough internet connection. Certification After studying the course materials, there will be a written assignment test which you can take at the end of the course. After successfully passing the test you will be able to claim the pdf certificate for £4.99 Original Hard Copy certificates need to be ordered at an additional cost of £8. Course Curriculum Module 01: Proofreading Basics Proofreading Basics 00:25:00 Module 02: Applying the Style Guide Applying the Style Guide 00:20:00 Module 03: Spelling and Grammar Spelling and Grammar 00:15:00 Module 04: Proofreading on Paper Proofreading on Paper 00:25:00 Module 05: Proofreading On-Screen Proofreading On-Screen 01:00:00 Module 06: Copy-Editing Basics Copy-Editing Basics 01:00:00 Module 07: Copy-Editing - The Use of Language Copy-Editing - The Use of Language 00:45:00 Module 08: Copy-Editing - Checking Accuracy and Facts Copy-Editing - Checking Accuracy and Facts 00:15:00 Module 09: Copy-Editing - The Beginning and The End Copy-Editing - The Beginning and The End 00:15:00 Module 10: Copy-Editing - Legal Checks Copy-Editing - Legal Checks 00:30:00 Module 11: Finding Work and Developing Your Career Finding Work and Developing Your Career 00:20:00 Assignment Assignment - Proofreading, Copywriting & Creative Writing Complete Course 00:00:00
TEFL / TESOL
By IOMH - Institute of Mental Health
Overview This TEFL / TESOL course will unlock your full potential and will show you how to excel in a career in TEFL / TESOL. So upskill now and reach your full potential. Everything you need to get started in TEFL / TESOL is available in this course. Learning and progressing are the hallmarks of personal development. This TEFL / TESOL will quickly teach you the must-have skills needed to start in the relevant industry. In This Mental Health Course, You Will: Learn strategies to boost your workplace efficiency. Hone your TEFL / TESOL skills to help you advance your career. Acquire a comprehensive understanding of various TEFL / TESOL topics and tips from industry experts. Learn in-demand TEFL / TESOL skills that are in high demand among UK employers, which will help you to kickstart your career. This TEFL / TESOL course covers everything you must know to stand against the tough competition in the TEFL / TESOL field. The future is truly yours to seize with this TEFL / TESOL. Enrol today and complete the course to achieve a TEFL / TESOL certificate that can change your professional career forever. Additional Perks of Buying a Course From Institute of Mental Health Study online - whenever and wherever you want. One-to-one support from a dedicated tutor throughout your course. Certificate immediately upon course completion 100% Money back guarantee Exclusive discounts on your next course purchase from Institute of Mental Health Enrolling in the TEFL / TESOL course can assist you in getting into your desired career quicker than you ever imagined. So without further ado, start now. Process of Evaluation After studying the TEFL / TESOL course, your skills and knowledge will be tested with a MCQ exam or assignment. You must get a score of 60% to pass the test and get your certificate. Certificate of Achievement Upon successfully completing the TEFL / TESOL course, you will get your CPD accredited digital certificate immediately. And you can also claim the hardcopy certificate completely free of charge. All you have to do is pay a shipping charge of just £3.99. Who Is This Course for? This TEFL / TESOL is suitable for anyone aspiring to start a career in TEFL / TESOL; even if you are new to this and have no prior knowledge on TEFL / TESOL, this course is going to be very easy for you to understand. And if you are already working in the TEFL / TESOL field, this course will be a great source of knowledge for you to improve your existing skills and take them to the next level. Taking this TEFL / TESOL course is a win-win for you in all aspects. This course has been developed with maximum flexibility and accessibility, making it ideal for people who don't have the time to devote to traditional education. Requirements This TEFL / TESOL course has no prerequisite. You don't need any educational qualification or experience to enrol in the TEFL / TESOL course. Do note: you must be at least 16 years old to enrol. Any internet-connected device, such as a computer, tablet, or smartphone, can access this online TEFL / TESOL course. Moreover, this course allows you to learn at your own pace while developing transferable and marketable skills. Course Curriculum TESOL/TEFL Module 01: Introduction to English Language Teaching & Learning 00:16:00 Module 02: Linguistics 00:46:00 Module 03: English Pronunciation 00:32:00 Module 04: Teaching Grammar and Vocabulary 00:36:00 Module 05: Language Teaching Methodologies 00:25:00 Module 06: Teaching Receptive Skills: Reading 00:20:00 Module 07: Teaching Productive Skills: Writing 00:18:00 Module 08: Teaching Receptive Skills: Listening 00:14:00 Module 09: Teaching Productive Skills: Speaking 00:18:00 Module 10: Lesson Planning and Creating Materials 00:30:00 Module 11: Use of Games and Activities 00:16:00 Module 12: Technology in Second Language Teaching & Learning 00:23:00 Module 13: Classroom Management and Student Motivation 00:34:00 Module 14: Teaching English: Situational Approach 00:38:00 Module 15: Professional Development and Employment 00:30:00

Phonics Teaching & Early Years Foundation Training
By EduXpress
In the heart of every child's educational journey lies the key to unlocking language: Phonics Teaching & Early Years Foundation. This course offers an unparalleled gateway to the world of literacy, particularly in the UK where recent statistics reveal over 80% of early years education incorporates phonics as a primary method of teaching reading. Engaging and comprehensive, this course equips educators with the essential tools to foster a love for reading and language development in young learners. With a curriculum designed to reflect the latest in educational methodologies, it provides a solid foundation for those seeking to make a significant impact in early childhood education. Learning Outcomes: Understand foundational principles of phonics in early education. Develop techniques for engaging young learners in reading. Implement effective phonics strategies in the classroom. Assess children's reading progress using phonics. Create inclusive phonics-based learning environments. Adapt phonics teaching to individual learner needs. Utilise modern resources for phonics education. Foster a lifelong love for reading in early learners. Who Is This Course For? Early Years Educators aspiring to enhance reading skills. Teaching Assistants in primary educational settings. Parents interested in supporting early literacy at home. Career changers aiming to enter the education sector. Volunteers working with children in literacy programs. Why Choose Us? Lifetime access to course materials Full tutor support is available Monday through Friday for all courses Learn essentials skills at your own pace from the comfort of your home Gain a thorough understanding of the course Access informative video modules taught by expert instructors 24/7 assistance and advice available through email and live chat Study the course on your computer, tablet, or mobile device Improve your chances of gaining professional skills and earning potential by completing the course. Why should you study this course? The course offers a comprehensive introduction to the subject matter and provides a solid foundation for further study. It will also help students to gain knowledge and skills that can be applied in their professional or personal life. Assessment The course includes a series of quizzes that will test your understanding and retention of the material covered in the course. The quizzes will help you to identify areas where you may need further practice, and you will have the opportunity to review the course materials as needed. Upon successfully passing the final quiz, you will be able to order your certificate of achievement. Career Path: Early Years Teacher: £24,000 - £30,000 Teaching Assistant: £18,000 - £25,000 Literacy Coordinator: £26,000 - £32,000 Educational Consultant: £30,000 - £40,000 Children's Librarian: £22,000 - £28,000 Reading Specialist: £25,000 - £35,000 Course Content Phonics Teaching & Early Years Foundation Training Module 1: Understanding Phonics Module 2: Phonics and the Alphabet Module 3: Phonics Teaching Strategies Module 4: Implementing Phonics in Reading Module 5: Implementing Phonics in Writing Module 6: Teaching Initial Sounds Module 7: Teaching Vowel Sounds Module 8: Teaching Consonant Sounds Module 9: Dealing with Common Phonics Difficulties Module 10: Developing Phonics Lesson Plans

Translation Freelance Translator Course: Launch Your Career in Language Services
4.3(43)By John Academy
Unlock the doors to a successful career in language services with our comprehensive 'Translation Freelance Translator Course.' Gain essential skills in translation, freelancing, marketing, and more. Launch your career confidently with expert guidance. Join now for a transformative journey into the world of freelance translation!
Learn the ins and outs of proofreading as well as crafting that flawless content with our expertly structured Proofreading & Copy editing course (with a special price, act quick the time's running out!). This course covers all the fundamentals of copy editing and proofreading, as well as the publishing process from the viewpoint of an expert. You will be exposed to trustworthy sources for grammar and spelling throughout the course, which will help you advance your proficiency to an entirely new degree. In addition, when you study the finest techniques for expert copy editing, you'll be alerted to several typical copywriting errors. Key Features of this Proofreading & copy editing course : This Proofreading & Copy editing course is CPD Certified Developed by Specialist Lifetime Access As you progress through the Proofreading & Copy editing course modules, witness the metamorphosis from adept proofreading to seasoned copy editor. Introduce the delicate dance of copy editing basics, a ballet where every comma pirouettes and each sentence is choreographed for maximum impact. Language precision takes center stage, where every word choice becomes a brushstroke on the canvas of communication. But This Proofreading & Copy editing course doesn't stop there - delve into the detective work of verifying facts, ensuring that the narrative not only sings but speaks the truth. Your journey concludes with a flourish, where career development and tantalising job opportunities beckon. The allure of the written word awaits your command - are you ready to wield the power of linguistic finesse? Course Curriculum Proofreading & Copy editing course: Module 01: Essentials of Proofreading Learn fundamental techniques and principles for effective proofreading, honing skills crucial for error detection and correction. Module 02: Implementing the Style Guide Master the application of style guides, ensuring consistency and adherence to established writing conventions across various documents. Module 03: Spelling and Grammar Mastery Develop proficiency in identifying and rectifying spelling and grammar errors, enhancing the clarity and professionalism of written content. Module 04: Proofreading in Print Explore specialized techniques tailored for proofreading printed materials, ensuring accuracy in traditional publishing formats. Module 05: On-Screen Proofreading Techniques Acquire strategies for proofreading digital content, optimizing efficiency and accuracy in the electronic editing process. Module 06: Basics of Copy Editing Delve into the foundational principles of copy editing, focusing on refining language and structure while maintaining authorial intent. Module 07: Language Precision in Copy Editing Refine your ability to scrutinize language choices, ensuring precision and coherence in written communication through meticulous editing. Module 08: Ensuring Accuracy and Verifying Facts in Copy Editing Learn methods for fact-checking and verifying information, crucial for maintaining credibility and reliability in edited texts. Module 09: Commencing and Concluding Copy Editing Tasks Gain insights into the effective initiation and closure of copy editing projects, managing workflow and delivering polished final products. Module 10: Legal Checks in Copy Editing Navigate legal considerations in Copy editing, understanding copyright laws, libel issues, and other legal implications pertinent to written content. Module 11: Career Development and Job Opportunities Explore avenues for professional growth and advancement in the Copy editing industry, identifying potential career paths and networking opportunities. Learning Outcomes Proofreading & Copy editing course: Essentials Mastery: Apply key proofreading skills for error-free content production. Style Guide Implementation: Demonstrate proficiency in adhering to established copy editing guidelines. Spelling Precision: Attain mastery in identifying and correcting spelling and grammar errors. Print Proofreading Skills: Execute effective proofreading techniques for printed materials. On-Screen Mastery: Utilise advanced on-screen proofreading techniques for digital content. Copy Editing Proficiency: Apply fundamental copy editing principles for polished and accurate documents. CPD 10 CPD hours / points Accredited by CPD Quality Standards Who is this course for? This Proofreading & Copy editing course is accessible to anyone eager to learn more about this topic. Through this course, you'll gain a solid understanding of Proofreading & Copy editing. Moreover, this course is ideal for: Aspiring Editors Writers and Journalists Communication Professionals Content Creators Entry-level Editorial Staff Requirements There are no requirements needed to enrol into this Proofreading & Copy editing course. We welcome individuals from all backgrounds and levels of experience to enrol into this Proofreading & Copy editing course. Career path After finishing this Proofreading & Copy editing course you will have multiple job opportunities waiting for you. Some of the the following Job sectors of Proofreading & Copy editing are: Editorial Assistant - £20K to 25K/year. Content Editor - £25K to 35K/year. Copywriter - £22K to 40K/year. Proofreader - £20K to 30K/year. Publishing Assistant - £18K to 24K/year. Certificates Digital certificate - Included Will be downloadable when all lectures have been completed.
