- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
362 Courses delivered Live Online
Hardening Cisco devices training course description A hands on course focusing on how to lock down Cisco IOS routers and switches. What will you learn Harden Cisco devices. Hardening Cisco devices training course details Who will benefit: Technical network staff. Technical security staff. Prerequisites: TCP/IP foundation for engineers. Duration 5 days Hardening Cisco devices training course content Introduction Router security, Switch security, Cisco IOS, IOS versions, Cisco advisories, the management plane, control plane, data plane. Hands on Checking IOS versions and advisories. Access control Infrastructure ACLs, Transit ACLs. Hands on Restricting access to the device, Filtering data traffic. Management plane: Securing operations Passwords, privilege levels, AAA, TACACS+, RADIUS. Hands on Password management. Management plane: Other general hardening Logging best practices, secure protocols, encrypting management sessions, configuration management. Hands on Hardening the management plane. Control plane Disabling reception and transmission of certain messages, Limiting CPU impact of control plane traffic, securing routing protocols. Hands on Hardening the control plane. Data plane Transit ACLs, disabling unused services, disabling unnecessary protocols, anti spoofing, limiting CPU impact of data plane traffic, identifying and tracing traffic, Netflow, VLANs, port security. Hands on hardening the data plane.

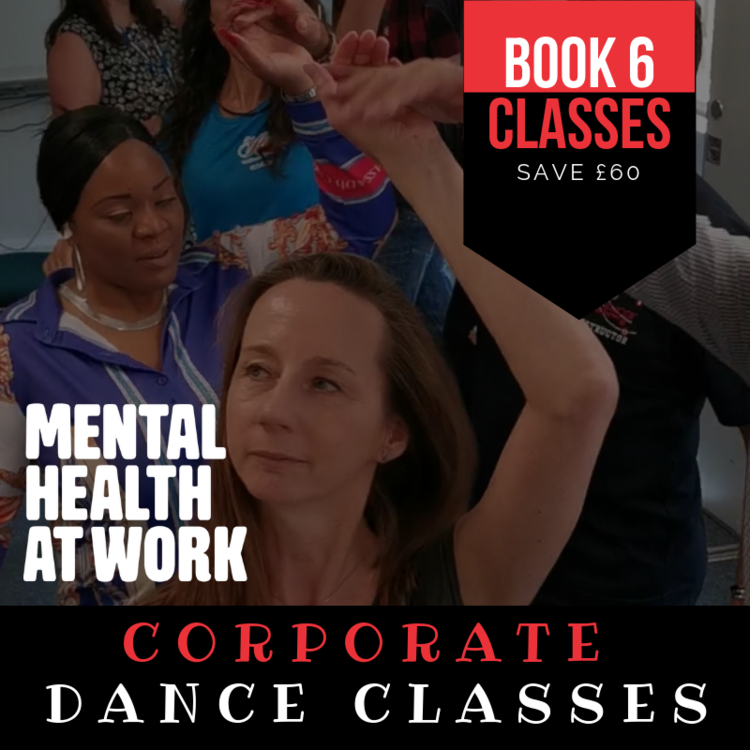
HOW DANCING CAN IMPROVE YOUR MENTAL AND PHYSICAL HEALTH Move your body to your favourite tunes – it’s the ultimate feel-good exercise and has some surprising effects on both the body and mind Music and dance have been fundamental parts of the human experience for thousands of years. No matter what your favourite tune may be, music can have a huge effect on your wellbeing – Charles Darwin even thought that our ability to make and understand rhythmic beats worked as an early form of communication. Whether or not we still share messages through music, we all know that it can change our mood and studies have shown that we share a natural sense of rhythm (no matter how much you might protest). Dance is therefore a natural outlet, and one which can do a lot to make us feel good. Club Azucar offers corporate dance packages for the workplace in order for your organisation (Companies, Institutions & Schools) not only function at its best, but to be happy and healthy in life. These are the expected benefits for the individual employee which have been also confirmed by the participants: Physical Health: Salsa/Zumba or any Latin Dance Classes improves mobility, coordination / motor skills and fitness level.while being a low-impact exercise which includes people of all ages, abilities and fitness levels Mental Health: Dancing requires full concentration so for one hour away from their desk ,participants will experience reduced stress levels, , feel refreshed and more alert and able to concentrate better following the lesson Music in combination with physical exercise has an uplifting effect through the release of endorphins and dopamine in the body & brain Learning a new skill is proven to train your brain, contribute to prevention of dementia and give the confidence to face new tasks and challenges in other areas of work and life The patience and encouragement of the teachers has furthered this new confidence and sense of achievement and contributed to participants’ belief in themselves and their ability to take themselves out of their “comfort zones” and take on new challenges Getting to know each other in a social rather than work context and learning a new skill together, dancing and laughing together, gives participants a sense of belonging and furthers team buildingDo you want more proof? Get involved and hire us!!! Booking Terms & Conditions 1. The above prices are only for Greater London 2. Fees are non refundable 3. Courses are subject to availability from both parties 4. Train, plane. petrol, or any sort of transport fares are to be refunded. 5. Cancellation must be before 24 hours every class
SC-200T00 Microsoft Security Operations Analyst
By Nexus Human
Duration 4 Days 24 CPD hours This course is intended for The Microsoft Security Operations Analyst collaborates with organizational stakeholders to secure information technology systems for the organization. Their goal is to reduce organizational risk by rapidly remediating active attacks in the environment, advising on improvements to threat protection practices, and referring violations of organizational policies to appropriate stakeholders. Responsibilities include threat management, monitoring, and response by using a variety of security solutions across their environment. The role primarily investigates, responds to, and hunts for threats using Microsoft Sentinel, Microsoft Defender for Cloud, Microsoft 365 Defender, and third-party security products. Since the Security Operations Analyst consumes the operational output of these tools, they are also a critical stakeholder in the configuration and deployment of these technologies. Learn how to investigate, respond to, and hunt for threats using Microsoft Sentinel, Microsoft Defender for Cloud, and Microsoft 365 Defender. In this course you will learn how to mitigate cyberthreats using these technologies. Specifically, you will configure and use Microsoft Sentinel as well as utilize Kusto Query Language (KQL) to perform detection, analysis, and reporting. The course was designed for people who work in a Security Operations job role and helps learners prepare for the exam SC-200: Microsoft Security Operations Analyst. Prerequisites Basic understanding of Microsoft 365 Fundamental understanding of Microsoft security, compliance, and identity products Intermediate understanding of Windows 10 Familiarity with Azure services, specifically Azure SQL Database and Azure Storage Familiarity with Azure virtual machines and virtual networking Basic understanding of scripting concepts. 1 - Introduction to Microsoft 365 threat protection Explore Extended Detection & Response (XDR) response use cases Understand Microsoft Defender XDR in a Security Operations Center (SOC) Explore Microsoft Security Graph Investigate security incidents in Microsoft Defender XDR 2 - Mitigate incidents using Microsoft 365 Defender Use the Microsoft Defender portal Manage incidents Investigate incidents Manage and investigate alerts Manage automated investigations Use the action center Explore advanced hunting Investigate Microsoft Entra sign-in logs Understand Microsoft Secure Score Analyze threat analytics Analyze reports Configure the Microsoft Defender portal 3 - Protect your identities with Microsoft Entra ID Protection Microsoft Entra ID Protection overview Detect risks with Microsoft Entra ID Protection policies Investigate and remediate risks detected by Microsoft Entra ID Protection 4 - Remediate risks with Microsoft Defender for Office 365 Automate, investigate, and remediate Configure, protect, and detect Simulate attacks 5 - Safeguard your environment with Microsoft Defender for Identity Configure Microsoft Defender for Identity sensors Review compromised accounts or data Integrate with other Microsoft tools 6 - Secure your cloud apps and services with Microsoft Defender for Cloud Apps Understand the Defender for Cloud Apps Framework Explore your cloud apps with Cloud Discovery Protect your data and apps with Conditional Access App Control Walk through discovery and access control with Microsoft Defender for Cloud Apps Classify and protect sensitive information Detect Threats 7 - Respond to data loss prevention alerts using Microsoft 365 Describe data loss prevention alerts Investigate data loss prevention alerts in Microsoft Purview Investigate data loss prevention alerts in Microsoft Defender for Cloud Apps 8 - Manage insider risk in Microsoft Purview Insider risk management overview Create and manage insider risk policies Investigate insider risk alerts Take action on insider risk alerts through cases Manage insider risk management forensic evidence Create insider risk management notice templates 9 - Investigate threats by using audit features in Microsoft Defender XDR and Microsoft Purview Standard Explore Microsoft Purview Audit solutions Implement Microsoft Purview Audit (Standard) Start recording activity in the Unified Audit Log Search the Unified Audit Log (UAL) Export, configure, and view audit log records Use audit log searching to investigate common support issues 10 - Investigate threats using audit in Microsoft Defender XDR and Microsoft Purview (Premium) Explore Microsoft Purview Audit (Premium) Implement Microsoft Purview Audit (Premium) Manage audit log retention policies Investigate compromised email accounts using Purview Audit (Premium) 11 - Investigate threats with Content search in Microsoft Purview Explore Microsoft Purview eDiscovery solutions Create a content search View the search results and statistics Export the search results and search report Configure search permissions filtering Search for and delete email messages 12 - Protect against threats with Microsoft Defender for Endpoint Practice security administration Hunt threats within your network 13 - Deploy the Microsoft Defender for Endpoint environment Create your environment Understand operating systems compatibility and features Onboard devices Manage access Create and manage roles for role-based access control Configure device groups Configure environment advanced features 14 - Implement Windows security enhancements with Microsoft Defender for Endpoint Understand attack surface reduction Enable attack surface reduction rules 15 - Perform device investigations in Microsoft Defender for Endpoint Use the device inventory list Investigate the device Use behavioral blocking Detect devices with device discovery 16 - Perform actions on a device using Microsoft Defender for Endpoint Explain device actions Run Microsoft Defender antivirus scan on devices Collect investigation package from devices Initiate live response session 17 - Perform evidence and entities investigations using Microsoft Defender for Endpoint Investigate a file Investigate a user account Investigate an IP address Investigate a domain 18 - Configure and manage automation using Microsoft Defender for Endpoint Configure advanced features Manage automation upload and folder settings Configure automated investigation and remediation capabilities Block at risk devices 19 - Configure for alerts and detections in Microsoft Defender for Endpoint Configure advanced features Configure alert notifications Manage alert suppression Manage indicators 20 - Utilize Vulnerability Management in Microsoft Defender for Endpoint Understand vulnerability management Explore vulnerabilities on your devices Manage remediation 21 - Plan for cloud workload protections using Microsoft Defender for Cloud Explain Microsoft Defender for Cloud Describe Microsoft Defender for Cloud workload protections Enable Microsoft Defender for Cloud 22 - Connect Azure assets to Microsoft Defender for Cloud Explore and manage your resources with asset inventory Configure auto provisioning Manual log analytics agent provisioning 23 - Connect non-Azure resources to Microsoft Defender for Cloud Protect non-Azure resources Connect non-Azure machines Connect your AWS accounts Connect your GCP accounts 24 - Manage your cloud security posture management? Explore Secure Score Explore Recommendations Measure and enforce regulatory compliance Understand Workbooks 25 - Explain cloud workload protections in Microsoft Defender for Cloud Understand Microsoft Defender for servers Understand Microsoft Defender for App Service Understand Microsoft Defender for Storage Understand Microsoft Defender for SQL Understand Microsoft Defender for open-source databases Understand Microsoft Defender for Key Vault Understand Microsoft Defender for Resource Manager Understand Microsoft Defender for DNS Understand Microsoft Defender for Containers Understand Microsoft Defender additional protections 26 - Remediate security alerts using Microsoft Defender for Cloud Understand security alerts Remediate alerts and automate responses Suppress alerts from Defender for Cloud Generate threat intelligence reports Respond to alerts from Azure resources 27 - Construct KQL statements for Microsoft Sentinel Understand the Kusto Query Language statement structure Use the search operator Use the where operator Use the let statement Use the extend operator Use the order by operator Use the project operators 28 - Analyze query results using KQL Use the summarize operator Use the summarize operator to filter results Use the summarize operator to prepare data Use the render operator to create visualizations 29 - Build multi-table statements using KQL Use the union operator Use the join operator 30 - Work with data in Microsoft Sentinel using Kusto Query Language Extract data from unstructured string fields Extract data from structured string data Integrate external data Create parsers with functions 31 - Introduction to Microsoft Sentinel What is Microsoft Sentinel? How Microsoft Sentinel works When to use Microsoft Sentinel 32 - Create and manage Microsoft Sentinel workspaces Plan for the Microsoft Sentinel workspace Create a Microsoft Sentinel workspace Manage workspaces across tenants using Azure Lighthouse Understand Microsoft Sentinel permissions and roles Manage Microsoft Sentinel settings Configure logs 33 - Query logs in Microsoft Sentinel Query logs in the logs page Understand Microsoft Sentinel tables Understand common tables Understand Microsoft Defender XDR tables 34 - Use watchlists in Microsoft Sentinel Plan for watchlists Create a watchlist Manage watchlists 35 - Utilize threat intelligence in Microsoft Sentinel Define threat intelligence Manage your threat indicators View your threat indicators with KQL 36 - Connect data to Microsoft Sentinel using data connectors Ingest log data with data connectors Understand data connector providers View connected hosts 37 - Connect Microsoft services to Microsoft Sentinel Plan for Microsoft services connectors Connect the Microsoft Office 365 connector Connect the Microsoft Entra connector Connect the Microsoft Entra ID Protection connector Connect the Azure Activity connector 38 - Connect Microsoft Defender XDR to Microsoft Sentinel Plan for Microsoft Defender XDR connectors Connect the Microsoft Defender XDR connector Connect Microsoft Defender for Cloud connector Connect Microsoft Defender for IoT Connect Microsoft Defender legacy connectors 39 - Connect Windows hosts to Microsoft Sentinel Plan for Windows hosts security events connector Connect using the Windows Security Events via AMA Connector Connect using the Security Events via Legacy Agent Connector Collect Sysmon event logs 40 - Connect Common Event Format logs to Microsoft Sentinel Plan for Common Event Format connector Connect your external solution using the Common Event Format connector 41 - Connect syslog data sources to Microsoft Sentinel Plan for syslog data collection Collect data from Linux-based sources using syslog Configure the Data Collection Rule for Syslog Data Sources Parse syslog data with KQL 42 - Connect threat indicators to Microsoft Sentinel Plan for threat intelligence connectors Connect the threat intelligence TAXII connector Connect the threat intelligence platforms connector View your threat indicators with KQL 43 - Threat detection with Microsoft Sentinel analytics What is Microsoft Sentinel Analytics? Types of analytics rules Create an analytics rule from templates Create an analytics rule from wizard Manage analytics rules 44 - Automation in Microsoft Sentinel Understand automation options Create automation rules 45 - Threat response with Microsoft Sentinel playbooks What are Microsoft Sentinel playbooks? Trigger a playbook in real-time Run playbooks on demand 46 - Security incident management in Microsoft Sentinel Understand incidents Incident evidence and entities Incident management 47 - Identify threats with Behavioral Analytics Understand behavioral analytics Explore entities Display entity behavior information Use Anomaly detection analytical rule templates 48 - Data normalization in Microsoft Sentinel Understand data normalization Use ASIM Parsers Understand parameterized KQL functions Create an ASIM Parser Configure Azure Monitor Data Collection Rules 49 - Query, visualize, and monitor data in Microsoft Sentinel Monitor and visualize data Query data using Kusto Query Language Use default Microsoft Sentinel Workbooks Create a new Microsoft Sentinel Workbook 50 - Manage content in Microsoft Sentinel Use solutions from the content hub Use repositories for deployment 51 - Explain threat hunting concepts in Microsoft Sentinel Understand cybersecurity threat hunts Develop a hypothesis Explore MITRE ATT&CK 52 - Threat hunting with Microsoft Sentinel Explore creation and management of threat-hunting queries Save key findings with bookmarks Observe threats over time with livestream 53 - Use Search jobs in Microsoft Sentinel Hunt with a Search Job Restore historical data 54 - Hunt for threats using notebooks in Microsoft Sentinel Access Azure Sentinel data with external tools Hunt with notebooks Create a notebook Explore notebook code

Total QoS training course description An advanced technical hands on course focusing on Quality of Service issues in IP networks. What will you learn Explain the difference between Integrated services and differentiated services. Explain how DiffServ works. Explain how RSVP works. Design networks supporting QoS. Total QoS training course details Who will benefit: Network administrators. Network operators. Prerequisites: TCP/IP Foundation for engineers Duration 3 days Total QoS training course contents What is QoS QoS and CoS, throwing bandwidth at the problem, Best effort services, Differentiated services, Integrated services, guarantees, the need for QoS, IETF working groups. Application issues Video, Voice, other applications, Jitter, delay, packet loss. Flows, per flow and per aggregate QoS, Stateful vs. stateless QoS, applications vs. network QoS. 'Traditional' IP QoS The TOS field and precedence, the obsolete OSPF use of the TOS field, TCP congestion avoidance. Queuing Where to use queuing, FIFO, Priority queuing, Custom queuing, Weighted Fair Queuing, CBWFQ, PQWFQ, LLQ, RED and WRED. DiffServ Architecture, DSCP, CU, packet classification and marking, meters and conditioners, Bandwidth brokers and COPS, Per Hop Behaviours, best effort PHB, Assured Forwarding PHB, Expedited forwarding PHB, Network Based Application Recognition (NBAR). Layer 2 issues Fragmentation and interleaving, compression (codecs, MPEG formats, header compressionâ¦), 802.1p, Subnet bandwidth management, Bandwidth allocators and requestor modules, the use of MPLS, traffic engineering, traffic shaping. RSVP What is RSVP? architectures, paths, path messages, reservations, traffic specifications, tear downs, guaranteed and controlled load, token buckets, Call Admission Control in voice networks, gatekeepers. Other issues Policy based routing, the Resource Allocation Protocol, QoS management tools, baselining networks, design issues, QoS in IPv6, QoS and multicasts.

SNMP training course description A hands-on generic look at the technical operation of SNMP. The course starts with an overview of all the components, which make up SNMP. Hands on starts early with configuration of a managed network. The major versions of SNMP are then put into perspective followed by a look at the SNMP protocol. MIBs are then studied both from the perspective of reading MIBs and writing MIBs. The course finishes with a look at the security implications of SNMP. What will you learn Describe the SNMP architecture. Analyse SNMP packets. Recognise the MIB structure. Describe the SMI. Recognise the strengths and weaknesses of SNMPv2 and SNMPv3. SNMP training course details Who will benefit: Network administrators. Network operators. Programmers writing MIBs and agents. Prerequisites: TCP/IP Foundation for engineers Hands on experience of an SNMP management station would also be beneficial. Duration 3 days SNMP training course contents Network management What is network management? Benefits, issues. What is SNMP? SNMP architecture, SNMP MIBs, SMI, the SNMP protocol, polling security, alternatives to SNMP: CMIP, web based management. Configuring SNMP Auto discovery for management stations, NMS configuration, agent configuration, traps. Hands on Configuring agents and an NMS. SNMP background SNMP history, RFCs, standards, SNMP protocol versions, SNMPv1, SNMPv2, SNMPv3, SNMP SMI versions, which version should you use? Futures. SNMPv1 packets SNMP in the 7 layer model, port numbers, general packet format, BER, GET, GET-NEXT, tables, SET, TRAP, bandwidth issues, in band versus out of band management. Hands on Analysing SNMPv1 packets. SNMPv2 packets SNMPv2 improvements, error handling, GETBULK, v2traps, INFORM. Hands on Analysing SNMPv2 packets. SNMPv3 packets SNMPv3 packet format, use of SNMPv2 messages, REPORT PDU. MIB structure The internet MIB branch, standard mib-2, extra parts of mib-2, private enterprise MIBs, loading extra MIBs. Hands on MIB browsing. mib-2 The mib-2 groups, system group, interfaces group, IP group, ICMP group, TCP group, UDP group, transmission group, SNMP group, RMON. Hands on mib-2 browsing in detail. SMI The MIB layout, obtaining a private enterprise number, MIB definitions, IMPORT, Module identity, Textual conventions, object definitions, notifications, compliance statements, object groups, base SMI data types, application data types, scalars, instances, tables, table definition, writing agents, SMIng. SNMP security Community strings, SNMPv1 and SNMPv2c security practices, SNMPv3 security, SNMPv3 architecture, SNMP applications, the SNMP engine, the EngineID, security fields in SNMPv3 packets, USM, authentication, encryption, timeliness, VBAC, SNMPv3 configuration.

VoIP training course description Convergence of voice and data is now a common place mainstream technology. Our Voice Over IP course investigates the characteristics of voice transmission and then studies the impact on IP networks. Practical sessions with soft phones, hard phones and gateways allow the students to see all aspects of VoIP. Network analysers are used to study packets on the wire. What will you learn Describe the issues of voice and data convergence. Describe techniques, which can be used in IP to provide low uniform delay. Evaluate VoIP technologies. Design data networks, which will support voice. VoIP training course details Who will benefit: Anyone working in the field of networking or telecommunications. Prerequisites: TCP/IP foundation for engineers Intro to data communications & networking Duration 3 days VoIP training course contents What is VoIP Voice over IP, brief review of IP, brief review of telephones and voice. Configuring IP softphones What are softphones? Downloading, installing. Hands on Building the base IP network, a simple VoIP call with softphones, Internet telephony. Addressing E164, FQDN, IP addresses, URIs, DNS, SIP addressing, H.323 addressing. VoIP issues Bandwidth, Delay, Jitter, digitising voice, digitisation steps, coding, quality issues, MOS, voice compression, silence suppression, packetising voice, prioritising voice, jitter buffers. Hands on Simple packet analysis. Architectures Desktop, backbone, gateway, hard phones, PoE, integrating phones and PCs, carriers, Softswitches. Hands on Integrating Softphones, hard phones and analog phones. IP performance and QoS ITU delay recommendations, IP DSCP field, DiffServ, IP precedence, queuing strategies; FIFO, WFQ, custom, priority, RED, LLQ. VoIP protocol stack RTP, RTCP, mixers and translators, RSVP. Bandwidth, Erlang models, link layer overhead. Hands on Calculating VoIP bandwidth, analysing RTP packets. ITU Recommendation H.323 Architecture, protocols, terminals, Call setup, Gatekeepers, gateway discovery, H.323 registration with a gatekeeper. Hands on PC to PC using H.323. IETF - Session Initiation Protocol What is SIP? SIP protocol stack, SDP, Sip architecture, SIP messages, Initial SIP phone startup, SIP servers, proxy server, redirect server. Hands on PC to PC using SIP. Carrier networks Signalling systems, SS7, media gateways, Media gateway controllers, signalling gateways, MGCP, Megaco, SIGTRAN. Hands on PSTN interworking. Video over IP Video components, digital video, pictures and audio, video codecs, issues and solutions, video conferencing, multipoint video conferencing, video protocol stack. Appendix 1: Multicasting. Appendix 2: Voice/data integration without IP.

LTE Architecture and Protocols course description This course provides a comprehensive tour of the LTE architecture along with services provided and the protocols used. What will you learn Describe the overall architecture of LTE. Explain the information flows through LTE. Describe the LTE security. Describe LTE mobility management. Recognise the next steps for LTE. LTE Architecture and Protocols course details Who will benefit: Anyone working with LTE. Prerequisites: Mobile communications demystified Duration 3 days LTE Architecture and Protocols course contents Introduction History, LTE key features. The 4G ITU process. The LTE 3GPP specifications. Specifications. System Architecture LTE hardware architecture. UE architecture and capabilities. E-UTRAN and eNB. EPC, MME functions, SGW, PGW and PCRF. System interfaces and protocol stacks. Example information flows. Dedicated and default bearers. EMM, ECM, RRC state diagrams. Radio transmission and reception OFDMA, SC-FDMA, MIMO antennas. Air interface protocol stack. Logical, transport and physical channels. Frame and slot structure, the resource grid. Resource element mapping of the physical channels and signals. Cell acquisition, data transmission and random access. MAC, RLC, PDCP protocols. LTE spectrum allocation. Power-on procedures Network and cell selection. RRC connection establishment. Attach procedure, including IP address allocation and default bearer activation. LTE detach procedure. Security in LTE networks LTE security features, identity confidentiality, ciphering and integrity protection. Architecture of network access security in LTE. Secure key hierarchy. Authentication and key agreement procedure. Security mode command procedure. Network domain security architecture. Security associations using IKE and IPSec. Mobility management RRC_IDLE, RRC_CONNECTED. Cell reselection, tracking area updates. Measurement reporting. X2 and S1 based handovers. Interoperation with UMTS, GSM and non-3GPP technologies such as cdma2000. QoS, policy control and charging QoS in LTE, EPS bearers, service data flows and packet flows. The architecture and signalling procedures for policy and charging control. Data transport using GPRS, differentiated services and MPLS. Offline and online charging in LTE. Delivery of voice and text messages over LTE Difficulties and solutions for Voice over LTE. Architecture and call setup procedures for circuit switched fallback. Architecture, protocols and call setup procedures in IP multimedia subsystem. Enhancements in release 9 LTE location services. Multimedia broadcast / multicast service and MBSFN. Cell selection, commercial mobile alert service. LTE Advanced and release 10 Impact of carrier aggregation on LTE air interface. Enhanced MIMO processing on uplink and downlink. Relaying. Release 11 and beyond. OAM and self organising networks Operation, administration, maintenance and provisioning for LTE. Self-configuration of base station parameters. Fractional frequency re-use, inter-cell interference co-ordination. Self-optimisation of base station procedures. Self-healing to detect and recover from faults.

Voice over LTE training course description This course provides a basic understanding of the 3G LTE Air Interface, SAE, as well as Voice over LTE options and LTE Advanced features. Investigating the standards for the EPS , formulated by the 3GPP standards body, the course will set out to examine and explain the 4G environment from user equipment to border gateway and beyond. This course will ensure the delegate has a grasp of all aspects of the current global deployments, the next steps in upgrades and the promise of things to come. What will you learn Describe the complete EPC architecture. Explain the use of QoS within the air interface & core network. Explore the features of LTE advanced. Describe the various methods of supporting voice services with 3G LTE. Describe IMS structure and control entities. Explain an IMS session. Voice over LTE training course details Who will benefit: Any engineers who are assisting in the deployment of voice services within their LTE networks. Prerequisites: Intro to Data comms & networking Telecommunications Introduction Duration 3 days Voice over LTE training course contents 3GPP standards body Release 8 - Release 12, Supported and expected features. The EPC revisited EPC revisited 3G LTE & EPC Architecture, NB, MME, SGW, PDNGW, PCRF, Interworking capabilities, Protocol stack explored, NAS signalling, Default EPS bearer, Slot allocation algorithms, Scheduling algorithms, Quality of Service requirements, Dedicated EPS bearers. VoLTE deployment strategies Common networks everywhere, GSM/WCDMA view, CDMA view. VoLTE system architecture LTE radio, LTE Radio background, LTE radio architecture, Evolved packet core, EPC entities & functions, EPS mobility management, MS entities, Home subscriber server, Policy & charging rules function. VoLTE functionality Radio functionality, Bearers & schedulers, Mobility, Circuit switched fall back handover, Mobility from 2G/3G back to LTE, Power Saving Features, Positioning services, UE radio access capabilities for VoLTE users. EPC functionalities, LTE subscriber identification, PDN connectivity establishment, EPS dedicated bearer setup, IMS identification, IP multimedia identification module, Public user identity, Private user identity, Relationship between public & private identity, identification of users device, identification of network entities, identification of services, identification without ISIM. IMS service provisioning, Enforcement of allowed services, Service triggering information, Selection of the AS, AS behaviour, Service provisioning in action. VoLTE end-to-end & signalling VoLTE subscription & device configuration. EPS attach for CSFB/IMS VoIP & default bearer. IMS registration, Constructing the REGISTER request, From UE to P-CSCF, From P-CSCF to I-CSCF, From I-CSCF to S-CSCF, S-CSCF challenges the UE, UE's response to the challenge, Registration at the S-CSCF, The 200 OK response, Third-party registration to application servers, Subscription to registration event package, Re-registration & re-authentication, De-registration, Related standards. IMS VoIP session, Constructing the INVITE request, Routing, Media negotiation, Media resource reservation & policy control, Charging, Session release. Voice continuity, PS - PS intersystem handover, Single radio voice call continuity. IMS emergency session, PDN Connection setup for emergency session, Emergency registration, Emergency session. CS fallback for EPS call case, Architecture of CS fallback in EPS, Description of SGs interface, Idle mode signalling reduction, Idle mode vs active mode, CS fallback attachment, Mobile originating call using CSFB, Mobile terminating call using CSFB, Call unrelated CSFB procedures, Mobile terminating roaming retry & forwarding. VoLTE Messaging, Native IMS messages, SMS interworking, Multimedia messaging service. Unstructured supplementary services data simulation in IMS. IMS services VoLTE radio performance Coverage, Latency, Capacity. LTE advanced features Carrier aggregation, Coordinated mMulti-point Operation (CoMP), ICIC & eICIC, Relay node deployment & donor eNBs, Improved cell edge coverage, Reduced control plane latency, Heterogeneous networks, HeNB, security gateways, HeNB gateways.

RACISM – ACKNOWLEDGING AND UNDERSTANDING
By Inclusive Solutions
In this course we deepen participants understanding of systemic racism and the spectrum of privilege. It challenges the participants to examine their behaviours and take close looks at some of the views they have held since a very young age, e.g. this area is a “bad” area, because it has a high proportion of black/brown people living in it, or that young black men in tracksuits are “thugs”. We think about where these messages come from and how people are indoctrinated by the media. Course Category Inclusion Team Building Leadership Emotional needs Description In this course we deepen participants understanding of systemic racism and the spectrum of privilege. It challenges the participants to examine their behaviours and take close looks at some of the views they have held since a very young age, e.g. this area is a “bad” area, because it has a high proportion of black/brown people living in it, or that young black men in tracksuits are “thugs”. We think about where these messages come from and how people are indoctrinated by the media. We explore the reasons why white people are so defensive when it comes to talking about race. We discuss having racial biases and the implications of them, such as unconsciously insulting people around us in the workplace. When we become aware of how our behaviours can affect people, we then look for solutions. The course is designed for groups of professionals to come together as a team to try and take responsibility for the racism that goes on in their workplace – empowering the leadership to have difficult conversations with team members and create a paradigm shift across the entire organisation. Please come with an open mind, and you might be surprised at what you find out. We are striving for a world where racism is an open conversation and not a topic that we shy away from. Testimonials “That was a really insightful session and thought provoking. I would love to attend more sessions on racism. Thank you for the engaging questions and delivery” “Lots of things to reflect on!” Learning Objectives Participants will: Confront their own racism and unconscious biases Become aware of the ways they treat people differently based on race Think about practical changes they can make in their workplaces Who Is It For? Leadership teams seeking guidance and reflection Educators who want to get it right People who have had not had much contact with people outside their own race People who believe they are “not racist” Course Content Background – brief history of systemic racism Racism as a binary – the problem with thinking only “bad” people can be racist Trust – how do we feel around people we don’t trust? Difference – how do we act when we feel different? What do Good Manners look like around people of different cultures? What does Good Allyship look like in the workplace? Why don’t we talk about race? What does your race mean to you? Examining our privilege – activity Interracial friendship video Visioning – what does the ideal workplace look like? Setting Actions – what achievable actions can we set to bring us closer to our dream future?

