- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
2187 Courses in Cardiff delivered Live Online
55133 PowerShell for System Center Configuration Manager Administrators
By Nexus Human
Duration 3 Days 18 CPD hours This course is intended for This course is intended for IT professionals who need to manage the day-to-day environment of an SCCM 2012 SP1 or newer environment. Knowledge of the workings of a standalone primary SCCM site and basic PowerShell experience is recommended. Overview Create additional site system roles on existing or new servers. Modify high level site settings. Create and modify Discovery Methods, Boundaries and Boundary Groups. Create Collections using any of the membership rules available. Delegate authority through Roles and Scopes. Install the Configuration Manager client, modify client settings and restrict access to site systems. Deploy software to clients. Deploy software updates to clients. Configure compliance settings targeted against collections. Modify settings that govern monitoring functions such as Alerts and Status Settings. Work with Task Sequences for Operating System Deployment. Write basic PowerShell scripts using cmdlets learned and scripting constructs to accomplish configuration tasks. This course provides students with the knowledge and skills needed to use PowerShell for System Center Configuration Manager (SCCM) administration. In this course, students learn how to access the PowerShell cmdlets included with SCCM 2012 R2 and use them to perform configuration tasks for a primary site. Individual cmdlets will be used in working with objects such as Boundaries, Boundary Groups, Collections, Software Deployment, Patching, Compliance Settings, OSD Task Sequences, and many others. Basic scripting will also be covered so that students can learn how to put PowerShell to use when working with large sets of objects. Prerequisites Basic Windows and Active Directory knowledge. Conceptual knowledge of Configuration Manager objects and how they interact. Basic experience performing configuration tasks in ECM using the graphical console. Experience working from a command prompt. Basic knowledge of the fundamentals of Windows PowerShell. 1 - REVIEW OF SYSTEM CENTER CONFIGURATION MANAGER CONCEPTS Architecture of an System Center 2012 Configuration Manager Installation Managing Assets Content Delivery and Management Security, Monitoring, and Remote Management 2 - MANAGING RESOURCES Implementing Discovery Organizing Resources with Collections Working with Boundaries 3 - WORKING WITH CLIENTS Installing the Configuration Manager Client Managing Client Settings Managing Client Operations Monitoring Client Status 4 - DISTRIBUTING SOFTWARE Configure the Software Distribution Components Working with Distribution Points Creating Content for Distribution Deploying Software Applications 5 - UPDATING SYSTEMS WITH WSUS AND SCCM Integrating Configuration Manager and WSUS Managing Updates through Software Update Groups Creating and Deploying Update Packages Working with Automatic Deployment Rules 6 - HOW POWERSHELL CAN MANAGE COMPLIANCE SETTINGS Creating Compliance Settings Objects Deploying and Monitor the Baseline 7 - CONFIGURING OPERATING SYSTEM DEPLOYMENT OBJECTS Preparing the OSD Environment Working with Task Sequences 8 - WORKING AT THE SITE LEVEL Modify the Site Adding Site System Roles Adding a Secondary Site 9 - SECURITY AND MONITORING Configuring Role Based Administration Implementing Endpoint Protection Configuring Monitoring Options 10 - USING POWERSHELL SCRIPTING TO AUTOMATE SCCM TASKS Review of Scripting Constructs Introduction to the Configuration Manager WMI Classes

PMI-PBA Exam Prep: In-House Training
By IIL Europe Ltd
PMI-PBA® Exam Prep: In-House Training The course provides targeted exam preparation support for PMI®'s Professional in Business Analysis exam candidates, including a content review of The PMI Guide to Business Analysis, a review of the PMI-PBA® reference books, and an exam preparation tutorial. You will be given a Study Guide that you can re-use to assess your knowledge gaps as part of your Personal Action Plan. Your score on this for each Knowledge Area can be compared to your results on the quiz at the end of each course module to guide your study efforts. What you will Learn Upon completion, participants will be able to: Demonstrate familiarity with the structure, content and framework of The PMI Guide to Business Analysis Explain the six Knowledge Areas of The PMI Guide to Business Analysis, as well as, their inter-relationships with each other and the six Process Groups Differentiate among the five business analysis domains in the project life cycle Create a personal action plan to study and prepare for the PMI-PBA® Exam Getting Started PMI-PBA Examination Certification Process The Credential Examination Foundation Concepts for PMI-PBA® Prep Business analysis terminology and definitions Business analysis project, program, and portfolio management Product and project life cycles Skills and qualities of a business analyst Introduction to Business Analysis in Projects Business analysis overview How organizations implement business analysis Business analyst and project manager relationships Requirements definitions and types Practice quiz On-Demand Segment A: Define the Business Problem (Pre-work for Needs Assessment) Needs Assessment Review Needs Assessment knowledge area Identify problem or opportunity Assess current and future state Determine options and provide recommendations Facilitate product roadmap development Assemble business case Practice quiz Stakeholder Engagement Review Stakeholder Engagement knowledge area Identify Stakeholders and conduct analysis Determine Stakeholder engagement and communication approach Conduct business analysis planning Practice quiz On-Demand Segment B: The Elicitation Plan (Pre-work for Elicitation) Elicitation Review Elicitation knowledge area Determine Elicitation approach Preparing for Elicitation Conducting Elicitation Confirming Elicitation results Practice quiz On-Demand Segment C: Overview of Requirements Analysis (Pre-work for Analysis) Analysis Review Analysis knowledge area Determine Analysis approach Create and analyze models Define requirements and acceptance criteria Verify, validate, and prioritize requirements Identify and analyze product risks Assess product design options Practice quiz Traceability and Monitoring Review Traceability and Monitoring knowledge area Determine Traceability and Monitoring approach Establish relationships and dependencies Select and approve requirements Make changes to requirements and other product information Practice quiz Solution Evaluation Review Solution Evaluation knowledge area Evaluate solution performance Determine solution evaluation approach Evaluate acceptance results and address defects Obtain solution acceptance for release Practice quiz Exam Application and Preparation Process Applying for the Exam Studying for the Exam Sitting for the Exam Reviewing your Knowledge Gap Practice Exam Study Guide - a reliable learning aid Summary and Next Steps Crystallizing the Business Analysis Domains Developing a Personal Action Plan for Exam Study

Essential DHCP training course description Almost all businesses use DHCP. This course builds on delegates existing IP knowledge and focuses on IP Address management using DHCP. Also covered is the role of DHCP in plug and play environments. What will you learn Explain how DHCP works. Configure DHCP servers. Troubleshoot DHCP. Essential DHCP training course details Who will benefit: Anyone working with TCP/IP. Prerequisites: TCP/IP Foundation for engineers Duration 1 day Essential DHCP training course contents Introduction What is DHCP?, IP configuration: Address, mask, default gateway, DNS. History of DHCP: RARP, BOOTP. Hands on Client configuration, releasing and renewing. DHCP servers Installation. Base configuration: Scope. Lease period. DHCP options. Hands on Server setup, Impact of lease times. Server monitoring. How DHCP works Client states. Obtaining, renewing leases. DHCP messages: DISCOVER, OFFER, REQUEST, NAK, ACK, DECLINE, RELEASE, INFORM. Hands on Troubleshooting DHCP using Wireshark. DHCP architecture DHCP relay agents. Server platforms, resilience, DHCP fail over, split scopes. Dynamic DNS and DHCP. Hands on DDNS, routers, Troubleshooting.

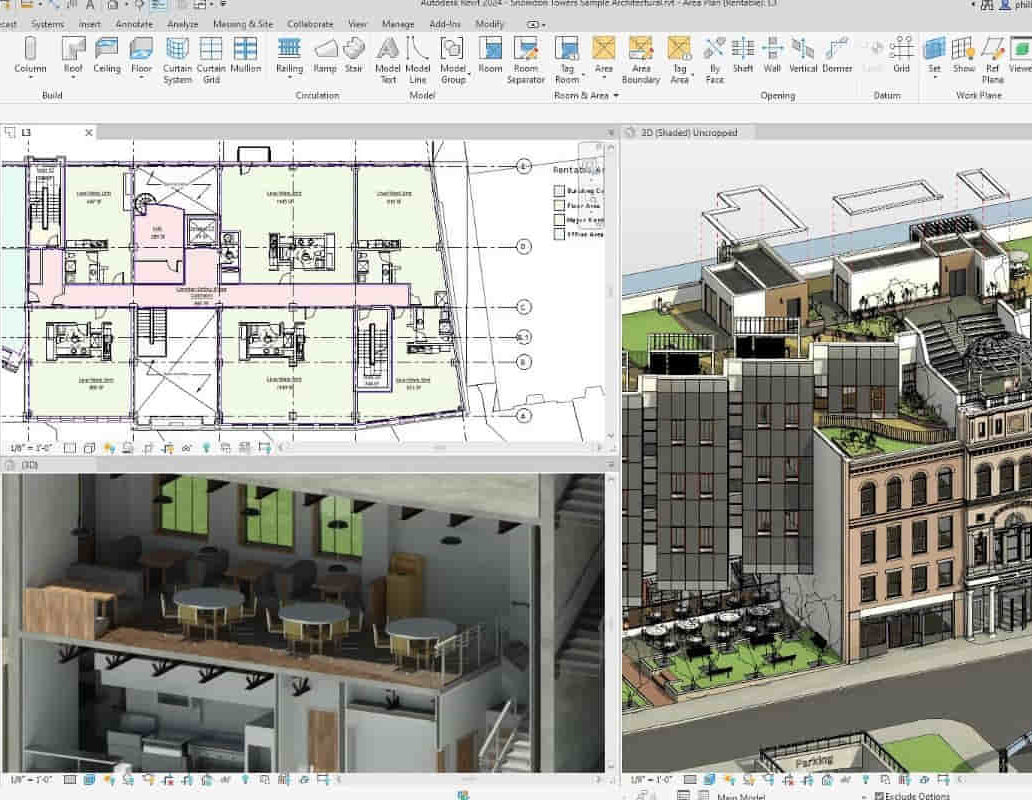
Revit V-Ray 3ds Max Visualization Training Course
By ATL Autocad Training London
Why Learn Revit V-Ray 3ds Max Visualization Training Course? Revit is perfect for architecture, and 3ds Max, with V-Ray rendering, offers super results. Autodesk Revit Interoperability integrates Revit and 3ds Max seamlessly, combining metadata, materials, and lighting. Architects and designers using 3ds Max tools for architectural designs. Check our Website Booking: 1-on-1 Duration: You can split these 40 hours over as many days, Mon to Sat between 9 am to 7 pm, or call 02077202581 to book In-person or Live Online Module 1: Revit Fundamentals (16 hours) Introduction to Revit: Acquaint yourself with Revit's essential concepts and tools. Interface and Workspace: Navigate Revit's interface and workspace seamlessly. Building Information Modeling (BIM) Workflow: Grasp the fundamental BIM workflow principles for effective modeling. Basic Building Model Creation: Learn to craft a foundational building model using Revit. Basic Modeling Techniques: Master elements like walls, doors, windows, floors, roofs, stairs, and railings. Advanced Revit Modeling: Dive into advanced topics, including family creation and working with intricate geometries. Annotation and Documentation: Enhance your projects with text, dimensions, schedules, and efficient printing/exporting methods. Module 2: 3ds Max Mastery (16 hours) Introduction to 3ds Max: Familiarize yourself with the core aspects and interface of 3ds Max. 3D Modeling Workflow: Understand the intricacies of creating basic 3D models in 3ds Max. Basic 3D Modeling Techniques: Work with primitive shapes, splines, and create complex 3D models. Materials and Textures: Explore the material editor, apply materials, and craft realistic textures. Lighting and Cameras: Learn to illuminate scenes, utilize the daylight system, and optimize camera angles. Module 3: V-Ray Rendering Proficiency (8 hours) Introduction to V-Ray: Grasp the fundamentals of V-Ray, including its interface and workflow. V-Ray Materials and Textures: Understand the intricacies of V-Ray materials and textures for lifelike renderings. Basic Rendering Techniques: Dive into essential rendering techniques, including lighting adjustments and global illumination. Advanced Rendering Methods: Explore advanced techniques to elevate the quality of your renders. Gain expertise in Revit, 3ds Max, and V-Ray through our comprehensive training, mastering the core concepts and advanced techniques necessary for stunning architectural visualizations. Upon completing the course, you will: Master Architectural Modeling: Proficiently create intricate architectural models using Revit and 3ds Max. Visualize Realistically: Utilize advanced rendering techniques in V-Ray for lifelike visualizations with realistic lighting and materials. Efficient Documentation: Learn annotation and documentation skills for clear and effective project communication. Enhance Collaboration: Understand file interoperability for seamless collaboration with diverse software platforms. Build a Professional Portfolio: Create a diverse portfolio showcasing your skills in architectural visualization. Career Opportunities: Upon completion, you can pursue roles such as: Architectural Visualizer 3D Modeler Render Artist BIM Specialist Freelancer/Consultant Architectural Technician Visualization Trainer Mastering these tools opens doors to versatile career opportunities in architectural visualization. Download Revit Download 3ds max Download Vray Revit and 3dsMax V-Ray Visualization Training: Master architectural visualization with our intensive course blending Revit, 3dsMax, and V-Ray. Dive into modeling, materials, lighting, and rendering for photorealistic results. Course Highlights: Comprehensive Learning: Cover fundamental and advanced techniques in Revit and 3dsMax, enhancing your visualization skills. V-Ray Expertise: Explore advanced V-Ray rendering techniques, from global illumination to realistic material creation. Real-World Projects: Work on industry-relevant projects, building a portfolio of professional-grade visualizations. Flexible Learning: Choose in-person or live online sessions for interactive instruction and engaging discussions. Lesson Recordings: Access session recordings to review concepts, reinforcing your learning at your own pace. Lifetime Support: Enjoy lifetime email support for ongoing guidance from experienced instructors, ensuring your success beyond the course. Enroll now to transform your architectural designs into captivating visualizations, impressing clients with your skills and creativity. Join our training for a comprehensive learning experience, enhancing your expertise in Revit, 3dsMax, and V-Ray. Revit | 3ds max | V-Ray Course Benefits: Comprehensive Skill Set: Master Revit, 3dsMax, and V-Ray for exceptional architectural visualization, from basic modeling to advanced rendering. Realistic Rendering: Harness V-Ray's capabilities for lifelike visuals, covering global illumination, materials, and textures. Practical Experience: Work on industry-relevant projects, building a professional portfolio with hands-on exercises. Flexible Learning: Choose in-person or live online sessions for interactive instruction and discussion, tailored to your preferences. Review Resources: Access recorded class sessions to reinforce your knowledge and skills at your convenience. Lifetime Support: Enjoy lifetime email support from experienced instructors, ensuring ongoing guidance for your projects.
Level 1 Award in Motor Vehicle Studies - OFQUAL Accredited (RQF)
By Evo Education and Training Centre
The Level 1 Award in Motor Vehicle Studies is designed to encourage and enable learners who have an interest in this area of study to acquire knowledge and skills to aid progression to further study or employment.

Portfolio, Programs, & Project Offices Practitioner: In-House
By IIL Europe Ltd
Portfolio, Programme, and Project Offices (P3O®) Practitioner: In-House Training P3O® is the AXELOS standard for the design of decision-making processes regarding changes in organizations. P3O provides a guideline for the design of portfolio, programme, and project offices in organizations. The P3O Practitioner Course is an interactive learning experience. The P3O Practitioner-level content provides you with sufficient knowledge and understanding of the P3O guidance to design, implement, manage or work within any component office of a P3O model. It enables participants to successfully complete the associated P30 Practitioner exam and achieve the qualification. In this course, you will be prepared to successfully attempt the P3O Practitioner exam and learn how to implement or re-energize a P3O model in their own organization. What you will Learn At the end of the P3O Practitioner course, you will be able to: Define a business case to get senior management approval for P3O Build a right P3O model to adapt to the organization's needs, taking account of the organization's size and portfolio, programme and project management maturity Identify the elements, roles, and functions deployed in a generalized P3O model Use tools and techniques in running the P3O and advising those who shape the portfolio of programmes and projects Introduction to P3O What is the purpose of P3O? Definitions What are P3Os? Portfolio, programme, and project lifecycles Governance and the P3O Designing a P3O Model Factors that affect the design Design considerations What functions and services should the P3O offer? Roles and responsibilities Sizing and tailoring of the P3O model Why have a P3O? How a P3O adds value Maximizing that value Getting investment for the P3O Overcoming common barriers Timescales Why have a P3O (Extension)? The P3O Business Case The P3O Model Blueprint Vision Statement Demonstrating the Value KPIs The Benefits of Claimed Capabilities Benefit Realisation and Strategic Objectives Benefit Profile How to Implement or Re-Energize a P3O Implementation lifecycle for a permanent P3O Identify Define Deliver Close Implementation lifecycle for a temporary programme or project office Organizational context Definition and implementation Running Closing Recycling How to operate a P3O Overview of tools and techniques Benefits of using standard tools and techniques Critical success factors P3O tools P3O techniques

EC-Council Certified Ethical Hacker (CEH) v12
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for The Certified Ethical Hacking v12 course will significantly benefit security officers, auditors, security professionals, site administrators, and anyone who is concerned about the integrity of the network infrastructure. Overview Information security controls, laws, and standards. Various types of footprinting, footprinting tools, and countermeasures. Network scanning techniques and scanning countermeasures Enumeration techniques and enumeration countermeasures Vulnerability analysis to identify security loopholes in the target organization?s network, communication infrastructure, and end systems. System hacking methodology, steganography, steganalysis attacks, and covering tracks to discover system and network vulnerabilities. Different types of malware (Trojan, Virus, worms, etc.), system auditing for malware attacks, malware analysis, and countermeasures. Packet sniffing techniques to discover network vulnerabilities and countermeasures to defend against sniffing. Social engineering techniques and how to identify theft attacks to audit human-level vulnerabilities and social engineering countermeasures. DoS/DDoS attack techniques and tools to audit a target and DoS/DDoS countermeasures. Session hijacking techniques to discover network-level session management, authentication/authorization, and cryptographic weaknesses and countermeasures. Webserver attacks and a comprehensive attack methodology to audit vulnerabilities in webserver infrastructure, and countermeasures. Web application attacks, comprehensive web application hacking methodology to audit vulnerabilities in web applications, and countermeasures. SQL injection attack techniques, injection detection tools to detect SQL injection attempts, and countermeasures. Wireless encryption, wireless hacking methodology, wireless hacking tools, and Wi-Fi security tools. Mobile platform attack vector, android vulnerability exploitations, and mobile security guidelines and tools. Firewall, IDS and honeypot evasion techniques, evasion tools and techniques to audit a network perimeter for weaknesses, and countermeasures. Cloud computing concepts (Container technology, serverless computing), the working of various threats and attacks, and security techniques and tools. Penetration testing, security audit, vulnerability assessment, and penetration testing roadmap. Threats to IoT and OT platforms and defending IoT and OT devices. Cryptography ciphers, Public Key Infrastructure (PKI), cryptography attacks, and cryptanalysis tools. CEH provides an in-depth understanding of ethical hacking phases, various attack vectors, and preventative countermeasures. It will teach you how hackers think and act maliciously so you will be better positioned to setup your security infrastructure and defend against future attacks. An understanding of system weaknesses and vulnerabilities helps organizations strengthen their system security controls to minimize the risk of an incident. CEH was built to incorporate a hands-on environment and systematic process across each ethical hacking domain and methodology, giving you the opportunity to work towards proving the required knowledge and skills needed to achieve the CEH credential. You will be exposed to an entirely different posture toward the responsibilities and measures required to be secure. Now in its 12th version, CEH continues to evolve with the latest operating systems, tools, tactics, exploits, and technologies. 1 - Introduction to Ethical Hacking Information Security Overview Cyber Kill Chain Concepts Hacking Concepts Ethical Hacking Concepts Information Security Controls Information Security Laws and Standards 2 - 2 - Foot-printing and Reconnaissance Footprinting Concepts Footprinting through Search Engines Footprinting through Web Services Footprinting through Social Networking Sites Website Footprinting Email Footprinting Who is Footprinting DNS Footprinting Network Footprinting Footprinting through Social Engineering Footprinting Tools Footprinting Countermeasures 3 - Scanning Networks Network Scanning Concepts Scanning Tools Host Discovery Port and Service Discovery OS Discovery (Banner Grabbing/OS Fingerprinting) Scanning Beyond IDS and Firewall Draw Network Diagrams 4 - Enumeration Enumeration Concepts NetBIOS Enumeration SNMP Enumeration LDAP Enumeration NTP and NFS Enumeration SMTP and DNS Enumeration Other Enumeration Techniques Enumeration Countermeasures 5 - Vulnerability Analysis Vulnerability Assessment Concepts Vulnerability Classification and Assessment Types Vulnerability Assessment Solutions and Tools Vulnerability Assessment Reports 6 - System Hacking System Hacking Concepts Gaining Access Escalating Privileges Maintaining Access Clearing Logs 7 - Malware Threats Malware Concepts APT Concepts Trojan Concepts Virus and Worm Concepts Fileless Malware Concepts Malware Analysis Countermeasures Anti-Malware Software 8 - Sniffing Sniffing Concepts Sniffing Technique: MAC Attacks Sniffing Technique: DHCP Attacks Sniffing Technique: ARP Poisoning Sniffing Technique: Spoofing Attacks Sniffing Technique: DNS Poisoning Sniffing Tools Countermeasures Sniffing Detection Techniques 9 - Social Engineering Social Engineering Concepts Social Engineering Techniques Insider Threats Impersonation on Social Networking Sites Identity Theft Countermeasures 10 - Denial-of-Service DoS/DDoS Concepts DoS/DDoS Attack Techniques BotnetsDDoS Case Study DoS/DDoS Attack Tools Countermeasures DoS/DDoS Protection Tools 11 - Session Hijacking Session Hijacking Concepts Application Level Session Hijacking Network Level Session Hijacking Session Hijacking Tools Countermeasures 12 - Evading IDS, Firewalls, and Honeypots IDS, IPS, Firewall, and Honeypot Concepts IDS, IPS, Firewall, and Honeypot Solutions Evading IDS Evading Firewalls IDS/Firewall Evading Tools Detecting Honeypots IDS/Firewall Evasion Countermeasures 13 - Hacking Web Servers Web Server Concepts Web Server Attacks Web Server Attack Methodology Web Server Attack Tools Countermeasures Patch Management Web Server Security Tools 14 - Hacking Web Applications Web Application Concepts Web Application Threats Web Application Hacking Methodology Web API, Webhooks, and Web Shell Web Application Security 15 - SQL Injection SQL Injection Concepts Types of SQL Injection SQL Injection Methodology SQL Injection Tools Evasion Techniques Countermeasures 16 - Hacking Wireless Networks Wireless Concepts Wireless Encryption Wireless Threats Wireless Hacking Methodology Wireless Hacking Tools Bluetooth Hacking Countermeasures Wireless Security Tools 17 - Hacking Mobile Platforms Mobile Platform Attack Vectors Hacking Android OS Hacking iOS Mobile Device Management Mobile Security Guidelines and Tools 18 - IoT and OT Hacking IoT Hacking IoT Concepts IoT Attacks IoT Hacking Methodology IoT Hacking Tools Countermeasures OT Hacking OT Concepts OT Attacks OT Hacking Methodology OT Hacking Tools Countermeasures 19 - Cloud Computing Cloud Computing Concepts Container Technology Serverless Computing Cloud Computing Threats Cloud Hacking Cloud Security 20 - Cryptography Cryptography Concepts Encryption Algorithms Cryptography Tools Public Key Infrastructure (PKI) Email Encryption Disk Encryption Cryptanalysis Countermeasures Additional course details: Nexus Humans EC-Council Certified Ethical Hacker (CEH) v.12 training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the EC-Council Certified Ethical Hacker (CEH) v.12 course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

Training Course for Architects & Interior Exterior Designers
By Real Animation Works
1-2-1 face to face training customised and bespoke.

Sketchup and Stable Diffusion Rendering Course
By Real Animation Works
1-2-1 bespoke training course

DWDM training course description A concise overview of Wave Division Multiplexing (WDM) with both Coarse Wave Division Multiplexing (CWDM) and Dense Wave Division Multiplexing (DWDM) being covered. The course starts with a review of the relevant elements of fibre transmission and multiplexing before then studying WDM components and architectures. Reliability, resilience and management are then followed by WDM services and futures. What will you learn Explain the benefits of WDM. Describe Dispersion and four way mixing. Describe the different WDM equipment components. Describe different WDM architectures. Explain How DWDM works. DWDM training course details Who will benefit: Anyone working with CWDM/DWDM. Prerequisites: Telecommunications Introduction Duration 2 days DWDM training course contents Fibre communications review Optical transmission, Fibre characteristics, Fibre component parts. Multi Mode Fibre (MMF). Single Mode Fibre (SMF). Fibre connections. Lasers. Attenuations, dispersion, optical signal noise ratios (OSNR) and their effects. Channel Spacing and Signal Direction. Limiting factors to single wavelength. WDM overview Multiplexing, TDM, WDM benefits. WDM standards. CWDM vs. DWDM. Four Wave Mixing (FWM). Impact and countermeasures to FWM on WDM. CWDM ITU G.694.2, channels, channel spacing. DWDM ITU G.694.1, channels, channel spacing. WDM Equipment Components Equipment components and building blocks. Optical Terminal Multiplexers (OTM). Optical Add/Drop Multiplexers (OADM). Adding versus dropping. Optical Amplifiers. Erbium Doped Fibre Amplifiers (EDFA). Transponders and Combiners. WDM/DWDM Hubs. Optical and Electrical Cross Connects (OXCs/DXCs). Types of Cross Connects (Transparent/Opaque). Advantages and disadvantages of various Optical cross connects. WDM Architectures WDM network sections. Point-to-Point, Optical switches, mesh, ring and star topology. Example of combined WDM and other technology network. Wavelength converting transponders, 1R, 2R, 3R. Protection for WDM Sub 50ms failover. Equipment protection. Card protection. Y cable, Splitter protection. Far end laser control. Line protection. OMSP 1+1, OMSP 1:1, OMSP 1: N. Self healing optical ring. Sub Network Connection Protection (SNCP). Automatically Switched Optical Networks (ASON). WDM Management Options In band management. Out of band management. The Optical Supervisory Channel (OSC). OSC capabilities. WDM services WDM Access. Bit rates, Transparent Networks. Modulation, DQPSK. SDH over WDM. Migrating from SDH to DWDM. Ethernet over WDM, IP over WDM. Optical Transport Networks G.709, 'digital wrapper', Optical Channel Payload Unit (OPU), Optical Channel Transport Unit ( OTU), Optical Channel Data Unit (ODU). OTU1, OTU2, OTU3, OTU4. WDM Futures All optical amplification, Raman amplification, distributed, lumped. Bit rates. Solitons. Coherent technologies.
