- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
1735 Courses delivered Live Online
CertNexus Certified Cyber Secure Coder (CSC-210)
By Nexus Human
Duration 3 Days 18 CPD hours This course is intended for This course is designed for software developers, testers, and architects who design and develop software in various programming languages and platforms, including desktop, web, cloud, and mobile, and who want to improve their ability to deliver software that is of high quality, particularly regarding security and privacy. This course is also designed for students who are seeking the CertNexus Cyber Secure Coder (CSC) Exam CSC-210 certification Overview In this course, you will employ best practices in software development to develop secure software.You will: Identify the need for security in your software projects. Eliminate vulnerabilities within software. Use a Security by Design approach to design a secure architecture for your software. Implement common protections to protect users and data. Apply various testing methods to find and correct security defects in your software. Maintain deployed software to ensure ongoing security... The stakes for software security are very high, and yet many development teams deal with software security only after the code has been developed and the software is being prepared for delivery. As with any aspect of software quality, to ensure successful implementation, security and privacy issues should be managed throughout the entire software development lifecycle. This course presents an approach for dealing with security and privacy throughout the entire software development lifecycle. You will learn about vulnerabilities that undermine security, and how to identify and remediate them in your own projects. You will learn general strategies for dealing with security defects and misconfiguration, how to design software to deal with the human element in security, and how to incorporate security into all phases of development. Identifying the Need for Security in Your Software Projects Identify Security Requirements and Expectations Identify Factors That Undermine Software Security Find Vulnerabilities in Your Software Gather Intelligence on Vulnerabilities and Exploits Handling Vulnerabilities Handle Vulnerabilities Due to Software Defects and Misconfiguration Handle Vulnerabilities Due to Human Factors Handle Vulnerabilities Due to Process Shortcomings Designing for Security Apply General Principles for Secure Design Design Software to Counter Specific Threats Developing Secure Code Follow Best Practices for Secure Coding Prevent Platform Vulnerabilities Prevent Privacy Vulnerabilities Implementing Common Protections Limit Access Using Login and User Roles Protect Data in Transit and At Rest Implement Error Handling and Logging Protect Sensitive Data and Functions Protect Database Access Testing Software Security Perform Security Testing Analyze Code to find Security Problems Use Automated Testing Tools to Find Security Problems Maintaining Security in Deployed Software Monitor and Log Applications to Support Security Maintain Security after Deployment

FORENSIC ANALYSIS BOOTCAMP
By Behind The Balance Sheet
The Forensic Analysis Bootcamp is an 8-week deep-dive into forensic equity analysis, featuring a 90-minute Zoom workshop each week. The content includes extensive use of real-life case studies and covers stocks spanning a wide range of sectors and regions. You will learn how companies manipulate expenses and inflate profits, how to spot balance sheet issues, weaknesses of the cash flow statement and issues and more.
Certified TIA-942 Design Consultant (CTDC)
By Nexus Human
Duration 3 Days 18 CPD hours This course is intended for Participants must possess a valid data centre training certificate such as CDCP or any other approved equivalent. Please submit a copy of your certificate for verification upon registration for the CTDC course. Overview After completion of the course the participant will be able to:1. Learn to properly comprehend and apply the ANSI/TIA-942 Standard requirements and guidelines2. Understand the proper intent of the ANSI/TIA-942 Standard to avoid both over- and/or under-investment3. Align the selection of redundancy levels and infrastructure investments to the business requirements.4. Understand the criteria and requirements for a high-availability data centre design and how to effectively establish the data centre from the perspective of the ANSI/TIA-942 Standard5. Understand how the ANSI/TIA-942 Standard relates to various worldwide standards This course, the participant will learn how to design an ANSI/TIA-942 compliant data centre. It will provide a clear understanding of the requirements of the ANSI/TIA-942 Standard and possible implementation variations. Introduction to Data Centre Facilities About the ANSI/TIA-942 Life of the ANSI/TIA-942 Standard Relation to other standards Architectural Electrical Mechanical Telecommunication Areas under scope High level redundancy definitions Redundancy options (N, N+1 etc.) Fault tolerant Concurrent maintainability Compartmentalisation Examples of redundancy levels Data Centre Space PlanningData Centre TopologiesRecommendations for Energy EfficiencyArchitectural Site selection Parking Multi-tenant building Building construction Vapor barrier Roofing Floor loading Raised flooring Suspended/drop ceiling Hanging load Seismic Building Security & Safety Security CCTV Staffing Bullet/ballistic proofing Lighting Safety - Signage Building and Room Access Security checkpoints Entry lobby Doors and windows Exit corridors Shipping and receiving areas Room/Area Design Requirements Administrative offices Security offce Operations centre Restroom and break room UPS/Battery rooms Generator and fuel storage area Computer room Electrical Utility power - Substation - Feed requirements - Self-generation HT/HV switch gear Generator and fuel supply LT/LV switch gear - ATS - Alternatives to ATS UPS and batteries PDU STS Grounding Surge protection EPO Central power monitoring Load banks Testing Equipment maintenance - Preventive maintenance - Facility training programs Mechanical Environmental design - Temperature and humidity requirements - Contamination - Sources - Clean air - Pressurisation - Radio sources - Vibration - Water ingress Water cooled systems - Heat rejection - Chilled water system - Condenser water? - Make up water Air cooled systems HVAC control systems Plumbing - Pipe routing Fire suppression Water leak detection Telecommunications Network topology Redundancy level design Media and connectors Cabling pathways Detailed cabling design considerations Administration and labeling Cable testing Data centre fabrics Exam: Certified TIA-942 Design Consultant Actual course outline may vary depending on offering center. Contact your sales representative for more information.

BOHS P901 Online - Management and control of building hot and cold water services
By Airborne Environmental Consultants Ltd
P901 - Management and control of building hot and cold water services is there to provide background and an overview of the risk of Legionella infection and how it can be controlled in domestic type hot and cold water systems. (This course is also a pre-requirement before undertaking course P903 - Management and Control of Evaporative Cooling Systems and other High Risk Industrial Systems or P904 - Management and Control in Leisure, Display, Therapy and other Non-Industrial Systems.)

BOHS P900 Online - Maintenance and testing of control measures for domestic hot and cold water systems
By Airborne Environmental Consultants Ltd
P900 - Maintenance and testing of control measures for domestic hot and cold water systems is there to provide the basis of competence of operatives undertaking the operation and monitoring of domestic hot and cold water systems in buildings. The objective is to enable the candidates to identify the risks posed by legionella bacteria and understand how to manage the risks in domestic water systems, to a standard which minimises the risk of exposure and ill health.

CCNA training course description The Implementing and Administering Cisco Solutions (CCNA) course gives you a broad range of fundamental knowledge for all IT careers. Through a combination of lecture, hands-on labs, and self-study, you will learn how to install, operate, configure, and verify basic IPv4 and IPv6 networks. The course covers configuring network components such as switches, routers, and wireless LAN controllers; managing network devices; and identifying basic security threats. It also gives a foundation in network programmability, and software-defined networking What will you learn Install, configure, and operate a small to medium sized network Gain a foundation in the essentials of networking, security, and automation Prepare for the 200-301 CCNA exam, which earns CCNA certification CCNA training course details Who will benefit: Network support help desk technicians involved in the basic installation, operation, and verification of Cisco networks. Anyone seeking CCNA certification. Prerequisites: Introduction to Data communications & networking Duration 5 days CCNA training course content After taking this course, you should be able to: Identify the components of a computer network and describe their basic characteristics. Understand the model of host-to-host communication. Describe the Cisco IOS software. Describe LANs and the role of switches within LANs. Describe Ethernet and describe the operation of switches. Install a switch and perform the initial configuration. Describe the TCP/IP Internet layer, IPv4, its addressing scheme, and subnetting. Describe the TCP/IP Transport and Application layers Explore functions of routing. Implement basic configuration on a Cisco router. Explain host-to-host comms across switches and routers. Identify and resolve common switched network issues and common problems associated with IPv4 addressing. Describe IPv6 main features and addresses, and configure and verify basic IPv6 connectivity. Describe static routing. Describe, implement, and verify VLANs and trunks. Describe inter VLAN routing. Explain the basics of dynamic routing protocols and describe components and terms of OSPF. Explain how STP and RSTP work. Configure link aggregation using EtherChannel. Describe the purpose of Layer 3 redundancy protocols. Describe basic WAN and VPN concepts. Describe the operation of access control lists (ACLs) and their applications in the network. Configure Internet access using DHCP clients and explain and configure NAT on Cisco routers. Describe basic QoS concepts. Describe the concepts of wireless networks, which types of wireless networks can be built, and how to use Wireless LAN Controllers (WLCs). Describe network and device architectures, introduce virtualization, network programmability and SDN and describe smart network management solutions such as Cisco DNA Centerâ¢, SD-Access, and SD-WAN. Configure basic IOS system monitoring tools. Describe the management of Cisco devices. Describe the current security threat landscape. Describe threat defence technologies. Implement a basic security configuration of the device management plane. Implement basic steps to harden network devices. Detailed course outline Exploring the Functions of Networking. The Host-to-Host Communications Model. Operating Cisco IOS Software. Introducing LANs. Exploring the TCP/IP Link Layer. Starting a Switch. The TCP/IP IP layer, IPv4 Addressing, and Subnets. The TCP/IP Transport Layer and Application Layer. Exploring the Functions of Routing. Configuring a Cisco Router. Exploring the Packet Delivery Process. Troubleshooting a Simple Network. Introducing Basic IPv6. Configuring Static Routing. Implementing VLANs and Trunks. Routing Between VLANs. Introducing OSPF. Redundant Switched Topologies with EtherChannel. Explaining Basics of ACL. Enabling Internet Connectivity. Explaining the Evolution of Intelligent Networks. Introducing System Monitoring. Managing Cisco Devices. Securing Administrative Access. Implementing Device Hardening. Self-Study: Building Redundant Switched Topologies. Exploring Layer 3 Redundancy. Introducing WAN Technologies. Introducing QoS. Explaining Wireless Fundamentals. Introducing Architectures and Virtualization. Examining the Security Threat Landscape. Threat Defense Technologies.

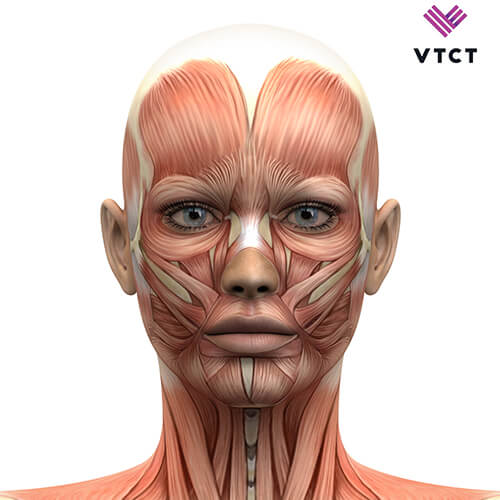
This Level 3 anatomy & physiology (or A & P as it is commonly known) is a perfect course for those who are looking to build upon their existing knowledge of skincare, but is also open to complete beginners. Please confirm dates and availability with us prior to purchasing Who Is This Course Suitable For? Pre-requisites None required. Course Content You will cover: Skin, nails and hair The skeletal system The muscular system The nervous system The endocrine system The respiratory system The cardiovascular system The lymphatic system The digestive system You will have 1 Assignment and 1 Exam Course Duration & Cost No date required, please go ahead and BOOK, we will email across all relevant home studying information directly to your email address You have a minimum of 6 weeks to study for the exam and a maximum of one year This course is ALL home studying You will need inform us when you feel you are ready to sit your exam, we can take a look at a few assessment dates for you at our Leicester centre. Remote (Webcam) Exams If you cannot attend our assessment Centre we can arrange for you to take your final assessment remotely via webcam. Dates for remote exams are flexible and can be booked in with our team when you have completed your online coursework. £330 Categories: ofqual
The BCS Foundation Certificate in Business Analysis is a foundation- level certification that provides a broad understanding of business analysis principles and techniques. It is offered by the British Computer Society (BCS), a professional association for IT professionals.

Safeguarding for Lawyers Course
By DG Legal
This training is for lawyers who may come into contact with vulnerable people through their work. In particular, it is aimed at those who hold legal aid contracts and must meet the requirements of the Specialist Quality Mark (SQM) standard in respect of safeguarding. Everyone has the right to be kept safe from harm, abuse or neglect. We all have obligations to ensure that vulnerable people are protected and that we have appropriate procedures in place to ensure that abuse is identified and reported. We will help you to understand the following; What is safeguarding? The different types of abuse Example signs of abuse, harm and neglect What action should be taken if abuse is suspected The SQM requirements What a Safeguarding Policy should include Target Audience The online course is suitable for staff of all levels, from support staff to senior partners and is aimed at firms maintaining or wishing to obtain the Specialist Quality Mark. Resources Comprehensive and up to date course notes will be provided to all delegates which may be useful for ongoing reference or cascade training. Please note a recording of the course will not be made available. Speaker Amie Higgins, Consultant, DG Legal Amie is a Senior Solicitor, qualified under the Law Society’s Immigration & Asylum Accreditation Scheme (IAAS) as an Advanced Caseworker and Supervisor. Amie specialises in all aspects of Immigration, Asylum and Human Rights work, with a specialism in human trafficking/modern slavery cases and working with vulnerable clients. Amie is an experienced trainer, delivering a range of training on both legal and practice management topics.

Red Hat Application Development I: Programming in Java EE with exam (AD184)
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for This course is designed for Java developers who want to learn more about the specifications that comprise the world of Java Enterprise Edition (Java EE). Overview As a result of attending this course, you should be able to describe most of the specifications in Java EE 7 and create a component with each specification. You will be able to convert a Java SE program into a multi-tiered Java EE application. You should be able to demonstrate these skills: Describe the architecture of multi-tiered Java EE applications. Package Java EE applications and deploy to Red Hat JBoss Enterprise Application Platform with various tools. Create an Enterprise Java Bean instance. Manage the persistence of data using Java Persistence API. Create a web service using JAX-RS. Properly apply context scopes to beans and inject resources into Java Beans. Store and retrieve messages using the Java Messaging Service. Secure a Java EE application. Red Hat Application Development I: Programming in Java EE with exam (AD184) exposes experienced Java Standard Edition (Java SE) developers to the world of Java Enterprise Edition (Java EE). This course is based on Red Hat© Enterprise Application Platform 7.0. This course is a combination of Red Hat Application Development I: Programming in Java EE (AD183) and Red Hat Certified Enterprise Application Developer Exam (EX183). In this course, you will learn about the various specifications that make up Java EE. Through hands-on labs, you will transform a simple Java SE command line application into a multi-tiered enterprise application using various Java EE specifications, including Enterprise Java Beans, Java Persistence API, Java Messaging Service, JAX-RS for REST services, Contexts and Dependency Injection (CDI), and JAAS for securing the application. Transition to multi-tiered applications Describe Java EE features and distinguish between Java EE and Java SE applications. Package and deploying applications to an application server Describe the architecture of a Java EE application server, package an application, and deploy the application to an EAP server. Create Enterprise Java Beans Develop Enterprise Java Beans, including message-driven beans. Manage persistence Create persistence entities with validations. Manage entity relationships Define and manage JPA entity relationships. Create REST services Create REST APIs using the JAX-RS specification. Implement Contexts and Dependency Injection Describe typical use cases for using CDI and successfully implement it in an application. Create messaging applications with JMS Create messaging clients that send and receive messages using the JMS API. Secure Java EE applications Use JAAS to secure a Java EE application. Comprehensive review of Red Hat JBoss Development I: Java EE Demonstrate proficiency of the knowledge and skills obtained during the course. Additional course details: Nexus Humans Red Hat Application Development I: Programming in Java EE with exam (AD184) training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the Red Hat Application Development I: Programming in Java EE with exam (AD184) course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.
