- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
CCNP training course description The Implementing and Operating Cisco Enterprise Network Core Technologies (ENCOR) v1.2 course provides the knowledge and skills needed to configure, troubleshoot, and manage enterprise wired and wireless networks. You'll learn to implement security principles within an enterprise network and how to overlay network design using solutions such as SDAccess and SD-WAN. Course content includes 3 days of self-study material. This course helps you prepare for the 350-401 Implementing Cisco Enterprise Network Core Technologies (ENCOR) exam What will you learn Configure, troubleshoot, and manage enterprise wired and wireless networks Implement security principles within an enterprise network Prepare you prepare to take the 350-401 Implementing Cisco Enterprise Network Core Technologies (ENCOR) exam CCNP training course details Who will benefit: Mid-level network engineers, Network administrators, Network support technicians, Help desk technicians. Prerequisites: Implementation of Enterprise LAN networks. Basic understanding of Enterprise routing and wireless connectivity, and Python scripting Duration 5 days CCNP training course content Cisco Enterprise Network Architecture: Access, distribution, core in the hierarchical network. Cisco Switching Paths: Switching mechanisms, TCAM, CAM, process switching, fast switching, and CEF. Implementing Campus LAN Connectivity: Troubleshoot L2 connectivity using VLANs and trunkingBuilding Redundant Switched Topology: STP Implementing Layer 2 Port Aggregation Troubleshoot link aggregation using Etherchannel EIGRP Implement and optimize OSPFv2/v3, including adjacencies, packet types, and areas, summarization, and route filtering for IPv4/v6 Implement EBGP interdomain routing, path selection, and single and dual-homed networkingImplementing Network Redundancy: HSRP and VRRP Implement static and dynamic NAT Virtualization Protocols and TechniquesVPNs and Interfaces: Overlay technologies such as VRF, GRE, VPN, and LISP Wireless Principles: RF, antenna characteristics, and wireless standards.Wireless Deployment: Models available, autonomous AP deployments and cloud-based designs within the centralized Cisco WLC architecture Wireless Roaming and Location ServicesWireless AP Operation: How APs communicate with WLCs to obtain software, configurations, and centralized managementWireless Client Authentication: EAP, WebAuth, and PSK wireless client authentication on a WLC. Troubleshoot wireless client connectivity issues using various available tools Troubleshoot networks using services such as NTP, SNMP, Cisco IP SLAs, NetFlow, and Cisco IOS EEM Explain network analysis and troubleshooting tools, which include show and debug commands, as well as best practices in troubleshootingMulticast Protocols: IGMP v2/v3, PIM DM/SM and RPs Introducing QoS: Concepts and features. Implementing Network Services: Secure administrative access for Cisco IOS devices using CLI access, RBAC, ACL, and SSH, and device hardening concepts to secure devices from less secure applications Using Network Analysis ToolsInfrastructure Security: Scalable administration using AAA and the local database, features and benefits Enterprise Network Security Architecture: VPNs, content security, logging, endpoint security, personal firewalls, and other security features. Automation and Assurance with Cisco DNA Center: Purpose, function, features, and workflow. Intent-Based Networking, for network visibility, proactive monitoring, and application experienceCisco SD-Access Solution: Nodes, fabric control plane, and data plane, VXLAN gatewaysCisco SD-WAN Solution: Components and features of Cisco SD-WAN solutions, including the orchestration, management, control, and data planesBasics of Python Programming: Python components and conditionals with script writing and analysis Network Programmability: NETCONF and RESTCONF APIs in Cisco DNA Center and vManage Labs: Investigate the CAM. Analyze CEF. Troubleshoot VLAN and Trunk Issues. Tuning STP and Configuring RSTP. Configure MSTP. Troubleshoot EtherChannel. Implement Multi-area OSPF. Implement OSPF Tuning. Apply OSPF Optimization. Implement OSPFv3. Configure and Verify Single-Homed EBGP. Implementing HSRP. Configure VRRP. Implement NAT. Configure and Verify VRF. Configure and Verify a GRE Tunnel. Configure Static VTI Point-to-Point Tunnels. Configure Wireless Client Authentication in a Centralized Deployment. Troubleshoot Wireless Client Connectivity Issues. Configure Syslog. Configure and Verify Flexible NetFlow. Configuring Cisco IOS EEM. Troubleshoot Connectivity and Analyze Traffic with Ping, Traceroute, and Debug. Configure and Verify Cisco IP SLAs. Configure Standard and Extended ACLs. Configure Control Plane Policing. Implement Local and Server-Based AAA. Writing and Troubleshooting Python Scripts. Explore JSON Objects and Scripts in Python. Use NETCONF Via SSH. Use RESTCONF with Cisco IOS XE.

Online IAM Diploma D24001
By Asset Management Consulting (Asset Management Academy)
Online Asset Management Diploma course. Sit the IAM Diploma anywhere in the world. February to March 2024

Annual Online Safety Update for DSLs, including emerging risks and trends
By Brightcore Consultancy
In this masterclass we'll unravel the complexities of the online world, shedding light on the most pressing current and emerging risks and opportunities faced by children and young people, from the perspective of the DSL, as Online Safety Lead.

Online IAM Diploma D23005
By Asset Management Consulting (Asset Management Academy)
Online Asset Management Diploma course. Sit the IAM Diploma anywhere in the world

Certificate in Business and Commercial Law (CBCL)
By EMG Associates UK Limited
Certificate in Business and Commercial Law (CBCL) Why Attend This course is designed for professionals with little or no prior legal background but who are required to make organizational decisions involving legal matters. It will provide participants with the fundamental principles of commercial law, including commercial contracts and negotiation, sale of goods, intellectual property rights and employee relations. It also covers all the legal aspects of setting up a business, running a business and closing a business Participants will gain an in-depth understanding of international commercial law with emphasis on the common law system. Participants will have the opportunity to learn and analyze key legal issues regarding contracts and the business as a whole which they are likely to encounter within their organization. Course Methodology In this interactive training course participants will frequently work in pairs as well as in larger groups to complete exercises as well as regional and international case studies. Course Objectives By the end of the course, participants will be able to: Apply legal rules and principles to speciï¬c commercial situations through consideration of relevant case law Negotiate commercial contracts complying with commercial and legal requirements Increase proï¬tability within their organization by selecting appropriate methods of distribution of goods Recognize and analyze how intellectual property rights aï¬ect their organization Evaluate and modify organizational employment practices complying with labor law requirements Target Audience This course is suitable for those with little or no formal training in commercial law yet would be required to understand the fundamentals of commercial law as it may directly impact their work. It will particularly beneï¬t directors and executives who have direct responsibility for legal decisions within the organization. In-house council new to the region, and those working within a legal department, will also ï¬nd this course highly beneï¬cial. Target Competencies Drafting Contracts Contract Negotiation Understanding Commercial Terms Understanding Employment Law Implementing Organizational Employment Practices Understanding Intellectual Property Understanding corporate restructuring Understanding the effect of breach of commercial contract terms Note The Dubai Government Legal Aï¬airs Department has introduced a Continuing Legal Professional Development (CLPD) programme to legal consultants authorised to practise through a licensed ï¬rm in the Emirate of Dubai. We are proud to announce that the Dubai Government Legal Aï¬airs Department has accredited EMG Associates as a CLPD provider. In addition, all our legal programmes have been approved. This PLUS Specialty Training Legal course qualiï¬es for 4 elective CLPD points. Overview of commercial & business law Areas of commercial and business law Types of commercial contracts Commercial contracts in the civil law and common law systems Sources of English law Civil law v Common law Civil law in the GCC Formalities for a binding contract Elements required for an enforceable contract Rules for contract interpretation implied terms v express terms identifying risks and how to minimise risks Structure of a commercial contract Preliminary documents in international transactions Memorandum of Understanding/ Heads of Terms. Are they legally binding? Commercial implications Boilerplate/ miscellaneous provisions- the important but forgotten clauses- beware! Force majeure v Frustration Notices Set oï¬ No waiver Entire Agreement/ non- reliance clause Times is of the essence Assignment v Novation Governing law Common mistakes in choice of law Jurisdiction clause Exclusive v Non-exclusive Factors in deciding the jurisdiction clause International dispute resolution Litigation Importance of Alternative Dispute Resolution (ADR) Arbitration Mediations Conciliation Negotiation Remedies for breach of contract Damages Specific performance Injunctions Advantages and disadvantages of different business forms Types of business vehicles Sole trader Partnerships Limited Liability Partnerships Companies Cross Border Transactions Distributorship Agency Joint Venture Acquisitions Share purchase v Business purchase Apportioning risks and liabilities through warranties and indemnities Negotiating warranties and indemnities Corporate insolvency Tests identifying insolvency Consequence for directors who fail to react to insolvency Types of insolvency Administration Receivership Creditor Voluntary Liquidation Compulsory Liquidation Commercial Tort Tort of negligence Defamation Libel Slander Recent case law on defamation Managing risk Prevention is better than cure: Eï¬ective risk management Intellectual Property Rights management Types of Intellectual Property copyright trademark patent design rights confidential information Assignment v Granting a license The law of passing off Intellectual Property in the GCC Employment law issues in the common law systems and the GCC Types of employment contracts Grounds for dismissal Wrongful dismissal Redundancy Unfair dismissal Commercial real estate in the GCC Leasehold Freehold

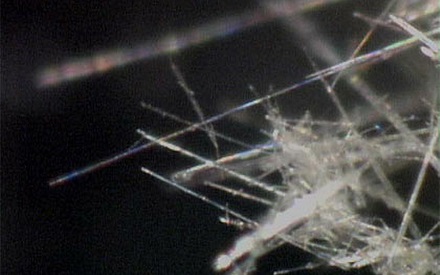
BOHS/OHTA W504 - Asbestos and other fibres
By Airborne Environmental Consultants Ltd
P404 Air Sampling of Asbestos and MMMF and Requirements for a Certificate of Reoccupation Following Clearance of Asbestos is the industry standard qualification for those whose work involves air sampling and clearance testing, such as asbestos analysts. In addition to holding the qualification, they are required to undertake and provide evidence of annual refresher training. RP404 Refresher is a new course, specifically designed to meet this requirement. RP404 Refresher enables candidates to revise and update their knowledge on air sampling and clearance testing techniques, and to receive a certificate of course completion by passing a written examination, which covers both the theory and practice of air sampling and clearance testing.
Securing UNIX systems training course description This course teaches you everything you need to know to build a safe Linux environment. The first section handles cryptography and authentication with certificates, openssl, mod_ssl, DNSSEC and filesystem encryption. Then Host security and hardening is covered with intrusion detection, and also user management and authentication. Filesystem Access control is then covered. Finally network security is covered with network hardening, packet filtering and VPNs. What will you learn Secure UNIX accounts. Secure UNIX file systems. Secure UNIX access through the network. Securing UNIX systems course details Who will benefit: Linux technical staff needing to secure their systems. Prerequisites: Linux system administration (LPIC-1) Duration 5 days Securing UNIX systems course contents Cryptography Certificates and Public Key Infrastructures X.509 certificates, lifecycle, fields and certificate extensions. Trust chains and PKI. openssl. Public and private keys. Certification authority. Manage server and client certificates. Revoke certificates and CAs. Encryption, signing and authentication SSL, TLS, protocol versions. Transport layer security threats, e.g. MITM. Apache HTTPD with mod_ssl for HTTPS service, including SNI and HSTS. HTTPD with mod_ssl to authenticate users using certificates. HTTPD with mod_ssl to provide OCSP stapling. Use OpenSSL for SSL/TLS client and server tests. Encrypted File Systems Block device and file system encryption. dm-crypt with LUKS to encrypt block devices. eCryptfs to encrypt file systems, including home directories and, PAM integration, plain dm-crypt and EncFS. DNS and cryptography DNSSEC and DANE. BIND as an authoritative name server serving DNSSEC secured zones. BIND as an recursive name server that performs DNSSEC validation, KSK, ZSK, Key Tag, Key generation, key storage, key management and key rollover, Maintenance and resigning of zones, Use DANE. TSIG. Host Security Host Hardening BIOS and boot loader (GRUB 2) security. Disable useless software and services, sysctl for security related kernel configuration, particularly ASLR, Exec-Shield and IP / ICMP configuration, Exec-Shield and IP / ICMP configuration, Limit resource usage. Work with chroot environments, Security advantages of virtualization. Host Intrusion Detection The Linux Audit system, chkrootkit, rkhunter, including updates, Linux Malware Detect, Automate host scans using cron, AIDE, including rule management, OpenSCAP. User Management and Authentication NSS and PAM, Enforce password policies. Lock accounts automatically after failed login attempts, SSSD, Configure NSS and PAM for use with SSSD, SSSD authentication against Active Directory, IPA, LDAP, Kerberos and local domains, Kerberos and local domains, Kerberos tickets. FreeIPA Installation and Samba Integration FreeIPA, architecture and components. Install and manage a FreeIPA server and domain, Active Directory replication and Kerberos cross-realm trusts, sudo, autofs, SSH and SELinux integration in FreeIPA. Access Control Discretionary Access Control File ownership and permissions, SUID, SGID. Access control lists, extended attributes and attribute classes. Mandatory Access Control TE, RBAC, MAC, DAC. SELinux, AppArmor and Smack. etwork File Systems NFSv4 security issues and improvements, NFSv4 server and clients, NFSv4 authentication mechanisms (LIPKEY, SPKM, Kerberos), NFSv4 pseudo file system, NFSv4 ACLs. CIFS clients, CIFS Unix Extensions, CIFS security modes (NTLM, Kerberos), mapping and handling of CIFS ACLs and SIDs in a Linux system. Network Security Network Hardening FreeRADIUS, nmap, scan methods. Wireshark, filters and statistics. Rogue router advertisements and DHCP messages. Network Intrusion Detection ntop, Cacti, bandwidth usage monitoring, Snort, rule management, OpenVAS, NASL. Packet Filtering Firewall architectures, DMZ, netfilter, iptables and ip6tables, standard modules, tests and targets. IPv4 and IPv6 packet filtering. Connection tracking, NAT. IP sets and netfilter rules, nftables and nft. ebtables. conntrackd Virtual Private Networks OpenVPN server and clients for both bridged and routed VPN networks. IPsec server and clients for routed VPN networks using IPsec-Tools / racoon. L2TP.

Prospect Maturation
By EnergyEdge - Training for a Sustainable Energy Future
About this Training Course The prospect maturation process, from a lead to a drillable prospect, is at the heart of the exploration business. This 5 full day course will cover all aspects of the prospect maturation process: play understanding in the context of regional geological understanding, detailed prospect evaluation; realistic risk & volume assessment consistent with the play understanding and prospect details, and an introduction to exploration economics. Throughout the course, there is a strong focus on pragmatic (geo)logical approach for assessing those aspects that are input parameters for a meaningful assessment of prospect risks and volumes, with emphasis on a balanced integration of contributions from different sub-surface disciplines. Many examples from basins from around the world are used to illustrate how traps, reservoirs, seals and charge occur in different basin settings. Specifics topics that will be discussed include the following: The statistical fundamentals for risk and volume assessment will be presented, with practical exercises for understanding the results of a risk & volume assessment as they are displayed in expectation curves. The difference between risk and uncertainty. A full discussion of the essential requirements for a working petroleum system: Trap, reservoir, seal and charge. Examples of how traps, reservoirs, seals and charge work in different basin types around the globe and in Australian basins. Exercises and guidelines for estimating uncertainties for prospect parameters, including advice for deciding which distribution type to use, and how to constrain those distributions for meaningful uncertainty ranges (setting minimum most likely and maximum values). Particular emphasis will be given to estimating hydrocarbon column lengths with their associated uncertainties in undrilled prospects. Prospects and plays: The value of play maps and how these should be used for assessment of prospect risks and for ranking of prospects within a play. Calculating volume ranges for prospects. Calculating volumes for groups of prospects; how to add risked prospect volumes for a statistically correct representation of the volume promise of a portfolio of prospects. Geophysical evidence: Incorporating geophysical evidence (DHIs) consistently and realistically in a risk assessment. An understandable and geology-based workflow, consistent with Bayes theorem, will be presented. Exploration economics. Training Objectives What this course will cover in 5 days: This course describes the various aspects that need to be considered in the prospect maturation process, including: Play development in the context of a sound understanding of the regional geology Detailed prospect evaluation and understanding of the critical aspects of traps, reservoirs, seals and charge Examples from plays and prospects in different basin settings from around the globe Realistic and pragmatic risk and volume assessment, based on the geological understanding of plays and prospects An introduction to exploration economics Examples of plays, oil and gas fields and prospects from basins from around the world, including the Far East, will be given. Target Audience This course is designed primarily for Geoscientists in exploration who would like to improve their expertise of the prospect maturation process and risk and volume assessment. The course has proven to be of value for explorers in the early phase of their career, seasoned explorers and team leaders. It will also benefit staff from disciplines working closely with exploration staff including Prospect Portfolio Analysts, Petrophysicists, Geophysicists and Reservoir Engineers. Course Level Intermediate Training Methods At the end of the course, the participants will have a good understanding of the essentials for realistic risk and volume assessments of exploration prospects. The course should allow participants to produce well-considered and realistic assessments for prospects they may be working on, and to understand and constructively challenge risk and volume assessments of colleagues and/ or partners/ competitors. Each topic is introduced by a lecture, and learning is re-inforced by practical exercises and discussions. Hand-out materials in paper and/or electronic format will be provided. Time will be made available to discuss aspects of prospects that may be brought in by course participants. Trainer Your expert course leader has a PhD in Geology from the University of Utrecht. He worked for 31 years (1979 -2010) with Shell as an exploration geologist in a variety of functions across the globe. As Principle Technical Expert, he was responsible for ensuring that Risk & Volume assessments were carried out consistently and correctly in all of Shell's exploration units. In this capacity, he led and participated in countless prospect review sessions and developed and conducted a successful in-house course on Risks & Volume assessment. As manager of the Exploration Excellence Team, he performed in depth analysis of basins and plays and provided advice on exploration opportunities to senior management. Together with his team, he visited most of Shell's exploration offices, working hands-on with Shell's local exploration teams to generate new play and prospect ideas and to suggest evaluation techniques and technologies to apply. In 2010, he was appointed as extraordinary professor Regional and Petroleum Geology at the VU university of Amsterdam and in 2012 also at the University of Utrecht. He was visiting professor at the University of Malaya (Malaysia). Through his own consultancy, as of 2010, he provides advice on exploration activities to several companies and is regularly invited to carry out technical reviews. Activities cover all continents and include Portfolio Reviews, Prospect assessment, Play-based Exploration, and Geothermal activities. He conducts courses on several topics including Risk & Volume Assessment, Prospect Maturation, Basin Analysis, Play-based Exploration, Trap & Seal Analysis, Petroleum Geology for Non-geologists. Some of his recent publications include: De Jager, J. & van Winden, M. (2020): Play-Based Exploration of the petroleum potential of the Tremp-Graus, AÃnsa and eastern Jaca Sub-basins in the southern Pyrenees. Invited contribution for Digital Geology, EAGE special publication (eds: Grötsch, J. & Pöppelreiter, M.) De Jager, J. (2020). Concepts of Conventional Petroleum Systems. Invited contribution for Regional Geology and Tectonics Volume 1: Global Concepts, Techniques and Methodology (eds: Adam, J., Chiarelly, D. & Scarselli, N.) De Jager, J. (2021): Handbook Risk & Volume Assessment. Self-published De Jager, J., Van Ojik, K & Smit, R. (2023 - in preparation): Geological Development of The Netherlands. In: Geology of The Netherlands (eds: Ten Veen, J., Vis, G-J., De Jager, J. @ Wong, T.) POST TRAINING COACHING SUPPORT (OPTIONAL) To further optimise your learning experience from our courses, we also offer individualized 'One to One' coaching support for 2 hours post training. We can help improve your competence in your chosen area of interest, based on your learning needs and available hours. This is a great opportunity to improve your capability and confidence in a particular area of expertise. It will be delivered over a secure video conference call by one of our senior trainers. They will work with you to create a tailor-made coaching program that will help you achieve your goals faster. Request for further information about post training coaching support and fees applicable for this. Accreditions And Affliations

Complete C programming training course description A hands-on introduction to programming in the ANSI C programming language. The course initially moves at a fast pace in order to spend as much time as possible on the subject of pointers - the area which cause the most bugs in C programs. What will you learn Write ANSI C programs Use the C libraries Debug C programs Examine existing code and determine its function. Complete C programming training course details Who will benefit: Programmers wishing to learn C. Programmers wishing to learn C++ or Java. Prerequisites: None, although experience in another high level language would be useful. Duration 5 days Complete C programming training course contents Getting started The compilation process, comments, main(), statement blocks, printf(). C data types and operators char, int, float and double, qualifiers, arithmetic and assignment operators, precedence, Associativity. Basic I/O C libraries, stdin and stdout, getchar(), putchar(), printf() formatting. Flow control if else, dangling elses, else if, while and for loops. switch statements, the null statement, break, continue and gotos. Functions Function calls, arguments and return types, function declarations (prototypes), function definitions, scope of variables. The preprocessor Preprocessor actions, macros, #include. Libraries and their relationship with header files. Conditional compilation. More data types and operators Logical, bitwise and other operators, type conversion, casting, typedefs and access modifiers. Arrays Declaring and handling arrays, common gotchas, multidimensional arrays. Pointers What are pointers? Why they are so important, declaring and using pointers,The three uses of the *,pointer example - scanf, pointers as arguments. More pointers Golden rules of pointers and arrays, pointers to arrays, pointer arithmetic, arrays of pointers, multiple indirection. Character/string manipulation Arrays of characters, string definition, working with strings, String library. Program arguments argc and argv, example uses,char *argv[] versus char ** argv. Program structure and storage classes Globals (externals), multi source programs, the look of a C program. Structures Declaration, the . and - operators, unions and bitfields. Library functions File handling, fopen and fclose, reading from and writing to files, fseek().calloc() and malloc()

Application of Structural Geology in Seismic Interpretation
By EnergyEdge - Training for a Sustainable Energy Future
About this Training Course Seismic interpretation requires an understanding of structural development and its interrelation with the stratigraphic system. Bias and misunderstanding have unfortunately resulted in countless dry holes. So go beyond tracing horizons and understand their context within the structural system by extracting key information from seismic surveys and other datasets. In this 5 full-day training course, participants will learn a variety of modern structural concepts and techniques and their role in the interpretation of seismic data. Using an applied 'hands-on' approach, participants will be exposed to a diversity of worldwide case examples with complementary exercises - both of an individual and group nature. The course is designed from an applied standpoint, with numerous examples and hands-on exercises from the petroleum industry. This course can also be offered through Virtual Instructor Led Training (VILT) format. Training Objectives By the end of this course, the participants will be able to: Go beyond tracing horizons and marking faults and truly understand the structural and stratigraphic system. Understand the role of tectonics and deformation in the formation of various types and orientations of geologic structures. Understand the interaction of the structural system with the stratigraphic and sedimentologic environment for better prediction of reservoir formation. Integrate data from the large seismic scale to subseismic scale, including seismic anisotropy, to understand better the overall petroleum system. Learn about the common pitfalls of interpretation. Target Audience This course is intended for geologists, geophysicists, reservoir engineers, and exploration/production managers. Course Level Intermediate Trainer Your expert course leader received his B.S. and M.S. degrees in Geology from the now University of Louisiana-Lafayette in 1989 and 1990 respectively, and his Ph.D. as a National Science Foundation fellow at Baylor University, Waco, Texas, in 1993. From 1994 - 1996, he studied planetary tectonics as a NASA-funded postdoctoral fellow at Southern Methodist University. In 1996, he returned to UL-Lafayette, where he was awarded in 1997 the Hensarling-Chapman Endowed Professorship in Geology. He began independent consulting activities in 1991, and in 2001, he left academia for full-time consulting for clients ranging from one-man shops to supermajors. He rejoined UL-Lafayette as an adjunct professor from 2011 - 2018. He is an active researcher, receiving several million dollars in grants from federal, state, and industry sources, presenting numerous talks, including a 2019 AAPG Levorsen award, and publishing on a diversity of geoscience topics, including a Grover E. Murray Best Published Paper award in 2017. He is co-author of the inaugural GCAGS/GCSSEPM Transactions Best Student Paper award in 2018. He served as the GCAGS Publisher since 2006 and in various GCAGS/GCSSEPM Transactions editing capacities since 2006, including the 2014 and 2017 - 2022 Editor (named Permanent Transactions Editor in 2017), and Managing Editor since 2011, receiving a GCAGS Distinguished Service Award in 2018. He served as the General Chair for GeoGulf 2020 (70th GCAGS/GCSSEPM Convention), the 1st hybrid geoscience conference in the world. He is a Past President of the Lafayette Geological Society and served as its Editor and Publisher from 2002 - 2018. In 2018, he founded the Willis School of Applied Geoscience, reformulating decades of industry-training experience to provide alternative opportunities for graduate-level education. In 2020, he received an Honorary Membership from GCSSEPM. He also joined the LSU faculty as an adjunct professor in 2020. In 2021, he co-founded the Society of Applied Geoscientists and Engineers, serving as its President, General Chair for the SAGE 2022 Convention & Exposition, and Vice-Chair for the Benghazi International Geoscience & Engineering Conference 2022 (BIGEC 2022). POST TRAINING COACHING SUPPORT (OPTIONAL) To further optimise your learning experience from our courses, we also offer individualized 'One to One' coaching support for 2 hours post training. We can help improve your competence in your chosen area of interest, based on your learning needs and available hours. This is a great opportunity to improve your capability and confidence in a particular area of expertise. It will be delivered over a secure video conference call by one of our senior trainers. They will work with you to create a tailor-made coaching program that will help you achieve your goals faster. Request for further information about post training coaching support and fees applicable for this. Accreditions And Affliations
