- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
1135 Courses in Cardiff delivered Live Online
Values Based Recruitment
By Mpi Learning - Professional Learning And Development Provider
Recruiting great people to our organisations is the key to high performance and sustainable business success.

Supervising Others
By Nexus Human
Duration 1 Days 6 CPD hours This course is intended for This course is intended for individuals who desire to supervise others more effectively. Overview Upon successful completion of this course, students will be equipped to supervise others more effectively and efficiently, contributing to job satisfaction and productivity. In this course, students will develop the skills required to be more efficient and proficient supervisors. 1 - GETTING STARTED Icebreaker Housekeeping Items The Parking Lot Workshop Objectives 2 - SETTING EXPECTATIONS Defining the Requirements Identifying Opportunities for Improvement and Growth Setting Verbal Expectations Putting Expectations in Writing 3 - SETTING GOALS Understanding Cascading Goals The SMART Way Helping Others Set Goals 4 - ASSIGNING WORK General Principles The Dictatorial Approach The Apple-Picking Approach The Collaborative Approach 5 - DEGREES OF DELEGATION Level One: Complete Supervision Level Two: Partial Supervision Level Three: Complete Independence 6 - IMPLEMENT DELEGATION Deciding to Delegate To Whom Should You Delegate? Providing Instructions Monitoring the Results Troubleshooting Delegation 7 - PROVIDING FEEDBACK Characteristics of Good Feedback Feedback Delivery Tools Informal Feedback Formal Feedback 8 - MANAGING YOUR TIME The 80/20 Rule Prioritizing with the Urgent-Important Matrix Using a Productivity Journal Using Routines and Rituals to Simplify Your Workday 9 - RESOLVING CONFLICT Using a conflict Resolution Process Maintaining Fairness Seeking help from Within the Team Seeking Help for Outside the Team 10 - TIPS FOR SPECIAL SITUATIONS What to Do If You?ve Been Promoted from within the Team What to Do If You're Leading a Brand New Team What to Do if You're Taking on an Established Team 11 - A SURVIVAL GUIDE FOR THE NEW SUPERVISOR Ask the Right Questions of the Right People Go to Gemba Keep Learning 12 - WRAPPING UP Words from the Wise Review of Parking Lot Lessons Learned Completion of Action Plans and Evaluations

AZ-900T00 Microsoft Azure Fundamentals
By Nexus Human
Duration 1 Days 6 CPD hours This course is intended for This course is suitable for IT personnel who are just beginning to work with Azure. This audience wants to learn about our offerings and get hands-on experience with the product. This course primarily uses the Azure portal and command line interface to create resources and does not require scripting skills. Students in this course will gain confidence to take other role-based courses and certifications, such as Azure Administrator. This course combines lecture, demonstrations, and hands-on labs. This course will also help prepare someone for the AZ-900 exam. This course will provide foundational level knowledge on cloud concepts; core Azure services; and Azure management and governance features and tools. Prerequisites There are no prerequisites for taking this course. Familiarity with cloud computing is helpful, but isn't necessary. 1 - Describe cloud computing What is cloud computing Describe the shared responsibility model Define cloud models Describe the consumption-based model 2 - Describe the benefits of using cloud services Describe the benefits of high availability and scalability in the cloud Describe the benefits of reliability and predictability in the cloud Describe the benefits of security and governance in the cloud Describe the benefits of manageability in the cloud 3 - Describe cloud service types Describe Infrastructure as a Service Describe Platform as a Service Describe Software as a Service 4 - Describe the core architectural components of Azure What is Microsoft Azure Get started with Azure accounts Describe Azure physical infrastructure Describe Azure management infrastructure 5 - Describe Azure compute and networking services Describe Azure Virtual Machines Describe Azure Virtual Desktop Describe Azure Containers Describe Azure Functions Describe application hosting options Describe Azure Virtual Networking Describe Azure Virtual Private Networks Describe Azure ExpressRoute Describe Azure DNS 6 - Describe Azure storage services Describe Azure storage accounts Describe Azure storage redundancy Describe Azure storage services Identify Azure data migration options Identify Azure file movement options 7 - Describe Azure identity, access, and security Describe Azure directory services Describe Azure authentication methods Describe Azure external identities Describe Azure conditional access Describe Azure role-based access control Describe zero trust model Describe defense-in-depth Describe Microsoft Defender for Cloud 8 - Describe cost management in Azure Describe factors that can affect costs in Azure Compare the Pricing and Total Cost of Ownership calculators Describe the Microsoft Cost Management tool Describe the purpose of tags 9 - Describe features and tools in Azure for governance and compliance Describe the purpose of Microsoft Purview Describe the purpose of Azure Policy Describe the purpose of resource locks Describe the purpose of the Service Trust portal 10 - Describe features and tools for managing and deploying Azure resources Describe tools for interacting with Azure Describe the purpose of Azure Arc Describe Azure Resource Manager and Azure ARM templates 11 - Describe monitoring tools in Azure Describe the purpose of Azure Advisor Describe Azure Service Health Describe Azure Monitor Additional course details: Nexus Humans AZ-900T00 Microsoft Azure Fundamentals training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the AZ-900T00 Microsoft Azure Fundamentals course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

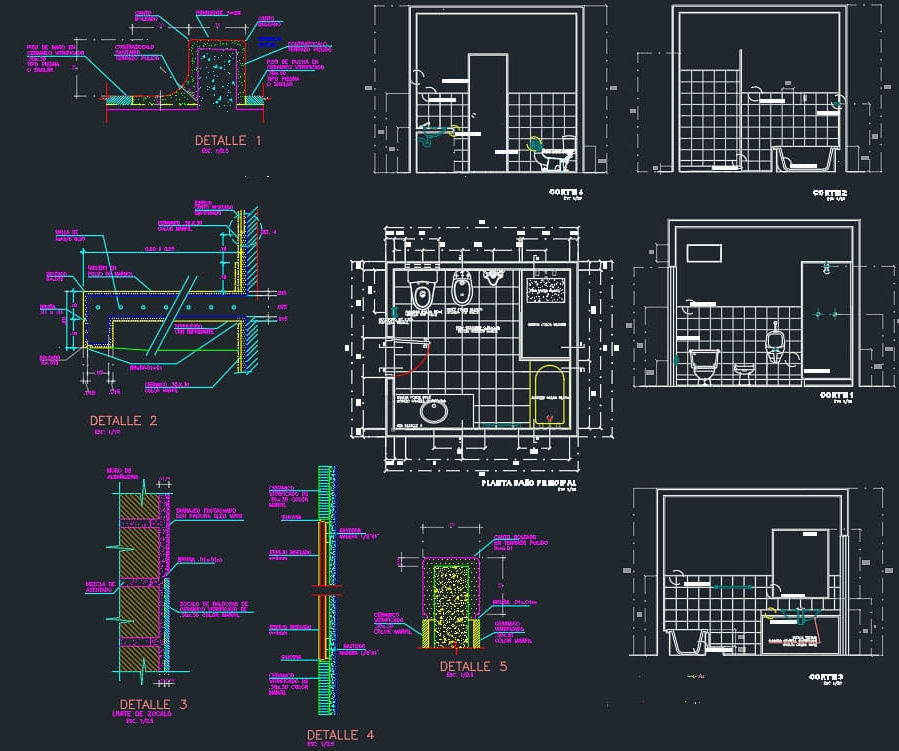
AutoCAD Basics-Advanced Training Classes
By London Design Training Courses
Why AutoCAD Basics-Advanced Training Classes? Click here for more info AutoCAD Basics to Advanced Level Training Master drawing, editing, and advanced techniques. Optimize productivity and customize workspace. Create precise 2D drawings for various industries. Access recorded lessons and lifetime email support. Duration: 16 hrs Method: 1-on-1, Personalized attention. Schedule: Tailor your own schedule by pre-booking a convenient hour of your choice, available from Mon to Sat between 9 am and 7 pm. The AutoCAD from Basics leading to Advanced Training Course offers a comprehensive learning experience for participants to become proficient in AutoCAD. Whether you're a beginner or an experienced user, this progressive program covers the full spectrum of AutoCAD functionality. Participants will learn core features like drawing, editing, annotations, and dimensioning, progressing to advanced topics such as object manipulation, workspace customization, and workflow optimization. Upon completion, participants will create precise 2D drawings and designs. Interactive learning experiences with experienced instructors are available in-person or through live online sessions. AutoCAD 2D Course Outline: Session 1: Introduction to AutoCAD interface, commands, and tools Managing drawings and drawing basic shapes Basic modification techniques (erase, move, rotate, scale) Session 2: Working with layers and properties Creating and modifying text and dimensions Introduction to blocks and attributes Session 3: Advanced object modification techniques (fillet, chamfer, trim, extend) Using grips to modify objects Creating and modifying polylines and splines Session 4: Creating and editing tables Working with layouts and viewports Printing and exporting drawings Construction detailing and Detailed sections Course Highlights: Engaging exercises and projects to reinforce skills. Q&A and troubleshooting support. Solid understanding of AutoCAD 2D for basic to intermediate drawings. List of Topics Covered: Drawing: Line, Polyline, Circle, Arc, Rectangle, Ellipse, Spline, Polygon, Ray, Hatching, Gradient. Inquiry: Measure and Select All. Modify: Move, Copy, Rotate, Mirror, Fillet, Trim, Extend, Erase, Offset, Explode, Array, Stretch, Break, Polyline Edit, Hatch Edit, Scale. Layers: Creating, Managing, Changing, Line Type, Line Weights. Annotation: Dimensions, Text, Dimension Style, Text Style, Leaders. Properties: Colors, Line weights, Line Types, Line Type Scaling. Blocks: Create, Insert, Edit, Explode, Export. Insert: Insert, Attach. View: Navigate, View, Windows. Plot/Print: Model Space, Layouts/Workspaces, Viewports, Layout Scaling, Paper Setup, What To Plot, Plot Scale, Plot Offset, Plot Options. Final Project: Create a Plan, Section, and Elevation drawing. Option for a personal project. Free Trial - Download AutoCAD Software & Toolsets: Participants can download a free trial of AutoCAD and industry-specific toolsets from Autodesk's official website: (https://www.autodesk.co.uk). Master AutoCAD Basics: Understand the interface, commands, and drawing tools. Create and Modify Drawings: Proficiently manage drawings and apply various modification techniques. Work with Layers and Annotations: Effectively use layers, text, and dimensions. Utilize Advanced Drawing Techniques: Apply advanced object modifications and work with polylines. Navigate Layouts and Viewports: Manage layouts, viewports, and printing/exporting. Hands-On Project Experience: Practice skills through exercises and a final project. Personalized Learning: Receive focused one-to-one attention. Convenient Options: Choose in-person or live online sessions. Lesson Recordings and Support: Access recorded lessons and receive ongoing email assistance. Enhance Career Opportunities: Develop valuable 2D drawing skills for career advancement.
Effective Management
By Nexus Human
Duration 1 Days 6 CPD hours This course is intended for Business professionals who are either at the managerial level, or are interested in becoming team leaders will benefit from this course. Overview Determine the roles that a manager must fill on a team, and explore the key areas of personal development. Discover how to detect silent messages through body language and other means of nonverbal communication. You will also bolster your listening skills through active listening. Discover ways of identifying problems, prioritizing problems, and implementing solutions effectively. Empower your workgroup through delegation and coaching. Discover the stages of team development and examine the need for regular team meetings. In this course, students will gain an understanding of the basic fundamentals of becoming an effective manager for their team. 1. Developing as a Manager Identify Effective Manager Roles Develop Personal Skills 2. Communicating Successfully Communicate Without Talking Manage Better by Listening Assert to Achieve 3. Cultivating Great Teams Create an Invincible Team Inspire Team Success Run Team Meetings Resolve Conflicts Positively 4. Empowering Your Workgroup Delegate For Results Coach for Achievement Optimize Staff Performance 5. Creating Successful Solutions Identify and Define the Problem Determine the Root Cause Identify a Solution Implement Solutions Decisively Additional course details: Nexus Humans Effective Management training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the Effective Management course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

Global Project Management: Virtual In-House Training
By IIL Europe Ltd
Global Project Management: Virtual In-House Training In this course, you will dig deeper-and differently-into project management processes, tools, and techniques, developing the ability to see them through the lens of global and cultural project impacts. In today's increasingly global environment, managing a project with customers and support organizations spread across multiple countries and continents is a major challenge. From identifying stakeholders and gathering requirements, to planning, controlling, and executing the project, the basic logistics of a global project present their own standard challenges. However, with additional cultural, language-based, and regional elements, global projects involve more complexities than teams often realize. There are unique communication needs, cultural awareness elements, varying customs and work expectations, and critical legal differences to consider. In this course, you will dig deeper-and differently-into project management processes, tools, and techniques, developing the ability to see them through the lens of global and cultural project impacts. This will leverage you to problem solve differently on global projects, prevent problems, and ensure success. The goal is for you to effectively navigate the challenges of leading projects with multi-regional footprints and globally diverse sets of stakeholders. What you Will Learn At the end of this program, you will be able to: Determine when a project meets the criteria of being a true global one Articulate global project needs based on the project grid and framework Identify and analyze global project stakeholders Recognize cultural differences and articulate how they impact project work Determine global project estimating, scheduling, and staffing challenges Assess global project risks and develop problem-solving responses Analyze complex cultural situations and align optimal project communication and negotiation tools and techniques Apply best practices for conducting virtual team work and mitigating virtual challenges Evaluate ways to control for global project scope, cost, and procurement Align customer management best practices with global customer needs Implement key global project closing activities Foundation Concepts What is a global project? What makes a global project different? A global project management framework Initiating the Global Project Launching a global project Respecting cultural differences Identifying and analyzing stakeholders Developing the communications plan Defining the ideal global project manager Crafting a global project charter Planning the Global Project Gathering requirements for a global project Defining the scope, region by region Estimating and scheduling for global projects Staffing the global project Developing the global risk management plan Executing the Global Project Managing global stakeholder expectations Embracing cultural diversity Honing global negotiation techniques Procuring goods and services on a global basis Managing global legal and regulatory issues at the micro and macro level Monitoring and Controlling the Global Project Status reporting Virtual communication Cost control Schedule control Scope control Customer satisfaction Closing the Global Project Contract closure at the macro and micro levels Administrative closure with global reach Lessons learned

The Art of Delegation and High-Impact Feedback: In-House Training
By IIL Europe Ltd
The Art of Delegation and High-Impact Feedback: In-House Training Whether you are a project manager, an executive, or simply someone involved in leading or helping others, a critical part of your work must involve delegating and giving feedback. These two skills, however, are not as simple as they seem. How do you know what to Partcipant? What kinds of feedback should you give? Knowing this and practicing this are two different things. Ultimately, delegating and giving feedback are skills that must be done mindfully, strategically, and meaningfully. They must be done in ways that not only positively impact performance, but also inspire growth, engagement, and motivation. When done poorly, they can create significant problems. But when done well, they can generate value for everyone and benefit future endeavors. In this course, you will learn to think more deeply about the importance of delegating and discover how to give better feedback. You will have opportunities to apply best practices and methodologies that you can use in the real world, ultimately paying off for you and for others. What you Will Learn At the end of this program, you will be able to: Explain why common excuses for NOT delegating are short-sighted Identify what needs delegating by using a proven methodology Utilize best practices in real world scenarios, delegating in a way that benefits you and the individual to whom you Partcipant Summarize key lessons learned in brain science which enhance the feedback-giving process Recognize the critical connection between feedback and performance Apply a proven model to deliver feedback that inspires growth, engagement, and motivation Getting Started What is delegation? What makes delegation hard? What do I Partcipant and why? How to Partcipant effectively Feedback Exploring the feedback process Why feedback is hard to give...and receive Why giving feedback effectively is important Feedback models

EC-Council Certified Ethical Hacker (CEH) v12
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for The Certified Ethical Hacking v12 course will significantly benefit security officers, auditors, security professionals, site administrators, and anyone who is concerned about the integrity of the network infrastructure. Overview Information security controls, laws, and standards. Various types of footprinting, footprinting tools, and countermeasures. Network scanning techniques and scanning countermeasures Enumeration techniques and enumeration countermeasures Vulnerability analysis to identify security loopholes in the target organization?s network, communication infrastructure, and end systems. System hacking methodology, steganography, steganalysis attacks, and covering tracks to discover system and network vulnerabilities. Different types of malware (Trojan, Virus, worms, etc.), system auditing for malware attacks, malware analysis, and countermeasures. Packet sniffing techniques to discover network vulnerabilities and countermeasures to defend against sniffing. Social engineering techniques and how to identify theft attacks to audit human-level vulnerabilities and social engineering countermeasures. DoS/DDoS attack techniques and tools to audit a target and DoS/DDoS countermeasures. Session hijacking techniques to discover network-level session management, authentication/authorization, and cryptographic weaknesses and countermeasures. Webserver attacks and a comprehensive attack methodology to audit vulnerabilities in webserver infrastructure, and countermeasures. Web application attacks, comprehensive web application hacking methodology to audit vulnerabilities in web applications, and countermeasures. SQL injection attack techniques, injection detection tools to detect SQL injection attempts, and countermeasures. Wireless encryption, wireless hacking methodology, wireless hacking tools, and Wi-Fi security tools. Mobile platform attack vector, android vulnerability exploitations, and mobile security guidelines and tools. Firewall, IDS and honeypot evasion techniques, evasion tools and techniques to audit a network perimeter for weaknesses, and countermeasures. Cloud computing concepts (Container technology, serverless computing), the working of various threats and attacks, and security techniques and tools. Penetration testing, security audit, vulnerability assessment, and penetration testing roadmap. Threats to IoT and OT platforms and defending IoT and OT devices. Cryptography ciphers, Public Key Infrastructure (PKI), cryptography attacks, and cryptanalysis tools. CEH provides an in-depth understanding of ethical hacking phases, various attack vectors, and preventative countermeasures. It will teach you how hackers think and act maliciously so you will be better positioned to setup your security infrastructure and defend against future attacks. An understanding of system weaknesses and vulnerabilities helps organizations strengthen their system security controls to minimize the risk of an incident. CEH was built to incorporate a hands-on environment and systematic process across each ethical hacking domain and methodology, giving you the opportunity to work towards proving the required knowledge and skills needed to achieve the CEH credential. You will be exposed to an entirely different posture toward the responsibilities and measures required to be secure. Now in its 12th version, CEH continues to evolve with the latest operating systems, tools, tactics, exploits, and technologies. 1 - Introduction to Ethical Hacking Information Security Overview Cyber Kill Chain Concepts Hacking Concepts Ethical Hacking Concepts Information Security Controls Information Security Laws and Standards 2 - 2 - Foot-printing and Reconnaissance Footprinting Concepts Footprinting through Search Engines Footprinting through Web Services Footprinting through Social Networking Sites Website Footprinting Email Footprinting Who is Footprinting DNS Footprinting Network Footprinting Footprinting through Social Engineering Footprinting Tools Footprinting Countermeasures 3 - Scanning Networks Network Scanning Concepts Scanning Tools Host Discovery Port and Service Discovery OS Discovery (Banner Grabbing/OS Fingerprinting) Scanning Beyond IDS and Firewall Draw Network Diagrams 4 - Enumeration Enumeration Concepts NetBIOS Enumeration SNMP Enumeration LDAP Enumeration NTP and NFS Enumeration SMTP and DNS Enumeration Other Enumeration Techniques Enumeration Countermeasures 5 - Vulnerability Analysis Vulnerability Assessment Concepts Vulnerability Classification and Assessment Types Vulnerability Assessment Solutions and Tools Vulnerability Assessment Reports 6 - System Hacking System Hacking Concepts Gaining Access Escalating Privileges Maintaining Access Clearing Logs 7 - Malware Threats Malware Concepts APT Concepts Trojan Concepts Virus and Worm Concepts Fileless Malware Concepts Malware Analysis Countermeasures Anti-Malware Software 8 - Sniffing Sniffing Concepts Sniffing Technique: MAC Attacks Sniffing Technique: DHCP Attacks Sniffing Technique: ARP Poisoning Sniffing Technique: Spoofing Attacks Sniffing Technique: DNS Poisoning Sniffing Tools Countermeasures Sniffing Detection Techniques 9 - Social Engineering Social Engineering Concepts Social Engineering Techniques Insider Threats Impersonation on Social Networking Sites Identity Theft Countermeasures 10 - Denial-of-Service DoS/DDoS Concepts DoS/DDoS Attack Techniques BotnetsDDoS Case Study DoS/DDoS Attack Tools Countermeasures DoS/DDoS Protection Tools 11 - Session Hijacking Session Hijacking Concepts Application Level Session Hijacking Network Level Session Hijacking Session Hijacking Tools Countermeasures 12 - Evading IDS, Firewalls, and Honeypots IDS, IPS, Firewall, and Honeypot Concepts IDS, IPS, Firewall, and Honeypot Solutions Evading IDS Evading Firewalls IDS/Firewall Evading Tools Detecting Honeypots IDS/Firewall Evasion Countermeasures 13 - Hacking Web Servers Web Server Concepts Web Server Attacks Web Server Attack Methodology Web Server Attack Tools Countermeasures Patch Management Web Server Security Tools 14 - Hacking Web Applications Web Application Concepts Web Application Threats Web Application Hacking Methodology Web API, Webhooks, and Web Shell Web Application Security 15 - SQL Injection SQL Injection Concepts Types of SQL Injection SQL Injection Methodology SQL Injection Tools Evasion Techniques Countermeasures 16 - Hacking Wireless Networks Wireless Concepts Wireless Encryption Wireless Threats Wireless Hacking Methodology Wireless Hacking Tools Bluetooth Hacking Countermeasures Wireless Security Tools 17 - Hacking Mobile Platforms Mobile Platform Attack Vectors Hacking Android OS Hacking iOS Mobile Device Management Mobile Security Guidelines and Tools 18 - IoT and OT Hacking IoT Hacking IoT Concepts IoT Attacks IoT Hacking Methodology IoT Hacking Tools Countermeasures OT Hacking OT Concepts OT Attacks OT Hacking Methodology OT Hacking Tools Countermeasures 19 - Cloud Computing Cloud Computing Concepts Container Technology Serverless Computing Cloud Computing Threats Cloud Hacking Cloud Security 20 - Cryptography Cryptography Concepts Encryption Algorithms Cryptography Tools Public Key Infrastructure (PKI) Email Encryption Disk Encryption Cryptanalysis Countermeasures Additional course details: Nexus Humans EC-Council Certified Ethical Hacker (CEH) v.12 training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the EC-Council Certified Ethical Hacker (CEH) v.12 course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

VMware Horizon: Deploy and Manage [V8.8]
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for Tier 1 Operators, administrators, and architects for VMware Horizon Overview By the end of the course, you should be able to meet the following objectives: Recognize the features and benefits of VMware Horizon Define a use case for your virtual desktop and application infrastructure Use vSphere to create VMs to be used as desktops for VMware Horizon Create and optimize Windows VMs to create VMware Horizon desktops Install and Configure Horizon Agent on a VMware Horizon desktop Configure, manage, and entitle desktop pools of full VMs Configure and manage the VMware Horizon Client systems and connect the client to a VMware Horizon desktop Configure, manage, and entitle pools of instant-clone desktops Create and use Remote Desktop Services (RDS) desktops and application pools Monitor the VMware Horizon environment using the VMware Horizon Console Dashboard and Horizon Help Desk Tool Identify VMware Horizon Connection Server installation, architecture, and requirements Describe the authentication and certificate options for the VMware Horizon environment Recognize the integration process and benefits of Workspace ONE Access⢠and Horizon 8 Compare the remote display protocols that are available in VMware Horizon Describe the 3D rendering options available in Horizon 8 Discuss scalability options available in Horizon 8 Describe different security options for the Horizon environment This five-day course gives you the hands-on skills to deliver virtual desktops and applications through a single virtual desktop infrastructure platform. You build on your skills in configuring and managing VMware Horizon© 8 through a combination of lecture and hands-on labs. You learn how to configure and deploy pools of virtual machines and how to provide a customized desktop environment to end-users. Additionally, you learn how to install and configure a virtual desktop infrastructure platform. You learn how to install and configure VMware Horizon© Connection Server?, VMware Unified Access Gateway?, how to configure a load balancer for use with Horizon, and how to establish Cloud Pod Architecture. Course Introduction Introductions and course logistics Course objectives Introduction to VMware Horizon Recognize the features and benefits of Horizon Describe the conceptual and logical architecture of Horizon Introduction to Use Case Convert customer requirements to use-case attributes Define a use case for your virtual desktop and application infrastructure vSphere for VMware Horizon Explain basic virtualization concepts Use VMware vSphere© Client? to access your VMware vCenter System and VMware ESXi? hosts Create a Windows virtual machine using vSphere Create Windows Desktops Outline the steps to install Horizon Agent on Windows virtual machines Install Horizon Agent on a Windows virtual Machine Optimize and prepare Windows virtual machines to set up Horizon desktop VMs Create Linux Desktops Create a Linux VM for Horizon Install Horizon Agent on a Linux virtual machine Optimize and prepare Linux virtual machines to set up Horizon desktop VMs Creating and Managing Desktop Pools Identify the steps to set up a template for desktop pool deployment List the steps to add desktops to the VMware Horizon© Connection Server? inventory Compare dedicated-assignment and floating-assignment pools Outline the steps to create an automated pool Define user entitlement Explain the hierarchy of global, pool-level, and user-level policies VMware Horizon Client Options Describe the different clients and their benefits Access the Horizon desktop using various Horizon clients and HTML Configure integrated printing, USB redirection, and the shared folders option Configure session collaboration and media optimization for Microsoft Teams Creating and Managing Instant-Clone Desktop Pools List the advantages of instant clones Explain the provisioning technology used for instant clone desktop pools Set up an automated pool of instant clones Push updated images to instant clone desktop pools Creating RDS Desktop and Application Pools Explain the difference between an RDS desktop pool and an automated pool Compare and contrast an RDS session host pool, a farm, and an application pool Create an RDS desktop pool and an application pool Access RDS desktops and application from Horizon Client Use the instant clone technology to automate the build-out of Remote Desktop Session Host farms Configure load-balancing for RDSHs on a farm Monitoring VMware Horizon Monitor the status of the Horizon components using the Horizon Administrator console dashboard Monitor desktop sessions using the HelpDesk tool Monitor the performance of the remote desktop using the Horizon Performance Tracker Horizon Connection Server Recognize the VMware Horizon reference architecture Identify the Horizon Connection Server supported features Identify the recommended system requirements for Horizon Connection Server Configure the Horizon event database Outline the steps for the initial configuration of Horizon Connection Server Discuss the AD LDS database as a critical {an important component?} component of the Horizon Connection Server installation Horizon Protocols Compare the remote display protocols that are available in VMware Horizon Describe the BLAST Display Protocol Codecs Summarize the BLAST Codec options List the ideal applications for each BLAST codec Describe the BLAST and PCoIP ADMX GPO common configurations Graphics in Horizon Describe the 3D rendering options available in Horizon 8 Compare vSGA and vDGA List the steps to configure graphics cards for use in a Horizon environment Securing Connections: Network Compare tunnels and direct connections for client access to desktops Discuss the benefits of using Unified Access Gateway List the Unified Access Gateway firewall rules Configure TLS certificates in Horizon Securing Connections: Authentication Compare the authentication options that Horizon Connection Server supports Restrict access to the Horizon remote desktops using restricted entitlements Describe the smart card authentication methods that Horizon Connection Server supports Explain the purpose of permissions, roles, and privileges in VMware Horizon Create custom roles Horizon Scalability Describe the purpose of a replica connection server Explain how multiple Horizon Connection Server instances in a pod maintain synchronization List the steps to configure graphics cards for use in a Horizon environment Configure a load balancer for use in a Horizon environment Explain Horizon Cloud Pod Architecture LDAP replication. Explain Horizon Cloud Pod Architecture scalability options Horizon Cloud and Universal Broker Recognize the features and benefits of Horizon Cloud Service Use Universal broker to connect to a Horizon Cloud instance Configure and pair the Horizon Cloud Connector appliance with Horizon Connection Server Workspace ONE Access and Virtual Application Management Recognize the features and benefits of Workspace ONE Access Explain identity management in Workspace ONE Access Explain access management in Workspace ONE Access Describe the requirements to install and configure True SSO in a Horizon environment Describe the Workspace ONE Access directory integration Deploy virtual applications with Workspace services Additional course details:Notes Delivery by TDSynex, Exit Certified and New Horizons an VMware Authorised Training Centre (VATC) Nexus Humans VMware Horizon: Deploy and Manage [V8.8] training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the VMware Horizon: Deploy and Manage [V8.8] course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.
![VMware Horizon: Deploy and Manage [V8.8]](https://cademy-images-io.b-cdn.net/9dd9d42b-e7b9-4598-8d01-a30d0144ae51/4c81f130-71bf-4635-b7c6-375aff235529/original.png?width=3840)
Management of Value (MoV) Foundation: In-House Training
By IIL Europe Ltd
Management of Value (MoV®) Foundation This interactive MoV® Foundation course provides a modular and case-study-driven approach to learning Management of Value (MoV). The core knowledge is structured and comprehensive; and well-rounded modules cover the methodology and various techniques. A case study is used to help appreciate the relevance of MoV in its practical application. What you will Learn Upon completion of an MoV course candidates should be able to discuss and explain: The main processes and techniques used within MoV and the reasons for using them How MoV may be applied at portfolio, program, project and operational levels The differences in applying MoV at different stages in a project and the expected outputs from a MoV Study at each stage The circumstances under which MoV should be used The concept of value and how value may be improved The main benefits arising from the use of MoV Approaches for implementing MoV How to respond to external and internal influences The principles of embedding MoV into an organization The key topics in document checklists, the toolbox, health check, organizational maturity and individual competence. Upon successful completion of this course, you will be able to: Organize and contribute constructively to a Management of Value (MoV) Study Demonstrate a knowledge of MoV principles, processes, approach and environment Analyse a company, program or project to establish its organizational value; includes identification and weighting of Value Drivers Pass the AXELOS MoV Foundation Examination Introduction to value management and MoV Value and Value Management Capabilities, Outcomes, Benefits and Disbenefits What is Value? What is Management of Value (MoV)? Why use MoV? Where use MoV? When MoV should be used? What using MoV involve? Selected MoV benefits Relationship with other AXELOS Global Best Practices and Models How MoV fits with other AXELOS Global Best Practice Guides MoV principles Align with organization's objectives Focus on functions and required outcomes Balance the variables to maximise value Apply throughout the investment decision Tailor MoV to suit the subject Learn from experience and improve Assign clear roles and responsibilities and build a supportive culture MoV processes Frame the programme or project Gather information Analyse information Process information Evaluate and select Develop Value Improving Proposals Implement and share outputs MoV techniques Function Analysis Function Analysis System Technique (FAST) Traditional (or classic) FAST Technical FAST Customer FAST Value Trees Measuring value Value profiling (a.k.a. value benchmarking) Simple multi-attribute rating technique (a.k.a. SMART) Value index Value metrics Value for money (VfM) ratio Value Engineering / Analysis Common techniques used in MoV Analysis of information Benchmarking Process Mapping Root Cause Analysis Discounted Cash Flow Analysis Generating Ideas Brainstorming Evaluation and option selection Option Selection Matrix Idea selection Allocation to Categories Idea Selection Matrix Weighting techniques Paired Comparisons Points Distribution Developing VIPs Developing Proposals Cost Benefit Analysis Building Decisions Implementing VIPs Implementation Plans Feedback Following up Tracking Benefits Approach to Implementation Generic approach to MoV implementation Plan the MoV activities Understand and articulate value Prioritize value Improve value Quantify value Monitor improvements in value Learn lessons Environmental factors Portfolio Considerations Programme considerations Project considerations Operational Considerations Embedding MoV into an organization Benefits of Embedding MoV into an organization MoV Policy MoV Policy Composition Embedding MoV into an organisation Key steps Suggested MoV Management Structure Overcoming barriers We do it anyway It takes up too much time We can't afford to make the changes What's in it for me? Don't fix it if it ain't broke Fixed returns on investment MoV products Briefing Meeting Agenda (A.1) Communications Checklist (A.2) Equipment list for an Effective Study/Workshop (A.3) Invitation to join the Study Team (A.4) Option Evaluation Matrix (A.5) Plan the Study (A.6) Recording Idea Selection (A.7) Reporting Study outputs (A.8) Scoping the Study (A.9) Study or Workshop Handbook (A.10) Value-Improvement Proposal Forms (A.11) Value Improvement Tracking Report (A.12) MoV toolbox MoV health check and maturity model P3M3 Maturity Model MoV Maturity Model (aligned with P3M3)
