- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
3892 Courses in Cardiff delivered Live Online
Managing Successful Programmes 5th Edition Foundation: In-House
By IIL Europe Ltd
Managing Successful Programmes (MSP®) 5th Edition Foundation: In-House Training Managing Successful Programmes (MSP®) is a globally-recognized framework for best practice programme management. MSP certification provides guidance for programme managers, business change managers and the next step for project managers to develop their knowledge and skills to be able to positively respond to the challenges for managing programmes and larger, more strategic or multiple projects. MSP 5th edition emphasizes flexibility, adaptability, and responsiveness by adopting an incremental approach to the programme lifecycle and thus enabling organizational agility. AXELOS offers two levels of MSP Examination: MSP Foundation and MSP Practitioner. The MSP Foundation Examination is intended to assess whether the candidate can demonstrate sufficient recall and understanding of the MSP programme management framework. The MSP Foundation qualification is a prerequisite for the MSP Practitioner Examination, which assesses the ability to apply understanding of the MSP programme management framework in context. The MSP® 5th Edition Foundation course is a training based on the exam specification for MSP Foundation certification and is aligned with the Managing Successful Programmes (5th Edition) guide from AXELOS. What you will Learn At the end of this course, participants will be able to: Understand key concepts relating to programmes and MSP Understand how the MSP principles underpin the MSP framework Understand the MSP themes and how they are applied throughout the programme Understand the MSP processes and how they are carried out throughout the programme Key Concepts of MSP Programmes Three Lenses of MSP Principles Themes and Governance Organization Organization Theme Organization Structure Individual Roles Stakeholder Management Design Design Theme Benefits Risk Identification and Prioritization Target Operating Model Documents and Key Roles Justification Justification Theme Business Case Financial Planning Documents and Key Roles Structure Structure Theme Delivery Planning Dependencies Benefits Realization Plan Resourcing Documents and Key Roles Knowledge Knowledge Theme Knowledge Management Information Management Document and Key Roles Assurance Assurance Theme Assurance at Multiple Levels Assurance Planning Document and Key Roles Decisions Decisions Theme Issue Resolution Risk Response Data Gathering and Reporting Options and Analysis Document and Key Roles MSP Processes Identify the Programmeâ¯â¯â¯ Design the Outcomes Plan Progressive Delivery Deliver the Capabilities Embed the Outcomes Evaluate New Information Close the Programme

Overview Overview The purpose of this course is to enable participants to understand and apply the principles of emergency response planning and crisis management. It considers the need for emergency and crisis response planning and an integrated approach to emergency management. Training typically covers: Crisis management structure and staffing an emergency response team Incident reporting and notification Operational processes Guidance of facility response policies and procedures Annual testing and evaluation of the crisis management plan Upcoming Events Online (USD 1950) Online Streaming Live (Flexible Dates) At Venue (USD 4500) Dubai 13 March - 17 March Istanbul 20 March - 24 March London 20 March - 24 March For more dates and Venue, Please email sales@gbacorporate.co.uk

SC-100T00 Microsoft Cybersecurity Architect
By Nexus Human
Duration 4 Days 24 CPD hours This course is intended for This course is for experienced cloud security engineers who have taken a previous certification in the security, compliance and identity portfolio. Specifically, students should have advanced experience and knowledge in a wide range of security engineering areas, including identity and access, platform protection, security operations, securing data, and securing applications. They should also have experience with hybrid and cloud implementations. Beginning students should instead take the course SC-900: Microsoft Security, Compliance, and Identity Fundamentals. This is an advanced, expert-level course. Although not required to attend, students are strongly encouraged to have taken and passed another associate level certification in the security, compliance and identity portfolio (such as AZ-500, SC-200 or SC-300) before attending this class. This course prepares students with the expertise to design and evaluate cybersecurity strategies in the following areas: Zero Trust, Governance Risk Compliance (GRC), security operations (SecOps), and data and applications. Students will also learn how to design and architect solutions using zero trust principles and specify security requirements for cloud infrastructure in different service models (SaaS, PaaS, IaaS). Prerequisites Highly recommended to have attended and passed one of the associate level certifications in the security, compliance and identity portfolio (such as AZ-500T00 Microsoft Azure Security Technologies, SC-200T00: Microsoft Security Operations Analyst, or SC-300T00: Microsoft Identity and Access Administrator.) Advanced experience and knowledge in identity and access, platform protection, security operations, securing data and securing applications. Experience with hybrid and cloud implementations. 1 - Introduction to Zero Trust and best practice frameworks Zero Trust initiatives Zero Trust technology pillars part 1 Zero Trust technology pillars part 2 2 - Design solutions that align with the Cloud Adoption Framework (CAF) and Well-Architected Framework (WAF) Define a security strategy Cloud Adoption Framework secure methodology Design security with Azure Landing Zones The Well-Architected Framework security pillar 3 - Design solutions that align with the Microsoft Cybersecurity Reference Architecture (MCRA) and Microsoft cloud security benchmark (MCSB) Design solutions with best practices for capabilities and controls Design solutions with best practices for attack protection 4 - Design a resiliency strategy for common cyberthreats like ransomware Common cyberthreats and attack patterns Support business resiliency Ransomware protection Configurations for secure backup and restore Security updates 5 - Case study: Design solutions that align with security best practices and priorities Case study description Case study answers Conceptual walkthrough Technical walkthrough 6 - Design solutions for regulatory compliance Translate compliance requirements into a security solution Address compliance requirements with Microsoft Purview Address privacy requirements with Microsoft Priva Address security and compliance requirements with Azure policy Evaluate infrastructure compliance with Defender for Cloud 7 - Design solutions for identity and access management Design cloud, hybrid and multicloud access strategies (including Azure AD) Design a solution for external identities Design modern authentication and authorization strategies Align conditional access and Zero Trust Specify requirements to secure Active Directory Domain Services (AD DS) Design a solution to manage secrets, keys, and certificates 8 - Design solutions for securing privileged access The enterprise access model Design identity governance solutions Design a solution to secure tenant administration Design a solution for cloud infrastructure entitlement management (CIEM) Design a solution for privileged access workstations and bastion services 9 - Design solutions for security operations Design security operations capabilities in hybrid and multicloud environments Design centralized logging and auditing Design security information and event management (SIEM) solutions Design solutions for detection and response Design a solution for security orchestration, automation, and response (SOAR) Design security workflows Design threat detection coverage 10 - Case study: Design security operations, identity and compliance capabilities Case study description Case study answers Conceptual walkthrough Technical walkthrough 11 - Design solutions for securing Microsoft 365 Evaluate security posture for collaboration and productivity workloads Design a Microsoft 365 Defender solution Design configurations and operational practices for Microsoft 365 12 - Design solutions for securing applications Design and implement standards to secure application development Evaluate security posture of existing application portfolios Evaluate application threats with threat modeling Design security lifecycle strategy for applications Secure access for workload identities Design a solution for API management and security Design a solution for secure access to applications 13 - Design solutions for securing an organization's data Design a solution for data discovery and classification using Microsoft Purview Design a solution for data protection Design data security for Azure workloads Design security for Azure Storage Design a security solution with Microsoft Defender for SQL and Microsoft Defender for Storage 14 - Case study: Design security solutions for applications and data Case study description Case study answers Conceptual walkthrough Technical walkthrough 15 - Specify requirements for securing SaaS, PaaS, and IaaS services Specify security baselines for SaaS, PaaS, and IaaS services Specify security requirements for web workloads Specify security requirements for containers and container orchestration 16 - Design solutions for security posture management in hybrid and multicloud environments Evaluate security posture by using Microsoft Cloud Security Benchmark Design integrated posture management and workload protection Evaluate security posture by using Microsoft Defender for Cloud Posture evaluation with Microsoft Defender for Cloud secure score Design cloud workload protection with Microsoft Defender for Cloud Integrate hybrid and multicloud environments with Azure Arc Design a solution for external attack surface management 17 - Design solutions for securing server and client endpoints Specify server security requirements Specify requirements for mobile devices and clients Specify internet of things (IoT) and embedded device security requirements Secure operational technology (OT) and industrial control systems (ICS) with Microsoft Defender for IoT Specify security baselines for server and client endpoints Design a solution for secure remote access 18 - Design solutions for network security Design solutions for network segmentation Design solutions for traffic filtering with network security groups Design solutions for network posture management Design solutions for network monitoring 19 - Case study: Design security solutions for infrastructure Case study description Case study answers Conceptual walkthrough Technical walkthrough Additional course details: Nexus Humans SC-100T00 Microsoft Cybersecurity Architect training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the SC-100T00 Microsoft Cybersecurity Architect course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

Certified Information Privacy Technologist (CIPT)
By Training Centre
The CIPT is the first and only certification of its kind worldwide. It was launched by the IAPP in 2014 and updated in early 2023 to meet the growing need that only tech pros can fill-securing data privacy at all stages of IT product and service lifecycles. Whether you work in the public or private sector, data privacy skills are quickly becoming a must-have-and that's a great opportunity for you. The CIPT certification also holds accreditation under ISO 17024: 2012 About This Course What will you learn? Critical data protection concepts and practices that impact IT Consumer data protection expectations and responsibility How to bake privacy into early stages of IT products and services for cost control, accuracy and speed-to-market How to establish data protection practices for data collection and transfer How to pre-empt data protection issues in the Internet of Things How to factor data protection into data classification and emerging tech such as cloud computing, facial recognition and surveillance How to communicate data protection issues with partners such as management, development, marketing and legal. This course has two programmatic modules, the first four areas focus on the fundamentals of data protection. The second module takes the fundamentals and puts it into practice. MODULE 1: Fundamentals of Information Privacy Unit 1: Common Principles and Approaches to Privacy This unit includes a brief discussion of the modern history of privacy, an introduction to types of information, an overview of information risk management and a summary of modern privacy principles. Unit 2: Jurisdiction and Industries This unit introduces the major privacy models employed around the globe and provides an overview of privacy and data protection regulation by jurisdictions and industry sectors. Unit 3: Information Security: Safeguarding Personal Information This unit presents introductions to information security, including definitions, elements, standards and threats/vulnerabilities, as well as introductions to information security management and governance, including frameworks, controls, cryptography and identity and access management (IAM). Unit 4: Online Privacy: Using Personal Information on Websites and with Other Internet-related Technologies This unit examines the web as a platform, as well as privacy considerations for sensitive online information, including policies and notices, access, security, authentication and data collection. Additional topics include children's online privacy, email, searches, online marketing and advertising, social media, online assurance, cloud computing and mobile devices. MODULE 2: Privacy in Technology Unit 1: Understanding the Need for Privacy in the IT Environment This unit highlights the impact that regulatory activities, security threats, advances in technology and the increasing proliferation of social networks have on IT departments. Unit 2: Core Privacy Concepts This unit reveals how privacy compliance becomes more attainable through developing information lifecycle plans, data identification and classification systems and data flow diagrams. Unit 3: Regulations and Standards Impacting Privacy in IT This unit introduces privacy laws, regulations and standards that can help IT professionals design better privacy programmes and systems to handle personal information throughout the data lifecycle. Unit 4: Privacy in Systems and Applications This unit develops an understanding of the risks inherent in the IT environment and how to address them. Unit 5: Online Privacy Issues This unit presents information about online threats, threat prevention and the role of IT professionals in ensuring proper handling of user data. Unit 6: De-identifying and Anonymizing Personally Identifiable Information This unit reveals the importance of personally identifiable information and methods for ensuring its protection. Unit 7: Cloud Computing This unit evaluates privacy and security concerns associated with cloud services, and standards that exist to advise on their use. Prerequisites There are no prerequisites for this course but attendees would benefit from a review of the materials on the IAPP site. What's Included? 1 years membership of the IAPP Refreshments & Lunch (Classroom courses only) Participant Guide Official Study Guides Official Practice Exam Official Q&A The Exam Fees Who Should Attend? The CIPT credential shows you've got the knowledge to build your organisation's data protection structures from the ground up. With regulators worldwide calling for tech professionals to factor data protection into their products and services, the job market for privacy-trained IT pros has never been stronger. As a result, the CIPT is targeted towards; Data Protection Officers IT Managers and Administrators Records Managers System Developers IT Security specialists Accreditation Our Guarantee We are an approved IAPP Training Partner. You can learn wherever and whenever you want with our robust classroom and interactive online training courses. Our courses are taught by qualified practitioners with a minimum of 25 years commercial experience. We strive to give our delegates the hands-on experience. Our courses are all-inclusive with no hidden extras. The one-off cost covers the training, all course materials, and exam voucher. Our aim: To achieve a 100% first time pass rate on all our instructor-led courses. Our Promise: Pass first time or 'train' again for FREE. *FREE training offered for retakes - come back within a year and only pay for the exam.

Primary School RSE for learners with SEND
By Claire Lightley
Aim The aim of this course is to develop the confidence and practical skills of participants to deliver great quality, timely RSE for pupils with SEND in primary education Learning outcomes By the end of the training participants will have: had an update of the DfE guidance about relationships education and health education and optional primary sex education thought about what language (spoken and visual) to use in the school to talk about private body parts and during personal care discussed how to deal with touching behaviours in the classroom identified relevant, age appropriate resources to use for RSE Course Outline Welcome and introductions and working agreement Government guidance Language and symbols Dealing with touching behaviours in the classroom Resources and how to use them Close

Prioritizing Your Time Effectively
By Nexus Human
Duration 2 Days 12 CPD hours This course is intended for Professionals wishing to maximize their productivity and efficiency by investing their time more effectively will benefit from this course. Overview Time Management Prioritization Organization Workflow Productivity Time is limited, so getting the most out of every minute is critical. In this course, students will learn to improve their focus, prioritize tasks, identify and avoid obstacles to staying on track, and develop strategies to get the most out of their time. Students will acquire time management tools and decision-making techniques to help focus on purpose and achieve your goals, balancing the needs of both business and personal life. Private classes on this topic are available. We can address your organization?s issues, time constraints, and save you money, too. Contact us to find out how. 1. Wise Time Management Identifying Time Wasters Applying the 80/20 Rule Utilizing Calendars Creating Rituals 2. Prioritizing Your Time Taking Charge of Your Time Protecting Your Time through Assertiveness 3. Planning Wisely Managing the Power of Your Productivity Journal Finding Hidden Time Chunking, Blocking, and Tackling 4. Organizing Your Workspace Decluttering Managing Workflow Taking Control over Email 5. Tackling Procrastination Knowing Why You Procrastinate Nine Ways to Avoid Procrastination 6. Crisis Management Weathering the Storm Creating and Executing a Plan Applying Lessons Learned 7. Increase Your Productivity Applying Productivity Tools Finding What Works Eliminating the Word \'Should\' Building on Success Additional course details: Nexus Humans Prioritizing Your Time Effectively training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the Prioritizing Your Time Effectively course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

ISO 27001: 2022 Internal Auditor
By Training Centre
During this training course, you will acquire the knowledge and skills to plan and carry out internal audits in compliance with ISO 19011. About This Course Based on a number of exercises, you will learn how to utilise audit techniques and become competent to manage an internal audit programme, communicate with customers, and manage conflict resolution. After acquiring the necessary expertise, you can sit for the exam and gain 'Certified ISO/IEC 27001: 2022 Internal Auditor' Certification. By holding this Certificate, you will demonstrate that you have the capabilities and competencies to audit organizations based on best practices. Learning objectives By the end of this training course, the participants will be able to: Explain the concepts and principles of an information security management system (ISMS) based on ISO/IEC 27001: 2022 Analyse the ISO/IEC 27001: 2022 requirements for an ISMS from the perspective of an auditor Evaluate the ISMS conformity requirements Plan, conduct, and close an ISO/IEC 27001: 2022 compliance audit programme Assist an organisation in transitioning from ISO 27001: 2013 Deliver an ISO/IEC 27001: 2022 Internal audit programme Our approach This training is based on both theory and best practices used in ISMS audits Lessons are illustrated with examples based on case studies Practical exercises are based on a real world case study Practice tests are similar to the Certification Exam Course Overview Module 1 Foundational Audit principles and concepts of Information Security Management System (ISMS) Module 2 The Information Security Management System (ISMS) Module 3 ISO 19011 audit concepts and principles Module 4 Preparation of an ISO/IEC 27001 audit Module 5 Providing an ISO/IEC 27001 audit Module 6 Closing an ISO/IEC 27001 audit Module 7 Managing an ISO/IEC 27001 Internal audit programme Course Agenda Day 1: Introduction to the information security management system (ISMS) and ISO/IEC 19011 Day 2: Audit principles, preparation, and initiation of an audit Day 3: Audit activities, Closing the Audit and the Certification exam Accreditation Assessment All candidates at official training courses are tested throughout their course with quizzes and exercises, in combination with a final exam held on the last day of the course. Both elements are a part of the overall score. For this course, the final exam constitutes a 10 question essay type which should be completed within 125 minutes. A passing score is achieved at 70%. Self-study candidates can purchase an exam voucher from our Store. Exam results are returned within 24 hours, with successful candidates receiving both a digital badge and a Certificate of Achievement Prerequisites A general understanding of ISO/IEC 27001: 2022 and knowledge of audit principles. Provided by This course is Accredited by NACS and Administered by the IECB What's Included? Refreshments & Lunch (Classroom courses only) Course Slide Deck Official Study Guides CPD Certificate The Exam Who Should Attend? Auditors seeking to perform Internal Information Security Management System (ISMS) certification audits Managers or consultants seeking to master an Information Security Management System audit process Individuals responsible for maintaining conformance with Information Security Management System requirements Technical experts seeking to prepare for an Information Security Management System audit Expert advisors in Information Security Management

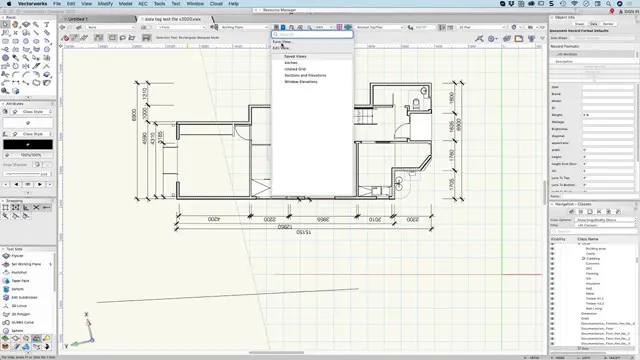
Vectorworks Evening Introduction Training Course
By Real Animation Works
Vectorworks Evening Course face to face One to one
IATP - Non-Licensable Work With Asbestos Including NNLW
By Airborne Environmental Consultants Ltd
This course provides the delegate with the theoretical and practical skills to undertake non-licensed works with ACM's. Persons requiring this type of training would include trade operatives undertaking tasks with ACM's as defined in HSG210 and in accordance with CAR 2012 Reg 3(2). In addition to the Asbestos Awareness, those employees whose work will knowingly disturb ACMs, and which is defined as non-licensable work or NNLW, should receive additional task-specific information, instruction and training.

How to talk to children who have a parent with a mental illness
By Our Time Charity
This comprehensive training equips you with practical strategies to talk to children about parental mental illness.
