- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
1234 Courses in Cardiff delivered Live Online
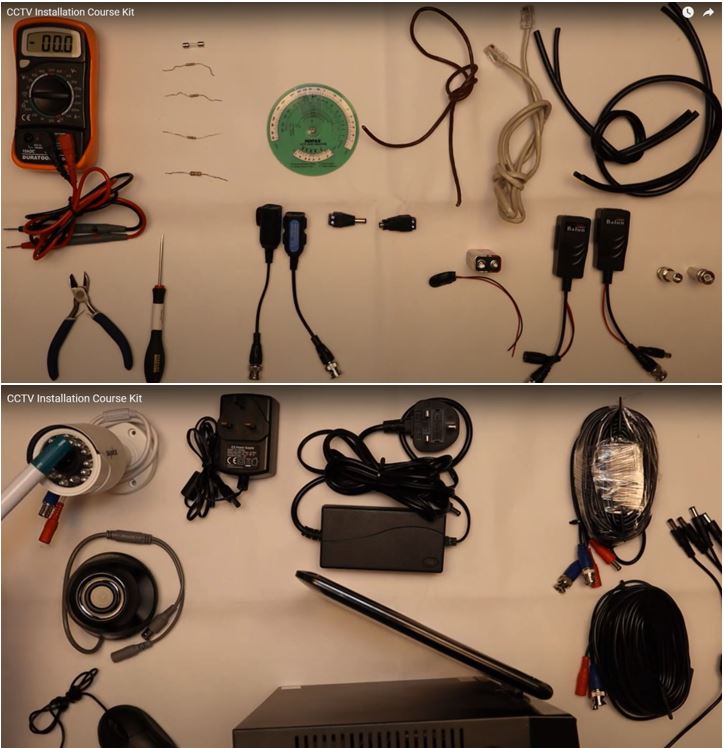
CCTV Installation Course
By Hi-Tech Training
Hi-Tech Training Closed Circuit Television (CCTV) Installation Course is designed to give participants a practical knowledge of the operation and installation of CCTV systems at a foundation level.
Internet of Things training course description A concise overview course covering The Internet of Things and the technologies involved. Particular emphasis is placed on the high level architecture of IoT and the benefits achievable. What will you learn Describe the structure of the IoT List the technologies involved in IoT. Explain how IoT works. Internet of Things training course details Who will benefit: Non-technical staff working with IoT. Prerequisites: None. Duration 1 day Internet of Things training course contents What is IoT The Internet, what is IoT? IoT and M2M, IoT technologies, IoT architecture. Wired and wireless communication. IoT applications; Smart houses, smart cities, smart cars, wearable, environment, other domain specific IoTs. IoT architecture Physical objects, virtual objects, cloud computing, data capture, communications. Big data. Components Hardware, sensors, actuators, chips, firmware, embedded systems. Open source platforms. Power options: Battery, solar, PoE. IoT communication RF, ZigBee, Bluetooth, Bluetooth LE, RFID, WiFi, 802.11ah, mobile technologies. Wired. Arduino (as an example) Microcontrollers, the platform, development, Arduino software, reading from sensors, I2C, SPI. Arduino and the Internet, HTTP, WiFi, GSM. The cloud and IoT: Pachube, nimbits, ThingSpeak Security in IoT Authentication, Encryption, secure booting, firewalls.

VMware NSX: Design [V4.x]
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for Network and security architects and consultants who design the enterprise and data center networks and NSX environments Overview By the end of the course, you should be able to meet the following objectives: Describe and apply a design framework Apply a design process for gathering requirements, constraints, assumptions, and risks Design a VMware vSphere virtual data center to support NSX requirements Create a VMware NSX Manager⢠cluster design Create a VMware NSX Edge⢠cluster design to support traffic and service requirements in NSX Design logical switching and routing Recognize NSX security best practices Design logical network services Design a physical network to support network virtualization in a software-defined data center Create a design to support the NSX infrastructure across multiple sites Describe the factors that drive performance in NSX This five-day course provides comprehensive training on considerations and practices to design a VMware NSX© environment as part of a software-defined data center strategy. This course prepares the student with the skills to lead the design of an NSX environment, including design principles, processes, and frameworks. The student gains a deeper understanding of the NSX architecture and how it can be used to create solutions to address the customer?s business needs. Course Introduction Introduction and course logistics Course objectives NSX Design Concepts Identify design terms Describe framework and project methodology Describe the role of VMware Cloud Foundation? in NSX design Identify customers? requirements, assumptions, constraints, and risks Explain the conceptual design Explain the logical design Explain the physical design NSX Architecture and Components Recognize the main elements in the NSX architecture Describe the NSX management cluster and the management plane Identify the functions and components of management, control, and data planes Describe the NSX Manager sizing options Recognize the justification and implication of NSX Manager cluster design decisions Identify the NSX management cluster design options NSX Edge Design Explain the leading practices for edge design Describe the NSX Edge VM reference designs Describe the bare-metal NSX Edge reference designs Explain the leading practices for edge cluster design Explain the effect of stateful services placement Explain the growth patterns for edge clusters Identify design considerations when using L2 bridging services NSX Logical Switching Design Describe concepts and terminology in logical switching Identify segment and transport zone design considerations Identify virtual switch design considerations Identify uplink profile and transport node profile design considerations Identify Geneve tunneling design considerations Identify BUM replication mode design considerations NSX Logical Routing Design Explain the function and features of logical routing Describe the NSX single-tier and multitier routing architectures Identify guidelines when selecting a routing topology Describe the BGP and OSPF routing protocol configuration options Explain gateway high availability modes of operation and failure detection mechanisms Identify how multitier architectures provide control over stateful service location Identify EVPN requirements and design considerations Identify VRF Lite requirements and considerations Identify the typical NSX scalable architectures NSX Security Design Identify different security features available in NSX Describe the advantages of an NSX Distributed Firewall Describe the use of NSX Gateway Firewall as a perimeter firewall and as an intertenant firewall Determine a security policy methodology Recognize the NSX security best practices NSX Network Services Identify the stateful services available in different edge cluster high availability modes Describe failover detection mechanisms Compare NSX NAT solutions Explain how to select DHCP and DNS services Compare policy-based and route-based IPSec VPN Describe an L2 VPN topology that can be used to interconnect data centers Explain the design considerations for integrating VMware NSX© Advanced Load Balancer? with NSX Physical Infrastructure Design Identify the components of a switch fabric design Assess Layer 2 and Layer 3 switch fabric design implications Review guidelines when designing top-of-rack switches Review options for connecting transport hosts to the switch fabric Describe typical designs for VMware ESXi? compute hypervisors with two pNICs Describe typical designs for ESXi compute hypervisors with four or more pNICs Differentiate dedicated and collapsed cluster approaches to SDDC design NSX Multilocation Design Explain scale considerations in an NSX multisite design Describe the main components of the NSX Federation architecture Describe the stretched networking capability in Federation Describe stretched security use cases in Federation Compare the Federation disaster recovery designs NSX Optimization and DPU-Based Acceleration Describe Geneve Offload Describe the benefits of Receive Side Scaling and Geneve Rx Filters Explain the benefits of SSL Offload Describe the effect of Multi-TEP, MTU size, and NIC speed on throughput Explain the available enhanced datapath modes and use cases List the key performance factors for compute nodes and NSX Edge nodes Describe DPU-Based Acceleration Define the NSX features supported by DPUs Describe the hardware and networking configurations supported with DPUs
![VMware NSX: Design [V4.x]](https://cademy-images-io.b-cdn.net/9dd9d42b-e7b9-4598-8d01-a30d0144ae51/4c81f130-71bf-4635-b7c6-375aff235529/original.png?width=3840)
Certified Data Protection Officer Training (CDPO)
By Training Centre
The IECB Certified Data Protection Officer training course will help you acquire the knowledge and skills to serve as a Data Protection Officer (DPO), allowing you to help organizations understand and implement solutions that meet the compliance requirements of the General Data Protection Regulation (GDPR), as well as a number of other regulatory requirements. The course takes a practical look at the GDPR requirements and advises on the mapping of solutions. In this way, delegates can master the role of the DPO and become competent to inform, advise, and monitor compliance with the GDPR and cooperate with the supervisory authority. About This Course After attending the training course, you can sit for the exam, and gain the 'Certified Data Protection Officer' credential, which validates that you have the Legal and regulatory knowledge required of a key adviser and practical knowledge to advise organisations how to meet their obligations regarding the GDPR compliance Learning Outcomes; Acquire a thorough understanding of the basic concepts and components of global Data Protection Regulation(s) Understand the correlation between the General Data Protection Regulation and best practice standards such as ISO 27701 Acquire a thorough understanding of the data protection by design requirements, particularly in relation to the protection of data Interpret the data protection requirements within the context of an organization Understand how to support an organization to plan, implement, manage, monitor and maintain ongoing compliance to the GDPR Our approach This training course is based on the practical application of best practices used in exercising the role of the DPO. Course modules include practical examples of the role of DPO. Delegates are encouraged to engage in discussions and exercises. A Case Study which brings the materials to life. Course agenda Day 1: Introduction to the GDPR Principles Day 2: The role of the DPO in the determination of a GDPR compliance program Day 3: The role of the DPO in business operations Day 4: Monitoring and maintenance of the GDPR compliance programme, as well as the examination Prerequisites A basic understanding of the GDPR will benefit course delegates. What's Included? Refreshments & Lunch (Classroom only) Course Slide Deck Official Study Materials CPD Certificate The Exam fees Who Should Attend? Individuals seeking to move into the role of DPO Team members who define, implement, and maintain a GDPR compliance programme Information Security Managers responsible for the personal data protection of an enterprise and the management of its risks Members of an information security, risk management, or Data Governance team Our Guarantee We are an approved IECB Training Partner. You can learn wherever and whenever you want with our robust classroom and interactive online training courses. Our courses are taught by qualified practitioners with commercial experience. We strive to give our delegates the hands-on experience. Our courses are all-inclusive with no hidden extras. The one-off cost covers the training, all course materials, and exam voucher. Our aim: To achieve a 100% first time pass rate on all our instructor-led courses. Our Promise: Pass first time or 'train' again for FREE. *FREE training offered for retakes - come back within a year and train for free, with the exam retake included too. Assessment All candidates at official training courses will be offered the opportunity to sit the associated exam. For CDPO, this constitutes a 12 question essay type exam which should be completed within 240 minutes. A passing score is achieved at 70%. Accreditation Provided by This course is Accredited by NACS and Administered by the IECB.

Cisco Protecting Against Malware Threats with Cisco AMP for Endpoints (SSFAMP) v6.0
By Nexus Human
Duration 3 Days 18 CPD hours This course is intended for The primary audience for this course is as follows: Cisco integrators, resellers, and partners Network administrators Security administrators Security consultants Systems engineers Technical support personnel Overview After taking this course, you should be able to: Cisco Advanced Malware Protection (AMP) Recognize the key features and concepts of the AMP for Endpoints product Navigate the AMP for Endpoints console interface and perform first-use setup tasks Identify and use the primary analysis features of AMP for Endpoints Use the AMP for Endpoints tools to analyze a compromised host Analyze files and events by using the AMP for Endpoints console and be able to produce threat reports Configure and customize AMP for Endpoints to perform malware detection Create and configure a policy for AMP-protected endpoints Plan, deploy, and troubleshoot an AMP for Endpoints installation Use Cisco Orbital to pull query data from installed AMP for Endpoints connectors. Describe the AMP Representational State Transfer (REST) API and the fundamentals of its use Describe all the features of the Accounts menu for both public and private cloud installations Protecting Against Malware Threats with Cisco AMP for Endpoints (SSFAMP) v6.0 is a 3-day course that shows you how to deploy and use Cisco© AMP for Endpoints, a next-generation endpoint security solution that prevents, detects, and responds to advanced threats. Through expert instruction and hands-on lab exercises, you will learn how to implement and use this powerful solution through a number of step-by-step attack scenarios. You?ll learn how to build and manage a Cisco AMP for Endpoints deployment, create policies for endpoint groups, and deploy connectors. You will also analyze malware detections using the tools available in the AMP for Endpoints console, Cisco Threat Grid, and the Cisco Orbital Advanced Search Tool. The course qualifies for 24 Cisco Continuing Education credits (CE) towards recertification.This class will help you:Learn how to deploy and manage Cisco AMP for EndpointsSucceed in today?s high-demand security operations roles Course Outline This course will cover the following topics: Introducing to Cisco AMP Technologies Introducing AMP for Endpoints Overview and Architecture Navigating the Console Interface Using Cisco AMP for Endpoints Identifying Attacks Analyzing Malware Managing Outbreak Control Creating Endpoint Policies Working with AMP for Endpoint Groups Using Orbital for Endpoint Visibility Introducing AMP REST API Navigating Accounts

FortiGate Infrastructure
By Nexus Human
Duration 2 Days 12 CPD hours This course is intended for Networking and security professionals involved in the design, implementation, and administration of a network infrastructure using FortiGate appliances. Overview Analyze a FortiGate's route table. Route packets using policy-based and static routes for multi-path and load balanced deployments. Configure SD-WAN to load balance traffic between multiple WAN links effectively. Inspect traffic transparently, forwarding as a Layer 2 device. Divide FortiGate into two or more virtual devices, each operating as an independent FortiGate, by configuring virtual domains (VDOMs). Establish an IPsec VPN tunnel between two FortiGate appliances. Compare policy-based to route-based IPsec VPN. Implement a meshed or partially redundant VPN. Diagnose failed IKE exchanges. Offer Fortinet Single Sign On (FSSO) access to network services, integrated with Microsoft Active Directory. Deploy FortiGate devices as an HA cluster for fault tolerance and high performance. Deploy implicit and explicit proxy with firewall policies, authentication, and caching. Diagnose and correct common problems. In this two-day course, you will learn how to use advanced FortiGate networking and security. Course Outline Module 1. Routing Module 2. Software-Defined WAN (SD-WAN) Module 3. Layer 2 Switching Module 4. Virtual Domains Module 5. Site-to-Site IPsec VPN Module 6. Fortinet Single Sign-On (FSSO) Module 7. High Availability (HA) Module 8. Web Proxy Module 9. Diagnostics

AWS Technical Essentials
By Nexus Human
Duration 1 Days 6 CPD hours This course is intended for Individuals responsible for articulating the technical benefits of AWS services Individuals interested in learning how to get started with using AWS SysOps Administrators, Solution Architects and Developers interested in using AWS services Overview Recognize terminology and concepts as they relate to the AWS platform and navigate the AWS Management Console. Understand the foundational services, including Amazon Elastic Compute Cloud (EC2), Amazon Virtual Private Cloud (VPC), Amazon Simple Storage Service (S3), and Amazon Elastic Block Store (EBS). Understand the security measures AWS provides and key concepts of AWS Identity and Access Management (IAM). Understand AWS database services, including Amazon DynamoDB and Amazon Relational Database Service (RDS). Understand AWS management tools, including Auto Scaling, Amazon CloudWatch, Elastic Load Balancing (ELB), and AWS Trusted Advisor. AWS Technical Essentials introduces you to AWS services, and common solutions. It provides you with fundamental knowledge to become more proficient in identifying AWS services. It helps you make informed decisions about IT solutions based on your business requirements and get started working on AWS. Prerequisites Working knowledge of distributed systems Familiarity with general networking concepts Working knowledge of multi-tier architectures Familiarity with cloud computing concepts 1 - AWS introduction and history AWS Global Infrastructure Demonstration: AWS Management Console 2 - AWS Storage Identify key AWS storage options Describe Amazon EBS Create an Amazon S3 bucket and manage associated objects 3 - Compute, network and storage services Amazon Elastic Compute Cloud (EC2) Amazon Virtual Private Cloud (VPC) Amazon Simple Storage Service (S3) Amazon Elastic Block Store (EBS) Demonstration: Amazon Simple Storage Service (S3) Hands-on lab: Build your VPC and launch a web server 4 - AWS Security, AWS Identity and Access Management (IAM) AWS Identity and Access Management (IAM) Demonstration: AWS Identity and Access Management (IAM) 5 - Compute Services & Networking Identify the different AWS compute and networking options Describe an Amazon Virtual Private Cloud (VPC) Create an Amazon EC2 instance Use Amazon EBS with Amazon EC2 6 - Managed Services & Database Describe Amazon DynamoDB Understand key aspects of Amazon RDS Launch an Amazon RDS instance 7 - Databases (RDS, DynamoDB) SQL and NoSQL databases Data storage considerations Hands-on lab: Build your database server and connect to it 8 - AWS elasticity and management tools Auto scaling Load balancing Cloud Watch Trusted Advisor Hands-on lab: Scale and load balance your architecture 9 - Deployment and Management Identify what is CloudFormation Describe Amazon CloudWatch metrics and alarms Describe Amazon Identity and Access Management (IAM)

HTTP streaming training course description This course looks at the delivery of video streams using HTTP adaptive streaming. Both MPEG DASH and HLS are investigated. Hands on sessions primarily involve using Wireshark to analyse streams. What will you learn Use Wireshark to analyse and troubleshoot HTTP video streams. Explain HTTP adaptive streaming works. Evaluate and compare MPEG DASH and HLS. Use tools to create HTTP adaptive streams. HTTP streaming training course details Who will benefit: Anyone working in the broadcast industry. Prerequisites: TCP/IP foundation for engineers Duration 2 days HTTP streaming training course contents What is HTTP streaming? The old way. Progressive downloads versus streaming. Why not UDP and RTP for delivery? Adaptive bit rate streaming. Standards. Hands on Base network setup. Using WireShark for HTTP streams. HTTP protocol stack IP, TCP, IPv6. HTTP. HTTP 1.0, HTTP 1.1, HTTP 2.0, HTTP header fields. HTML 5. Hands on Analysing HTTP. Adaptive bitrate streaming principles Chunks, fragments, segments. Manifest files. Encoding, resolution, bitrates. Addressing, relative and absolute URLs, redirection. When does the client switch streams? Switch points. Hands on Walk through of client behaviours on a stream. HTTP streaming architecture Server components, distribution components, client software. CDN, caching, multiple servers. Hands on Analysing CDN and Internet delivery. TCP and HTTP streaming interactions TCP ACK, TCP connections, unicast only. TCP flow control, TCP and performance. Hands on TCP window sizes. MPEG DASH Stakeholders, DASH architecture and model, codec agnostic, XML, Media Presentation Description, Media Presentation, segment formats. Hands on MPEG DASH analysis. HTTP Live Streaming and others Stakeholders. Media segments, media playlists, master playlists. Adobe HTTP dynamic streaming, Microsoft smooth streaming. Hands on Analysing HLS. Tools mp4dash, mp4fragment, libdash. Apple developer tools for HLS. Hands on Creating segmented content. Security HTTPS, encryption, content protection. Hands on Encryption analysis. Summary Choosing a streaming method. Impact of live versus VoD. Web sockets.

IP broadcast training course description A current hot topic in recent years has been the provision of multimedia services over IP networks aka triple or quadruple play. This course investigates the characteristics of video transmission and then studies the impact on IP networks. What will you learn Use Wireshark to analyse and troubleshoot TV streams. Describe techniques, which can be used in IP to provide low uniform delay. Evaluate IPTV technologies. Design data networks, which will support IPTV. IP broadcast training course details Who will benefit: Anyone working in broadcast. Prerequisites: TCP/IP foundation for engineers Duration 3 days IP broadcast training course contents What is IPTV? What is IP? What is TV? Pixels, frames, colour, digital modulation, digital video broadcasting. SDTV, HDTV, 4K. IPTV architectures, Contribution, distribution, delivery. IPTV standards. Hands on Base IP connectivity, VLC. IPTV protocol stacks IP, TCP, UDP, RTP. IPv6. HTTP. Bandwidth requirements. Hands on IPTV bandwidth calculations. Video codecs What is a CODEC, pictures and audio, digitisation, sampling, quantisation, encoding, compressing. MPEG, bit rates, resolution. I, B, P frames, GOP. MPEG 2, MPEG 4, H.264, H.265, VP9, AV1. Hands on Analysing MPEG frames. IP issues Quality vs. bandwidth. Bandwidth, delay, latency, jitter, signalling. Routers. Hands on Analysing jitter and other performance issues. IPTV performance and QoS IP DSCP field, queuing strategies; FIFO, WFQ, custom, priority, RED. Differentiated services, Diffserv. 802.1Q. Traffic shaping. QoE. Hands on best effort versus prioritisation. UDP versus TCP Reliable, unreliable, connection oriented, connectionless. Broadcasts, multicasts and unicasts. TCP flow control, TCP and performance. Hands on TCP window sizes. RTP RTP, ports, mixers, translators, RTCP, SMPTE, FEC. Hands on RTP analysis with Wireshark. Multicasting Multicasting compared to unicasting and broadcasting, when to use and when not to use multicasting. IGMP, PIM-SM, SSM. MLD. Hands on Analysing multicast streams. OTT TV HTTP, HTTPS, Chunked HTTP. Adaptive streaming. HTML5. DASH vs HLS. Hands on Analysing HTTP streams. Security Firewalls, TLS, DRM, watermarking. Encryption. Geolocation. VPNs. IPTV architecture and other protocols Content providers, Service providers, delivery networks, home networks. Caching, Service discovery. RTSP. SAP, SDP. DHCP, DNS, NTP

