- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
Supporting Microsoft IIS training course description This course provides students with the fundamental knowledge and skills to configure and manage Internet Information Services. This course is intended to help provide pre-requisite skills supporting a broad range of Internet web applications, security, and knowledge to help support other products that use IIS such as Exchange and SharePoint. What will you learn Install IIS. Configure IIS. Secure websites. Maintain IIS. Supporting Microsoft IIS training course details Who will benefit: Technical staff working with Microsoft IIS. Prerequisites: TCP/IP foundation for engineerss Supporting Windows ( XP or 2000 or 2003) Duration 5 days Supporting Microsoft IIS course contents Overview and Installing IIS Web Server infrastructure, installing IIS. Hands on Default install of IIS, verify and test.. Configuring the default website Default website, IIS Manager, default IIS file structure, configuring DNS records for a website, creating virtual directories and Applications. Hands on Configuring the Default website for public access. Creating Virtual Directories and Applications. Application Pools Application Pool Architecture, Application Pool recycling. Hands on Creating and managing Application Pools. Creating additional websites Multiple websites on a single server, website bindings. Hands on Creating new websites. Website and Web application support Configuring Common features, adding support for web applications. Hands on Adding support for web applications. Securing Websites and applications Access control, sites, applications, authentication and permissions. URL authorization rules. Hands on Configuring Authentication and permissions. Securing Data Transmissions with SSL Certificates and SSL, creating certificates for a web server, adding a certificate to a website. Hands on Certificates and HTTPS. Using the Central Certificate Store The Central Certificate Store. Hands on Install and configure the Central Certificate Store. Configuring Remote Administration Installing and Configuring the Management Service. Connecting to remote web servers and websites. Delegating Management Access. Hands on Remote administration. Implementing FTP Implementing FTP, configuring an FTP site. Hands on Install and configure a secured FTP site. Monitoring IIS IMonitoring IIS logs with Log Parser. Hands on Analyze a set of IIS log files for possible issues using Log Parser. Analyze performance data for performance related problems using PerfMon. Backing up and Restoring IIS The IIS environment. Hands on Performing a backup and restore of a website. Building Load-Balanced Web Farms Load-balancing mechanisms, building a Load-Balanced Web Farm using ARR, sharing content to a Web Farm using a network share, Sharing content to a Web Farm using DFS-R, Sharing IIS Configurations in a Web Farm. Hands on Installing and configuring ARR, sharing content to a Web Farm using network share and DFS-R, sharing IIS Configurations in a Web Farm.

3G training course description This course is designed to give the delegate an understanding of the technologies used within a 3G UMTS mobile network. During the course we will investigate the UMTS air interface and the use of Wideband-Code Division Multiple Access (WCDMA) to facilitate high speed data access, together with HSPA to offer mobile broadband services. We will describe the use of soft handover rather than hard handover procedures and soft capacity sharing. The course includes a brief exploration of the UMTS protocol stack and the use of PDP Context and QoS support features. What will you learn Explain the 3G UMTS architecture. Describe the role of a Drifting & Serving RNC. Explain the use of ARQ & HARQ for mobile broadband. Describe how IMS integrates into the architecture. Describe the use of Media Gateway Controllers. Identify the temporary identities used within 3G UMTS. 3G training course details Who will benefit: Anyone working within the telecommunications area, especially within the mobile environment. Prerequisites: Mobile communications demystified Telecommunications Introduction Duration 2 days 3G training course contents D3GPP specifications 3GPP standards body, Evolution path, Frequency and bandwidth, Conceptual model, UMTS general architecture, UTRAN architecture & radio access bearer. CDMA principles CDMA principle, Code characteristics, Code requirements. CDMA requirements Synchronization, Power control, Soft handover, Rake receiver, Antenna consideration, Multi-user detection. Radio interface protocol architecture Access stratum & non-access stratum, Overall protocol structure, Logical and transport channels, Physical channels, Protocol termination. Layer 2 Protocols Medium Access Control (MAC) Protocol, Radio Link Control (RLC) Protocol, Packet Data Convergence Protocol (PDCP) protocol, Radio Interface for Broadcast/Multicast Services. Radio Resource Control (RRC) Protocol RRC Architecture, RRC Protocol State, Broadcast of information, RRC connection management, Radio bearer management, RRC connection mobility functions, Power control, Ciphering and Integrity. Mobile procedures Mobility management states and transitions, UMTS identities, Procedures in Idle mode (location updates, cell selection/ re-selection), Circuit-switched call set-up, Packet-switched context activation and context preservation, Data transfer initialization, Soft-handover procedure. Introduction to HSPA The need for high speed data, Fast HARQ, Improved scheduling, Additional channels, Soft combining, HS-DSCH codes, Uplink HSPA vs downlink HSPA, Full HSPA, Use of MIMO, Enhanced CELL_FACH.

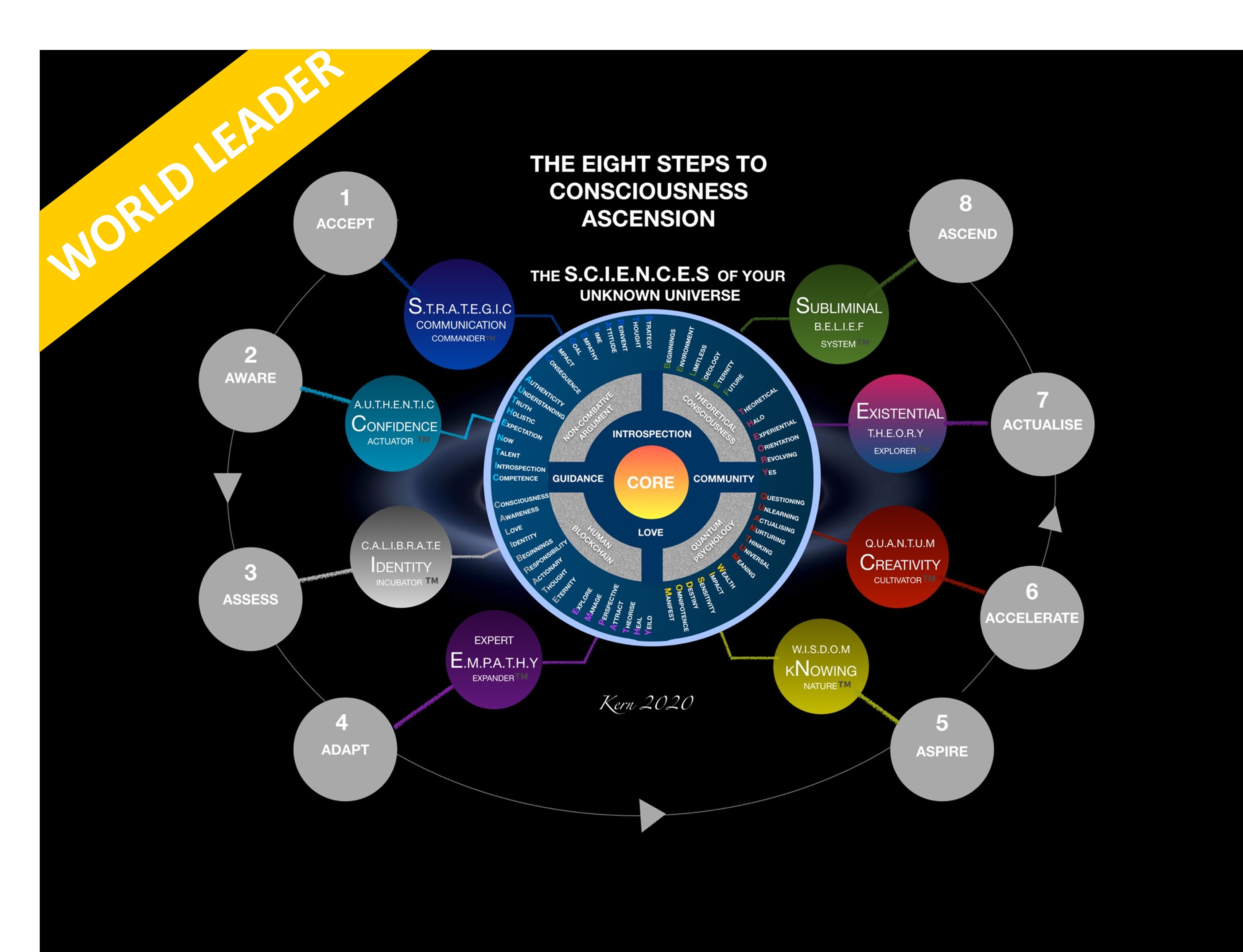
S.C.I.E.N.C.E.S Of Your Unknown Universe - World Leader
By Council For Human Development Swiss Association
The S.C.I.E.N.C.E.S World Leader Program is a 6-month powerful personal development training tool incl. Polymathic Training and Coaching Sessions, based around Neuroplastic Mental Acceleration (NMA): encompassing the eight steps to ascension, spread over 60 x 30 minute training sessions: Accept, Aware, Assess, Adapt, Aspire, Accelerate, Actualise, Ascend. The program is designed to provide mental well-being & acceleration by promoting fluid intelligence (the brain’s ability to learn new skills) though activating neuroplasticity - synaptogenisis & neurogenisis.
Security+ training course description A hands on course aimed at getting delegates successfully through the CompTia Security+ examination. What will you learn Explain general security concepts. Describe the security concepts in communications. Describe how to secure an infrastructure. Recognise the role of cryptography. Describe operational/organisational security. Security+ training course details Who will benefit: Those wishing to pass the Security+ exam. Prerequisites: TCP/IP foundation for engineers Duration 5 days Security+ training course contents General security concepts Non-essential services and protocols. Access control: MAC, DAC, RBAC. Security attacks: DOS, DDOS, back doors, spoofing, man in the middle, replay, hijacking, weak keys, social engineering, mathematical, password guessing, brute force, dictionary, software exploitation. Authentication: Kerberos, CHAP, certificates, usernames/ passwords, tokens, biometrics. Malicious code: Viruses, trojan horses, logic bombs, worms. Auditing, logging, scanning. Communication security Remote access: 802.1x, VPNs, L2TP, PPTP, IPsec, RADIUS, TACACS, SSH. Email: S/MIME, PGP, spam, hoaxes. Internet: SSL, TLS, HTTPS, IM, packet sniffing, privacy, Javascript, ActiveX, buffer overflows, cookies, signed applets, CGI, SMTP relay. LDAP. sftp, anon ftp, file sharing, sniffing, 8.3 names. Wireless: WTLS, 802.11, 802.11x, WEP/WAP. Infrastructure security Firewalls, routers, switches, wireless, modems, RAS, PBX, VPN, IDS, networking monitoring, workstations, servers, mobile devices. Media security: Coax, UTP, STP, fibre. Removable media. Topologies: Security zones, DMZ, Intranet, Extranet, VLANs, NAT, Tunnelling. IDS: Active/ passive, network/host based, honey pots, incident response. Security baselines: Hardening OS/NOS, networks and applications. Cryptography basics Integrity, confidentiality, access control, authentication, non-repudiation. Standards and protocols. Hashing, symmetric, asymmetric. PKI: Certificates, policies, practice statements, revocation, trust models. Key management and certificate lifecycles. Storage: h/w, s/w, private key protection. Escrow, expiration, revocation, suspension, recovery, destruction, key usage. Operational/Organisation security Physical security: Access control, social engineering, environment. Disaster recovery: Backups, secure disaster recovery plans. Business continuity: Utilities, high availability, backups. Security policies: AU, due care, privacy, separation of duties, need to know, password management, SLAs, disposal, destruction, HR policies. Incident response policy. Privilege management: Users, groups, roles, single sign on, centralised/decentralised. Auditing. Forensics: Chain of custody, preserving and collecting evidence. Identifying risks: Assets, risks, threats, vulnerabilities. Role of education/training. Security documentation.

AZ-500T00 Microsoft Azure Security Technologies
By Nexus Human
Duration 4 Days 24 CPD hours This course is intended for This course is for Azure Security Engineers who are planning to take the associated certification exam, or who are performing security tasks in their day-to-day job. This course would also be helpful to an engineer that wants to specialize in providing security for Azure-based digital platforms and play an integral role in protecting an organization's data. This course provides IT Security Professionals with the knowledge and skills needed to implement security controls, maintain an organization?s security posture, and identify and remediate security vulnerabilities. This course includes security for identity and access, platform protection, data and applications, and security operations. Prerequisites AZ-104T00 - Microsoft Azure Administrator Security best practices and industry security requirements such as defense in depth, least privileged access, role-based access control, multi-factor authentication, shared responsibility, and zero trust model. Be familiar with security protocols such as Virtual Private Networks (VPN), Internet Security Protocol (IPSec), Secure Socket Layer (SSL), disk and data encryption methods. Have some experience deploying Azure workloads. This course does not cover the basics of Azure administration, instead the course content builds on that knowledge by adding security specific information. Have experience with Windows and Linux operating systems and scripting languages. Course labs may use PowerShell and the CLI. 1 - Manage identities in Microsoft Entra ID Secure users in Microsoft Entra ID Secure groups in Microsoft Entra ID Recommend when to use external identities Secure external identities Implement Microsoft Entra Identity protection 2 - Manage authentication by using Microsoft Entra ID Configure Microsoft Entra Verified ID Implement multifactor authentication (MFA) Implement passwordless authentication Implement password protection Implement single sign-on (SSO) Integrate single sign-on (SSO) and identity providers Recommend and enforce modern authentication protocols 3 - Manage authorization by using Microsoft Entra ID Configure Azure role permissions for management groups, subscriptions, resource groups, and resources Assign built-in roles in Microsoft Entra ID Assign built-in roles in Azure Create and assign a custom role in Microsoft Entra ID Implement and manage Microsoft Entra Permissions Management Configure Microsoft Entra Privileged Identity Management Configure role management and access reviews by using Microsoft Entra Identity Governance Implement Conditional Access policies 4 - Manage application access in Microsoft Entra ID Manage access to enterprise applications in Microsoft Entra ID, including OAuth permission grants Manage app registrations in Microsoft Entra ID Configure app registration permission scopes Manage app registration permission consent Manage and use service principals Manage managed identities for Azure resources Recommend when to use and configure a Microsoft Entra Application Proxy, including authentication 5 - Plan and implement security for virtual networks Plan and implement Network Security Groups (NSGs) and Application Security Groups (ASGs) Plan and implement User-Defined Routes (UDRs) Plan and implement Virtual Network peering or gateway Plan and implement Virtual Wide Area Network, including secured virtual hub Secure VPN connectivity, including point-to-site and site-to-site Implement encryption over ExpressRoute Configure firewall settings on PaaS resources Monitor network security by using Network Watcher, including NSG flow logging 6 - Plan and implement security for private access to Azure resources Plan and implement virtual network Service Endpoints Plan and implement Private Endpoints Plan and implement Private Link services Plan and implement network integration for Azure App Service and Azure Functions Plan and implement network security configurations for an App Service Environment (ASE) Plan and implement network security configurations for an Azure SQL Managed Instance 7 - Plan and implement security for public access to Azure resources Plan and implement Transport Layer Security (TLS) to applications, including Azure App Service and API Management Plan, implement, and manage an Azure Firewall, Azure Firewall Manager and firewall policies Plan and implement an Azure Application Gateway Plan and implement an Azure Front Door, including Content Delivery Network (CDN) Plan and implement a Web Application Firewall (WAF) Recommend when to use Azure DDoS Protection Standard 8 - Plan and implement advanced security for compute Plan and implement remote access to public endpoints, Azure Bastion and just-in-time (JIT) virtual machine (VM) access Configure network isolation for Azure Kubernetes Service (AKS) Secure and monitor AKS Configure authentication for AKS Configure security for Azure Container Instances (ACIs) Configure security for Azure Container Apps (ACAs) Manage access to Azure Container Registry (ACR) Configure disk encryption, Azure Disk Encryption (ADE), encryption as host, and confidential disk encryption Recommend security configurations for Azure API Management 9 - Plan and implement security for storage Configure access control for storage accounts Manage life cycle for storage account access keys Select and configure an appropriate method for access to Azure Files Select and configure an appropriate method for access to Azure Blob Storage Select and configure an appropriate method for access to Azure Tables Select and configure an appropriate method for access to Azure Queues Select and configure appropriate methods for protecting against data security threats, including soft delete, backups, versioning, and immutable storage Configure Bring your own key (BYOK) Enable double encryption at the Azure Storage infrastructure level 10 - Plan and implement security for Azure SQL Database and Azure SQL Managed Instance Enable database authentication by using Microsoft Entra ID Enable and monitor database audit Identify use cases for the Microsoft Purview governance portal Implement data classification of sensitive information by using the Microsoft Purview governance portal Plan and implement dynamic mask Implement transparent data encryption? Recommend when to use Azure SQL Database Always Encrypted 11 - Plan, implement, and manage governance for security Create, assign, and interpret security policies and initiatives in Azure Policy Configure security settings by using Azure Blueprint Deploy secure infrastructures by using a landing zone Create and configure an Azure Key Vault Recommend when to use a dedicated Hardware Security Module (HSM) Configure access to Key Vault, including vault access policies and Azure Role Based Access Control Manage certificates, secrets, and keys Configure key rotation Configure backup and recovery of certificates, secrets, and keys 12 - Manage security posture by using Microsoft Defender for Cloud Implement Microsoft Defender for Cloud Identify and remediate security risks by using the Microsoft Defender for Cloud Secure Score and Inventory Assess compliance against security frameworks and Microsoft Defender for Cloud Add industry and regulatory standards to Microsoft Defender for Cloud Add custom initiatives to Microsoft Defender for Cloud Connect hybrid cloud and multicloud environments to Microsoft Defender for Cloud Identify and monitor external assets by using Microsoft Defender External Attack Surface Management 13 - Configure and manage threat protection by using Microsoft Defender for Cloud Enable workload protection services in Microsoft Defender for Cloud, including Microsoft Defender for Storage, Databases, Containers, App Service, Key Vault, Resource Manager, and DNS Configure Microsoft Defender for Servers Configure Microsoft Defender for Azure SQL Database Manage and respond to security alerts in Microsoft Defender for Cloud Configure workflow automation by using Microsoft Defender for Cloud Evaluate vulnerability scans from Microsoft Defender for Server 14 - Configure and manage security monitoring and automation solutions Monitor security events by using Azure Monitor Configure data connectors in Microsoft Sentinel Create and customize analytics rules in Microsoft Sentinel Configure automation in Microsoft Sentinel Additional course details: Nexus Humans AZ-500T00 Microsoft Azure Security Technologies training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the AZ-500T00 Microsoft Azure Security Technologies course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

Cisco Deploying Cisco SD-Access (ENSDA)
By Nexus Human
Duration 4 Days 24 CPD hours This course is intended for The primary audience for this course is as follows: System Engineers Network Engineers Technical Architects Technical Support Personnel Channel Partners Resellers Overview Upon completing the course, the learner will be able to meet these overall objectives: Describe Cisco SD-Access and how it relates to Cisco DNA Orchestrate a Cisco SD-Access solution using the Cisco DNA Center⢠orchestration platform Use the Network Data Platform to demonstrate the assurance and analytics capabilities of SD-Access The Deploying Cisco SD-Access (ENSDA) v1.0 course is an instructor-led, lab based, hands-on course that teaches students how to successfully deploy the Cisco© Software-Defined Access (SD-Access) solution within their enterprise networks. The course discusses how Cisco SD-Access fits into the Cisco Digital Network Architecture (Cisco DNA?). It covers SD-Access fundamentals, provisioning, policies, wireless integration, border operations, and migration strategies. Module 1: Cisco SD-Access Overview Lesson 1: Exploring Cisco SD-Access Lesson 2: Describing the Cisco SD-Access Architecture Lesson 3: Exploring Cisco DNA Center Lesson 4: Configuring Underlay Automation Module 2: Cisco SD-Access Implementation Lesson 1: ISE Integration in DNA Center Lesson 2: Policy Provisioning Basics Lesson 3: Navigating and Managing the Policy Application Workflows Module 3: Cisco SD-Access Border Operations Lesson 1: Cisco SD-Access Deployment Models Lesson 2: Connecting the Fabric to External Domains Module 4: Wireless Integration Orchestration Lesson 1: Integrating Wireless with the Cisco SD-Access Solution Lesson 2: Workflow of Cisco SD-Access Wireless Lesson 3: Cisco SD-Access Wireless Network Design Lesson 4: Cisco SD-Access Wireless Basic Operation Module 5: Cisco SD-Access Assurance and Migration Lesson 1: Cisco Network Data Platform Lesson 2: Cisco SD-Access Migration Strategies

Concise Cisco routers course description A fast paced practical hands on introduction to Cisco routers concentrating on basic product knowledge needed for the real world. Starts with the basics of routing through configuring static routes, RIP, OSPF, and EIGRP ending with access lists. Hands on sessions follow all the major chapters with a major practical at the end to reinforce all that was learnt in the course. What will you learn Use the Cisco setup script. Use the Cisco command line. Perform basic troubleshooting. Configure - Interfaces - RIP, IGRP - OSPF, EIGRP Concise Cisco routers course details Who will benefit: Anyone who will be working with Cisco routers. In particular: Network Administrators, Field engineers, Network support personnel Prerequisites: None, although a knowledge of the TCP/IP protocols would be advantageous. Duration 3 days Concise Cisco routers course content Basics of routing What are routers? Network protocols, Routing protocols. The Cisco routers Router models, The IOS, DRAM, SRAM, NVRAM, Flash, ROM and boot flash. Getting started Accessing the router, installing a Cisco, using the setup script. The command line interface User and privilege modes, online help show, debug, basic troubleshooting Configuring Ciscos The configuration editor, Global, major and sub commands, enable, secret and other passwords, telnet. Miscellaneous exercises Buffered logging, web access, CDP⦠Subnetting IP addressing rules. The need for subnetting, subnet masks, Calculating network numbers. Configuring Interfaces Basics, Ethernet, Serial lines, PPP, DCE, loopback interfaces. Static routes Why use static routes? Configuring static routes, default routes. Configuring RIP and IGRP How they work, configuration, troubleshooting. OSPF Configuration and troubleshooting. EIGRP Configuration and troubleshooting. Housekeeping Configuration management, offline editing and TFTP usage. Cisco boot sequence, IOS upgrades. Bypassing Cisco passwords. Access lists What are access lists? General rules, basic and extended IP access lists. Putting it all together A series of exercises based around, installs, adds, moves, changes, upgrades and troubleshootin

Reiki Master Practitioner Level 3 Online Course
By Margaret Cook - Learn More About Reiki
I am a Reiki Teacher in Manchester and one of the few traditionally trained Reiki Masters in the UK who have been trained by international best-selling Reiki author Penelope Quest. My teaching methods use traditional Reiki techniques perfected over many years and you can be assured of my support during and after your course. I teach all three levels of Reiki courses, level 1 reiki. level 2 reiki and reiki master level 3

ADO.NET training course description This ADO.net training course is designed to enable developers to use the toolset provided with.NET for data access including ADO.net objects, data controls, designers and interoperability with earlier ADO objects. The course is applicable for those using C# or VB.NET with ADO.NET What will you learn Retrieve and manipulate data using Microsoft's ADO.NET library. Work with the ADO.NET object model. Update data, including handling stored procedures, parameters, and return value. Search, sort and filter data. Leverage the power of XML. ADO.NET training course details Who will benefit: Programmers working with ADO.Net. Prerequisites: Effective programming with VB.NET or Concise introduction to C# Duration 2 days ADO.NET training course contents Introducing ADO.Net Traditional Data Access Architecture. ADO.Net Disconnected Data Access Architecture. Different components of ADO.Net. A review of basic SQL queries SQL SELECT Statement. SQL INSERT Statement. SQL UPDATE Statement. SQL DELETE Statement. Common data access tasks with ADO.Net Accessing Data using ADO.Net. Defining the connection string. Defining a Connection. Defining the command or command string. Defining the Data Adapter. Creating and filling the DataSet. A Demonstration Application The Interface. Loading the table. Filling the controls on the Form. Navigating through the records. Updating Data Steps for updating the table. Building the Application. Loading the table and displaying data in the form's controls. Initialising Commands. Adding Parameters to the commands. The ToggleControls() method of our application. Editing (or Updating) Records. Event Handler for the Save Button. Event Handler for the Cancel Button. Inserting Records. Deleting a Record. Using Stored Procedures Sample Stored Procedures. UPDATE Stored Procedure. INSERT Stored Procedure. DELETE Stored Procedure. SELECT Stored Procedure. Using Stored Procedures with ADO.Net.

