- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
5281 Courses in Cardiff delivered Live Online
JL3V - Junos Layer 3 VPNs
By Nexus Human
Duration 3 Days 18 CPD hours This course is intended for This course benefits individuals responsible for configuring and monitoring devices running the Junos OS. Overview Describe the value of MPLS VPNs. Describe the differences between provider-provisioned VPNs and customer-provisioned VPNs. Describe the differences between Layer 2 VPNs and Layer 3 VPNs. List the provider-provisioned MPLS VPN features supported by the JUNOS software. Describe the roles of a CE device, PE router, and P router in a BGP Layer 3 VPN. Describe the format of the BGP routing information, including VPN-IPv4 addresses and route distinguishers. Describe the propagation of VPN routing information within an AS. List the BGP design constraints to enable Layer 3 VPNs within a provider network. Explain the operation of the Layer 3 VPN data plane within a provider network. Create a routing instance, assign interfaces to a routing instance, create routes in a routing instance, and import/export routes from a routing instance using route distinguishers/route targets. Describe the purpose of BGP extended communities, configure extended BGP extended communities, and use BGP extended communities. List the steps necessary for proper operation of a PE-CE dynamic routing protocol. List the troubleshooting and monitoring techniques for routing instances. Explain the difference between the bgp.l3vpn table and the inet.0 table of a routing instance. Monitor the operation of a CE-PE dynamic routing protocol. Explain the operation of a PE mulit-access interface in a Layer 3 VPN and list commands to modify that behavior. Describe ways to support communication between sites attached to a common PE router. Provision and troubleshoot hub-and-spoke Layer 3 VPNs, Describe the flow of control traffic and data traffic in a hub-and-spoke Layer 3 VPN. Describe QoS mechanisms available in L3VPNs. Configure L3VPN over GRE tunnels. Describe the RFC 4364 VPN options. Describe the carrier-of-carriers model. Configure the carrier-of-carriers and ''Option C'' configuration. Describe the flow of control and data traffic in a draft-rosen multicast VPN. Describe the configuration steps for establishing a draft-rosen multicast VPN. Monitor and verify the operation of draft-rosen multicast VPNs. Describe the flow of control traffic and data traffic in a next-generation multicast VPN. Describe the configuration steps for establishing a next-generation multicast VPN. Describe the configuration steps for establishing a next-generation multicast VPN. Monitor and verify the operation of next-generation multicast VPNs. This three-day course is designed to provide students with MPLS-based Layer 3 virtual private network (VPN) knowledge and configuration examples. Chapter 1: Course Introduction Course Introduction Chapter 2: MPLS VPNs MPLS VPNs Provider-Provisioned VPNs Chapter 3: Layer 3 VPNs Layer 3 VPN Terminology VPN-IPv4 Address Structure Operational Characteristics Chapter 4: Basic Layer 3 VPN Configuration Preliminary Steps PE Router Configuration Lab: Layer 3 VPN with Static and BGP Routing Chapter 5: Layer 3 VPN Scaling and Internet Access Scaling Layer 3 VPNs Public Internet Access Options Lab: LDP over RSVP Tunnels and Public Internet Access Chapter 6: Layer 3 VPNs ? Advanced Topics Exchanging Routes between Routing Instances Hub-and-Spoke Topologies Layer 3 VPN CoS Options Layer 3 VPN and GRE Tunneling Integration Layer 3 VPN and IPSec Integration Layer 3 VPN Egress Protection BGP prefix-independent convergence (PIC) edge for MPLS VPNs VRF Localization Provider Edge Link Protection Support for configuring more than 3 million L3VPN Labels Lab: GRE Tunneling Chapter 7: Interprovider Backbones for Layer 3 VPNs Hierarchical VPN Models Carrier-of-Carriers Model Option C Configuration Lab: Carrier of Carrier Layer 3 VPNs Chapter 8: Troubleshooting Layer 3 VPNs Working with Multiple Layers Troubleshooting Commands on a PE Device Multiaccess Interfaces in Layer 3 VPNs PE and CE-based Traceroutes Layer 3 VPN Monitoring Commands Lab: Troubleshooting Layer 3 VPNs Chapter 9: Draft Rosen Multicast VPNs Multicast Overview Draft Rosen MVPN Overvie Draft Rosen MVPN Operation Configuration Monitoring Chapter 10: Next Generation Multicast VPNs Multicast VPN Overview Next-Generation MVPN Operation Configuration Monitoring Internet Multicast Ingress Replication Internet Multicast Signaling and Data Plane Configuring MVPN Internet Multicast Monitoring MVPN Internet Multicast Lab: MVPN Internet Multicast

Agile project management (In-House)
By The In House Training Company
Agile project management, already widely used for software development, is increasingly recognised as having much more general application. Continuous improvement programmes, business change projects, new technology development, research and development and a variety of other scenarios characterised by rapid change and high uncertainty can all benefit from an Agile approach. This programme presents the concepts and methods of Agile project management, and shows how to apply them to a range of project and change management situations. Participants will learn: how Agile project management can help with project and change management the 4 values and 12 principles of the Agile 'manifesto' and the range of Agile methodologies how to apply Agile project management methods and techniques in a range of project scenarios alternative Agile project management methods and how they can be applied and adapted what makes Agile project teams succeed the key roles and responsibilities needed to enable Agile project teams to work effectively how to encourage an Agile mindset within their organisation and how to move toward an Agile approach to managing projects 1 Introduction to Agile project management Overview of 'classical' project management and methodologies The link between project success and management performance Limitations of classical approaches and the need for Agile methods The 4 values and 12 principles of the Agile manifesto explained Agile project management values:Individuals and interactions over processes and toolsWorking outputs over comprehensive documentationCustomer collaboration over contract negotiationResponding to change over following a plan The cultural challenges of using Agile project management Choosing when and how to adopt Agile project management 2 Initiating a project using Agile project management Some key Agile methodologies explained: SCRUM, XP, Crystal Identifying and engaging project stakeholders; defining roles and responsibilities Setting the project vision and goals; defining project scope The Agile approach to requirements capture and elicitation of needs Tools and techniques for capturing and characterising requirements The role of documentation, reporting and process management 3 The Agile approach to definition and planning Understanding Agile planning; the 'planning onion' concept Developing the culture needed for collaborative involvement and iterative planning Defining project deliverables; the 'product backlog' concept Tools and techniques for defining and prioritising requirements in Agile projects Understanding and applying Agile estimating techniques Dealing with uncertainty and managing risks 4 The Agile approach to execution and delivery The results orientated, fast adapting culture of Agile teams The monthly 'Sprint' process for project planning and review The disciplines needed for effective daily SCRUM meetings Reviewing progress, managing change and project reporting Testing, completing and handing over of work packages Managing the interface between the project team and the business 5 Leadership and teamwork in Agile project teams Why Agile teams are different: the importance of individuals and interactions The skills and attributes needed to lead an Agile project team The challenges faced and skills needed by Agile team members Recognising team development needs; adopting the right leadership style Making the transition from project manager to Agile coach Key coaching skills explored: mentoring, facilitating, managing conflict

Risk Assessing in the Care Sector
By Prima Cura Training
This course is designed to enable learners to increase their understanding of risk assessment and risk management in Health and Social Care settings.

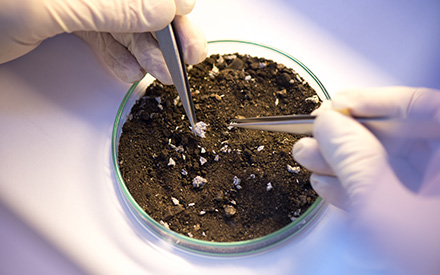
Asbestos in soils and contaminated land
By Airborne Environmental Consultants Ltd
The course covers investigation and risk assessment of asbestos-contaminated soils and sites, including waste classification and land remediation. It will cover the current HSE and EA legislation and guidance, assessing risk to health from asbestos in soils and how to assess the land, analysis types and interpretation, and remedial actions.
Sales skills for selling products (In-House)
By The In House Training Company
Bad news - people don't buy your product. Better news - they don't buy anyone else's product either. Best news - they do buy what a product gives them, whether it be removing 'pain' or giving 'pleasure'. So what a challenge it is that every single person buys your product for a slightly different reason! What's the secret to selling in that sort of sales environment? This programme provides a great roadmap. This course will help participants: Build rapport with authenticity Use open questions, listening and summary to properly understand the prospect Use 'impact' questions to 'stack the pain' of remaining with the status quo Convert features into personalised benefits that reflect stated needs Handle objections with calm confidence Identify buying signals Close effectively Convey credible urgency centred on the prospect's - not the salesperson's - interests 1 What makes a customer buy any product? Moving towards 'pleasure' Moving away from 'pain' Robert Cialdini's Psychology of Influence - buying motives Understanding what your product does for customers Why there is never a 'one size fits all' approach What are the real 'unique selling points' and why the salesperson is the real 'USP' At what point does the customer emotionally buy your product? 2 Getting past gatekeepers What gatekeepers' motivations are How to make them your friend rather than your enemy How to make your call harder to block than to put through How to control the gatekeeper with questions, not answers Using Cialdini's 'reciprocity' law to get put through more often Practical exercise in which the trainer poses as gatekeeper 3 Questioning and listening skills How to use open questions to get the customer talking What questions to avoid and why How to 'stack the pain' of the status quo with 'impact questions' Practical 'pain stacking' exercise in pairs What listening is and what it isn't Question funnelling - how to earn deeper disclosure through probing Practical funnelling exercise in pairs The power of summary 4 How to create tailored benefits and not 'dive into solution' What is 'diving into solution'? Examples and analogies Why it is to be avoided Practical exercise in pairs - how it feels to have solutions offered up too early How to avoid 'feature-dumping' What is 'value selling'? How to create tailored benefits How to convert product features into benefits How to deal with the prospect's competitor allegiance 5 Handling objections and testing the water How to overcome the price objection by selling value Common objections the participants encounter and answers that work The objections salespeople carry in their own heads The 'A-C-E' objection-handling model How to uncover objections When - and when not - to trial close 6 Closing skills Why salespeople often close too early How to identify buying signals How to use urgency with skill and effectiveness Four killer closing techniques that work How to avoid buying the product back by careless post-sale talk How to ask for referrals for your product How to 'farm' the account for future opportunities 7 Wrap-up Key learnings from each participant Individual action planning - steps that can and will be implemented in the workplace

Asbestos in soils and contaminated land Online
By Airborne Environmental Consultants Ltd
The course covers investigation and risk assessment of asbestos-contaminated soils and sites, including waste classification and land remediation. It will cover the current HSE and EA legislation and guidance, assessing risk to health from asbestos in soils and how to assess the land, analysis types and interpretation, and remedial actions.

BTEC Assignment Writing Service
By New Assignment Help
Get help with you BTEC assignments at affordable prices and live a stress free life.
HND Assignment Writing Service
By New Assignment Help
Get help in you HND assignment writing task from exprts at affordable prices.
Introduction to Writing SQL Queries (TTSQL003)
By Nexus Human
Duration 3 Days 18 CPD hours This course is intended for This is an introductory- level course appropriate for those who are developing applications using relational databases, or who are using SQL to extract and analyze data from databases and need to use the full power of SQL queries. Overview This course combines expert lecture, real-world demonstrations and group discussions with machine-based practical labs and exercises. Working in a hands-on learning environment led by our expert practitioner, attendees will learn to: Maximize the potential of SQL to build powerful, complex and robust SQL queries Query multiple tables with inner joins, outer joins and self joins Construct recursive common table expressions Summarize data using aggregation and grouping Execute analytic functions to calculate ranks Build simple and correlated subqueries Thoroughly test SQL queries to avoid common errors Select the most efficient solution to complex SQL problems A company?s success hinges on responsible, accurate database management. Organizations rely on highly available data to complete all sorts of tasks, from creating marketing reports and invoicing customers to setting financial goals. Data professionals like analysts, developers and architects are tasked with creating, optimizing, managing and analyzing data from databases ? with little room for error. When databases aren?t built or maintained correctly, it?s easy to mishandle or lose valuable data. Our SQL Programming and Database Training Series provides students with the skills they require to develop, analyze and maintain data and in correctly structured, modern and secure databases. SQL is the cornerstone of all relational database operations. In this hands-on course, you learn to exploit the full potential of the SELECT statement to write robust queries using the best query method for your application, test your queries, and avoid common errors and pitfalls. It also teaches alternative solutions to given problems, enabling you to choose the most efficient solution in each situation. Introduction: Quick Tools Review Introduction to SQL and its development environments Using SQL*PLUS Using SQL Developer Using the SQL SELECT Statement Capabilities of the SELECT statement Arithmetic expressions and NULL values in the SELECT statement Column aliases Use of concatenation operator, literal character strings, alternative quote operator, and the DISTINCT keyword Use of the DESCRIBE command Restricting and Sorting Data Limiting the Rows Rules of precedence for operators in an expression Substitution Variables Using the DEFINE and VERIFY command Single-Row Functions Describe the differences between single row and multiple row functions Manipulate strings with character function in the SELECT and WHERE clauses Manipulate numbers with the ROUND, TRUNC and MOD functions Perform arithmetic with date data Manipulate dates with the date functions Conversion Functions and Expressions Describe implicit and explicit data type conversion Use the TO_CHAR, TO_NUMBER, and TO_DATE conversion functions Nest multiple functions Apply the NVL, NULLIF, and COALESCE functions to data Decode/Case Statements Using the Group Functions and Aggregated Data Group Functions Creating Groups of Data Having Clause Cube/Rollup Clause SQL Joins and Join Types Introduction to JOINS Types of Joins Natural join Self-join Non equijoins OUTER join Using Subqueries Introduction to Subqueries Single Row Subqueries Multiple Row Subqueries Using the SET Operators Set Operators UNION and UNION ALL operator INTERSECT operator MINUS operator Matching the SELECT statements Using Data Manipulation Language (DML) statements Data Manipulation Language Database Transactions Insert Update Delete Merge Using Data Definition Language (DDL) Data Definition Language Create Alter Drop Data Dictionary Views Introduction to Data Dictionary Describe the Data Dictionary Structure Using the Data Dictionary views Querying the Data Dictionary Views Dynamic Performance Views Creating Sequences, Synonyms, Indexes Creating sequences Creating synonyms Creating indexes Index Types Creating Views Creating Views Altering Views Replacing Views Managing Schema Objects Managing constraints Creating and using temporary tables Creating and using external tables Retrieving Data Using Subqueries Retrieving Data by Using a Subquery as Source Working with Multiple-Column subqueries Correlated Subqueries Non-Correlated Subqueries Using Subqueries to Manipulate Data Using the Check Option Subqueries in Updates and Deletes In-line Views Data Control Language (DCL) System privileges Creating a role Object privileges Revoking object privileges Manipulating Data Overview of the Explicit Default Feature Using multitable INSERTs Using the MERGE statement Tracking Changes in Data

Managing and Troubleshooting PCs - Part 1
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for If you are getting ready for a career as an entry-level information technology (IT) professional or personal computer (PC) service technician, the CompTIA© A+© Certification course is the first step in your preparation. Overview In this course, you will install, configure, optimize, troubleshoot, repair, upgrade, and perform preventive maintenance on personal computers, digital devices, and operating systems. You will:Identify the hardware components of personal computers and mobile digital devices.Identify the basic components and functions of operating systems.Identify networking and security fundamentals.Identify the operational procedures that should be followed by professional PC technicians.Install, configure, and troubleshoot display devices.Install and configure peripheral components.Manage system components.Manage data storage.Install and configure Microsoft Windows.Optimize and maintain Microsoft Windows.Work with other operating systems.Identify the hardware and software requirements for client environment configurations.Identify network technologies.Install and configure networking capabilities.Support mobile digital devices.Support printers and multifunction devices.Identify security threats, vulnerabilities, and controls.Implement security controls.Troubleshoot system-wide issues. In this course, you will acquire the essential skills and information you will need to install, upgrade, repair, configure, troubleshoot, optimize, and perform preventative maintenance of basic personal computer hardware and operating systems. Hardware Fundamentals Topic A: Personal Computer Components Topic B: Storage Devices Topic C: Mobile Digital Devices Topic D: Connection Interfaces Operating System Fundamentals Topic A: PC and Mobile Operating Systems Topic B: PC Operating System Tools and Utilities Networking & Security Fundamentals Topic A: Network Types Topic B: Network Components Topic C: Common Network Services Topic D: Cloud Concepts Topic E: Security Fundamentals Safety & Operational Procedures Topic A: Basic Maintenance Tools and Techniques Topic B: Personal and Electrical Safety Topic C: Environmental Safety and Materials Handling Topic D: Professionalism and Communication Topic E: Organizational Policies and Procedures Topic F: Troubleshooting Theory Supporting Display Devices Topic A: Install Display Devices Topic B: Configure Display Devices Topic C: Troubleshoot Video and Display Devices Installing & Configuring Peripheral Components Topic A: Install and Configure Input Devices Topic B: Install and Configure Output Devices Topic C: Install and Configure Input/Output Devices Topic D: Install and Configure Expansion Cards Managing System Components Topic A: Identify Motherboard Components and Features Topic B: Install and Configure CPUs and Cooling Systems Topic C: Install Power Supplies Topic D: Troubleshoot System Components Managing Data Storage Topic A: Identify RAM Types and Features Topic B: Troubleshoot RAM Issues Topic C: Install and Configure Storage Devices Topic D: Configure the System Firmware Topic E: Troubleshoot Hard Drives and RAID Arrays Installing & Configuring Microsoft Windows Topic A: Implement Client-Side Virtualization Topic B: Install Microsoft Windows Topic C: Use Microsoft Windows Topic D: Configure Microsoft Windows Topic E: Upgrade Microsoft Windows Optimizing & Maintaining Microsoft Windows Topic A: Optimize Microsoft Windows Topic B: Back Up and Restore System Data Topic C: Perform Disk Maintenance Topic D: Update Software Working with Other Operating Systems Topic A: The OS X Operating System Topic B: The Linux Operating System Customized Client Enviroments Topic A: Types of Common Business Clients Topic B: Custom Client Environments Networking Technologies Topic A: TCP/IP Properties and Characteristics Topic B: TCP/IP Topic C: Internet Connections Topic D: Ports and Protocols Topic E: Networking Tools Installing & Configuring Networking Capabilities Topic A: Configure Basic Windows Networking Topic B: Configure Network Perimeters Topic C: Using Windows Networking Features Topic D: Install and Configure SOHO Networks Supporting Mobile Digital Devices Topic A: Install and Configure Exterior Laptop Components Topic B: Install and Configure Interior Laptop Components Topic C: Other Mobile Devices Topic D: Mobile Device Accessories and Ports Topic E: Mobile Device Connectivity Topic F: Mobile Device Synchronization Topic G: Troubleshoot Mobile Device Hardware Supporting Printers & Multifunction Devices Topic A: Printer and Multifunction Technologies Topic B: Install and Configure Printers Topic C: Maintain Printers Topic D: Troubleshoot Printers Security Threats, Vulnerabilities, and Controls Topic A: Common Security Threats and Vulnerabilities Topic B: General Security Controls Topic C: Mobile Security Controls Topic D: Data Destruction and Disposal Methods Implementing Security Controls Topic A: Secure Operating Systems Topic B: Secure Workstations Topic C: Secure SOHO Networks Topic D: Secure Mobile Devices Troubleshooting System-Wide Issues Topic A: Troubleshoot PC Operating Systems Topic B: Troubleshoot Mobile Device Operating Systems and Applications Topic C: Troubleshoot Wired and Wireless Networks Topic D: Troubleshoot Common Security Issues
