- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
863 Courses in Liverpool delivered Live Online
55265 Microsoft© PowerApps
By Nexus Human
Duration 2 Days 12 CPD hours This course is intended for This class has something for everything, from beginners who wish to customise their data entry forms in SharePoint right up to advanced users who need to use advanced formulas to deliver more bespoke actions to their apps. Overview After taking this course, students will be able to: - Understand when to use PowerApp. - Describe the components of PowerApps and their correct use. - Create PowerApps from existing data sources. - Brand PowerApps. - Customize PowerApps beyond just using the automated wizards. - Connect to a range of data sources from Excel to Azure SQL. - Understand the difference between canvas apps and model-driven apps. - Integrate PowerApps with other Office 365 systems ? including Teams and SharePoint Online. - Administer and Maintain PowerApps Students will be taught how to design, test and publish new apps that work with a variety of data sources. We will take users through a selection of well-crafted lessons to help them build new applications for their business. 1 - AN INTRODUCTION TO POWERAPPS What is PowerApps? The benefits of apps How to get PowerApps Canvas Apps and Model-Driven Apps License Options and Costs Discover PowerApps with Templates Lab 1: Introduction to PowerApps 2 - GETTING STARTED WITH POWERAPPS Building a new app from a data source Add, edit and remove controls Intro to Formulas Testing an app App Settings Publish and Share Apps Version History and Restore PowerApps Mobile App Lab 1: Getting Started 3 - BRANDING AND MEDIA Less is more Duplicate Screens Fonts Screen Colours and Matching Colours Screen Backgrounds Buttons and Icons Hide on Timer Size and Alignment by reference Show and Hide on Timer Lab 1: Branding and Media 4 - POWERAPPS CONTROLS Text Controls for Data Entry and Display Controls ? Drop downs, combo box, date picker, radio button and more Forms ? Add and edit data in underlying data sources quickly Charts ? present information in pie, line and bar charts Lab 1: Build Apps from Blank 5 - DATA SOURCES AND LOGIC Data Storage and Services How do I decide which database to use? Connect to on-premises data - Gateway What is Delegation? Specific Data Examples Displaying Data Lab 1: Data Source and Logic 6 - MODEL-DRIVEN APPS What is a model-driven app? Where will my data be stored? How do create a model-driven app Canvas vs model-driven summary Lab 1: Model-Driven App 7 - POWERAPP INTEGRATION Embed PowerApps in Teams Embed PowerApps in SharePoint Online Start a Flow from a PowerApp Lab 1: PowerApp Integration 8 - ADMINISTRATION AND MAINTENANCE OF POWERAPPS Identify which users have been using PowerApps Reuse an app in another location (move from testing or development to production) Review app usage Prevent a user from using PowerApps Manage environments Lab 1: Administration and Maintenance Additional course details: Nexus Humans 55265 Microsoft PowerApps training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the 55265 Microsoft PowerApps course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

Interior Design Tutor one to one
By Real Animation Works
Interior design tutor one to one open 7 days 9 am to 9 pm

Process Control and Instrumentation
By EnergyEdge - Training for a Sustainable Energy Future
About this Training Course This course will begin with a presentation of topics to familiarize Process and Instrumentation Engineers with procedures and practices involved in the choice of sensors related to the measurement of temperature, pressure, level and flow in relation to single-phase flows. It will provide guidance on the optimum commercially available devices through a detailed comparison of their relative merits. At the heart of this course is sensor calibration which is a crucial element for these topics. The course will also examine the various types of flow control valve, including Globe, Slide, Needle, Eccentric plug and Ball valves and their characteristics in industrial application, while focusing on the problems of Cavitation and Flashing and methods to minimise or eradicate these issues. With the use of examples, industry case studies and a wide range of videos, this course will also cover all aspects of proportional (P), derivative (D) and integral (I) control. In particular, it will address the advantages and disadvantages of PI and PID control. It will also describe Cascade, Feed forward, Split Range, Override and Ratio Control techniques. Training Objectives By attending this course, participants will acquire the following knowledge and skills: Apply an in-depth knowledge to the measurement of temperature, pressure, level and flow as well as to the fluid mechanics of pipe flows Assess the advantages and disadvantages of the major flowmeter types including the differential pressure, rotary positive displacement, rotary-inferential, electromagnetic, ultrasonic and Coriolis mass flowmeters to determine the optimum choice for a given application Make a considered judgement of the choice of fluid level measurement devices Understand the various types of flow calibration, metering systems and provers Carry out tank measurement and tank calibration methods and to calculate net sellable quantities Discuss valve characteristics & trim selection and illustrate the process of control valve sizing Explain the terms Open and Closed loop Define Process Variable, Measured Variable, Set Point and Error Define Direct and Reverse controller actions Explain the terms Process Lag, Measurement Lag, Transmission Lag, and Response Lag and their effect on controllability Explain ON/ OFF Control and the inherent disadvantages Explain Proportional Control, Offset, Gain and Proportional Band and the advantages and disadvantages of Proportional only control Explain the fundamentals and operation principles of Integral (I) Action and the disadvantages of proportional plus integral control Explain the fundamentals and operation principles of Derivative (D) Action in conjunction with P action Describe the operating principles of a PID Controller and explain the applications and advantages of PID control Describe Cascade, Forward, Split Range and Ratio Control operation principles Target Audience This course will benefit instrumentation, inspection, control, custody metering and process engineers and other technical staff. It is also suitable for piping engineers, pipelines engineers, mechanical engineers, operations engineers, maintenance engineers, plant/field supervisors and foremen and loss control coordinators. Trainer Your expert course leader is a Senior Mechanical & Instrumentation Engineer (UK, B. Sc., M.Eng., Ph D) with over 45 years of industrial experience in Process Control & Instrumentation, Pumps, Compressors, Turbines and Control Valve Technology. He is currently a Senior Independent Consultant to various petrochemical industries in the UK, USA, Oman, Kuwait and KSA where he provides consultancy services on both the application and operational constraints of process equipment in the oil & gas industries. During his early career, he held key positions in Rolls Royce (UK) where he was involved in the design of turbine blading for jet engines, subject to pre-specified distributions of pressure. During this period and since, he has also been closely involved in various aspects of Turbomachinery, Thermodynamics and Fluid Mechanics where he has become a recognised authority in these areas. Later, he joined the academic staff of University of Liverpool in the UK as a Professor in Mechanical Engineering Courses. A substantial part of his work has been concerned with detailed aspects of Flowmetering - both of single & multiphase flows. He has supervised doctoral research students in this area in collaboration with various European flowmeter manufacturers. He joined Haward Technology Middle East in 2002 and was later appointed as European Manager (a post which has since lapsed) and has delivered over 150 training courses in Flowmeasurement (single- and multi-phase), Control, Heat Exchangers, Pumps, Turbines, Compressors, Valve and Valve Selection as well as other topics throughout the UK, USA, Oman and Kuwait. During the last two years, he has delivered courses with other training companies operating in the Far and Middle East. He has published about 150 papers in various Engineering Journals and International Conferences and has contributed to textbooks on the topics listed above. POST TRAINING COACHING SUPPORT (OPTIONAL) To further optimise your learning experience from our courses, we also offer individualized 'One to One' coaching support for 2 hours post training. We can help improve your competence in your chosen area of interest, based on your learning needs and available hours. This is a great opportunity to improve your capability and confidence in a particular area of expertise. It will be delivered over a secure video conference call by one of our senior trainers. They will work with you to create a tailor-made coaching program that will help you achieve your goals faster. Request for further information post training support and fees applicable Accreditions And Affliations

COBIT 2019 Foundation
By Nexus Human
Duration 2 Days 12 CPD hours This course is intended for The COBIT 2019 Foundation course would suit candidates working in the following IT professions or areas: IT Auditors IT Managers IT Quality professionals IT Leadership IT Developers Process practitioners Managers in IT service providing firms The above list is a suggestion only; individuals may wish to attend based on their own career aspirations, personal goals or objectives. Delegates may take as few or as many Intermediate qualifications as they require, and to suit their needs. Overview This COBIT 2019 Foundation course is designed as an introduction to COBIT 2019 and enables you to understand how an integrated business framework for the governance and management of enterprise IT can be utilized to achieve IT business integration, cost reductions and increased productivity. The syllabus areas that this course is designed to cover are: New framework introduction Key concepts and terminology Governance and Framework Principles Governance system and components Governance and management objectives Performance management Designing a tailored governance system COBIT 2019 builds on and integrates more than 25 years of development in this field, not only incorporating new insights from science, but also operationalizing these insights as practice. The heart of the COBIT framework updates COBIT principles while laying out the structure of the overall framework including: New concepts are introduced and terminology is explained?the COBIT Core Model and its 40 governance and management objectives provide the platform for establishing your governance program. The performance management system is updated and allows the flexibility to use maturity measurements as well as capability measurements. Introductions to design factors and focus areas offer additional practical guidance on flexible adoption of COBIT 2019, whether for specific projects or full implementation. From its foundation in the IT audit community, COBIT has developed into a broader and more comprehensive information and technology (I&T) governance and management framework and continues to establish itself as a generally accepted framework for I&T governance. 1 - COBIT 5 OVERVIEW AND INTRODUCTION Course Administration Course Objectives Exam Overview Certification Scheme History of COBIT COBIT 2019 Improvements Major differences with 2019 Misconceptions about COBIT COBIT and Other Standards 2 - KEY CONCEPTS AND TERMINOLOGY Introduction to Enterprise Governance of Information and Technology Benefits of Information and Technology Governance COBIT Information and Technology Governance Framework Distinction of Governance and Management Three Principles of a Governance Framework Six Principles for a Governance System 3 - GOVERNANCE SYSTEMS AND COMPONENTS Introduction to the Components of a Governance System Processes and Capability Levels Organizational Structures and Defined Roles Information Flows and Items People, Skills and Competencies Principles, Policies and Frameworks Culture, Ethics and Behavior Services, Infrastructure and Applications 4 - GOVERNANCE MANAGEMENT OBJECTIVES Governance and Management Objectives Publication Governance and Management Objectives Governance and Management Objectives Core Model Evaluate, Direct and Monitor Align, Plan and Organize Build, Acquire and Implement Deliver, Service and Support Monitor, Evaluate and Assess 5 - GOALS CASCADE Governance and Management Objective Relationships Governance and Management Objective Descriptions High-Level Information Example Introduction to the Goals Cascade Enterprise Goals Alignment Goals Mapping Tables ? Appendix A 6 - PERFORMANCE MANAGEMENT Introduction to Performance Management COBIT Performance Management Principles COBIT Performance Management (CPM) Overview Process Capability Levels Rating Process Activities Focus Area Maturity Levels Performance Management of Organizational Structures Performance Management of Information Items Performance Management of Culture and Behavior 7 - DESIGNING A TAILORED GOVERNANCE SYSTEM The Need for Tailoring Design Factors Enterprise Strategy Enterprise Goals Risk Profile I&T Related Issues Threat Landscape Compliance Requirements Role of IT Sourcing Model for IT IT Implementation Methods Technology Adoption Strategy Enterprise Size Focus Areas Designing a Tailored Governance System Management Objective Priority and Target Capability Levels Component Variations Specific Focus Areas Stages and Steps in the Design Process 8 - IMPLEMENTING ENTERPRISE GOVERNANCE OF IT The Business Case The COBIT Implementation Guide Purpose COBIT Implementation Approach Phase 1 ? What are the Drivers Phase 2 ? Where are we Now Phase 3 ? Where do we Want to be Phase 4 ? What Needs to be Done Phase 5 ? How do we get There Phase 6 ? Did we get There Phase 7 How do we Weep the Momentum Going? EGIT Implementation Program Challenges

Usability Testing
By Experience Thinkers
Gain robust techniques for obtaining feedback from end users throughout product design, and learn how to identify new opportunities for design improvement.
Interaction Design
By Experience Thinkers
Learn how to establish deliberate and creative interactions that allow users to navigate a platform in the ways that makes sense to them.

Adobe After Effects One Day Course (Live Online Only)
By London Design Training Courses
Click here for more info Duration: 5 hrs Method: 1-2-1, Personalized attention, Tailored content, Flexible pace, Individual support. Schedule: Personalized training experience with our flexible 1-2-1 sessions. Choose your convenient hour from Monday to Saturday between 9 am and 7 pm. After Effects CC Training: From Novices to Experts Immerse yourself in the world of motion graphics and VFX with our Adobe Certified After Effects Courses, suitable for total novices and experts alike. Learn to create captivating motion graphics, smooth animations, and stunning special effects in a professional environment. Choose from four learning options: London Classroom: Attend in-person sessions 1-2-1 in our dynamic studio. Live Online Classes: Join interactive classes from the comfort of your home or office. Bespoke Training: Tailor the course to your specific needs and preferences. Whichever path you select, all options cover the same lesson plan delivered by our Certified Professional Trainers. Rest assured, your learning experience is fully supported by our 100% Satisfaction Guarantee. Adobe After Effects Essentials (5-hour course) Session 1: Introduction to After Effects (1 hour) Overview of After Effects and its applications in motion graphics and visual effects. Understanding the workspace and interface. Importing and organizing assets for seamless workflow. Creating projects and compositions. Session 2: Animation Basics (1.5 hours) Working with layers: Adding, editing, and arranging layers in the timeline. Keyframe animation: Introduction to keyframes and creating simple animations. Motion paths: Manipulating motion paths for dynamic animations. Easing motion: Applying ease in and ease out to smoothen animations. Animation presets: Utilizing built-in presets for efficient animation. Session 3: Effects and Compositing (1.5 hours) Applying effects: Adding visual effects to layers and compositions. Compositing techniques: Understanding blending modes and layer styles. Masking and track mattes: Using masks to control the visibility of layers and apply effects. Motion tracking: Applying tracking data to objects in a scene. Session 4: Text and Shape Animation (1 hour) Text animation: Creating and animating text layers with different styles. Shape layers: Introduction to shape layers and their applications. Animating shapes: Using shape layers to create dynamic animations. Session 5: Final Project and Exporting (1 hour) Applying all the learned techniques to create a final motion graphics project. Refining the project and adding finishing touches. Understanding export settings and rendering the final output. By the end of this 5-hour Adobe After Effects Essentials course, participants will achieve the following learning outcomes: Introduction to After Effects: Understand the fundamentals of After Effects, its interface, and workspace. Animation Basics: Master keyframe animation and motion path manipulation for smooth and dynamic animations. Effects and Compositing: Apply visual effects, utilize blending modes, and work with masks and track mattes for creative compositing. Text and Shape Animation: Create and animate text layers with various styles and explore the versatility of shape layers in animations. Final Project and Exporting: Apply all learned techniques to create a final motion graphics project and export the finished output.

CompTIA Network+
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for This course is intended for entry-level computer support professionals with a basic knowledge of computer hardware, software, and operating systems who wish to increase their knowledge and understanding of networking concepts and acquire the required skills to prepare for a career in network support or administration, or who wish to prepare for the CompTIA Network+ certification. CompTIA Network+ is the first certification IT professionals specializing in network administration and support should earn. Network+ is aimed at IT professionals with job roles such as network administrator, network technician, network installer, help desk technician, and IT cable installer. This course is also designed for students who are seeking the CompTIA Network+ certification and who want to prepare for the CompTIA Network+ N10-008 Certification Exam. Overview In this course, you will describe the major networking technologies and systems of modern networks and configure, manage, and troubleshoot modern networks. Explain the OSI and TCP/IP Models. Explain properties of network traffic. Install and configure switched networks. Configure IP networks. Install and configure routed networks. Configure and monitor ports and protocols. Explain network application and storage issues. Monitor and troubleshoot networks. Explain network attacks and mitigations. Install and configure security devices. Explain authentication and access controls. Deploy and troubleshoot cabling solutions. Implement and troubleshoot wireless technologies. Compare and contrast WAN technologies. Use remote access methods. Identify site policies and best practices. CompTIA's Network+ certification is a foundation-level certification designed for IT professionals with around one year of experience, whose job role is focused on network administration. The CompTIA Network+ exam will certify the successful candidate has the knowledge and skills required to troubleshoot, configure, and manage common network devices; establish basic network connectivity; understand and maintain network documentation; identify network limitations and weaknesses; and implement network security, standards, and protocols. The candidate will have a basic understanding of enterprise technologies, including cloud and virtualization technologies. The Official CompTIA© Network+© (Exam N10-008): will teach you the fundamental principles of installing, configuring, and troubleshooting network technologies and help you to progress a career in network administration. In this course, you will build on your existing user-level knowledge and experience with personal computer operating systems and networks to master the fundamental skills and concepts that you will need to use on the job in any type of networking career. Prerequisites CompTIA A+ Certification (Exams 220-1001 and 220-1002) 1 - Explaining the OSI and TCP/IP Models Topic A: Explain OSI Model Layers Topic B: Explain the TCP/IP Suite 2 - Explaining Properties of Network Traffic Topic A: Explain Media Types and Access Methods Topic B: Deploy Ethernet Standards Topic C: Configure and Monitor Network Interfaces 3 - Installing and Configuring Switched Networks Topic A: Install and Configure Hubs and Bridges Topic B: Install and Configure Switches Topic C: Compare and Contrast Network Topologies Topic D: Compare and Contrast Network Types 4 - Configuring IP Networks Topic A: Configure IPv4 Addressing Components Topic B: Test IP Interfaces with Command Line Tools Topic C: Configure IPv4 Subnets Topic D: Configure Private and Public IPv4 Addressing Schemes Topic E: Configure IPv6 Addressing Components Topic F: Configure DHCP Services 5 - Installing and Configuring Routed Networks Topic A: Explain Characteristics of Routing Topic B: Install and Configure Routers 6 - Configuring and Monitoring Ports and Protocols Topic A: Explain the Uses of Ports and Protocols Topic B: Use Port Scanners and Protocol Analyzers Topic C: Explain the Use of Name Resolution Services Topic D: Configure DNS and IPAM Services 7 - Explaining Network Application and Storage Services Topic A: Explain the Uses of Network Applications Topic B: Explain the Uses of Voice Services and Advanced Networking Devices Topic C: Explain the Uses of Virtualization and Network Storage Services Topic D: Summarize the Concepts of Cloud Services 8 - Monitoring and Troubleshooting Networks Topic A: Monitor Network Interfaces and Logs Topic B: Explain Network Troubleshooting Methodology Topic C: Troubleshoot Common Network Services Issues 9 - Explaining Networking Attacks and Mitigations Topic A: Summarize Common Networking Attacks Topic B: Explain the Characteristics of VLANs Topic C: Explain the Characteristics of NAT and Port Forwarding 10 - Installing and Configuring Security Devices Topic A: Install and Configure Firewalls and Proxies Topic B: Explain the Uses of IDS/IPS and UTM 11 - Explaining Authentication and Access Controls Topic A: Explain Authentication Controls and Attacks Topic B: Explain the Uses of Authentication Protocols and Directory Services Topic C: Explain the Uses of Port Security and NAC Topic D: Implement Network Device Hardening Topic E: Explain Patch Management and Vulnerability Scanning Processes 12 - Deploying and Troubleshooting Cabling Solutions Topic A: Deploy Structured Cabling Systems Topic B: Deploy Twisted Pair Cabling Solutions Topic C: Test and Troubleshoot Twisted Pair Cabling Solutions Topic D: Deploy Fiber Optic Cabling Solutions 13 - Implementing and Troubleshooting Wireless Technologies Topic A: Install and Configure Wireless Technologies Topic B: Troubleshoot Wireless Performance Issues Topic C: Secure and Troubleshoot Wireless Connectivity 14 - Comparing and Contrasting WAN Technologies Topic A: Compare and Contrast WAN Core Service Types Topic B: Compare and Contrast WAN Subscriber Service Types Topic C: Compare and Contrast WAN Framing Service Types Topic D: Compae and Contrast Wireless and IoT WAN Technologies 15 - Using Remote Access Methods Topic A: Use Remote Access VPNs Topic B: Use Remote Access Management Methods 16 - Identifying Site Policies and Best Practices Topic A: Manage Networks with Documentation and Diagrams Topic B: Summarize the Purposes of Physical Security Devices Topic C: Compare and Contrast Business Continuity and Disaster Recovery Concepts Topic D: Identify Policies and Best Practices

EC-Council Computer Hacking Forensic Investigator (CHFI) v10.0
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for The CHFI course will benefit: Police and other laws enforcement personnel Defense and Military personnel e-Business Security professionals Systems administrators Legal professionals Banking, Insurance and other professionals Government agencies Overview At the end of this course, you will possess the skills needed to: Understand the fundamentals of computer forensics Understand the computer forensic investigation process Describe in detail different types of hard disks and file systems Understand data acquisition and duplication Counteract anti-forensic techniques Leverage forensic skills in Windows, Linux, and Mac Investigate web attacks Understand dark web forensics Deploy forensic techniques for databases, cloud, and networks Investigate email crimes including malware Perform forensics in mobile and IoT environments Every crime leaves a digital footprint, and you need the skills to track those footprints. In this course, students will learn to unravel these pieces of evidence, decode them and report them. From decoding a hack to taking legal action against the perpetrators, they will become an active respondent in times of cyber-breaches. Computer Forensics in Today?s World 1.1. Understand the Fundamentals of Computer Forensics 1.2. Understand Cybercrimes and their Investigation Procedures 1.3. Understand Digital Evidence 1.4. Understand Forensic Readiness, Incident Response and the Role of SOC (Security Operations Center) in Computer Forensics 1.5. Identify the Roles and Responsibilities of a Forensic Investigator 1.6. Understand the Challenges Faced in Investigating Cybercrimes 1.7. Understand Legal Compliance in Computer Forensics Computer Forensics Investigation Process 2.1. Understand the Forensic Investigation Process and its Importance 2.2. Understand the Pre-investigation Phase 2.3. Understand First Response 2.4. Understand the Investigation Phase 2.5. Understand the Post-investigation Phase Understanding Hard Disks and File Systems 3.1. Describe Different Types of Disk Drives and their Characteristics 3.2. Explain the Logical Structure of a Disk 3.3. Understand Booting Process of Windows, Linux and Mac Operating Systems 3.4. Understand Various File Systems of Windows, Linux and Mac Operating Systems 3.5. Examine File System Using Autopsy and The Sleuth Kit Tools 3.6 Understand Storage Systems 3.7. Understand Encoding Standards and Hex Editors 3.8. Analyze Popular File Formats Using Hex Editor Data Acquisition and Duplication 4.1. Understand Data Acquisition Fundamentals 4.2. Understand Data Acquisition Methodology 4.3. Prepare an Image File for Examination Defeating Anti-forensics Techniques 5.1. Understand Anti-forensics Techniques 5.2. Discuss Data Deletion and Recycle Bin Forensics 5.3. Illustrate File Carving Techniques and Ways to Recover Evidence from Deleted Partitions 5.4. Explore Password Cracking/Bypassing Techniques 5.5. Detect Steganography, Hidden Data in File System Structures, Trail Obfuscation, and File Extension Mismatch 5.6. Understand Techniques of Artifact Wiping, Overwritten Data/Metadata Detection, and Encryption 5.7. Detect Program Packers and Footprint Minimizing Techniques 5.8. Understand Anti-forensics Countermeasures Windows Forensics 6.1. Collect Volatile and Non-volatile Information 6.2. Perform Windows Memory and Registry Analysis 6.3. Examine the Cache, Cookie and History Recorded in Web Browsers 6.4. Examine Windows Files and Metadata 6.5. Understand ShellBags, LNK Files, and Jump Lists 6.6. Understand Text-based Logs and Windows Event Logs Linux and Mac Forensics 7.1. Understand Volatile and Non-volatile Data in Linux 7.2. Analyze Filesystem Images Using The Sleuth Kit 7.3. Demonstrate Memory Forensics Using Volatility & PhotoRec 7.4. Understand Mac Forensics Network Forensics 8.1. Understand Network Forensics 8.2. Explain Logging Fundamentals and Network Forensic Readiness 8.3. Summarize Event Correlation Concepts 8.4. Identify Indicators of Compromise (IoCs) from Network Logs 8.5. Investigate Network Traffic 8.6. Perform Incident Detection and Examination with SIEM Tools 8.7. Monitor and Detect Wireless Network Attacks Investigating Web Attacks 9.1. Understand Web Application Forensics 9.2. Understand Internet Information Services (IIS) Logs 9.3. Understand Apache Web Server Logs 9.4. Understand the Functionality of Intrusion Detection System (IDS) 9.5. Understand the Functionality of Web Application Firewall (WAF) 9.6. Investigate Web Attacks on Windows-based Servers 9.7. Detect and Investigate Various Attacks on Web Applications Dark Web Forensics 10.1. Understand the Dark Web 10.2. Determine How to Identify the Traces of Tor Browser during Investigation 10.3. Perform Tor Browser Forensics Database Forensics 11.1. Understand Database Forensics and its Importance 11.2. Determine Data Storage and Database Evidence Repositories in MSSQL Server 11.3. Collect Evidence Files on MSSQL Server 11.4. Perform MSSQL Forensics 11.5. Understand Internal Architecture of MySQL and Structure of Data Directory 11.6. Understand Information Schema and List MySQL Utilities for Performing Forensic Analysis 11.7. Perform MySQL Forensics on WordPress Web Application Database Cloud Forensics 12.1. Understand the Basic Cloud Computing Concepts 12.2. Understand Cloud Forensics 12.3. Understand the Fundamentals of Amazon Web Services (AWS) 12.4. Determine How to Investigate Security Incidents in AWS 12.5. Understand the Fundamentals of Microsoft Azure 12.6. Determine How to Investigate Security Incidents in Azure 12.7. Understand Forensic Methodologies for Containers and Microservices Investigating Email Crimes 13.1. Understand Email Basics 13.2. Understand Email Crime Investigation and its Steps 13.3. U.S. Laws Against Email Crime Malware Forensics 14.1. Define Malware and Identify the Common Techniques Attackers Use to Spread Malware 14.2. Understand Malware Forensics Fundamentals and Recognize Types of Malware Analysis 14.3. Understand and Perform Static Analysis of Malware 14.4. Analyze Suspicious Word and PDF Documents 14.5. Understand Dynamic Malware Analysis Fundamentals and Approaches 14.6. Analyze Malware Behavior on System Properties in Real-time 14.7. Analyze Malware Behavior on Network in Real-time 14.8. Describe Fileless Malware Attacks and How they Happen 14.9. Perform Fileless Malware Analysis - Emotet Mobile Forensics 15.1. Understand the Importance of Mobile Device Forensics 15.2. Illustrate Architectural Layers and Boot Processes of Android and iOS Devices 15.3. Explain the Steps Involved in Mobile Forensics Process 15.4. Investigate Cellular Network Data 15.5. Understand SIM File System and its Data Acquisition Method 15.6. Illustrate Phone Locks and Discuss Rooting of Android and Jailbreaking of iOS Devices 15.7. Perform Logical Acquisition on Android and iOS Devices 15.8. Perform Physical Acquisition on Android and iOS Devices 15.9. Discuss Mobile Forensics Challenges and Prepare Investigation Report IoT Forensics 16.1. Understand IoT and IoT Security Problems 16.2. Recognize Different Types of IoT Threats 16.3. Understand IoT Forensics 16.4. Perform Forensics on IoT Devices

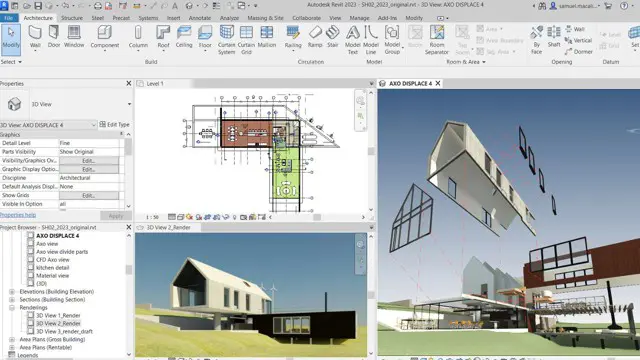
Revit One to One Basic to Advance Weekends Online or Face to Face
By Real Animation Works
Revit face to face training customised and bespoke. Online or Face to Face