- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
3897 Courses in Cardiff delivered Live Online
Cloud technologies training course description This course provides an introduction to cloud technologies, including, configuration and deployment, security, maintenance, and management. It covers all aspects of cloud computing infrastructure. It will help you to master the fundamental concepts, terminology, and characteristics of cloud computing. . What will you learn Contrast and compare AWS, GCP and Azure. Explain the different cloud services, models and characteristics. Explain cloud virtualization components and options. Explain cloud security options. Describe cloud automation, orchestration, monitoring and performance options. Cloud technologies training course details Who will benefit: Anyone working with or looking to work with cloud technologies. Prerequisites: None. Duration 2 days Cloud technologies training course contents What is the cloud? The Internet Cloud computing Benefits Disadvantages Cloud services IaaS, PaaS, SaaS, others. Cloud service providers AWS, GCP Microsoft Azure, others Cloud architectures Private, public, hybrid others Cloud based delivery The cloud and virtualization Virtual Machines, networks, storage, deployment. Accessing the Virtual Machine Secure cloud environments Security considerations. Data privacy considerations Automation and orchestration Monitoring and performance Performance Cost issues Cost containment

Fundamentals of E&P Data Management
By EnergyEdge - Training for a Sustainable Energy Future
About this Virtual Instructor Led Training (VILT) The energy industry has started its journey to be more data centric by embracing the industry 4.0 concept. As a result, data management - which was considered until recently as a back-office service to support geoscience, reservoir management, engineering, production and maintenance - is now given the spotlight! To become an active stakeholder in this important transition in E&P data management, it is necessary to understand the new technical opportunities offered by the Cloud, Artificial Intelligence and how data governance can pave the way towards more reliable and resilient processes within E&P domain. Several key questions that need to be addressed: Why place more focus on data assets? Is data management just about serving geoscientists or engineers with fresh data? What is the value of data management in the E&P sector for decision making? How to convince the data consumers that the data we provide is reliable? Is the data architecture of my organization appropriate and sustainable? The purpose of this 5 half-day Virtual Instructor Led Training (VILT) course is to present the data challenges facing the energy organizations today and see how they practically solve them. The backbone of this course is based on the DAMA Book of Knowledge for Data Management. The main data management activities are described in sequence with a particular focus on recent technological developments. Training Objectives Upon completion of this VILT course, the participants will be able to: Understand why the data asset is now considered as a main asset by energy organizations Appreciate the importance of data governance and become an active stakeholder of it Understand the architecture and implementation of data structure in their professional environment Get familiarized with the more important data management activities such as data security and data quality Integrate their subsurface and surface engineering skills with the data managements concepts This VILT course is unique on several points: All notions are explained by some short presentations. For each of them, a set of video, exercises, quizzes will be provided to help develop an engaging experience between the trainer and the participants A pre-course questionnaire to help the trainer focus on the participants' needs and learning objectives A detailed reference manual A lexicon of terms for data-management Limited class size to encourage the interactivity Target Audience This VILT course is intended for: Junior/new data managers Geoscientists Reservoir engineers Producers Maintenance specialists Construction specialists Human resources Legal Course Level Basic or Foundation Training Methods The VILT course will be delivered online in 5 half-days consisting 4 hours per day, with 2 breaks of 10 minutes per day. Course Duration: 5 half-day sessions, 4 hours per session (20 hours in total). Trainer Your expert course leader is a geologist by education who has dedicated his career to subsurface data management services. In 2016, he initiated a tech startup dedicated to Data Management using Artificial Intelligence (AI) tools. He is heavily involved in developing business plans, pricing strategies, partnerships, marketing and SEO, and is the co-author of several Machine Learning publications. He also delivers training on Data Management and Data Science to students and professionals. Based in France, he was formerly Vice President, Sales & Marketing at CGG where he was in charge of the Data Management Services strategy, Sales Manager at Spie O&G Services where he initiated the Geoscience technical assistance activities and Product Manager of interactive seismic inversion software design and marketing at Paradigm. POST TRAINING COACHING SUPPORT (OPTIONAL) To further optimise your learning experience from our courses, we also offer individualized 'One to One' coaching support for 2 hours post training. We can help improve your competence in your chosen area of interest, based on your learning needs and available hours. This is a great opportunity to improve your capability and confidence in a particular area of expertise. It will be delivered over a secure video conference call by one of our senior trainers. They will work with you to create a tailor-made coaching program that will help you achieve your goals faster. Request for further information about post training coaching support and fees applicable for this. Accreditions And Affliations

SDH training course description Our SDH training course is designed for those with a basic knowledge of the principles of telecommunication digital transmission techniques. An overview of the existing transmission hierarchies and their limitations is provided with an introduction to the Synchronous Digital Hierarchy (SDH). The advantages of SDH are explained fully. What will you learn Identify the major limitations of the PDH network. Outline the advantages of using the SDH. Illustrate the various SDH equipment and network topologies. Describe the principles of the SDH multiplexing structure. SDH training course details Who will benefit: Anyone working with SDH. Prerequisites: It should be noted that this course will assume some basic telecommunication transmission knowledge from the delegates attending. This may be accomplished by attending the Introduction to Telecommunications course. Duration 2 days SDH training course contents Introduction to SDH Timing and synchronisation of digital signals, the plesiochronous digital hierarchy (PDH), the synchronous digital hierarchy (SDH), service protection with SDH SDH Multiplexing Techniques The multiplexing principles of SDH, mapping and aligning a 2Mbit/s tributary into a TU-12, aligning the VC-12 in a TU-12, multiplexing TU-12's into a TUG-2, multiplexing TUG-2's into a TUG-3, multiplexing TUG-3's into a VC-4, the VC-4 path overhead, the STM-1 frame, the AU-4 pointer, the STM-1 section overheads, multiplexer section protection, transmission at rates higher than STM-1, concatenation line transmission functions in SDH SONET Multiplexing Techniques Mapping a DS1 tributary into a virtual tributary, aligning the VT-SPE into a VT frame, mapping the VTGs into a STS-1 SPE, the STS-1 synchronous payload envelope, the STS-1 frame SONET network sections and lines transmissions at higher rates than STS-1 SDH Functions and Facilities SDH network topologies, structure of SDH equipment, synchronisation of SDH networks, protection switching in SDH networks, SDH alarm structure, SDH performance monitoring, testing of SDH, equipment and systems, network management and SDH, asynchronous transfer mode (ATM), future services and technologies OSI Telecommunications Network Management Definition of network management, managing telecom equipment, the managed object library, the management information base, the telecommunications management network (TMN), the Q3 protocol.

ISO 22301 Lead Auditor
By Training Centre
ISO 22301 Lead Auditor training enables you to develop the necessary expertise to perform a Business Continuity Management System (BCMS) audit by applying widely recognized audit principles, procedures and techniques. About This Course During this training course, you will acquire the knowledge and skills to plan and carry out internal and external audits in compliance with ISO 19011 and ISO/IEC 17021-1 certification process. Based on practical exercises, you will be able to master audit techniques and become competent to manage an audit program, audit team, communication with customers, and conflict resolution. After attending this 4 day course, candidates can sit for the exam with the aim of gaining the "ISO22301 Lead Auditor' credential. You will then be in a position to demonstrate that you have the capabilities and competencies to audit organizations based on best practices. Learning objectives Understand the operations of a Business Continuity Management System based on ISO 22301 Acknowledge the correlation between ISO 22301 and other standards and regulatory frameworks Understand an auditor's role to: plan, lead and follow-up on a management system audit in accordance with ISO 19011 Learn how to lead an audit and audit team Learn how to interpret the requirements of ISO 22301 in the context of a BCMS audit Acquire the competencies of an auditor to: plan an audit, lead an audit, draft reports, and follow-up on an audit in compliance with ISO 19011 Educational approach This training is based on both theory and best practices used in BCMS audits Lecture sessions are illustrated with examples based on case studies Practical exercises are based on a case study which includes role playing and discussions Practice tests are similar to the Certification Exam Prerequisites A foundational understanding of ISO 22301 and knowledge of audit principles. What's Included? Refreshments & Lunch (Classroom courses only) Course Slide Deck Official Study Materials CPD Certificate The Exam fees Who Should Attend? Auditors seeking to perform and lead Business Continuity Management System (BCMS) certification audits Managers or consultants seeking to master a Business Continuity Management System audit process Individuals responsible for maintaining conformance with Business Continuity Management System requirements Technical experts seeking to prepare for a Business Continuity Management System audit Expert advisors in Business Continuity Management Our Guarantee We are an approved IECB Training Partner. You can learn wherever and whenever you want with our robust classroom and interactive online training courses. Our courses are taught by qualified practitioners with commercial experience. We strive to give our delegates the hands-on experience. Our courses are all-inclusive with no hidden extras. The one-off cost covers the training, all course materials, and exam voucher. Our aim: To achieve a 100% first time pass rate on all our instructor-led courses. Our Promise: Pass first time or 'train' again for FREE. *FREE training offered for retakes - come back within a year and only pay for the exam. Assessment The exam is a 12 question essay type exam completed in the afternoon of Day 4. The pass mark for the exam is 70%. Exam results are provided within 24 hours. Provided by This course is Accredited by NACSand administered by the IECB. Accreditation

ISO 9001 Lead Auditor
By Training Centre
The ISO 9001 Lead Auditor training enables you to develop the necessary expertise to perform a Quality Management System (QMS) audit by applying widely recognized audit principles, procedures and techniques. About This Course During this training course, you will acquire the knowledge and skills to plan and carry out internal and external audits in compliance with ISO 19011 and the certification process according to ISO/IEC 17021-1. Based on practical exercises, you will be able to master the audit techniques and become competent to manage an audit program, audit team, communication with customers, and conflict resolution. After acquiring the necessary expertise to perform this audit, you can sit for the exam and gain "Certified ISO 9001 Lead Auditor' credential. By holding this Certificate,, you will demonstrate that you have the capabilities and competencies to audit organizations based on best practices. Learning objectives Understand the operations of a Quality Management System (QMS) based on ISO 9001 Acknowledge the correlation between ISO 9001 and other standards and regulatory frameworks Understand the auditor's role to: plan, lead and follow-up on a management system audit in accordance with ISO 19011 Learn how to lead an audit and audit team Learn how to interpret the requirements of ISO 9001 in the context of a QMS audit Acquire the competencies of an auditor to: plan an audit, lead an audit, draft reports, and follow-up on an audit in compliance with ISO 19011 Educational approach This training is based on both theory and best practices used in QMS audits Lecture sessions are illustrated with practical questions and examples Practical exercises include examples and case study discussions Practice tests are similar to the Certification Exam Prerequisites A fundamental understanding of ISO 9001 and comprehensive knowledge of audit principles. What's Included? Refreshments & Lunch (Classroom only) Course Slide Deck Official Study Guides The Exam Who Should Attend? Auditors seeking to perform and lead Quality Management System (QMS) certification audits Managers or consultants seeking to master a Quality Management System audit process Individuals responsible for maintaining conformance with QMS requirements Technical experts seeking to prepare for a Quality Management System audit Expert advisors in Quality Management Accreditation Our Guarantee We are an approved IECB Training Partner. You can learn wherever and whenever you want with our robust classroom and interactive online training courses. Our courses are taught by qualified practitioners with commercial experience. We strive to give our delegates the hands-on experience. Our courses are all-inclusive with no hidden extras. The one-off cost covers the training, all course materials, and exam voucher. Our aim: To achieve a 100% first time pass rate on all our instructor-led courses. Our Promise: Pass first time or 'train' again for FREE. *FREE training and exam retake offered Assessment Delegates sit a combined exam, consisting of in-course quizzes and exercises, as well as a final 12 question, essay type exam on Day 4 of the course. The overall passing score is 70%, to be achieved within the 150 minute time allowance. Exam results are provided within 24 hours, with both a Certificate and a digital badge provided as proof of success. Provided by This course is Accredited by NACS and Administered by theIECB

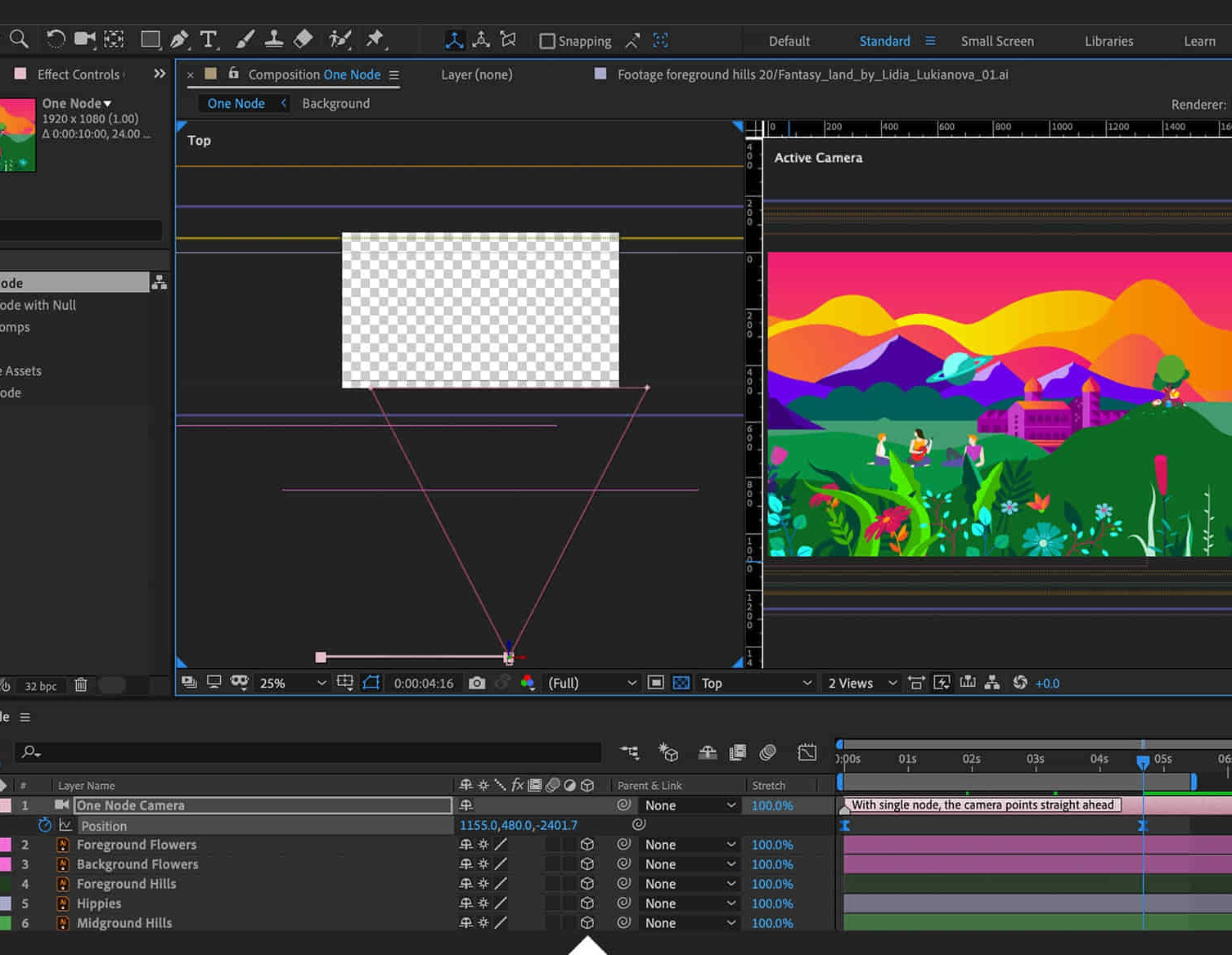
Adobe After Effects Beginners to Advanced Course
By ATL Autocad Training London
Adobe After Effects Beginners to Advanced Course Tailored for motion graphics designers basic to expert level. Explore advanced topics including motion tracking, green screen compositing, text animation, and techniques like expressions. Learn animations based on geometric proportions in our Advanced Motion Methods module. Click here for more info: Website Duration: 40 hours Approach: 1-on1 sessions and Customized content. Schedule: Choose your own day and time. Mon to Sat between 9 am and 5 pm. Module 1: Introduction to After Effects Exploring Adobe After Effects Navigating the Interface Configuring Preferences Utilizing Auto-Save Feature Module 2: Projects and Compositions Creating New Projects/Compositions Importing and Organizing Assets Working with Layers Module 3: Animation Techniques Keyframe Essentials Motion Paths and Modifications Graph Editor Insights Motion Control Tools Module 4: Layer Management Organizing and Navigating Layers Layer Visibility and Locking Switches and Modes in Detail Module 5: Shape Manipulation Shape Layers Fundamentals Creating and Animating Shapes Anchor Point Adjustment Module 6: Effects Mastery Applying and Customizing Effects Exploring Various Effects Examples Module 7: Masks and Track Mattes Mask Creation and Animation Track Matte Techniques Module 8: Text and Typography Animation Working with Text Layers Text Animation Presets Layer Styles for Typography Module 9: Exporting Your Creations Export Options Overview Direct Export from After Effects Utilizing Media Encoder After Effects https://www.adobe.com By the end of this 40-hour After Effects training, you will: Master Essentials: Understand fundamental and advanced After Effects features for diverse projects. Create Impactful Visuals: Craft compelling motion graphics, animations, and visual effects. Expert Animation Skills: Perfect keyframing, motion paths, and dynamic animations. Streamlined Workflow: Organize projects efficiently, ensuring smooth project execution. Creative Expression: Manipulate shapes, animate text, apply effects, and create masks creatively. Professional Exporting: Master export techniques for various platforms and media. Confidence and Expertise: Solve challenges confidently, applying skills in real-world projects. Industry-Ready: Gain skills applicable in filmmaking, animation, marketing, and creative sectors. Ongoing Support: Access post-training support for continued assistance. Certification: Receive a recognized certification, enhancing your professional profile. Course Title: Adobe After Effects Comprehensive Training Key Details: Duration: 40 hours Learning Approach: Personalized Training: Tailored content with 1-2-1 sessions. Flexible Schedule: Choose hours between 9 am and 7 pm, Monday to Saturday. Method: Hands-on learning with step-by-step demonstrations. Course Highlights: Master Essential Tools: From basics to advanced features for motion graphics and visual effects. Expert Guidance: Certified trainers provide personalized attention. Creative Animation: Learn advanced animation techniques, motion paths, and effects application. Efficient Workflow: Optimize project organization, layer management, and export techniques. Real-World Projects: Apply skills in filmmaking, animation, marketing, and more. Post-Training Support: Lifetime access to email and phone assistance for continued guidance. Certification: Receive a recognized certificate upon course completion. Benefits: Industry-Relevant Skills: Gain expertise for diverse creative sectors. Unleash Creativity: Craft compelling motion graphics, animations, and visual effects. Confidence in Execution: Solve challenges confidently with real-world application. Professional Recognition: Enhance your profile with a certified After Effects proficiency. Course Materials and Certification: Upon enrollment, you will receive a valuable After Effects training guide in PDF format, serving as a useful resource during and after the course. Additionally, upon successful completion, you'll be awarded an e-certificate, validating your achievement in the Adobe After Effects training program. Post-Course Support: Rest assured, you'll have access to lifetime email support from your dedicated After Effects trainer, providing assistance for any inquiries or challenges arising after the course. Prerequisites and Software Version: No prior After Effects knowledge is required for enrollment. The training is tailored for After Effects 2023, with techniques applicable to recent software releases. Whether you're a Windows or Mac user, the training suits your needs. Our Guarantees: We prioritize your satisfaction with our double guarantee - a price assurance ensuring the best value for your investment and a training guarantee ensuring you master essential concepts and skills.
CompTIA Security+
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for This course is designed for people who are seeking to launch a career in cybersecurity. Overview Assess the security posture of an enterprise environment and recommend and implement appropriate security solutions; Monitor and secure hybrid environments, including cloud, mobile, and IoT; Operate with an awareness of applicable laws and policies, including principles of governance, risk, and compliance; Identify, analyze, and respond to security events and incidents. CompTIA Security+ is a global certification that validates the baseline skills necessary to perform core security functions and is the first security certification a candidate should earn. CompTIA Security+ establishes the core knowledge required of any cybersecurity role and provides a springboard to intermediate-level cybersecurity jobs. Lesson 1: Summarize Fundamental Security Concepts Security Concepts Security Controls Lesson 2: Compare Threat Types Threat Actors Attack Surfaces Social Engineering Lesson 3: Explain Cryptographic Solutions Cryptographic Algorithms Public Key Infrastructure Cryptographic Solutions Lesson 4: Implement Identity and Access Management Authentication Authorization Identity Management Lesson 5: Secure Enterprise Network Architecture Enterprise Network Architecture Network Security Appliances Secure Communications Lesson 6: Secure Cloud Network Architecture Cloud Infrastructure Embedded Systems and Zero Trust Architecture Lesson 7: Explain Resiliency and Site Security Concepts Asset Management Redundancy Strategies Physical Security Lesson 8: Explain Vulnerability Management Device and OS Vulnerabilities Application and Cloud Vulnerabilities Vulnerability Identification Methods Vulnerability Analysis and Remediation Lesson 9: Evaluate Network Security Capabilities Network Security Baselines Network Security Capability Enhancement Lesson 10: Assess Endpoint Security Capabilities Implement Endpoint Security Mobile Device Hardening Lesson 11: Enhance Application Security Capabilities Application Protocol Security Baselines Cloud and Web Application Security Concepts Lesson 12: Explain Incident Response and Monitoring Concepts Incident Response Digital Forensics Data Sources Alerting and Monitoring Tools Lesson 13: Analyze Indicators of Malicious Activity Malware Attack Indicators Physical and Network Attack Indicators Application Attack Indicators Lesson 14: Summarize Security Governance Concepts Policies, Standards, and Procedures Change Management Automation and Orchestration Lesson 15: Explain Risk Management Processes Risk Management Processes and Concepts Vendor Management Concepts Audits and Assessments Lesson 16: Summarize Data Protection and Compliance Concepts Data Classification and Compliance Personnel Policies Additional course details: Nexus Humans CompTIA Security Plus Certification (Exam SY0-601) training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the CompTIA Security Plus Certification (Exam SY0-601) course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

The Art of Negotiation: Virtual In-House Training
By IIL Europe Ltd
The Art of Negotiation: Virtual In-House Training Confidence, rapport, curiosity, and patience are essential ingredients to successfully handling a difficult conversation and negotiation. In this course, you will learn to identify and manage aspects of a negotiation, distinguish needs from wants, and manage expectations. The course will cover communication best practices, strategies for handling difficult conversations, and the basics of the art of negotiation. What you Will Learn Master the different ways to say 'no' Determine negotiation strategies based on typical client strategies Develop solutions to break deadlocks Getting Started Introductions Course structure Course goals and objectives Establishing personal learning objectives Foundation Concepts Exercise: Most Challenging Scenarios and Outcomes Debrief: Impact versus intent Addressing customer expectations Needs versus wants Key skills for managing customer relationships Elicitation (requirements gathering) Communication and active listening Sensitivity and empathy Handling Difficult Conversations Saying 'no' The Ladder of Inference 4-Step approach for handling difficult conversations Characteristics of a trusted advisor Communication Best Practices Attunement and active listening Exercise: Identifying Effective Techniques Communication pitfalls and best practices Building rapport and influence Words of wisdom Exercise: Reflection on Challenges Negotiation Strategies Negotiation basics Five phases of negotiation Identifying different strategies Traditional versus Progressive Hard - Soft - Principled Exercise: Your Preferred Techniques Selecting appropriate strategy for project negotiations Common pitfalls to avoid The impact of culture on negotiation Looking at conflict through the lens of negotiation Exercise: Mapping a Resolution

BOHS P403 - Asbestos Fibre Counting (PCM) (including Sampling Strategies)
By Airborne Environmental Consultants Ltd
Who is this course suitable for? Required to undertake asbestos fibre counting as part of their work Considering a career in asbestos analysis Responsible for managing asbestos analysts Prior Knowledge and Understanding Candidates for this course are expected to be aware of HSG 248 Asbestos: The Analysts' Guide (July 2021), and in particular Appendix 1, Fibres in air: sampling and evaluation of by phase contrast microscopy. Candidates will preferably have prior experience of analysing fibre count samples and may already be participating in a quality control scheme. In addition, candidates are expected to have had training to cover the core competencies outlined within the foundation material detailed within Table A9.1 of HSG248 Asbestos: The Analysts' Guide (July 2021). This may be achieved by In -house learning or through the P400 foundation module.

Organizational Communication
By Nexus Human
Duration 1 Days 6 CPD hours This course is intended for This course is intended for customer service professionals with any level of experience who want to expand their knowledge, improve their skill set, and increase the understanding of customer benefits. This course teaches basic communication terms and organization basics. Students will learn how to communicate effectively, motivate employees, overcome communication barriers, develop leadership habits, understand how communication flows within an organization, develop networks, and identify the roles that individuals fulfill in an organization. Course activities also cover applying technology to organizational communication, discussing innovation and change, examining how environmental context affects communication, and discussion how power and politics affect an organization. Students will also learn how to manage change, stress, conflict, and empower individuals. The manual is designed for quick scanning in the classroom and filled with interactive exercises that help ensure student success. Prerequisites This course is intended for customer service professionals with any level of experience who want to expand their knowledge, improve their skill set, and increase the understanding of customer benefits. 1. Communication basics Effective communication Organizational management Organization types and characteristics Communication flow 2. Leadership and motivation Communication and leadership Communication and motivation 3. Relational context and organizations Relational context Relationships and organizations 4. Technology in the workplace Workplace technology Impact of technology Technology guidelines 5. Context, stress, and managerial tools Environmental context Stress and communication 6. Innovation and change Aspects of innovation Aspects of change 7. Power, politics, and diversity Power and communication Diversity and communication Empowerment and communication Additional course details: Nexus Humans Organizational Communication training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the Organizational Communication course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.
