- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
4162 Courses delivered Live Online
Total NetFlow training course description A comprehensive hands on course covering NetFlow. The course starts with the basics of flows moving swiftly onto configuring NetFlow and studying the information it provides. What will you learn Describe NetFlow. Configure generators and collectors. Recognise how NetFlow can be used. Describe the issues in using NetFlow. Compare NetFlow with SNMP, RMON and sflow. Total NetFlow training course details Who will benefit: Technical staff working with NetFlow. Prerequisites: TCP/IP Foundation Duration 2 days Total NetFlow for engineers What is NetFlow? Flows. Where to monitor traffic. Hands on Wireshark flow analysis. Getting started with NetFlow NetFlow configuration. Hands on Accessing NetFlow data using the CLI. NetFlow architecture Generators and collectors. When flows are exported. NetFlow reporting products. SolarWinds. Hands on Collector software. NetFlow features and benefits Real time segment statistics, real time top talkers, traffic matrices. Hands on Traffic analysis with NetFlow. NetFlow issues NetFlow impact, agent resources, server resources, comparing NetFlow with SNMP, RMON and sflow. Hands on Advanced NetFlow configuration. Export formats Flow aging timers, NetFlow versions, export formats, templates, IPFIX. Hands on NetFlow packet analysis. NetFlow MIBs The NetFlow MIB, configuration, retrieving NetFlow statistics. Hands on Integrating NetFlow with SNMP.

Certified Information Security Systems Professional (CISSP)
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for This course is intended for experienced IT security-related practitioners, auditors, consultants, investigators, or instructors, including network or security analysts and engineers, network administrators, information security specialists, and risk management professionals, who are pursuing CISSP training and certification to acquire the credibility and mobility to advance within their current computer security careers or to migrate to a related career. Through the study of all eight CISSP Common Body of Knowledge (CBK) domains, students will validate their knowledge by meeting the necessary preparation requirements to qualify to sit for the CISSP certification exam. Additional CISSP certification requirements include a minimum of five years of direct professional work experience in two or more fields related to the eight CBK security domains, or a college degree and four years of experience. Overview #NAME? In this course, students will expand upon their knowledge by addressing the essential elements of the 8 domains that comprise a Common Body of Knowledge (CBK)© for information systems security professionals. Prerequisites CompTIA Network+ Certification 1 - Security and Risk Management Security Governance Principles Compliance Professional Ethics Security Documentation Risk Management Threat Modeling Business Continuity Plan Fundamentals Acquisition Strategy and Practice Personnel Security Policies Security Awareness and Training 2 - Asset Security Asset Classification Privacy Protection Asset Retention Data Security Controls Secure Data Handling 3 - Security Engineering Security in the Engineering Lifecycle System Component Security Security Models Controls and Countermeasures in Enterprise Security Information System Security Capabilities Design and Architecture Vulnerability Mitigation Vulnerability Mitigation in Embedded, Mobile, and Web-Based Systems Cryptography Concepts Cryptography Techniques Site and Facility Design for Physical Security Physical Security Implementation in Sites and Facilities 4 - Information Security Management Goals Organizational Security The Application of Security Concepts 5 - Information Security Classification and Program Development Information Classification Security Program Development 6 - Risk Management and Ethics Risk Management Ethics 7 - Software Development Security Software Configuration Management Software Controls Database System Security 8 - Cryptography Ciphers and Cryptography Symmetric-Key Cryptography Asymmetric-Key Cryptography Hashing and Message Digests Email, Internet, and Wireless Security Cryptographic Weaknesses 9 - Physical Security Physical Access Control Physical Access Monitoring Physical Security Methods Facilities Security

Essential SDN training course description Software Defined Networking (SDN) has become one of the industries most talked technologies. This training course cuts through the hype and looks at the technology, architecture and products available for SDN along with looking at the impact it may have on your network. What will you learn Explain how SDN works. Describe the architecture of SDN. Explain the relationship between SDN and OpenFlow. Recognise the impact SDN will have on existing networks. Essential SDN training course details Who will benefit: Anyone wishing to know more about SDN. Prerequisites: None. Duration 2 days Essential SDN training course contents Introduction What is SDN? What is OpenFlow? SDN benefits. The SDN stack and architecture. SDN architecture SDN applications, SDN switches, SDN controllers, Network Operating Systems. Control plane, data plane. Control to Data Plane Interface (CDPI), Northbound interfaces. SDN components, control and data plane abstractions. Network Operating Systems Finding the topology, Global view, control program, configuration based on views, graph algorithm. OpenFlow Just one part of SDN. Open Networking Foundation, OpenFlow ports, Flow tables, OpenFlow Channels. The OpenFlow protocol, OpenFlow header, OpenFlow operations. OpenFlow versus OpFlex. SDN and open source OpenDaylight, OpenVSwitch, Open Networking Forum, Open Network Operating System. OpenStack Neutron. SDN implications Separation of control and data plane, NOS running on servers, Emphasis on edge complexity, core simplicity, OpenvSwitch, Incremental migration, importance of software. SDN vs NVF.

50255 Managing Windows Environments with Group Policy
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for This course is intended for Enterprise network staff responsible for help desk support, system administration, and network design. Overview At Course Completion: - Features and functions of Group Policy - Use Group Policy management tools to manage security policies - Design a Group Policy infrastructure - Group Policy processing architecture - Back up, restore, import, and copy Group Policy Objects through the Group Policy - Management Console - Use Windows PowerShell to manage Group Policy - Implement security using Group Policy - Configure the desktop environment with Group Policy - Configure roaming profiles and Folder Redirection - Assign and publish software packages - Implement AppLocker and software restriction policies - Create and deploy Administrative Templates - Configure Group Policy preferences In this course, you will learn how to reduce costs and increase efficiencies in your network. You will discover how to consolidate the administration of an enterprise IT infrastructure with Group Policy, and you will learn to control and manage computer systems and domain users running Windows Server 2016 and Windows clients. Create Group Policies, implement administrative and security templates, and determine best practices when deploying software packages. Walk away with the experience and tools needed to optimize your enterprise systems and networks, implement administrative and security templates, and determine best practices when deploying software packages. 1 - Introduction to Configuration Management Configuration Management Overview Configuration Management Using Group Policy Group Policy Features Introduced with Later Versions of Windows Using Windows PowerShell in the Configuration Management Process 2 - Using Group Policy Management Tools Local and Domain Policies Using Group Policy Management Console Understanding Group Policy Refresh 3 - Designing a Group Policy Infrastructure Design Stages for a Group Policy Infrastructure Planning your Group Policy Design Designing Your Group Policy Solution Deploying Your Group Policy Solution Managing Your Group Policy Solution 4 - Understanding the Architecture of Group Policy Processing Group Policy Components in AD DS Understanding the Group Policy Deployment Order Modifying Group Policy Processing 5 - Troubleshooting and Backing Up GPOs Using Group Policy Troubleshooting Tools Integration of RSoP Functionality Group Policy Logging Options Backing Up, Restoring, Importing, and Copying GPOs Building Migration Tables 6 - Securing Windows Using Group Policy Exploring the Windows Security Architecture Securing User Accounts Exploring Security Policies Windows Firewall with Advanced Security Implementing Domain Security Security Policy Options for Window Client and Windows Server 7 - Implementing Application Security Using Group Policy Managing UAC Settings Defending Against Malware Using AppLocker to Restrict Software Implementing Windows App Security Settings 8 - Configuring the Desktop Environment with Group Policy Exploring Script Types and Controlling Script Execution Defining the Desktop, Start Menu, and Taskbar Settings Defining the Control Panel Settings Defining the Windows Components Settings Configuring the Printer Management and Pruning Settings Defining the Network Settings Discovering the new Group Policy Settings 9 - Implementing User State Virtualization Configuring Folder Redirection Managing Offline Files Implementing User Experience Virtualization OneDrive for Business 10 - Assigning and Publishing Software Packages Using MSI Packages to Distribute Software Using Group Policy as a Software Deployment Method Deploying Software Setting Up Distribution Points Using the Systems Center Configuration Manager to Distribute Software 11 - Configuration Management with Windows PowerShell Introducing Windows PowerShell Using Windows PowerShell Writing PowerShell Scripts Windows PowerShell Library for Group Policy Windows PowerShell-Based Logon Scripts 12 - Implementing PowerShell Desired State Configuration Introducing Group Policy Preferences Comparing Preferences and Policy Settings Options for Applying Preferences Configure Preference Settings 13 - Configuring Group Policy Preferences Introducing Group Policy Preferences Comparing Preferences and Policy Settings Options for Applying Preferences Configuring Preferences Settings Additional course details: Nexus Humans 50255 Managing Windows Environments with Group Policy training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the 50255 Managing Windows Environments with Group Policy course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

Intro to containers training course description This course looks at the technologies of containers and microservices. The course starts with a look at what containers are, moving onto working with containers. Networking containers and container orchestration is then studied. The course finishes with monitoring containers with Prometheus and other systems. Hands on sessions are used to reinforce the theory rather than teach specific products, although Docker and Kubernetes are used. What will you learn Use containers. Build containers. Orchestrate containers. Evaluate container technologies. Intro to containers training course details Who will benefit: Those wishing to work with containers. Prerequisites: Introduction to virtualization. Duration 2 days Intro to containers training course contents What are containers? Virtualization, VMs, What are containers? What are microservices? Machine containers, application containers. Benefits. Container runtime tools Docker, LXC, Windows containers. Architecture, components. Hands on Installing Docker client and server. Working with containers Docker workflow, Docker images, Docker containers, Dockerfile, Building, running, storing images. Creating containers. Starting, stopping and controlling containers. Public repositories, private registries. Hands on Exploring containers. Microservices What are microservices? Modular architecture, IPC. Hands on Persistence and containers. Networking containers Linking, no networking, host, bridge. The container Network Interface. Hands on Container networking Container orchestration engines Docker swarm: Nodes, services, tasks. Apache Mesos: Mesos master, agents, frameworks. Kubernetes: Kubectl, master node, worker nodes. Openstack: Architecture, containers in OpenStack. Amazon ECS: Architecture, how it works. Hands on Setup and access a Kubernetes cluster. Managing containers Monitoring, logging, collecting metrics, cluster monitoring tools: Heapster. Hands on Using Prometheus with Kubernetes.

Securing Kubernetes training course description This course introduces concepts, procedures, and best practices to harden Kubernetes based systems and container-based applications against security threats. It deals with the main areas of cloud-native security: Kubernetes cluster setup, Kubernetes cluster hardening, hardening the underlying operating system and networks, minimizing microservices vulnerabilities, obtaining supply chain security as well as monitoring, logging, and runtime security. What will you learn Harden Kubernetes systems and clusters. Harden containers. Configure and use Kubernetes audit logs. Securing Kubernetes training course details Who will benefit: Technical staff working with Kubernetes Prerequisites: Kubernetes_for_engineers_course.htm Definitive Docker for engineers Duration 2 days Securing Kubernetes training course contents This course does not only deal with the daily security administration of Kubernetes-based systems but also prepares delegates for the official Certified Kubernetes Security Specialist (CKS) exams of the Cloud Native Computing Foundation (CNCF). Structure: 50% theory 50% hands on lab exercise Module 1: User and authorization management Users and service accounts in Kubernetes Authenticating users Managing authorizations with RBAC Module 2: Supply chain security Vulnerabilit checking for images Image validation in Kubernetes Reducing image footprint Secure image registries Module 3: Validating cluster setup and penetration testing Use CIS benchmark to review the security configuration of Kubernetes components. Modify the cluster components' configuration to match the CIS Benchmark. Penetration testing Kubernetes for known vulnerabilities. Module 4: System hardening Use kernel hardening tools Setup appropriate OS level security domains Container runtime sandboxes Limit network access Module 5: Monitoring and logging Configure Kubernetes audit logs Configure Audit Policies Monitor applications behaviour with Falco

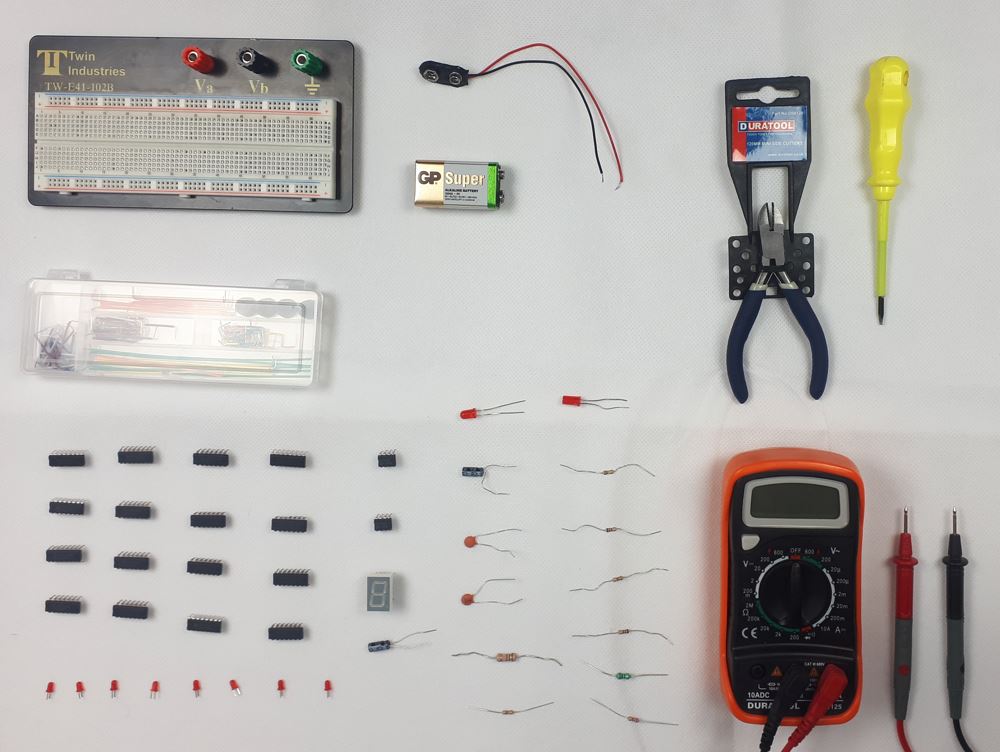
Digital Electronics Course Online
By Hi-Tech Training
This Digital Electronics Course is designed to give practical knowledge of the type of electronic circuitry used in a modern Computer System or in any type of Computer Controlled equipment such as Photocopiers, Cash Registers, Tablets, mobile phones and many other types of IT equipment. Digital Electronics involves the use of Silicon chips (Integrated Circuits). The internal structure of a computer is to a large extent comprised of Digital Electronic Circuits.
Designated Safeguarding Lead Refresher Training
By Brightcore Consultancy
The Designated Safeguarding Lead Advanced Course is an expert-led update and refresher course for school and college DSLs and their Deputies. It is an extensive, authoritative and highly rated, full-day training course that ensures DSL/DDSLs have the most comprehensive, effective and up-to-date knowledge and strategies in place to lead the safeguarding provision in their setting.

Netgear switches training course description A hands on course covering the product specifics of Netgear switches. Installation, configuration, maintenance and troubleshooting are all covered in a practical oriented way. What will you learn Install Netgear switches. Use the command line interface and the web based interface to manage Netgear switches. Configure and troubleshoot Netgear switches. Perform software upgrades. Netgear switches training course details Who will benefit: Anyone working with Netgear switches. Particularly aimed at engineers and technicians supporting Netgear switches. Prerequisites: None. Duration 2 days Netgear switches training course content Introduction How Ethernet works with hubs, How Ethernet works with switches. Installing Netgear switches. Hands on Building a network with a hub, building a network with a Netgear switch. Basic troubleshooting The Netgear switch range, LEDs, cabling issues, factory resets, default settings. Hands on Building a network with multiple Netgear switches. Configuration methods Managed vs. unmanaged switches, Console port access, telnet, web based access, SNMP, saving configurations, NVRAM, switch stacks, stacking ports. Hands on Accessing the switch using the console, IP address configuration, telnet. Console interface Password protection, the menus, menu options. Hands on Setting a password, displaying the switch configuration. Web based interface Getting started, basic format. Hands on Configuring the switch using the web interface. Port configuration Common port configuration tasks, port trunking. Hands on Configuring ports. STP configuration What is STP? Configuring STP. Hands on Enabling and disabling STP, configuring STP VLAN configuration What are VLANS? 802.1Q, tagged/untagged, creating VLANS, applying VLANS. Hands on Setting up VLANS, setting up 802.1Q, Inter VLAN traffic. Housekeeping TFTP, upgrades Hands on Boot from net. SNMP SNMP configuration, NMS's. Hands on Using SNMP to manage a Netgear switch, putting it all together: troubleshooting.

Network virtualization training course description This course covers network virtualization. It has been designed to enable network engineers to recognise and handle the requirements of networking Virtual Machines. Both internal and external network virtualization is covered along with the technologies used to map overlay networks on to the physical infrastructure. Hands on sessions are used to reinforce the theory rather than teach specific manufacturer implementations. What will you learn Evaluate network virtualization implementations and technologies. Connect Virtual Machines with virtual switches. Explain how overlay networks operate. Describe the technologies in overlay networks. Network virtualization training course details Who will benefit: Engineers networking virtual machines. Prerequisites: Introduction to virtualization. Duration 2 days Network virtualization training course contents Virtualization review Hypervisors, VMs, containers, migration issues, Data Centre network design. TOR and spine switches. VM IP addressing and MAC addresses. Hands on VM network configuration Network virtualization What is network virtualization, internal virtual networks, external virtual networks. Wireless network virtualization: spectrum, infrastructure, air interface. Implementations: Open vSwitch, NSX, Cisco, others. Hands on VM communication over the network. Single host network virtualization NICs, vNICs, resource allocation, vSwitches, tables, packet walks. vRouters. Hands on vSwitch configuration, MAC and ARP tables. Container networks Single host, network modes: Bridge, host, container, none. Hands on Docker networking. Multi host network virtualization Access control, path isolation, controllers, overlay networks. L2 extensions. NSX manager. OpenStack neutron. Packet walks. Distributed logical firewalls. Load balancing. Hands on Creating, configuring and using a distributed vSwitch. Mapping virtual to physical networks VXLAN, VTEP, VXLAN encapsulation, controllers, multicasts and VXLAN. VRF lite, GRE, MPLS VPN, 802.1x. Hands on VXLAN configuration. Orchestration vCenter, vagrant, OpenStack, Kubernetes, scheduling, service discovery, load balancing, plugins, CNI, Kubernetes architecture. Hands on Kubernetes networking. Summary Performance, NFV, automation. Monitoring in virtual networks.
