- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
493 Courses in Cardiff delivered Live Online
Symantec PGP Universal Server 3.2 and PGP Desktop 10.2 Administration
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for This course is intended for those responsible for the installation, configuration, maintenance, or troubleshooting of PGP Universal Server or PGP Desktop. Overview This course provides instruction on PGP Universal Server 3.2 and PGP Desktop 10.2.At the completion of the course, you will be able to: Describe the features, concepts, components, and terminology of both the PGP Universal Server 3.2 and PGP Desktop 10.2products. Install PGP Universal Server 3.2 and complete setup using the most commonly configured options. Install a managed and customized PGP Desktop 10.2 client. Configure, complete administration tasks for, and use PGP Whole Disk Encryption and other PGP Desktop features. Configure policy-based messaging security for internal and external recipients. Create and modify users, user policies, and groups using either manual or directory integration methods. Combine two or more PGP Universal Servers into a cluster. This is designed to provide you with the fundamental knowledge a nd hands-on lab experience to install, administer, and troubleshoot the PGP Universal Management Server and primary client product. Cryptography Essentials Cryptography defined Caesar cipher Symmetric-Key Cryptography Public-Key Cryptography PGP Public-Key Cryptography Digital Signatures Trust Models Keys, Key Signatures and Key properties Verifying keys with key fingerprints Passphrases Certificates PGP Product Information PGP Universal Server PGP Desktop PGP Command Line PGP Support Package for BlackBerry PGP Mobile PGP iOS Viewer Installing PGP Universal Server PGP Universal Server overview Installation tasks and options Completing the PGP Universal Server Setup Assistant Administrative Keys A review of trust and verification The Organization Key The Organization Certificate Configuration and usage of the Additional Decryption Key Other certificates used for trust on PGP Universal Server Ignition key types and features Consumers and Groups Consumers and Groups PGP product user definition Consumer groups Introduction to consumer policy How users, groups, and policy work together Server Messaging Learn Mode In-depth look at Mail Proxy configuration Description of server mail flow and typical configurations Monitoring and Reporting Server monitoring and logging Updates, backups, and restoring Mail Policy Definition of policy chains and rules Rule conditions, actions, and key searches Default mail flow and message policy Adding custom chains to mail flow Overview of various types of policy chains Demonstration and detailed explanation of adding a rule Special messaging actions and dictionaries Key Not Found Problems that require a Key Not Found policy Introduction to Key Not Found configuration Web Messenger Definition of Web Messenger Description of functionality Demonstration of end-user inbox creation Inbox and service administration Inbox replication and backup Customization templates Regular Email option for Web Messenger PDF Messenger statement and certified delivery How the Out of Mail Stream Consumer Policy option functions PGP public key directories Smart Trailer invitation option overview PGP Desktop / S/MIME option overview PGP Universal Satellite overview Preparing Universal Server for PGP Desktop Clients Introduction to directory synchronization High-level overview of LDA P How the server uses a directory to add and assign users to groups Configuring PGP Universal Server Directory Synchronization Keys Managed key configuration Key modes Subkeys Key usage flags Smart card Introduction to key management services Installing PGP Desktop System requirements Citrix and TS compatibility Downloading a custom PGP Desktop installer Modifying installed components Configuring Client Enrollment Definition of enrollment Email, LDA P, and Silent enrollment type overview General PGP Desktop Policy General PGP Desktop Policy Options on the General Card of the PGP Desktop settings of a consumer policy Licensing managed PGP Desktop clients Updating settings for managed installations PGP Desktop Messaging How PGP Desktop affects messaging infrastructure Options on the Messaging Card of the PGP Desktop settings of a consumer policy MAPI encrypt and sign buttons and offline mail processing Configuring PGP Whole Disk Encryption What is Whole Dis k Encryption Configuring WDE PGP Whole Disk Encryption for Windows PGP Whole Disk Encryption for Mac OSX PGP w hole Disk Encryption for Linux PGP Whole Disk Encryption Management and Recover The pgpwd command-line tool Logon failure and reporting The WDE-ADMIN group for large-scale administration PGP Whole Disk Encryption in the PGP Desktop settings of a consumer policy, including authentication methods and user per missions Recovery options PGP NetShare Defining PGP NetShare Encrypted folder creation Configuration of the PGP Universal Server Consumer Policy options for NetShare, including automated folder protection and application-based file protection Client-side administration features for PGP NetShare Miscellaneous compatibility and feature information about PGP NetShare Active Directory Group integration and PGP NetShare usage demonstrations Other PGP Desktop Utilities PGP Zip file and folder protection Securely erasing information using PGP Shredder and the Shred Free Space features PGP Virtual Disk secure volumes Usage cases and PGP Portable definition Clustering How PGP Universal Server Clustering works Using the DMZ Clustering Zone Cluster failover Web Messenger inbox replication Demonstration of cluster creation

Cisco Meeting Server Advanced (COLLAB350)
By Nexus Human
Duration 3 Days 18 CPD hours This course is intended for The primary audience for this course is as follows: Channel partners and reseller engineers installing, configuring, and maintaining scalable and resilient deployments of Cisco Meeting Server Channel partners and reseller engineers providing presales support for scalable and resilient Cisco Meeting Server deployments Customer engineers supporting scalable and resilient Cisco Meeting Server deployments Overview Upon completion of this course, the learner should be able to meet the following objectives: Cisco Meeting Server API commands Scalable and resilient deployments Customization Recording In this 3-day course Cisco Meeting Server Advanced (COLLAB350), you will learn advanced techniques in installing, troubleshooting, and maintaining a single server and single server split deployment of Cisco Meeting Servers. The recently purchased Acano collaboration hardware and software includes video and audio-bridging technology that allows customers to connect video systems from multiple vendors across both cloud and hybrid environments. Cisco has incorporated Acano collaboration technologies into the new Meeting Server tool. Module 1: Reviewing Cisco Meeting Server Intermediate Component parts of a Cisco Meeting Solution Configuration steps for a Cisco Meeting Solution Module 2: APIs Purpose of APIs Benefits of APIs Types of APIs Function of the GET, POST, PUT, and DELETE commands Module 3: Configuring Software with an API How a user can interact with software using an API Download and install Chrome Postman Other API software Download the Cisco Meeting Server API guide Module 4: Configuring Spaces with the Cisco Meeting Server API Cisco Meeting Server API structure Use Chrome Postman for information on calls and spaces with the GET command Use Chrome Postman to post a new call space with the POST command Use Chrome Postman to place changes in a space, including adding a member, with the PUT command Use Chrome Postman to delete a space with the DELETE command Module 5: Customization Configuration Create and modify a user profile and assign users Create and modify a dual-tone multifrequency (DTMF) profile and apply to a user profile Modify the interactive voice response (IVR), color scheme, and background Module 6: Planning a Resilient and Scalable Cisco Meeting Server Deployment Resilient server solutions Scalable server solutions Geographically dispersed configurations and GeoDNS Domain Name System (DNS) records required for a resilient and scalable solution Certificate requirements for a resilient and scalable solution Module 7: Configuring a Database Cluster Relationship between cluster master and cluster slaves in a database cluster Certificate requirements for a secure database cluster Configure the certificates for a database cluster Configure a database cluster Module 8: Configuring a Call Bridge Cluster Relationship between the Call Bridge and the Database How cross-cluster spaces behave Configure certificates for Call Bridge clustering Storage of configuration when entering with the API and the individual web interfaces for Lightweight Directory Access Protocol (LDAP) and Call Bridge clustering Configure a Call Bridge Cluster Connect XMPP server to multiple Call Bridges Module 9: Configuring Load Balancers and Trunks Relationship between the XMPP server, Trunk and Load Balancer Configure certificates for multiple trunks and load balancers Configure multiple Trunks to multiple Load Balancers Module 10: Configuring Multiple Web Bridges Relationship between multiple Web Bridges and Call Bridges Internal and external DNS records support for both internal and external Web Bridges Configure certificates for multiple Web Bridges Configure multiple Web bridges Connect multiple Call Bridges to multiple Web Bridges Module 11: Configuring Multiple TURN Servers Relationship between multiple TURN servers and multiple Call Bridges Configure certificates for multiple TURN servers Configure multiple TURN servers Connect multiple Call Bridges to multiple TURN servers Module 12: Configuring Multiple Recorders Features of the recording capability Software, hardware, and licensing requirements for recording DNS records Configure the Recorder Relationship between multiple Recorders and multiple Call Bridges Configure a Call Bridge to use a Recorder Configure certificates for multiple Recorders servers Configure multiple Recorder servers Connect multiple Call Bridges to multiple Recorder servers Module 13: Integrating with a Resilient and Scalable Cisco Meeting Server Deployment Integration with Cisco TelePresence Video Communication Server (VCS) or Cisco Unified Communications Manager and multiple Call Bridges Integration with Cisco Expressway technology and multiple Call Bridges Integration with Microsoft Skype for Business and multiple Call Bridges Integration with Cisco TelePresence Management Suite and multiple Call Bridges Module 14: Deploying an H.323 Gateway Cisco preferred architecture for H.323 and Session Initiation Protocol (SIP) interoperability Functionality of the Cisco Meeting Server H.323 gateway Configuration the Cisco Meeting Server H.323 gateway Module 15: Multitenancy Options Purpose of the multitenancy capabilities Options for multitenancy capabilities on the Cisco Meeting Server Module 16: Customization Options Options available to customize Cisco Meeting Apps License keys required for customization Web Server requirements for customization Options available to customize recorded messaging Customization options available for invitation text

40-minute Zoom Interior Decor Colour Consultation
By FLOCK interiors
This is a great way to get instant colour palette ideas for a room in your home. FLOCKS zoom consultation process is extremely simple. Nikki will help you identify your colour preference whilst answering any questions plus suggest the best colour palette for your space. After the call, you'll receive a presentation specially tailored to you and your home decor needs. All paint colours suggested will be referenced and free samples will be posted out.
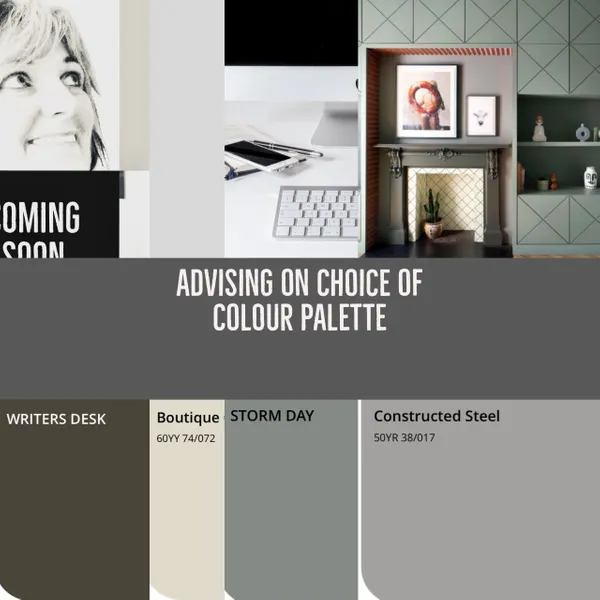
Interior design and decor onsite 5 week course
By FLOCK interiors
This is a one to one course running over five weeks, providing two hours a week of tuition on a flexible basis. The course is aimed at those keen to discover more about the practical aspect of interior design. Whether you are about to embark on a project of your own, are keen to learn more about your individual style, or are just looking to gain more confidence, this course will give you the knowledge and tools to confidently create stylish interiors.

VMware Site Recovery Manager: Install, Configure, Manage [V8.6]
By Nexus Human
Duration 2 Days 12 CPD hours This course is intended for vSphere administrators, architects, system engineers, and systems integrators who are responsible for the deployment or management of Site Recovery Manager Overview By the end of the course, you should be able to meet the following objectives: Summarize the components of Site Recovery Manager architecture Deploy and configure the Site Recovery Manager appliance Describe the principal disaster recovery topologies that are used with Site Recovery Manager Configure inventory and resource mappings Describe the storage replication options that are used with Site Recovery Manager Configure Site Recovery Manager to leverage array-based replication Describe VMware vSphere Replication⢠functionality Describe the vSphere Replication architecture Deploy and configure vSphere Replication for use with Site Recovery Manager Build Site Recovery Manager array-based protection groups, protection groups based on vSphere Replication, and Virtual Volumes protection groups. Build, edit, execute, test, and remove a recovery plan Perform a planned migration This two-day, hands-on training course gives experienced VMware vSphere© administrators the knowledge to install, configure, and manage VMware Site Recovery Manager? 8.6. This course also shows you how to write and test disaster recovery plans that use Site Recovery Manager. Course Introduction Introductions and course logistics Course objectives Site Recovery Manager Architecture Describe Site Recovery Manager architecture Identify disaster recovery options with Site Recovery Manager Evaluate how Site Recovery Manager integrates with VMware products Describe Site Recovery Manager licensing options List the disaster recovery topologies supported by Site Recovery Manager Describe how VMware Site Recovery for VMware Cloud on AWS integrates with Site Recovery Manager Deploying and Configuring Site Recovery Manager Identify the vSphere and vCenter Server requirements for deploying Site Recovery Manager Define Site Recovery Manager virtual appliance system requirements Deploy the Site Recovery Manager appliance Navigate the Site Recovery Manager configuration UI Describe the process for registering Site Recovery Manager with vCenter Server Describe how to start and stop services in Site Recovery Manager Identify ways to perform updates to the Site Recovery Manager appliance Describe the options for accessing the Site Recovery Manager Describe the process for configuring site pairing Describe how to import and export Site Recovery Manager configuration Navigate the Site Recovery Manager configuration UI Describe the process for registering Site Recovery Manager with vCenter Server Describe how to start and stop services in Site Recovery Manager Identify ways to perform updates to the Site Recovery Manager appliance Describe the options for accessing the Site Recovery Manager Describe the process for configuring site pairing Describe how to import and export Site Recovery Manager configuration Configuring Inventory Mappings Explain the importance of inventory mappings Identify configuration options for inventory mappings Describe the importance of placeholder virtual machines and datastores Describe the importance of the vSphere inventory changes for Site Recovery Manager operation Using Array-Based Replication Describe array-based replication Describe Storage Replication Adapters and explain their role for the array-based replication Describe the concept and configuration of array pairs Describe datastore groups and the relationship between devices and datastore groups Describe the role of consistency groups Identify the advantages of array-based replication vSphere Replication Describe Site Recovery Manager with vSphere Replication Architecture Discuss the role of vSphere Replication components Discuss use cases for vSphere Replication Discuss system requirements and operational limits of vSphere Replication Determine how to calculate bandwidth requirements for vSphere Replication Identify the advantages of vSphere Replication Deploy a vSphere Replication appliance Configure a vSphere Replication appliance and register it with vCenter Server Pair vSphere Replication appliances Deploy an additional vSphere Replication server Register a vSphere Replication server with a vSphere Replication management server Replicating VMs Using vSphere Replication Describe the replication process used by vSphere Replication List vSphere Replication replica states Describe vSphere Replication of encrypted virtual machines Describe vSphere native key provider Describe how to configure vSphere Replication Discuss vSphere Replication RPO settings Describe MPIT instances Describe additional vSphere Replication settings Describe how to disable vSphere Replication Protection Groups Define protection group functionality Examine the differences between array-based protection groups, protection groups based on vSphere Replication, and Virtual Volumes protection groups Create a protection group View a placeholder virtual machine in the inventory Configure protection for virtual machines and edit protection groups Recovery Plans Discuss recovery plan concepts Discuss network planning Discuss the organization of storage for recovery plans Describe customization options in recovery planning Describe priority groups and VM dependencies Describe how to implement a recovery plan Configure VM recovery plan properties Describe the customization of recovery plans Configure additional steps in the recovery plan Delete a recovery plan Executing Recovery Plans Discuss use cases for Site Recovery Manager Describe planned migration Identify Site Recovery Manager workflows Examine Site Recovery Manager integration with various vSphere technologies Describe how to conduct a recovery plan test Perform a recovery plan test Identify the effect on the storage layer during the test recovery steps Review the recovery plan test steps Describe how to cancel a recovery plan test and clean up after recovery plan test cancelation Explain a recovery plan execution in planned migration or disaster recovery mode Identify the recovery steps for each execution type Describe a forced recovery Explain the importance of reprotection processes and states Examine failback steps Describe how to reprotect a data center Monitoring and Troubleshooting Identify Site Recovery Manager alarm options Generate Site Recovery Manager recovery plan history reports Configure Site Recovery Manager advanced settings Identify Site Recovery Manager logs Describe the vRealize Operations management pack for Site Recovery Manager
![VMware Site Recovery Manager: Install, Configure, Manage [V8.6]](https://cademy-images-io.b-cdn.net/9dd9d42b-e7b9-4598-8d01-a30d0144ae51/4c81f130-71bf-4635-b7c6-375aff235529/original.png?width=3840)
VMware NSX for Intrinsic Security [V4.x]
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for Experienced security administrators Overview By the end of the course, you should be able to meet the following objectives: Define the concepts related to information security Explain the different types of firewalls and their use cases Describe the operation of intrusion detection and intrusion prevention systems Differentiate between Malware Prevention approaches Describe the VMware intrinsic security portfolio Use NSX segmentation to implement Zero-Trust Security Configure user and role management Configure and troubleshoot Distributed Firewall, Identity Firewall, and time-based policies Configure and troubleshoot Gateway Security Use VMware Aria Operations⢠for Logs and VMware Aria Operations⢠for Networks to operate NSX firewalls Explain the security best practices related to grouping, tagging, and rule configuration Describe north-south and east-west service insertion Describe endpoint protection Configure and troubleshoot IDS/IPS Deploy NSX Application Platform Configure and troubleshoot NSX Malware Prevention Describe the capabilities of NSX Intelligence and NSX NDR This five-day, hands-on training course provides you with the knowledge, skills, and tools to achieve competency in configuring, operating, and troubleshooting VMware NSX© for intrinsic security. This course introduces all the security features in NSX, including Distributed Firewall and Gateway Firewall, Intrusion Detection and Prevention (IDS/IPS), NSX Application Platform, NSX Malware Prevention, VMware NSX© Intelligence?, and VMware NSX© NDR?. In addition, this course presents common configuration issues and gives a methodology to resolve them. Course Introduction Introduction and course logistics Course objectives Security Basics Define the concepts related to information security Explain the different types of firewalls and their use cases Describe the operation of IDS/IPS Differentiate between Malware Prevention approaches VMware Intrinsic Security Define the VMware intrinsic security strategy Describe the VMware intrinsic security portfolio Explain how NSX aligns with the intrinsic security strategy Implementing Zero-Trust Security Define Zero-Trust Security Describe the five pillars of a Zero-Trust architecture Define NSX segmentation and its use cases Describe the steps needed to enforce Zero-Trust with NSX segmentation User and Role Management Integrate NSX and VMware Identity Manager? Integrate NSX and LDAP Describe the native users and roles in NSX Create and assign custom user roles Explain object-based RBAC in a multitenancy environment Distributed Firewall Configure Distributed Firewall rules and policies Describe the NSX Distributed Firewall architecture Troubleshoot common problems related to NSX Distributed Firewall Configure time-based policies Configure Identity Firewall rules Configure the distributed firewall to block malicious IPs Gateway Security Configure Gateway Firewall rules and policies Describe the architecture of the Gateway Firewall Identify and troubleshoot common Gateway Firewall issues Configure TLS Inspection to decrypt traffic for both internal and external services Configure URL filtering and identify common configuration issues Operating Internal Firewalls Use VMware Aria Operations for Logs and VMware Aria Operations for Networks to operate NSX firewalls Explain security best practices related to grouping, tagging, and rule configuration Network Introspection Explain network introspection Describe the architecture and workflows of north-south and east-west service insertion Troubleshoot north-south and east-west service insertion Endpoint Protection Explain endpoint protection Describe the architecture and workflows of endpoint protection Troubleshoot endpoint protection Intrusion Detection and Prevention Describe the MITRE ATT&CK framework Explain the different phases of a cyber attack Describe how NSX security solutions can be used to protect against cyber attacks Configure and troubleshoot Distributed IDS/IPS Configure and troubleshoot North-South IDS/IPS NSX Application Platform Describe NSX Application Platform and its use cases Identify the topologies supported for the deployment of NSX Application Platform Deploy NSX Application Platform Explain the NSX Application Platform architecture and services Validate the NSX Application Platform deployment and troubleshoot common issues NSX Malware Prevention Identify use cases for NSX Malware Prevention Identify the components in the NSX Malware Prevention architecture Describe the NSX Malware Prevention packet flows for known and unknown files Configure NSX Malware Prevention for east-west and north-south traffic NSX Intelligence and NSX NDR Describe NSX Intelligence and its use cases Explain NSX Intelligence visualization, recommendation, and network traffic analysis capabilities Describe NSX NDR and its use cases Explain the architecture of NSX NDR in NSX Describe the visualization capabilities of NSX NDR Additional course details:Notes Delivery by TDSynex, Exit Certified and New Horizons an VMware Authorised Training Centre (VATC) Nexus Humans VMware NSX for Intrinsic Security [V4.x] training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the VMware NSX for Intrinsic Security [V4.x] course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.
![VMware NSX for Intrinsic Security [V4.x]](https://cademy-images-io.b-cdn.net/9dd9d42b-e7b9-4598-8d01-a30d0144ae51/4c81f130-71bf-4635-b7c6-375aff235529/original.png?width=3840)
A 40 minute overview of FLOCKS online Interior decor course
By FLOCK interiors
This 40 minute live chat allows you to get an overview of some of the key elements of Nikki’s 5 week online interior decor course from the comfort of your own home.So whether you just want to gain a better appreciation of the step by step process Nikki has devised, or are thinking about studying on one of her 5 week courses, this practical 40 minute zoom chat provides a compelling, comprehensive and enjoyable Introduction.
Cisco SD-WAN Cloud (SDWAN-CLD-CT)
By Nexus Human
Duration 5 Days 30 CPD hours Overview Upon completing this course, you will be able to meet the following objectives: SD-WAN Overview Cloud Concepts Cloud Technologies SD-WAN Direct Cloud Access (DCA) SD-WAN SaaS Cloud On-RAMP for IAAS (AWS) Cloud On-RAMP for IAAS (AZURE) Cloud Configuration for GCP Cloud On-RAMP for MULTI-CLOUD Cloud On-RAMP for CO-LOCATIONS This is a 5 day hands-on course on Cisco SD-WAN Cloud Configuration, Monitoring and Troubleshooting. This course provides the student with the knowledge to connect SD-WAN to SaaS Applications, as well as the ability to connect their Branches to AWS, AZURE, GCP Data Centers in the Cloud. Students will also learn how to Configure, Monitor, and Troubleshoot SD-WAN Co-Locations and SD-WAN Multicloud. SD-WAN Overview SD-WAN Controller SD-WAN WAN Edges supported in Cloud Instances Cloud Concepts Cloud Ops vs WAN Ops Cloud Connectivity Cloud Access Control Cloud Network Connectivity Cloud Regions Cloud Availability Zones Virtual Networks Cloud Routing Internet Gateways VS VPN Gateways VPC/VNET: IP Addressing Cloud Network Load Balancing Cloud Peering Cloud Transit Networks Cloud Technologies Azure Azure Basics Resource Groups vNets Availability zones Availability Set Workload and Public IP Network Virtual Appliance Load Balancer User Defined Routes Network Security Group VPN Gateway Express Routes Creating VNET for SDWAN AWS AWS Basics Region VPCs Availability zones Subnets EC2 Instance Elastic IPs Security Groups Internet Gateway NAT Gateway Route Table VPN Gateway Direct Connect Elastic Load Balancer Subscribe to Amazon machine images Setting AWS resource limits AWS Transit Gateways Creating VPC for SDWAN AWS IAM Role AWS Security Groups Service limits AWS SSH key pair Google Cloud GCP Basics Project Region Virtual Private Cloud Availability Zone Subnets Compute Engine Cloud Load Balancer Cloud DNS VPC Routing Cloud VPN & VPC peering VPC Firewall Rules SD-WAN Direct Cloud Access (DCA) DCA Prerequisites DNS on VPN 0 DIA Central Policy Configuration Match Traffic Set QOS Set External Access SD-WAN SaaS Supported Platforms and Versions SaaS Prerequisites DNS on VPN 0 DIA SaaS Access Methods Cloud Access through Direct Internet Access Links Cloud Access through a Gateway Site Hybrid Approach Supported SaaS Applications SaaS Security Options SaaS Configuration Common Scenarios for Using Cloud onRamp for SaaS Specify Office 365 Traffic Category Enable Cloud onRamp for SaaS, Cisco IOS XE SD-WAN Devices Configure Applications for Cloud onRamp for SaaS Using Cisco vManage Configure Sites for Cloud onRamp for SaaS Using Cisco vManage View Details of Monitored Applications Cloud On-RAMP for IAAS (AWS) Prerequisite AWS Configuration Verify prerequisites Configure AWS for Cisco SD-WAN Cloud On-RAMP for AWS Overview Define WAN Edge Type used Define Template Attach Devices to Template Deploy Cloud Onramp AWS IAM Role Select Region Select CPU and Memory Transit Networking IP Addresses Discover and Map Host VPCs AWS to SD-WAN Security Monitor Cisco Cloud Onramp for AWS Troubleshoot Cisco Cloud Onramp for AWS Interconnecting Cisco SD-WAN with AWS Transit Gateway (TGW) Cloud On-RAMP for IAAS (AZURE) Prerequisite AZURE Configuration Cloud On-RAMP for AZURE Configure AWS for Cisco SD-WAN Define WAN Edge Type used Define Template Attach Devices to Template Deploy Cloud Onramp Select Region Discover and Map Host VPCs Monitor Cisco Cloud Onramp for Azure Troubleshoot Cisco Cloud Onramp for AZURE Azure Virtual Wan (VWAN) Integration Cloud Configuration for GCP Prerequisite GCP Configuration SD-WAN Configuration Configure Google Cloud for SD-WAN Google Cloud GCP Basics Deploy cEdge Catalyst 8000V Edges Setup IPSEC Connections Setup BGP Connections Cloud On-RAMP for MULTI-CLOUD AWS Transit Gateway Microsoft vWAN Create Cisco Cloud GW Discover host VPCs/VNets Map Branch nets to VPCs Cloud On-RAMP for CO-LOCATIONS SD-WAN CO-LOCATIONS Overview Colocation facilities Cisco Colocation Equipment Cisco Cloud Services Platform 5444 Cisco Network Function Virtualization Infrastructure Software (NFVIS) Virtual Network Functions Network Fabric Cisco Catalyst 9500-48Y4C switch Cisco Catalyst 9500-40X switch Device Configuration and Connectivity Sizing the Colocation Solution Devices Cisco Colocation Manager Deploy Network Services at the Network Edge Colocation Solution?Deployment Workflow Monitor Cisco SD-WAN Colocation Devices Cisco Colocation Manager States for Switch Configuration Cisco Colocation Manager States and Transitions from Host Cisco Colocation Manager Notifications VM Alarms Cloud Services Platform Real-Time Commands Colocation High Availability Troubleshoot Cisco SD-WAN Cloud onRamp for Colocation Solution Troubleshoot Catalyst 9500 Issues Troubleshoot Cloud Services Platform Issues DHCP IP Address Assignment Troubleshoot Cisco Colo Manager Issues Troubleshoot Service Chain Issues Troubleshoot Physical Network Function Management Issues Log Collection from CSP Troubleshoot vManage Issues Additional course details: Nexus Humans Cisco SD-WAN Cloud (SDWAN-CLD-CT) training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the Cisco SD-WAN Cloud (SDWAN-CLD-CT) course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

AWS Developing Serverless Solutions on AWS
By Nexus Human
Duration 3 Days 18 CPD hours This course is intended for Developers who have some familiarity with serverless and experience with development in the AWS Cloud Overview In this course, you will learn to: Apply event-driven best practices to a serverless application design using appropriate AWS services Identify the challenges and trade-offs of transitioning to serverless development, and make recommendations that suit your development organization and environment Build serverless applications using patterns that connect AWS managed services together, and account for service characteristics, including service quotas, available integrations, invocation model, error handling, and event source payload Compare and contrast available options for writing infrastructure as code, including AWS CloudFormation, AWS Amplify, AWS Serverless Application Model (AWS SAM), and AWS Cloud Development Kit (AWS CDK) Apply best practices to writing Lambda functions inclusive of error handling, logging, environment re-use, using layers, statelessness, idempotency, and configuring concurrency and memory Apply best practices for building observability and monitoring into your serverless application Apply security best practices to serverless applications Identify key scaling considerations in a serverless application, and match each consideration to the methods, tools, or best practices to manage it Use AWS SAM, AWS CDK, and AWS developer tools to configure a CI/CD workflow, and automate deployment of a serverless application Create and actively maintain a list of serverless resources that will assist in your ongoing serverless development and engagement with the serverless community This course gives developers exposure to and practice with best practices for building serverless applications using AWS Lambda and other services in the AWS serverless platform. You will use AWS frameworks to deploy a serverless application in hands-on labs that progress from simpler to more complex topics. You will use AWS documentation throughout the course to develop authentic methods for learning and problem-solving beyond the classroom. Introduction Introduction to the application you will build Access to course resources (Student Guide, Lab Guide, and Online Course Supplement) Thinking Serverless Best practices for building modern serverless applications Event-driven design AWS services that support event-driven serverless applications API-Driven Development and Synchronous Event Sources Characteristics of standard request/response API-based web applications How Amazon API Gateway fits into serverless applications Try-it-out exercise: Set up an HTTP API endpoint integrated with a Lambda function High-level comparison of API types (REST/HTTP, WebSocket, GraphQL) Introduction to Authentication, Authorization, and Access Control Authentication vs. Authorization Options for authenticating to APIs using API Gateway Amazon Cognito in serverless applications Amazon Cognito user pools vs. federated identities Serverless Deployment Frameworks Overview of imperative vs. declarative programming for infrastructure as code Comparison of CloudFormation, AWS CDK, Amplify, and AWS SAM frameworks Features of AWS SAM and the AWS SAM CLI for local emulation and testing Using Amazon EventBridge and Amazon SNS to Decouple Components Development considerations when using asynchronous event sources Features and use cases of Amazon EventBridge Try-it-out exercise: Build a custom EventBridge bus and rule Comparison of use cases for Amazon Simple Notification Service (Amazon SNS) vs. EventBridge Try-it-out exercise: Configure an Amazon SNS topic with filtering Event-Driven Development Using Queues and Streams Development considerations when using polling event sources to trigger Lambda functions Distinctions between queues and streams as event sources for Lambda Selecting appropriate configurations when using Amazon Simple Queue Service (Amazon SQS) or Amazon Kinesis Data Streams as an event source for Lambda Try-it-out exercise: Configure an Amazon SQS queue with a dead-letter queue as a Lambda event source Writing Good Lambda Functions How the Lambda lifecycle influences your function code Best practices for your Lambda functions Configuring a function Function code, versions and aliases Try-it-out exercise: Configure and test a Lambda function Lambda error handling Handling partial failures with queues and streams Step Functions for Orchestration AWS Step Functions in serverless architectures Try-it-out exercise: Step Functions states The callback pattern Standard vs. Express Workflows Step Functions direct integrations Try-it-out exercise: Troubleshooting a Standard Step Functions workflow Observability and Monitoring The three pillars of observability Amazon CloudWatch Logs and Logs Insights Writing effective log files Try-it-out exercise: Interpreting logs Using AWS X-Ray for observability Try-it-out exercise: Enable X-Ray and interpret X-Ray traces CloudWatch metrics and embedded metrics format Try-it-out exercise: Metrics and alarms Try-it-out exercise: ServiceLens Serverless Application Security Security best practices for serverless applications Applying security at all layers API Gateway and application security Lambda and application security Protecting data in your serverless data stores Auditing and traceability Handling Scale in Serverless Applications Scaling considerations for serverless applications Using API Gateway to manage scale Lambda concurrency scaling How different event sources scale with Lambda Automating the Deployment Pipeline The importance of CI/CD in serverless applications Tools in a serverless pipeline AWS SAM features for serverless deployments Best practices for automation Course wrap-up Additional course details: Nexus Humans AWS Developing Serverless Solutions on AWS training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the AWS Developing Serverless Solutions on AWS course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

Coding (HTML, C++, Python, JavaScript & IT)
By NextGen Learning
Course Overview This comprehensive course on Coding (HTML, C++, Python, JavaScript & IT) offers a structured introduction to the world of coding and information technology. It covers an expansive array of programming languages and technologies, including HTML, CSS, JavaScript, C++, Python, and PHP, alongside key IT concepts such as cybersecurity, cloud computing, and network security. Learners will develop a deep understanding of programming logic, software development, web development, and essential IT operations. Whether you're aiming to explore programming for the first time or expand your technical skill set, this course equips you with the knowledge required to navigate modern computing systems and coding environments. Upon completion, learners will be better prepared to pursue roles in web development, programming, system administration, and IT support across various industries. Course Description This course delivers an in-depth exploration of both coding and IT fundamentals, offering a diverse curriculum that spans core programming languages such as HTML, C++, Python, JavaScript, and R. It extends into cybersecurity, Linux scripting, ethical hacking, and computer networking—creating a well-rounded foundation for digital fluency. Learners are introduced to the design and development of web applications, front-end and back-end technologies, and essential tools such as GitHub, Heroku, and MySQL. The course further includes IT administration, encryption methods, cloud infrastructure, and system troubleshooting, ensuring coverage of key concepts necessary in today’s tech-driven world. With a focus on conceptual clarity and structured progression, learners will gain valuable knowledge aligned with current industry needs and expectations. Course Modules Module 01: Introduction to Coding With HTML, CSS, & Javascript Module 02: C++ Development: The Complete Coding Guide Module 03: Python Programming: Beginner To Expert Module 04: Learn Ethical Hacking From A-Z: Beginner To Expert Module 05: Bash Scripting, Linux and Shell Programming Module 06: JavaScript Project – Game Development with JS Module 07: R Programming for Data Science Module 08: Secure Programming of Web Applications Module 09: Advanced Diploma in PHP Web Development with MySQL, GitHub & Heroku Module 10: The Complete Front-End Web Development Course! Module 11: The Complete MySQL Server from Scratch: Bootcamp Module 12: Cyber Security Awareness Training Module 13: Cloud Computing / CompTIA Cloud+ (CV0-002) Module 14: CompTIA A+ (220-1001) Module 15: Building Your Own Computer Module 16: Computer Networks Security from Scratch to Advanced Module 17: IT Administration and Networking Module 18: Encryption Module 19: Advance Windows 10 Troubleshooting for IT HelpDesk Module 20: Microsoft Excel Complete Course (See full curriculum) Who is this course for? Individuals seeking to understand programming languages and IT fundamentals. Professionals aiming to transition into coding or expand their IT knowledge. Beginners with an interest in computing, programming, or digital technologies. Students or career changers preparing for roles in the tech sector. Career Path Web Developer Software Programmer IT Support Technician Network Administrator Cybersecurity Analyst Cloud Computing Technician Data Analyst Systems Engineer Helpdesk Specialist IT Consultant
