- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
1613 Courses in Cardiff delivered Live Online
Overview With the major responsibility of managing finances, managers have also responsibilities to write and control budgets. They face a number of decisions that need planning and forecasting, especially preparing budgets. Using examples and exercises from the gas and oil industry, this course is designed to break down all sorts of financial restrictions in an informative yet engaging style. It will provide the necessary skills to develop efficient strategic planning, forecasting and budgeting processes. The main aim of the training is to enable the participants to understand the framework that builds strategies for annual budgets targeting efficient management and organisational performance. Our course will explain financial terms and budgeting tools in such a way that a financial professional or even a non-financial profession will be able to understand and relate to in their working environment. It will include a lot of examples, a budgeting format and case studies.

Overview In this course you will learn to build a financial model by working in Excel and how to perform sensitivity analysis in Excel. You will also learn the formulas, functions and types of financial analysis to be an Excel power user. By attending this course, you will be able to effectively prepare and build financial models. Objectives Harness Excel's tools within a best practice framework Add flexibility to their models through the use of switches and flexible lookups Work efficiently with large data volumes Model debt effectively Approach modelling for tax, debt, pensions and disposals with confidence Build flexible charts and sensitivity analysis to aid the presentation of results Learn and apply Excel tools useful in financial forecasting Understand and design the layout of a flexible model Forecast financial statements of a public or private company Apply scenario analysis to the forecasted financial statements and prepare charts for data presentation

Overview This course will provide you with the skills and knowledge required by Non-Accounts Managers to understand Finance and Accounting processes they face in their daily work schedule. The main objective of this course is to highlight accounting, understand the framework of accounting, and stages of accounts and also to elaborate rules and principles of accounting. With a lot of Case studies and open discussions with live examples, participants will gain detailed knowledge to understand their company from a financial perspective and also to help manage financial matters. At the end of the course, you will learn how to apply financial techniques, understand financial reports and annual reports, the relationship between accounting and finance thereby gaining knowledge of the use of debits and credits and last but not least to identify limitations of financial statements. At the end of this training course, participants will: Be able to Record Transactions in the Accounting System Understand the Format and Contents of Financial Statements Use Accounting Information to Interpret and Evaluate a Business Make Efficient and Profitable Decisions, based on Cost Information Apply Budgetary Control Techniques to ensure that Targets are Achieved

Climate science workshop - Climate Fresk
By The C Collective
Join a Climate Fresk Climate science workshop to learn about the causes and effects of climate change through a fun and collaborative experience.

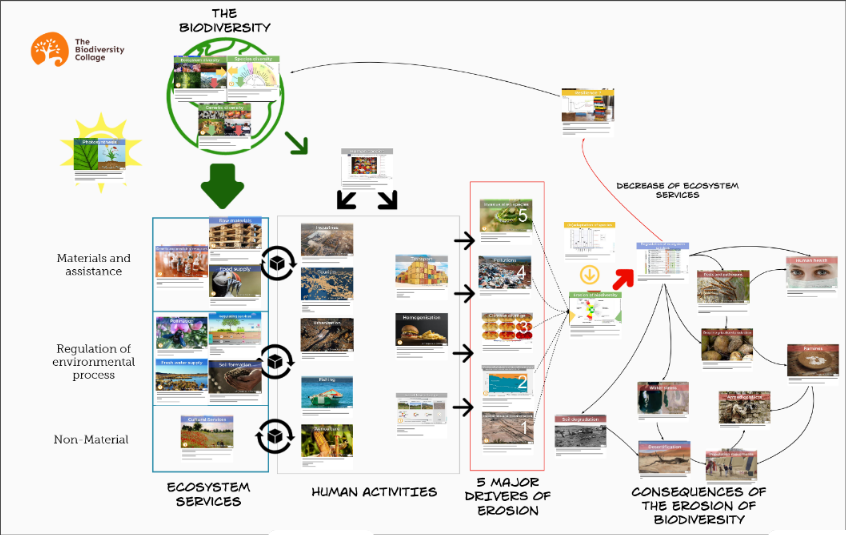
Biodiversity training - Biodiversity collage workshop
By The C Collective
Join a Biodiversity collage workshop to learn about the biodiversity crisis and how to tackle it.
What does this course cover? This is an online course for developing history leadership in primary teaching. This term, we will be piloting the course as an immersive programme covering the key elements of primary history subject leadership, enabling all involved in history leadership at primary to carry out their role effectively. How is this course structured and delivered? Sessions 1, 8 and 10 are compulsory to attend live. Participants will be required to complete a gap task after each session and contribute to an online reflection diary. The other sessions will be recorded for participants to work through at their convenience. Who is this course for? This programme is designed for anyone who is a subject coordinator or subject leader for history in their primary school. You may have just been appointed as a subject leader, or be more experienced but looking for formal training or fresh inspiration and direction. What are the outcome? This course will: equip you fully for the demands of history leadership in primary schools increase your confidence to develop an innovative, inclusive and effective history curriculum in your school develop your understanding of efficient action planning and how to make a wider impact help you to make the case for history with senior leaders enable you to enthuse others and lead staff meetings about history develop your understanding of current issues in primary history education The course will include a chance to share resources and assessment approaches, plus much more What will each session cover? Session 1: Introductory meeting (Live attendance) Wednesday 15 October 2025, 4pm–5.30pm Introduction and aims Reflection activity on the current state of history in your school Key responsibilities of the history subject leader Current Ofsted implications for the subject and what to expect in an inspection How the HA and latest Ofsted material can support you Session 2: What makes an effective history subject leader? (Recorded) How to effectively support teachers and learners as a history leader How to create a vision, lead change, and manage time Effective action planning and improvement Auditing your history provision and building your evidence trail Developing an innovative, inclusive and effective history curriculum in your school Disciplinary knowledge: What is history? What do historians do? Suggested gap task: Conducting teacher and/or pupil voice questionnaires. Compulsory gap task: Add to your reflection diary for the programme. If relevant, reflect on how you will use the teacher questionnaire or pupil voice. Session 3: What makes effective teaching of history? (Recorded) The role of the teacher Supporting SEND pupils Securing substantive knowledge and concepts across the curriculum How to support colleagues by identifying core knowledge How to involve the whole staff in mapping out and embedding the progression of concepts across the curriculum Suggested gap task: Consider SEND in your curriculum. Compulsory gap task: Add to your reflection diary for the programme reflecting on SEND. Session 4: Curriculum and practice at EYFS (Recorded) Unpicking and supporting the requirements of the EYFS curriculum and Development Matters Developing historical and chronological understanding in EYFS as part of Understanding the world Progression and transition from EYFS to Key Stage 1 Ensuring coherence: how to start developing concepts Making use of the local history on your doorstep for EYFS and KS1 Accessing resources and support for EYFS Suggested gap task: Fact finding and liaison. Compulsory gap task: Add to your reflection diary for the programme reflecting on current EYFS practice. Session 5: Curriculum and practice at Key Stage 1 (Recorded) Unpicking and supporting the requirements of the National Curriculum for KS1 Progression: building upon transition from EYFS What do KS1 require before KS2? Ensuring coherence: further developing the school’s chosen substantive concepts How to develop disciplinary concepts Developing appropriate chronological understanding in KS1 Enhancing and engaging children’s knowledge and retention through enquiry The use of working walls in KS1 to support learning Accessing resources and support for KS1 Suggested gap task: Check your KS1 curriculum for coverage and progression, building upon what they have learnt in EYFS. Compulsory gap task: Add to your reflection diary for the programme reflecting on KS1 practice in your setting. Session 6: Curriculum and practice at Key Stage 2 (Recorded) Unpicking and supporting the requirements of the National Curriculum for KS2 How to incorporate local history with progression in KS2 What do we want the children in Year 6 to leave with? Developing appropriate chronological understanding in KS2 Preparing for transition to Key Stage 3 Ensuring coherence: building upon the school’s chosen concepts for progression What the HA can do to support the teaching of KS2 units? Resources and support for KS2 Suggested gap task: Check your KS2 curriculum for coverage and progression, building upon what they have learnt in EYFS and KS1. Compulsory gap task: Add to your reflection diary for the programme reflecting on KS2 practice in your setting. Session 7: Approaching sensitive issues in history (Recorded) What do we mean by diversity in history and why is it important? How to ensure a wider diversity in your history teaching Barriers to making the curriculum more diverse and how to overcome them Approaches to sensitive issues in history lessons, including: - Refugees and migration history - War - Climate change Suggested gap task: Consider opportunities for increasing diverse voices and raising climate issues in your curriculum. Compulsory gap task: Add to your reflection diary for the programme considering how you might address the sensitive or current issues raised in this session. Session 8: Interim review meeting (Live attendance) Monday 19 January 2026, 4pm–5.30pm A review session allowing subject leaders to reflect upon their progress so far Opportunity to respond to suggestions, clarify information, or raise issues from the previous sessions Time to ask questions, share good practice or recommended resources with the rest of the cohort Suggested gap task: Time to follow up on anything raised in this session or to complete any previous tasks, following clarification and inspiration from this session. Compulsory gap task: Add to your reflection diary for the programme, reflecting on your priorities and actions using suggestions from the presenter or other delegates. Session 9: Assessment and evidence (Recorded) Assessment and expectations A word about writing Triangulating the evidence What to look for in a work scrutiny Suggested gap task: Conduct a work scrutiny on one aspect to check across the school, in conjunction with a focused pupil voice on the same aspect. Compulsory gap task: Add to your reflection diary considering how you will conduct a work scrutiny and what you will focus on – or, if relevant, reflect on what you discovered and how you will address any issues. Session 10: Final meeting (Live attendance) Wednesday 11 February 2026, 4pm–5.30pm Following up any requests arising from the interim meeting (Session 8) Discussion or clarification of any issues arising from previous sessions Discussion of priorities, next steps and any issues Sharing ideas for enthusing others and leading staff meetings: “What worked for me?” Communicating with headteachers, governors, colleagues and parents Are you ready for the HA Quality Mark? Suggested gap task: Identifying your school’s next steps Compulsory gap task: Complete your final piece in your reflection diary.

Prospect Maturation
By EnergyEdge - Training for a Sustainable Energy Future
About this Training Course The prospect maturation process, from a lead to a drillable prospect, is at the heart of the exploration business. This 5 full day course will cover all aspects of the prospect maturation process: play understanding in the context of regional geological understanding, detailed prospect evaluation; realistic risk & volume assessment consistent with the play understanding and prospect details, and an introduction to exploration economics. Throughout the course, there is a strong focus on pragmatic (geo)logical approach for assessing those aspects that are input parameters for a meaningful assessment of prospect risks and volumes, with emphasis on a balanced integration of contributions from different sub-surface disciplines. Many examples from basins from around the world are used to illustrate how traps, reservoirs, seals and charge occur in different basin settings. Specifics topics that will be discussed include the following: The statistical fundamentals for risk and volume assessment will be presented, with practical exercises for understanding the results of a risk & volume assessment as they are displayed in expectation curves. The difference between risk and uncertainty. A full discussion of the essential requirements for a working petroleum system: Trap, reservoir, seal and charge. Examples of how traps, reservoirs, seals and charge work in different basin types around the globe and in Australian basins. Exercises and guidelines for estimating uncertainties for prospect parameters, including advice for deciding which distribution type to use, and how to constrain those distributions for meaningful uncertainty ranges (setting minimum most likely and maximum values). Particular emphasis will be given to estimating hydrocarbon column lengths with their associated uncertainties in undrilled prospects. Prospects and plays: The value of play maps and how these should be used for assessment of prospect risks and for ranking of prospects within a play. Calculating volume ranges for prospects. Calculating volumes for groups of prospects; how to add risked prospect volumes for a statistically correct representation of the volume promise of a portfolio of prospects. Geophysical evidence: Incorporating geophysical evidence (DHIs) consistently and realistically in a risk assessment. An understandable and geology-based workflow, consistent with Bayes theorem, will be presented. Exploration economics. Training Objectives What this course will cover in 5 days: This course describes the various aspects that need to be considered in the prospect maturation process, including: Play development in the context of a sound understanding of the regional geology Detailed prospect evaluation and understanding of the critical aspects of traps, reservoirs, seals and charge Examples from plays and prospects in different basin settings from around the globe Realistic and pragmatic risk and volume assessment, based on the geological understanding of plays and prospects An introduction to exploration economics Examples of plays, oil and gas fields and prospects from basins from around the world, including the Far East, will be given. Target Audience This course is designed primarily for Geoscientists in exploration who would like to improve their expertise of the prospect maturation process and risk and volume assessment. The course has proven to be of value for explorers in the early phase of their career, seasoned explorers and team leaders. It will also benefit staff from disciplines working closely with exploration staff including Prospect Portfolio Analysts, Petrophysicists, Geophysicists and Reservoir Engineers. Course Level Intermediate Training Methods At the end of the course, the participants will have a good understanding of the essentials for realistic risk and volume assessments of exploration prospects. The course should allow participants to produce well-considered and realistic assessments for prospects they may be working on, and to understand and constructively challenge risk and volume assessments of colleagues and/ or partners/ competitors. Each topic is introduced by a lecture, and learning is re-inforced by practical exercises and discussions. Hand-out materials in paper and/or electronic format will be provided. Time will be made available to discuss aspects of prospects that may be brought in by course participants. Trainer Your expert course leader has a PhD in Geology from the University of Utrecht. He worked for 31 years (1979 -2010) with Shell as an exploration geologist in a variety of functions across the globe. As Principle Technical Expert, he was responsible for ensuring that Risk & Volume assessments were carried out consistently and correctly in all of Shell's exploration units. In this capacity, he led and participated in countless prospect review sessions and developed and conducted a successful in-house course on Risks & Volume assessment. As manager of the Exploration Excellence Team, he performed in depth analysis of basins and plays and provided advice on exploration opportunities to senior management. Together with his team, he visited most of Shell's exploration offices, working hands-on with Shell's local exploration teams to generate new play and prospect ideas and to suggest evaluation techniques and technologies to apply. In 2010, he was appointed as extraordinary professor Regional and Petroleum Geology at the VU university of Amsterdam and in 2012 also at the University of Utrecht. He was visiting professor at the University of Malaya (Malaysia). Through his own consultancy, as of 2010, he provides advice on exploration activities to several companies and is regularly invited to carry out technical reviews. Activities cover all continents and include Portfolio Reviews, Prospect assessment, Play-based Exploration, and Geothermal activities. He conducts courses on several topics including Risk & Volume Assessment, Prospect Maturation, Basin Analysis, Play-based Exploration, Trap & Seal Analysis, Petroleum Geology for Non-geologists. Some of his recent publications include: De Jager, J. & van Winden, M. (2020): Play-Based Exploration of the petroleum potential of the Tremp-Graus, AÃnsa and eastern Jaca Sub-basins in the southern Pyrenees. Invited contribution for Digital Geology, EAGE special publication (eds: Grötsch, J. & Pöppelreiter, M.) De Jager, J. (2020). Concepts of Conventional Petroleum Systems. Invited contribution for Regional Geology and Tectonics Volume 1: Global Concepts, Techniques and Methodology (eds: Adam, J., Chiarelly, D. & Scarselli, N.) De Jager, J. (2021): Handbook Risk & Volume Assessment. Self-published De Jager, J., Van Ojik, K & Smit, R. (2023 - in preparation): Geological Development of The Netherlands. In: Geology of The Netherlands (eds: Ten Veen, J., Vis, G-J., De Jager, J. @ Wong, T.) POST TRAINING COACHING SUPPORT (OPTIONAL) To further optimise your learning experience from our courses, we also offer individualized 'One to One' coaching support for 2 hours post training. We can help improve your competence in your chosen area of interest, based on your learning needs and available hours. This is a great opportunity to improve your capability and confidence in a particular area of expertise. It will be delivered over a secure video conference call by one of our senior trainers. They will work with you to create a tailor-made coaching program that will help you achieve your goals faster. Request for further information about post training coaching support and fees applicable for this. Accreditions And Affliations

Complete VB.Net training course description A hands on introduction to programming in Visual BASIC .Net. What will you learn Build Visual BASIC applications. Build simple components Debug Visual BASIC programs. Examine existing code and determine its function. Complete VB.Net training course details Who will benefit: Anyone wishing to program in Visual BASIC. Anyone wishing to build Windows based applications. Prerequisites: None although experience in another high level language would be useful. Duration 5 days Complete VB.Net training course contents Writing your first program Visual Studio, forms designer, running VB programs, the UI, properties, writing the code. Toolbox Controls Basic use, input controls, ActiveX controls. Menus and Dialog Boxes Menus, Dialog Box controls, event procedures. Visual Basic .NET variables and operators Variables, I/O, data types, constants, operators, Math Methods, precedence. Decision Structures and Loops and Timers Event-Driven programming, Ifâ¦Then, Select Case, Forâ¦Next Loops, Timer Control. Debugging Visual Basic .NET Programs Break Mode, watch & command windows. Structured Error Handling Try...Catch, Finally, Err Object, retry periods. Modules and Procedures Standard modules, public variables, procedures. Arrays and Collections to Manage Data Fixed-Size & dynamic Arrays, ReDim Preserve, object collections, Controls Collection. Text Files and String Processing Text Box object, Text String methods, sorting. Automating Office Applications Application objects, automation in VB, the Object Browser, the Process Component. Deploying Visual Basic .NET Applications Planning a deployment, ways to deploy an application, deployment projects, options. Managing Windows Forms Forms, positioning, manipulation, adding controls, organizing controls, Startup Object. Adding Graphics and Animation Effects System.Drawing namespace, coordinates, SystemPaint Event, animation, transparency. Inheriting Forms and Creating Base Classes Inheriting forms, inheritance picker, base classes and inheritance, classes in projects. Working with Printers PrintDocument class, Text Box object, Print Preview and Page Setup Dialog Boxes. Database programming with ADO.NET Databases, ADO.NET, Data Adapters, Datasets, Bound & Navigation Controls. Displaying database records, formatting DataGrid cells, updating the database. Displaying HTML Documents Using IE IE Object, Internet Controls, IE Events. Web Forms for Interactive Web Applications ASP.NET, Web Forms vs. Windows Forms, HTML controls, web applications, event procedures for web forms controls.

Perl training course description A hands on introduction to programming in Perl. What will you learn Write Perl programs. Use Perl modules. Debug Perl programs. Examine existing code and determine its function. Perl training course details Who will benefit: Anyone wishing to learn Perl. Prerequisites: None although experience in another high level language would be useful. Duration 5 days Perl training course contents Introduction to Perl What is Perl? When to use Perl, downloading Perl, installing Perl, documentation, perldoc, running Perl, the Perl environment. Perl under UNIX, Perl under Windows. "Hello world". Variables Scalars, data types, $_, strings and numbers, assignment, constants, strict, scope, STDIN. Operators Number operators, string operators, precedence and associativity, converting numbers and strings, shortcut operators. Flow control Blocks, if, else, elseif, unless, foreach, while, for do, until. Regular expressions What are regular expressions? Pattern matching, Perl as a filter, file editing. Strings Comparing strings, concatenating, substrings, chomp, chop, formatting, string manipulation. Subroutines Comparing strings, concatenating, substrings, chomp, chop, formatting, string manipulation. Arrays and hashes Working with arrays, element access, push(), pop(), shift(), unshift(), <STDIN> as an array, associative arrays, hashes of arrays, hash references, arrays of hashes, hashes of hashes. Files Simple file handling, open, close, <FILEHANDLE>, <>, file tests, directory access, directory handles, database access, packing and packing binary data. I/O STDIN, STDOUT and STDERR, Command line arguments,@ARGV. Perl debugging The built in debugger, running the debugger, debugger commands, graphical debuggers. Script syntax errors, single stepping, breakpoints, watches. Packages and modules CPAN, Finding modules, installing modules, using modules, scope. Report formatting Formats, defining a format, invoking a format, field holders. Process management System interaction, system(), exec(), signals. Security issues.

Complete VBA programming training course description This course helps you extend the capabilities of the entire Office suite using Visual Basic for Applications (VBA). Even if you have no programming experience, you'll be automating routine computing processes quickly using the simple, yet powerful VBA programming language. We start at the beginning to get you acquainted with VBA so you can start recording macros right away. You'll then build upon that foundation to utilize the full capabilities of the language in Word, Excel, Outlook, and PowerPoint. What will you learn Record, write and run macros. Work with VBA Editor. Use the huge library of built-in functions. Create simple dialog boxes and complex forms. Customize Word, Excel, PowerPoint, Outlook, and Access. Program the Office 2016 ribbon. Complete VBA programming training course details Who will benefit: Anyone looking to extend the capabilities of the entire Office suite using VBA. Prerequisites: None. Duration 5 days Complete VBA programming training course contents Macros and getting started in VBA VBA syntax, variables, constants, and enumerations, array variables, finding objects, methods, and properties. Working with VBA 1 VBA syntax, variables, constants, and enumerations, array variables, finding objects, methods, and properties. Decisions, loops and functions Built-in functions, creating your own functions, making decisions in your code, using loops to repeat actions. Using message boxes, input boxes, and dialog boxes Getting user input with message boxes and input boxes, creating simple custom dialog boxes, creating complex forms. Creating effective code Building modular code and using classes, debugging your code and handling errors, building well-behaved code, exploring VBA's security features. Programming the Office applications The Word object model and key objects, working with widely used objects in Word, the Excel object model and key objects, working with widely used objects in Excel, the PowerPoint object, model and key objects, working with shapes and running slide shows, the Outlook object model and key objects, working with events in Outlook, the Access object model and key objects, manipulating the data in an Access database via VBA, accessing one application from another application, programming the Office 2016 ribbon.
